The announcement of general availability for AWS IAM Identity Center multi-Region support marks a significant advancement in cloud identity and access management, empowering organizations to enhance the resilience, performance, and compliance of their AWS account access and managed application deployments across geographically dispersed operations. This strategic update allows enterprises to replicate workforce identities, permission sets, and associated metadata from a primary AWS Region to additional chosen Regions, fundamentally transforming how global businesses manage identity infrastructure within the AWS ecosystem.
This newly launched capability is designed to address critical challenges faced by organizations operating at scale, particularly those with global workforces or stringent data residency requirements. By enabling the replication of identity data, the AWS IAM Identity Center now offers a robust framework for ensuring uninterrupted access to AWS accounts and applications, even in the unlikely event of a service disruption in a primary Region. This means that an organization’s workforce, whose identities are managed through external identity providers (IdPs) such as Microsoft Entra ID or Okta, can maintain active access to their critical cloud resources from an alternative, replicated Region.
The essence of multi-Region support lies in its dual benefit: enhanced business continuity and optimized user experience. Enterprises can now proactively configure their identity infrastructure to withstand regional outages, a paramount concern for mission-critical operations. Simultaneously, by deploying AWS managed applications closer to their end-users and respective datasets, businesses can significantly reduce latency, thereby improving application responsiveness and overall productivity for their global teams. This proximity also becomes a cornerstone for adhering to complex data residency mandates, enabling organizations to architect their identity and application layers to keep data within specific geographic boundaries.
Understanding AWS IAM Identity Center: A Foundation of Secure Access
To fully appreciate the impact of multi-Region support, it is crucial to understand the foundational role of AWS IAM Identity Center. Formerly known as AWS Single Sign-On (SSO), AWS IAM Identity Center serves as a centralized service that simplifies the management of access to multiple AWS accounts and cloud applications. It provides a unified portal for users to access all their assigned AWS accounts and applications with a single set of credentials, typically federated from an existing corporate directory or an external identity provider.
Before this multi-Region enhancement, while AWS itself operates across numerous global regions, the IAM Identity Center instance for an organization was primarily anchored to a single AWS Region. This architecture, while robust, presented specific considerations for large-scale global deployments. A regional service disruption, however rare, could potentially impact access to AWS accounts and applications for the entire organization, necessitating comprehensive disaster recovery strategies that often involved complex manual interventions or alternative, less streamlined access methods. Furthermore, for multinational corporations, ensuring optimal performance for users geographically distant from the primary Identity Center Region was an ongoing challenge, as was meeting diverse regulatory requirements concerning data locality for identity-related metadata. This new feature directly addresses these long-standing operational and compliance considerations.
The Evolution Towards Global Resilience: A Chronology of Enhancements
The introduction of multi-Region support is not an isolated event but rather a strategic progression in AWS’s ongoing commitment to delivering enterprise-grade identity solutions. This latest feature builds upon a series of enhancements designed to fortify the security and scalability of IAM Identity Center, reflecting AWS’s responsiveness to evolving enterprise needs for distributed and highly available cloud infrastructure.
A key precursor to multi-Region capabilities was the support for customer-managed AWS Key Management Service (AWS KMS) keys for encryption at rest, which became generally available in October 2025. This update was foundational, providing customers with greater control over the encryption of their identity data stored within IAM Identity Center. Notably, AWS experts had already recommended the adoption of multi-Region AWS KMS keys at that time, unless restricted by company policies to single-Region keys. This earlier recommendation underscored the foresight in designing an encryption infrastructure that could inherently support future multi-Region replication needs, providing consistent key material across regions while maintaining independent key infrastructure in each. The current multi-Region support for IAM Identity Center leverages this capability directly, making multi-Region KMS keys a prerequisite for seamless identity replication, thereby ensuring data consistency and security across distributed environments.

This chronological development highlights a deliberate strategy by AWS to empower customers with finer-grained control over their security posture and operational resilience, laying the groundwork for more sophisticated, globally distributed identity management architectures that can adapt to the dynamic demands of modern cloud computing.
Strategic Advantages: Resiliency, Performance, and Compliance at Scale
The multi-Region capability of AWS IAM Identity Center offers several profound strategic advantages for enterprises operating in a globalized and highly regulated environment:
Unprecedented Resiliency and Business Continuity
By replicating workforce identities and permission sets across multiple AWS Regions, organizations can significantly bolster their disaster recovery posture. In the unlikely scenario of a complete service disruption in the primary IAM Identity Center Region, users can still access their AWS accounts through an active AWS access portal endpoint in an additional, replicated Region. This "failover" mechanism is critical for maintaining operational continuity, minimizing downtime, and ensuring that essential cloud resources remain accessible to authorized personnel. This proactive approach to resilience moves beyond traditional backup strategies, offering a live, geographically distributed identity service that enhances availability, aligning identity infrastructure with the high-availability standards of other core AWS services. This directly contributes to a stronger Recovery Time Objective (RTO) and Recovery Point Objective (RPO) for identity-dependent operations.
Optimized User Experience for Global Workforces
For enterprises with a globally distributed workforce, network latency can be a significant impediment to productivity. By enabling the deployment of AWS managed applications in Regions geographically closer to application users, IAM Identity Center multi-Region support dramatically reduces network latency. This results in faster login times, quicker application loading, and a more responsive overall user experience, directly contributing to increased workforce efficiency and satisfaction. For example, a user in Europe accessing an application deployed in an EU Region will experience far superior performance than if the application and identity data were exclusively housed in a US Region, thereby fostering greater user adoption and reducing frustration.
Meeting Stringent Data Residency and Compliance Requirements
Many industries and geographies impose strict regulations regarding where data, particularly identity data, must reside. With multi-Region support, organizations can now strategically deploy AWS managed applications and replicate identity data to specific Regions that align with these data residency requirements. This capability provides a crucial tool for achieving compliance with regulations such as GDPR in Europe, CCPA in California, or industry-specific mandates, simplifying the complex landscape of global data governance. The ability to localize identity data, while maintaining centralized control, is a powerful enabler for businesses operating in highly regulated sectors like finance, healthcare, and government, where data sovereignty is non-negotiable.
Simplified Global Management with Centralized Control
Despite distributing identity infrastructure across multiple Regions, the management of IAM Identity Center configurations, including workforce identities and permission sets, remains centralized from the primary Region. This ensures administrative efficiency, consistency in policy enforcement, and reduces the operational overhead typically associated with managing distributed identity systems. Administrators can configure once and replicate, maintaining a single source of truth for identity governance across their global footprint. This centralized management model, combined with distributed access, offers the best of both worlds: operational simplicity for administrators and enhanced resilience for end-users.
Technical Implementation: A Step-by-Step Overview
Enabling multi-Region support for AWS IAM Identity Center involves a clear, structured process, primarily centered around configuring customer-managed AWS KMS keys and initiating the replication from the AWS console.
Prerequisite: Multi-Region Customer Managed AWS KMS Keys
The foundational step for enabling multi-Region support is ensuring that the AWS managed applications currently in use support customer-managed AWS KMS keys enabled in AWS Identity Center. Crucially, before replicating IAM Identity Center to an additional Region, organizations must first replicate their customer-managed AWS KMS key to that target Region. This replica key must then be configured with the necessary permissions for IAM Identity Center operations.
Multi-Region keys are pivotal because they provide consistent key material across different Regions while maintaining independent key infrastructure in each. This design ensures that encrypted identity data, when replicated, can be decrypted and utilized securely in the target Region without compromising cryptographic integrity or requiring complex key synchronization mechanisms. The AWS KMS Developer Guide offers comprehensive instructions for creating these multi-Region replica keys, guiding users through the necessary steps to prepare their encryption infrastructure, ensuring cryptographic best practices are maintained across all replicated instances.
Configuring Replication via the AWS Console
Once the multi-Region KMS key infrastructure is in place, enabling IAM Identity Center replication is straightforward:
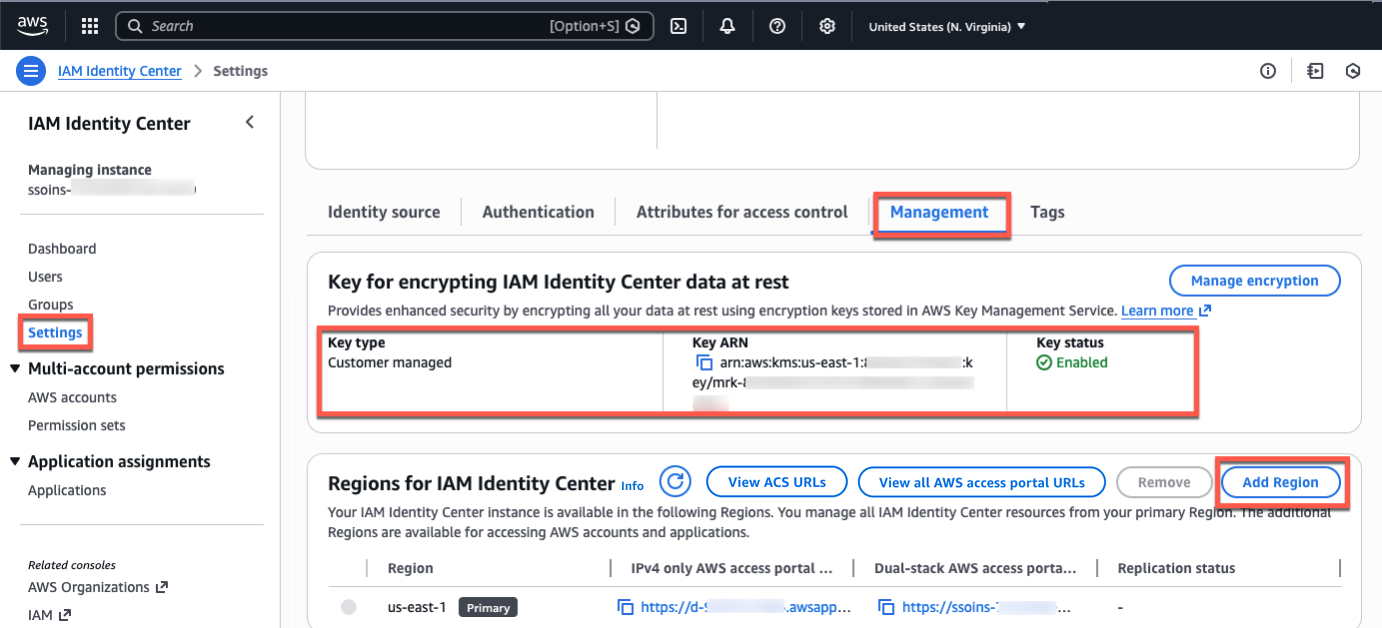
- Access the IAM Identity Center Console: Navigate to the IAM Identity Center console in the designated primary Region (e.g., US East (N. Virginia)).
- Verify KMS Key Configuration: Select "Settings" from the left-navigation pane and then the "Management" tab. Here, administrators must confirm that the configured encryption key is indeed a multi-Region customer-managed AWS KMS key. If not, this must be configured first, as it is a mandatory prerequisite for multi-Region functionality.
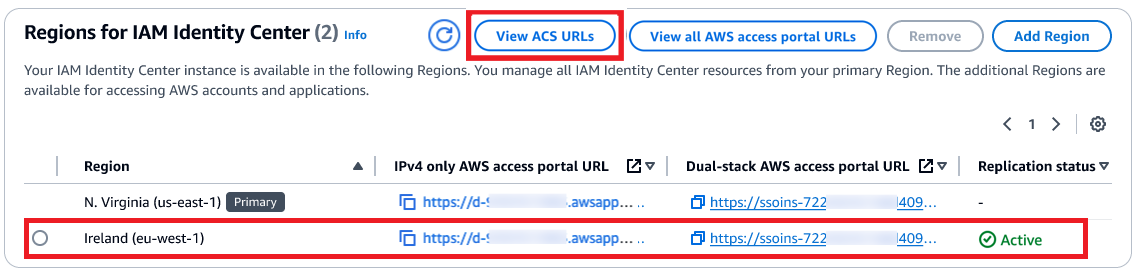
- Add Additional Regions: Choose "Add Region" to initiate the process of selecting target Regions for replication.
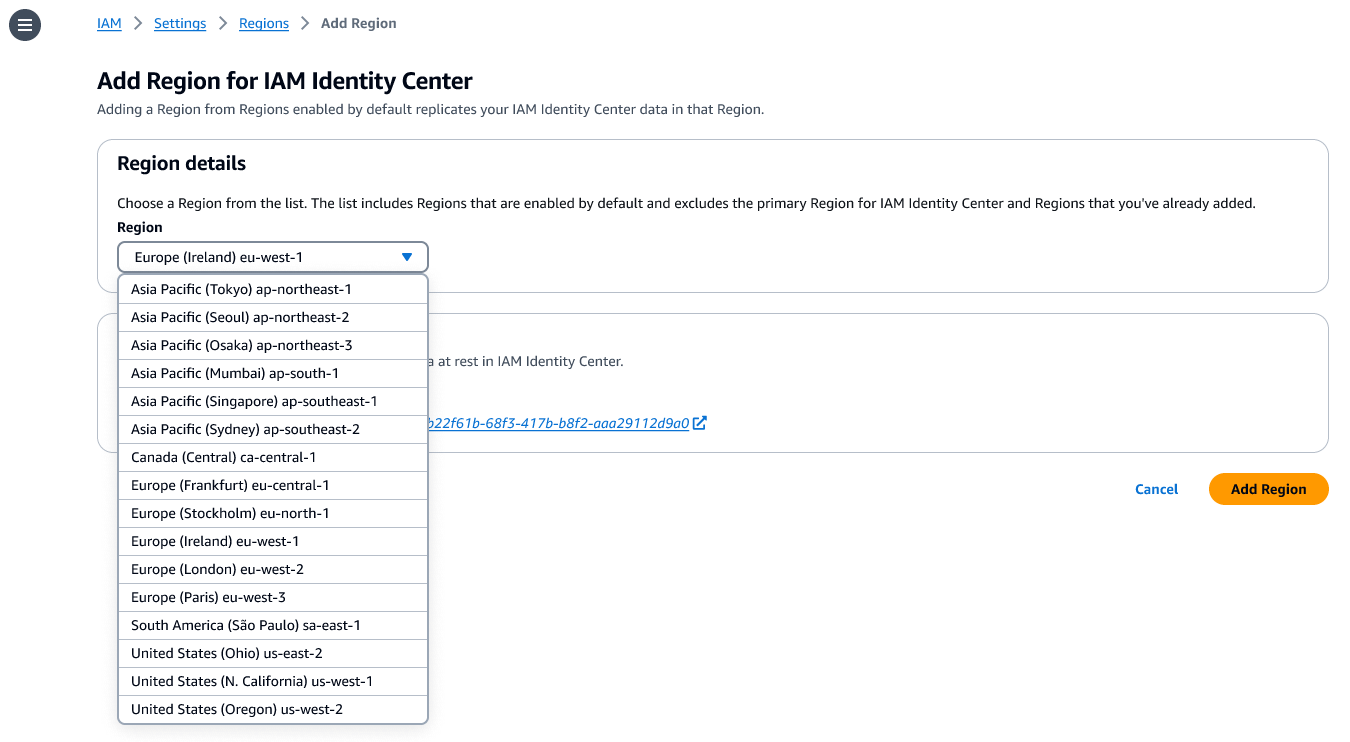
- Strategic Region Selection: When choosing additional Regions, organizations must carefully consider their specific use cases. Factors such as data compliance requirements (e.g., replicating to an EU Region for GDPR adherence), proximity to application users for optimal experience, and the availability of specific AWS managed applications in those Regions are paramount. The IAM Identity Center User Guide provides a comprehensive list of supported applications and their regional availability to aid in this critical decision-making process.
- Initiate Replication: After selecting the desired additional Regions, selecting "Add Region" commences the initial data replication. The duration of this process will vary depending on the size and complexity of the existing Identity Center instance, including the number of users, groups, and permission sets.
- Post-Replication Verification: Upon completion, the console will display the newly replicated Regions. Administrators can then view Assertion Consumer Service (ACS) URLs for both the primary and additional Regions, which are essential for configuring external Identity Providers to direct user traffic efficiently.
Integrating with External Identity Providers (IdPs)
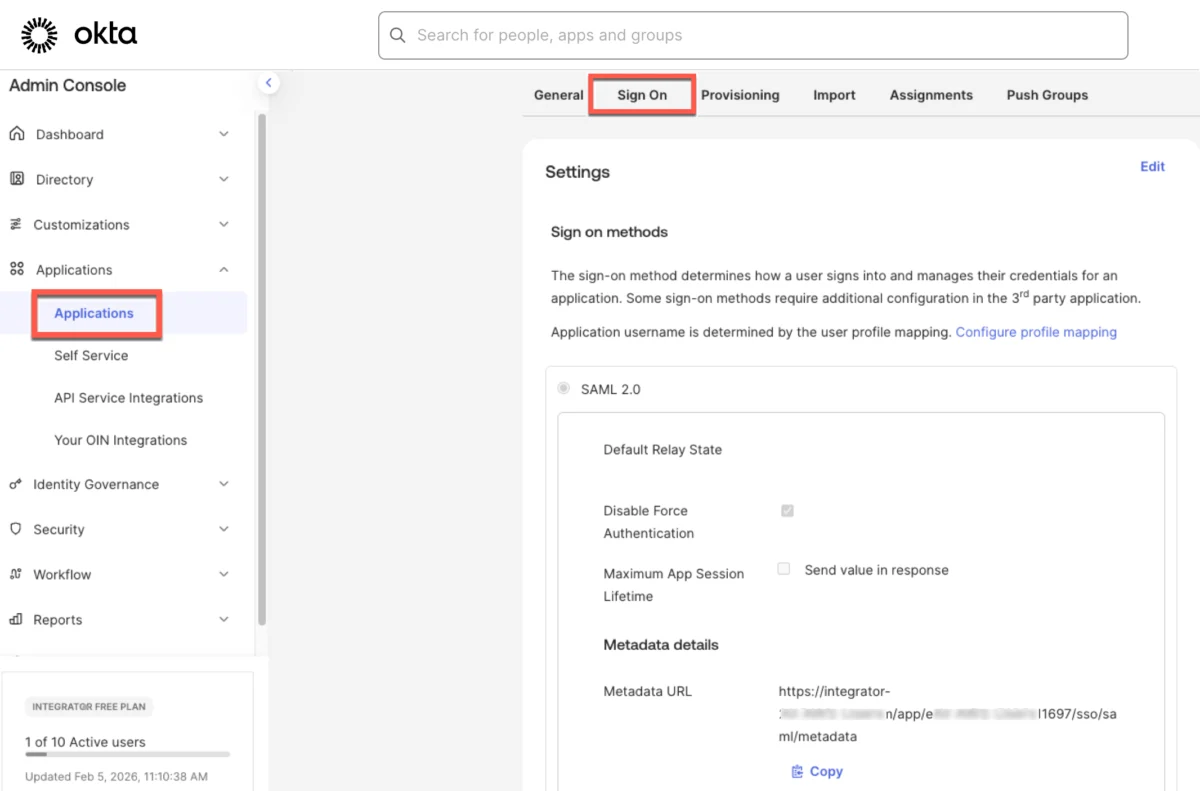
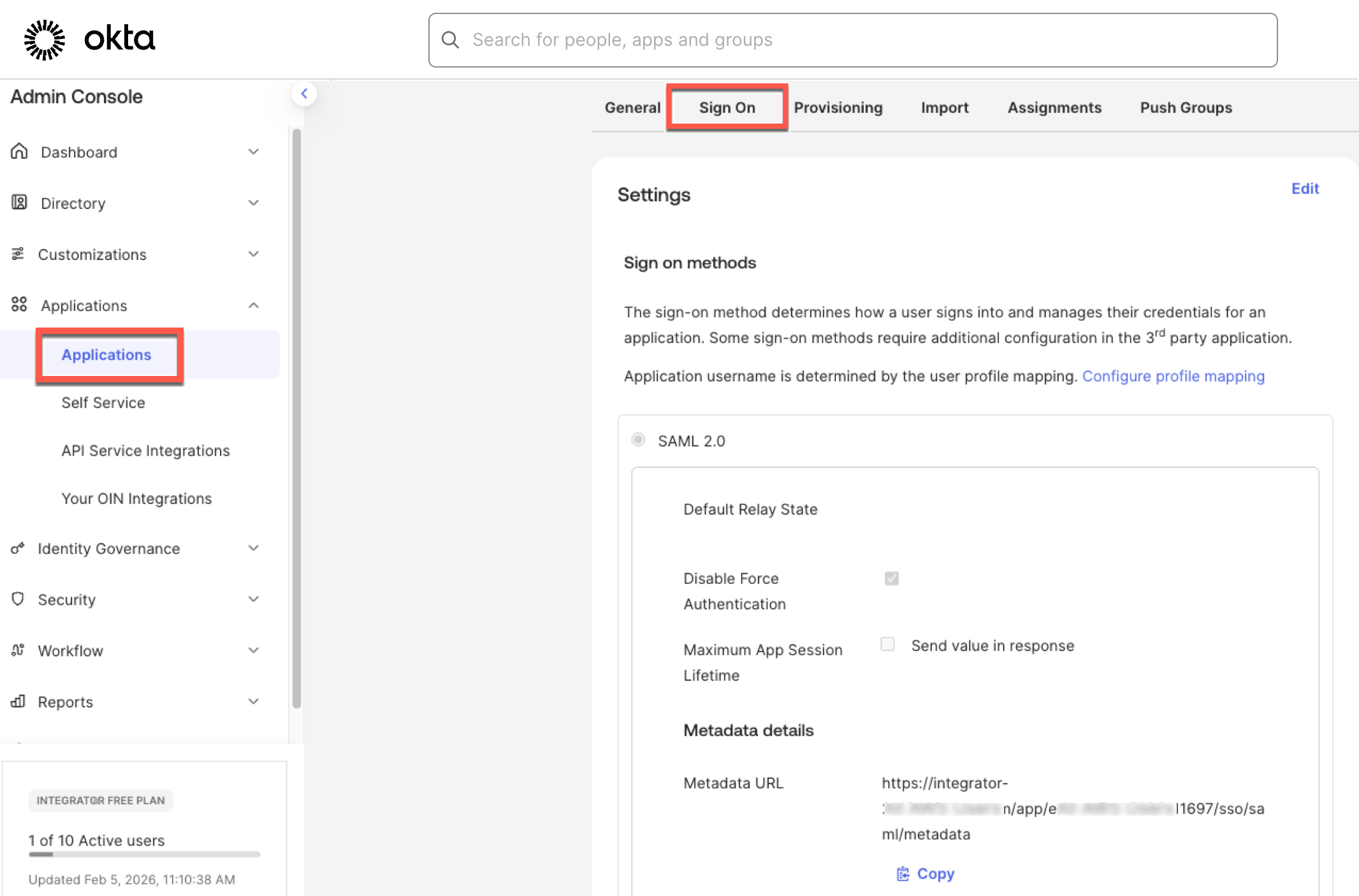
For organizations leveraging external IdPs like Microsoft Entra ID (formerly Azure Active Directory) or Okta for SAML-based single sign-on, an additional configuration step is required to fully utilize the multi-Region capabilities. When a user authenticates through their IdP, they are redirected to the AWS access portal. To ensure users can be redirected to the AWS access portal in a newly added replicated Region, the additional Region’s ACS URL must be incorporated into the IdP’s configuration.
For instance, in the Okta admin console, this typically involves adding the new ACS URL to the AWS application settings. Furthermore, administrators can create "bookmark applications" within their IdP. These bookmark apps function akin to a browser bookmark, containing only the URL to the AWS access portal in the additional Region, providing a discoverable and direct access point for users. This ensures that users can seamlessly access their AWS accounts and applications through the most geographically appropriate and performant access portal endpoint, leveraging the distributed identity infrastructure for optimal performance and resilience.
Broader Implications and Industry Impact
The launch of multi-Region support for AWS IAM Identity Center represents a pivotal moment for enterprises navigating the complexities of cloud adoption and global operations, signaling a significant evolution in cloud identity management paradigms.
Enhanced Enterprise Cloud Strategy
This feature fundamentally alters how enterprises can design their cloud identity architecture. It moves identity from a potential single point of failure to a highly available, globally distributed service, aligning it with the robust, resilient nature of other critical AWS services. This allows for more aggressive cloud-first strategies, particularly for industries with zero-downtime requirements like financial services, healthcare, and telecommunications, where uninterrupted access is paramount for core business functions. It enables a truly global operational model, where identity is not a bottleneck but an enabler of distributed workflows.
Competitive Landscape and Market Positioning
By offering such advanced resiliency and compliance features natively within its identity management service, AWS further strengthens the competitive positioning of IAM Identity Center. It provides a compelling reason for organizations to consolidate their identity management within the AWS ecosystem, reducing reliance on third-party solutions for core AWS access management and potentially simplifying their overall identity stack. This move solidifies AWS’s leadership in providing comprehensive, integrated cloud services that cater to the most demanding enterprise requirements.
Security and Governance Frameworks
While distributing identity data across multiple regions, the underlying security principles of AWS remain paramount. The mandatory use of customer-managed KMS keys ensures that organizations retain granular control over the encryption of their sensitive identity information, even as it is replicated across regions. This combination of geographic distribution and strong encryption provides a robust security posture, critical for protecting user credentials and access policies against both regional outages and potential data breaches. The centralized management model further ensures consistent application of governance policies and audit trails across all replicated regions, simplifying compliance reporting.
Future of Cloud Identity
This development points towards a future where cloud identity services are inherently designed for global scale, extreme resilience, and granular compliance. It sets a new benchmark for what organizations can expect from their cloud providers in terms of identity infrastructure. As more enterprises expand their global cloud footprint, such capabilities will become not just desirable, but indispensable for maintaining operational integrity, meeting regulatory obligations, and delivering an optimal experience to a diverse, global workforce.
Availability and Cost Considerations
AWS IAM Identity Center multi-Region support is now broadly available across the 17 enabled-by-default commercial AWS Regions. This wide availability ensures that a significant portion of AWS’s global customer base can immediately leverage this new capability. AWS has confirmed that the feature itself comes at no additional cost, making it an attractive proposition for organizations looking to enhance their resilience without incurring new service fees for the core identity replication. However, standard AWS KMS charges will apply for the storage and usage of customer-managed keys, which are a mandatory prerequisite for enabling this multi-Region functionality. These charges are typically based on the number of keys created and the volume of cryptographic operations performed.
For organizations planning to implement this feature, consulting the AWS Capabilities by Region page will provide the most up-to-date information on regional availability and any future roadmap developments. Comprehensive documentation is also available in the IAM Identity Center User Guide, which details the technical steps, best practices, and considerations for deploying multi-Region identity infrastructure. AWS also encourages feedback through AWS re:Post for Identity Center or direct AWS Support contacts, indicating a commitment to continuous improvement based on user experience and evolving enterprise needs.
Conclusion
The general availability of multi-Region support for AWS IAM Identity Center represents a significant leap forward in cloud identity management. It directly addresses the evolving needs of global enterprises for enhanced resiliency, optimized performance, and stringent data compliance. By enabling the seamless replication of workforce identities and permission sets across AWS Regions, AWS empowers organizations to build more robust, agile, and secure cloud environments that can truly operate at a global scale, ensuring uninterrupted access to critical resources and applications regardless of geographic distribution or unforeseen regional events. This strategic enhancement solidifies IAM Identity Center’s position as a cornerstone service for modern enterprise cloud operations, providing a vital layer of distributed identity resilience for the digital age.