Cybersecurity researchers have recently unveiled a significant new threat in the evolving landscape of cybercrime: a Mirai-derived botnet self-identifying as xlabs_v1. This sophisticated malware specifically targets internet-exposed devices running the Android Debug Bridge (ADB) service, enlisting them into a vast network capable of launching powerful distributed denial-of-service (DDoS) attacks. The discovery highlights the persistent vulnerability of IoT and Android-based devices when fundamental security practices are neglected, feeding a burgeoning black market for "DDoS-for-hire" services.
The revelation comes from Hunt.io, a prominent cybersecurity research firm that meticulously detailed the malware’s operations and infrastructure. Their investigation began with the identification of an exposed directory on a server hosted in the Netherlands, accessible without any authentication at the IP address "176.65.139[.]44". This unsecured server served as a critical entry point for researchers to uncover the inner workings of xlabs_v1, revealing a meticulously engineered system designed for maximum impact and illicit profit. The unauthenticated access provided an unusual, albeit fortunate, window into the threat actor’s command and control (C2) infrastructure, allowing for a comprehensive analysis of the botnet’s capabilities and its intended targets.
Understanding xlabs_v1: A New Threat Emerges
xlabs_v1 is not an entirely novel construct; it is a derivative of the infamous Mirai botnet, a name synonymous with large-scale IoT attacks since its emergence in 2016. Mirai gained notoriety for its ability to compromise poorly secured IoT devices, turning them into an army of "bots" to launch massive DDoS attacks that crippled major internet services, including significant portions of the internet’s DNS infrastructure. The architecture and fundamental principles of xlabs_v1 bear the hallmarks of its Mirai lineage, albeit with notable enhancements and a refined focus on specific device types and attack vectors, demonstrating the continuous evolution of cyber threats.
The malware boasts an impressive array of 21 flood variants, spanning TCP, UDP, and raw protocols. These include specialized techniques like RakNet and OpenVPN-shaped UDP floods, which are specifically engineered to bypass common consumer-grade DDoS protection mechanisms. RakNet, a popular networking engine for games, and OpenVPN, a widely used virtual private network protocol, highlight the botnet’s tailored approach to disrupt services that rely on these specific protocols. This broad spectrum of attack methods underscores the operator’s intent to deliver a versatile and effective service to their paying clientele. Hunt.io’s analysis confirms that xlabs_v1 is primarily offered as a DDoS-for-hire service, with a distinct emphasis on disrupting online gaming experiences by targeting game servers and Minecraft hosts. The profitability of such services in the competitive online gaming world, where disruption can lead to competitive advantage or simply cause widespread frustration, has made this sector a recurring and lucrative target for cybercriminals.
The Android Debug Bridge (ADB) Vulnerability: A Gateway for Compromise
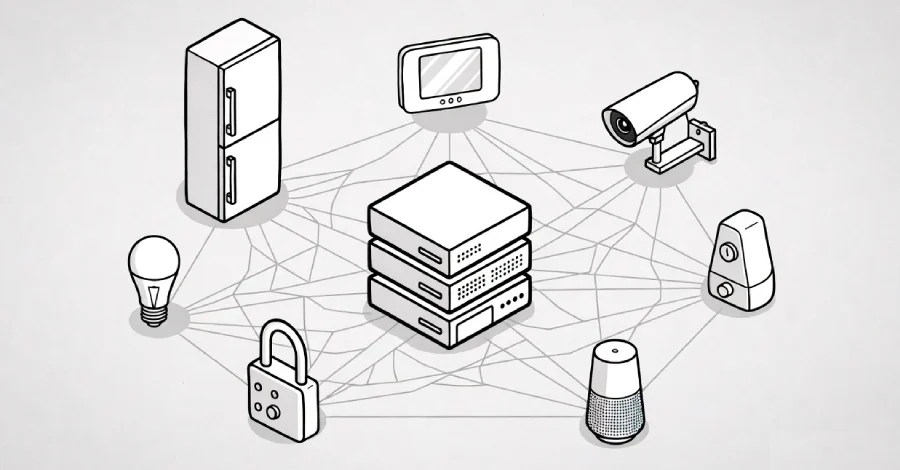
What truly distinguishes xlabs_v1 from many other Mirai variants is its specific targeting mechanism: it actively seeks out Android devices that have an exposed ADB service running on TCP port 5555. ADB is a versatile command-line tool that allows developers to communicate with an Android device for various tasks, including installing and debugging applications, accessing device logs, and executing shell commands. While indispensable for development and troubleshooting, leaving ADB exposed to the internet without proper authentication is a severe security oversight, essentially providing an open backdoor to the device. Many devices, particularly those designed for specific functions or hobbyist use, often ship with ADB enabled by default, or users may enable it for convenience without understanding the associated risks.
This vulnerability transforms a wide range of everyday smart devices into potential recruits for the botnet. Android TV boxes, set-top boxes, and smart TVs are prime targets due to their widespread use, often being connected directly to home networks and frequently overlooked in terms of cybersecurity hygiene. These devices, designed for entertainment and convenience, are typically not subjected to the same security scrutiny as personal computers or smartphones, making them easy prey for automated scanning and exploitation. The simplicity of exploiting an open ADB port – often requiring nothing more than a simple command to push malware onto the device – makes it an attractive vector for threat actors seeking to rapidly expand their botnet infrastructure with minimal effort.
Beyond Android-specific targets, xlabs_v1 also demonstrates multi-architecture support, encompassing ARM, MIPS, x86-64, and ARC builds. This broad compatibility indicates that the botnet is not exclusively focused on Android-based entertainment systems but is also engineered to compromise a wider array of internet-of-things (IoT) hardware, including residential routers. The inclusion of these architectures significantly expands the potential pool of vulnerable devices, reflecting a strategy to maximize the botnet’s scale and attack capacity by exploiting common weaknesses across diverse hardware platforms. Many routers and IoT devices run embedded Linux distributions on these architectures, making them susceptible to Mirai-style attacks if default credentials or known vulnerabilities are not addressed.
Infrastructure and Discovery Timeline
The discovery of xlabs_v1 began with Hunt.io’s proactive monitoring of suspicious network activity. In a timeline typical of advanced threat intelligence, their systems flagged an unauthenticated, publicly exposed directory on a Netherlands-hosted server at IP address "176.65.139[.]44". This initial finding provided a critical pivot point, leading researchers to uncover the botnet’s command and control (C2) infrastructure. The server was found to host the malware binaries, configuration files, and potentially logs related to the botnet’s operations. The operator’s panel, identified as "xlabslover[.]lol," serves as the central hub from which attack commands are issued and bot activity is monitored. This panel likely provides a user interface for clients of the DDoS-for-hire service to initiate and manage their attacks.

Unique Operational Design: Bandwidth Profiling and Lack of Persistence
One of the most intriguing aspects of xlabs_v1’s design is its bandwidth-tiered pricing model, a feature directly linked to a unique bandwidth-profiling routine. The botnet incorporates a sophisticated mechanism to collect victim device bandwidth and geolocation data. This is achieved by opening 8,192 parallel TCP sockets to the geographically nearest Speedtest server, saturating these connections for 10 seconds, and then reporting the measured data transfer rate (in Megabits per second, Mbps) back to the operator’s control panel. This elaborate routine, typically seen in more advanced commercial operations, enables the operators to accurately assign each compromised device to a specific pricing tier for paying customers of the DDoS-for-hire service. This allows them to charge premium prices for attacks leveraging high-bandwidth bots, maximizing their illicit revenue and offering a granular service to their clientele.
An important, and somewhat unusual, characteristic of xlabs_v1 is its deliberate lack of a persistence mechanism. Unlike many other malware strains that seek to embed themselves deeply within a system to survive reboots or system cleanups, xlabs_v1 does not write itself to disk persistence locations, modify init scripts, create systemd units, or register cron jobs. This means that once the bandwidth information is sent, the bot exits. For the device to be used in a subsequent attack, or for its bandwidth to be re-profiled, the operator must re-infect it through the same ADB exploitation channel.
Hunt.io interprets this design choice not as a flaw, but as an intentional operational strategy: "This design suggests the operator views bandwidth probing as an infrequent fleet-tier-update operation rather than a per-attack pre-flight check, and the resulting exit-and-re-infect cycle is the design intent." This approach minimizes the bot’s footprint on the compromised device, potentially reducing the chances of detection by some security tools, and streamlines the process for the operator to update their inventory of available attack power without maintaining constant, resource-intensive connections to every bot. It implies a "fire-and-forget" approach for data collection, followed by targeted re-infection for actual attacks, suggesting a trade-off between persistence and stealth.
The "Killer" Subsystem and Competitive Landscape
The world of botnets is fiercely competitive, with different operators vying for control over compromised devices. xlabs_v1 includes a "killer" subsystem, a common feature in modern botnets, designed to terminate rival malware processes on infected devices. By eliminating competitors, xlabs_v1 ensures it can usurp the victim device’s full upstream bandwidth, dedicating it entirely to carrying out its DDoS attacks. This internal warfare among botnets highlights the economic drivers of cybercrime, where control over digital resources directly translates to profit. A device with multiple botnets competing for resources would be less effective for any single operator, making the "killer" function a crucial component for maximizing the value of each compromised host and ensuring optimal attack performance.
Identifying the Threat Actor: "Tadashi" and Co-located Threats
While the full identity of the individuals or group behind xlabs_v1 remains unknown, researchers have uncovered a moniker associated with the threat actor: "Tadashi." This name was found embedded within a ChaCha20-encrypted string present in every build of the bot, serving as a digital signature of sorts for the malware’s creator or primary operator. Attribution in cybersecurity is notoriously difficult, but such embedded identifiers can sometimes provide crucial clues or connections to other activities attributed to the same entity, aiding law enforcement and intelligence agencies in their investigations.
Further analysis of the co-located infrastructure revealed additional concerning activity. On a host adjacent to the xlabs_v1 server, specifically at IP address 176.65.139[.]42, researchers discovered a VLTRig Monero-mining toolkit. Monero (XMR) is a privacy-focused cryptocurrency often favored by cybercriminals for its anonymity features, making it a popular target for illicit mining operations (cryptojacking). While the presence of a Monero miner on an adjacent host raises suspicions, it is currently not definitively known if the xlabs_v1 botnet operations and the Monero-mining activities are the work of the same threat actor. However, the co-location suggests a potential link or, at the very least, indicates that the infrastructure is being used for multiple illicit purposes, a common practice among cybercriminal groups to maximize resource utilization and obfuscate individual operations.
Broader Context: The DDoS-for-Hire Ecosystem and Mirai’s Legacy
Hunt.io characterizes xlabs_v1 as "mid-tier" in the commercial-criminal landscape. It is deemed "more sophisticated than the typical script-kiddie Mirai fork," indicating a certain level of technical competence in its development and operation. However, it falls short of the "top tier of commercial DDoS-for-hire operations," which often employ far more elaborate evasion techniques, persistence mechanisms, and global infrastructure. This assessment suggests that the operator, "Tadashi," is primarily "competing on price and attack variety, not technical sophistication." Their target demographic—consumer IoT devices, residential routers, and small game-server operators—aligns with this strategy, as these targets are often less protected and more susceptible to relatively straightforward exploitation compared to enterprise-level targets.
The emergence of xlabs_v1 underscores the enduring legacy of the Mirai botnet. Since its source code was leaked in 2016, Mirai has served as a foundational blueprint for countless derivative botnets, continuously adapted and refined by various threat actors. These variants often target new vulnerabilities or specific types of devices, ensuring that the threat of IoT-driven DDoS attacks remains potent. The DDoS-for-hire market continues to thrive, fueled by the accessibility of botnet tools and the demand for disruptive services. This illicit economy poses a significant challenge to online businesses and service providers, particularly those in the gaming sector, which faces constant threats.
The Gaming Industry Under Siege
The gaming industry continues to be a primary target for DDoS attacks, and xlabs_v1 further solidifies this trend. Online gaming platforms, servers, and competitive esports events are frequently disrupted by malicious actors, often for reasons ranging from competitive sabotage to extortion, or simply to cause chaos and demonstrate capability. The financial stakes in the gaming world are enormous, with millions of dollars in revenue from game sales, in-game purchases, and esports sponsorships, making it an attractive target for those seeking to leverage DDoS attacks for profit or competitive advantage. These attacks can lead to significant downtime, loss of player trust, and direct financial losses for gaming companies.

Further illustrating this ongoing threat, Darktrace, another prominent cybersecurity firm, recently revealed its own findings regarding a DDoS botnet. An intentionally misconfigured Jenkins instance within Darktrace’s honeypot network was targeted by unknown threat actors who deployed a DDoS botnet downloaded from a remote server ("103.177.110[.]202"). This incident, occurring concurrently with the xlabs_v1 discovery, emphasizes the widespread and persistent nature of botnet campaigns. Darktrace noted that the attackers took active steps to evade detection, a common tactic in sophisticated operations, showcasing the cat-and-mouse game between defenders and attackers.
Darktrace’s analysis concluded, "The presence of game-specific DoS techniques further highlights that the gaming industry continues to be extensively targeted by cyber attackers." This observation aligns perfectly with xlabs_v1’s focus on game servers and Minecraft hosts. The company’s warning serves as a crucial reminder for server operators to implement robust DDoS mitigation strategies and ensure their infrastructure is adequately protected against such assaults. The impact of these attacks extends beyond mere inconvenience, potentially leading to significant financial losses for businesses and severe reputational damage within the highly competitive gaming community.
Implications and Recommendations
The discovery of xlabs_v1 carries significant implications for both consumers and device manufacturers. For individuals, it serves as a stark reminder of the security risks associated with internet-connected devices, especially those that come with powerful debugging tools like ADB enabled by default. The casual disregard for security in the pursuit of convenience creates a fertile ground for exploitation, turning everyday appliances into tools for cybercrime.
For Consumers:
- Disable ADB: If you are not an Android developer, ensure that ADB is disabled on all your Android-based devices (smart TVs, TV boxes, media players, etc.). Check your device settings for developer options and disable "USB debugging" or "ADB over network."
- Change Default Passwords: For all IoT devices and routers, immediately change default usernames and passwords to strong, unique credentials. Many botnets, including earlier Mirai variants, rely on default credentials for initial compromise.
- Regular Software Updates: Keep all device firmware and software updated to patch known vulnerabilities. Manufacturers frequently release security patches that address such exploits.
- Network Segmentation: Consider segmenting your home network to isolate IoT devices from your main computers and sensitive data. This can limit the impact if an IoT device is compromised.
- Firewall Rules: Implement robust firewall rules on your router to block unsolicited incoming connections, especially to ports like TCP 5555, if not explicitly required for legitimate services.
For Manufacturers and Developers:
- Secure by Design: Devices should ship with ADB disabled by default and require explicit, multi-step user action to enable it, along with clear warnings about the security implications. Security should be a foundational principle, not an afterthought.
- Strong Authentication: If ADB must be enabled, it should always require strong authentication, ideally public-key cryptography, and not be exposed to the internet.
- Regular Security Audits: Conduct thorough security audits of device firmware and operating systems to identify and remediate vulnerabilities before products reach the market. Post-launch monitoring and patching are also critical.
- Clear Communication: Provide clear and accessible security guidelines to end-users, emphasizing the importance of securing their devices. User education is a key component of overall cybersecurity.
For Game Server Operators:
- DDoS Mitigation Services: Invest in professional DDoS mitigation services that can detect and filter malicious traffic at scale. These services can absorb large-volume attacks and allow legitimate traffic to pass through.
- Network Architecture: Design network architecture with redundancy and resilience in mind. Distribute servers across different geographical locations and cloud providers to minimize single points of failure.
- Traffic Monitoring: Implement continuous traffic monitoring and anomaly detection systems to identify unusual traffic patterns indicative of a DDoS attack. Early detection allows for quicker response and mitigation.
Conclusion
The emergence of xlabs_v1 underscores the relentless innovation within the cybercriminal underworld and the persistent vulnerabilities in the rapidly expanding ecosystem of internet-connected devices. As long as devices are deployed with insecure configurations, and as long as there is a lucrative market for disruptive cyberattacks, botnets like xlabs_v1 will continue to evolve and pose a significant threat. The fight against these threats requires a collaborative effort from cybersecurity researchers, law enforcement, device manufacturers, and, crucially, informed consumers to build a more secure digital future. The "mid-tier" sophistication of xlabs_v1 should not be underestimated; its effectiveness lies in exploiting widespread, fundamental security oversights, making it a potent weapon in the hands of malicious actors like "Tadashi." The ongoing vigilance and proactive security measures are paramount to safeguarding digital infrastructure from such pervasive and insidious threats.