CUPERTINO, CA – In an unprecedented move reflecting a heightened state of mobile security alert, Apple has begun dispatching direct Lock Screen notifications to iPhones and iPads still operating on outdated versions of iOS and iPadOS. These critical alerts serve as an urgent warning to users about active web-based attacks and unequivocally implore them to install the latest software updates to safeguard their devices. This proactive measure underscores the severity of current threats, particularly the proliferation of advanced exploit kits like Coruna and DarkSword, which are rapidly democratizing sophisticated surveillance capabilities previously reserved for state-sponsored actors.
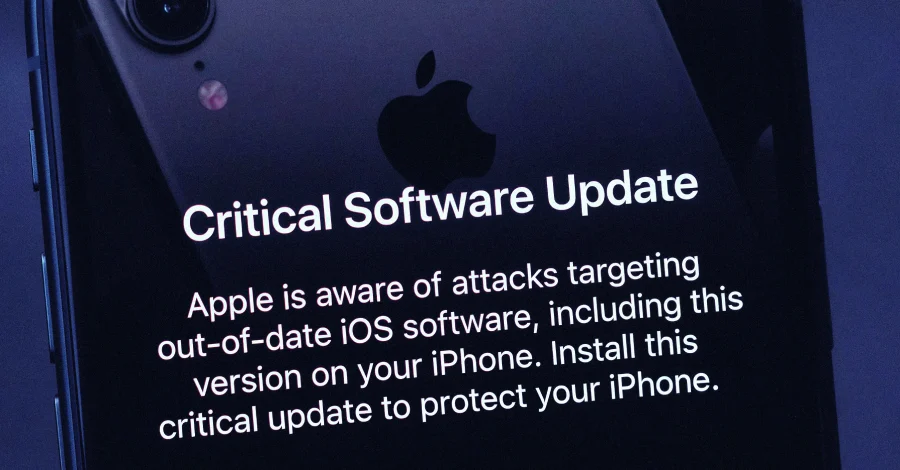
The direct-to-Lock Screen notifications, first reported on March 27, 2026, by MacRumors, represent a significant escalation in Apple’s communication strategy regarding cybersecurity threats. The message displayed prominently on users’ devices leaves no room for ambiguity: "Apple is aware of attacks targeting out-of-date iOS software, including the version on your iPhone. Install this critical update to protect your iPhone." This direct engagement method bypasses traditional channels like email, in-app prompts, or support documents, ensuring that the urgent message reaches users even if they are not actively checking system settings or tech news. The decision to use such an intrusive yet effective notification mechanism highlights the perceived immediacy and widespread nature of the threats.
The Genesis of Alarm: Apple’s Prior Warnings and the Exploit Kit Menace
This assertive communication follows a crucial advisory issued just a week prior, where Apple released a comprehensive support document urging users on older iOS and iPadOS versions to update their devices. That initial warning stemmed from the discovery and analysis of new, potent iOS exploit kits dubbed Coruna and DarkSword. These kits are not merely theoretical threats; multiple threat actors with diverse motivations have been actively leveraging them over the past year. Their modus operandi involves delivering malicious payloads when unsuspecting users navigate to compromised websites, turning ordinary web browsing into a high-stakes security risk.
The term "exploit kit" refers to a collection of exploits designed to automatically detect and compromise vulnerabilities on a target system. In the context of iOS, these kits often chain together multiple zero-day or recently patched vulnerabilities to achieve persistent access or extract sensitive data without the user’s explicit knowledge or interaction. The sophistication of these particular kits, Coruna and DarkSword, suggests a significant leap in the capabilities available to a broader range of malicious actors.
Coruna: An Evolution of State-Sponsored Surveillance
Among the newly identified threats, the Coruna exploit kit has drawn particular attention due to its sophisticated lineage. A recent report published this week by Kaspersky, a renowned Russian cybersecurity vendor, revealed that Coruna is a direct evolution of the framework employed in "Operation Triangulation." This highly sophisticated campaign, which first came to light in June 2023, targeted iPhones through zero-click iMessage exploits – meaning a device could be compromised simply by receiving a specially crafted message, without the user ever opening it or interacting with it.
Kaspersky’s analysis paints a stark picture of Coruna’s capabilities. "Coruna is not a patchwork of public exploits; it is a continuously maintained evolution of the original Operation Triangulation framework," the report stated. This indicates a dedicated development effort, suggesting that the kit is regularly updated and refined to maintain its efficacy against Apple’s evolving security measures. Coruna is specifically designed to target a wide range of devices running iOS versions between 13.0 and 17.2.1, encompassing a substantial portion of Apple’s active device base, particularly those users who might not have updated to the absolute latest major iOS release.

DarkSword: Expanding the Attack Surface
Complementing Coruna is the DarkSword iOS exploit kit, which focuses on a different, yet equally critical, segment of the iOS ecosystem. DarkSword is tailored to exploit iPhones running iOS versions between 18.4 and 18.7. While these versions are relatively current in the rapidly advancing iOS landscape of 2026, their vulnerability underscores that even users who generally keep their devices updated are not immune if they delay critical patch releases within their major OS version. DarkSword is reported to leverage six distinct flaws to achieve its objectives, indicating a multi-pronged attack vector designed for robust compromise. The mention of a "leaked newer version of DarkSword" further amplifies concerns, suggesting that its capabilities are not static but are continually being enhanced and disseminated within the cybercriminal underworld.
The existence of two distinct, highly capable exploit kits targeting different ranges of iOS versions indicates a broad and persistent threat landscape. This dual threat ensures that a wider array of devices, from those several generations behind to those merely a few minor updates shy of the absolute latest, remain susceptible to compromise.
A Chronology of Mounting Concerns
The events leading to Apple’s urgent Lock Screen notifications illustrate a clear escalation of mobile security threats:
- June 2023: The discovery of "Operation Triangulation" marks a turning point, revealing the existence of highly sophisticated, nation-state-level zero-click exploits targeting iPhones. This sets a precedent for advanced mobile surveillance.
- Past Year (circa 2025-2026): Intelligence gathered over the past twelve months indicates a concerning trend: various threat actors, moving beyond state-sponsored entities, begin actively leveraging exploit kits identified as Coruna and DarkSword. This signifies a broadening of access to these powerful tools.
- Week Prior to March 27, 2026: Apple publishes a detailed support document, acknowledging the existence of these new exploit kits and advising users on older iOS/iPadOS versions to update. This serves as an initial, less direct warning.
- This Week (leading up to March 27, 2026): Kaspersky releases its in-depth report on Coruna, cementing its connection to Operation Triangulation and detailing its sophisticated, continuously evolving nature.
- March 27, 2026: Recognizing the urgency and the potential for widespread impact, Apple initiates direct Lock Screen notifications to millions of users, signaling a critical need for immediate action.
The Alarming Trend: Democratization of Cyber Warfare Capabilities
Perhaps the most troubling aspect of these developments is the implied mechanism through which these advanced exploit kits have become so widely accessible. It remains unclear precisely how Coruna and DarkSword found their way into the hands of numerous threat actors and cybercriminals. However, recent cybersecurity research has increasingly highlighted the possibility of an active and thriving market for "second-hand zero-day exploits."
Historically, zero-day exploits – vulnerabilities unknown to the vendor and for which no patch exists – were the exclusive domain of highly resourced state intelligence agencies or specialized, high-end mercenary spyware firms. These exploits commanded exorbitant prices and were deployed sparingly against high-value targets. The concept of "second-hand" exploits suggests that these once-exclusive tools, or their underlying frameworks, are being resold, leaked, or reverse-engineered and then made available to a much broader clientele. This could include less sophisticated criminal gangs, corporate espionage outfits, or even individuals with malicious intent.
The emergence of these kits, coupled with the reported leak of a newer version of DarkSword, fundamentally shifts the landscape of mobile security. It raises profound concerns that these tools could "democratize" access to exploits that were previously reserved for nation-states, effectively turning them into mass-exploitation tools. This commoditization of sophisticated hacking capabilities drastically lowers the barrier to entry for cyberattacks, potentially transforming millions of iPhones and iPads into a significantly larger and more accessible attack surface than ever before. The implications extend beyond individual privacy, posing risks to corporate data, critical infrastructure, and even national security if widely deployed.

Apple’s Defensive Posture and User Recommendations
In response to this evolving threat landscape, Apple continues to emphasize the paramount importance of software updates. For many users, simply installing the latest available version of iOS or iPadOS will patch the vulnerabilities exploited by these kits. However, the challenge lies in the significant portion of users who, for various reasons, delay or neglect updates. These reasons can range from concerns about device performance on newer software, limited storage space, or simply a lack of awareness regarding the critical security implications of outdated systems.
For users who are unable to update to a supported version – perhaps due to device age or compatibility issues – Apple advises considering the activation of Lockdown Mode, if available. Introduced in 2022 with iOS 16 and later, Lockdown Mode is a specialized, extreme protection option designed for a very small number of users who might be at heightened risk of highly targeted cyberattacks, such as journalists, human rights activists, or government officials. When enabled, Lockdown Mode significantly hardens device defenses and strictly limits certain functionalities to reduce the attack surface. This includes disabling message attachment types other than images, restricting certain complex web technologies, blocking FaceTime calls from unknown numbers, and preventing wired connections to computers when the device is locked.
Apple has robustly endorsed the efficacy of Lockdown Mode in its statement shared with TechCrunch: "We are not aware of any successful mercenary spyware attacks against a Lockdown Mode-enabled Apple device." This affirmation provides a strong testament to its protective capabilities for those facing the most sophisticated threats. However, it’s crucial to note that Lockdown Mode is a drastic measure that impacts user experience, and it is not a panacea for devices too old to receive any security updates at all. For those legacy devices, the risk remains considerably higher, prompting difficult choices for users between continued use and upgrading hardware.
Broader Implications for Mobile Security and User Vigilance
The current situation highlights several enduring challenges in the realm of mobile security. The problem of device fragmentation – where a significant percentage of users operate on older OS versions – creates a persistent vulnerability gap. While Apple provides updates for many years, eventually older hardware loses support, leaving millions of devices permanently exposed to newly discovered exploits. This creates a difficult ethical and practical dilemma for both manufacturers and consumers.
Moreover, the increasing sophistication and accessibility of exploit kits signify an ongoing "arms race" between security defenders and malicious actors. As companies like Apple invest heavily in securing their platforms, attackers are simultaneously innovating, often leveraging loopholes in the supply chain of exploits or reverse-engineering powerful tools. The shift from highly targeted, nation-state operations to potentially widespread, mass-exploitation campaigns represents a significant paradigm shift, making virtually every connected device a potential target.
This development underscores the critical importance of user vigilance and proactive security hygiene. Beyond simply updating software, users must adopt a multi-layered approach to digital security: exercising caution when clicking on links, being wary of unsolicited messages, using strong and unique passwords, enabling two-factor authentication, and regularly backing up their data. The Lock Screen notifications from Apple are not merely technical advisories; they are a stark reminder that personal devices are constantly under threat and that active participation from users is an indispensable component of modern cybersecurity defense.
As the digital landscape continues to evolve, the line between state-sponsored cyber warfare and widespread cybercrime blurs. Apple’s unprecedented move to send Lock Screen alerts signals a new era of urgency in mobile security, demanding immediate action from users and ongoing innovation from device manufacturers to protect the integrity of our increasingly interconnected lives.