Amazon Web Services (AWS) today announced the general availability of multi-Region support for AWS IAM Identity Center, a pivotal advancement designed to significantly enhance the resilience, performance, and compliance capabilities for enterprises managing workforce access to AWS accounts and integrated applications. This strategic expansion allows organizations to replicate their identity infrastructure, including workforce identities, permission sets, and associated metadata, from a primary AWS Region to additional Regions. This move marks a substantial leap forward in cloud identity management, addressing critical business continuity, disaster recovery, and data residency challenges that global enterprises frequently encounter.
Enhanced Resiliency and Uninterrupted Business Continuity
The core benefit of multi-Region support lies in its ability to fortify an organization’s identity infrastructure against regional disruptions. Previously, a service disruption in the primary AWS Region where IAM Identity Center was deployed could potentially impede workforce access to critical AWS accounts and applications. With this new capability, organizations can now establish an active-standby or even active-active posture for their identity services across multiple geographic locations. By replicating workforce identities to an additional Region, an active AWS access portal endpoint becomes available in that secondary location. This means that in the rare event of an IAM Identity Center service disruption in its primary Region, employees can seamlessly redirect to the AWS access portal in an additional Region. This ensures continuous access to their AWS accounts and applications, leveraging already provisioned permissions, thereby minimizing downtime and safeguarding critical business operations.
This architecture significantly strengthens an organization’s disaster recovery (DR) strategy. For enterprises heavily reliant on AWS for their mission-critical workloads, the ability to maintain identity continuity across Regions is paramount. It shifts the paradigm from a single point of failure to a distributed, highly available system, aligning with industry best practices for robust cloud infrastructure. Organizations can maintain centralized control over IAM Identity Center configurations from their primary Region, ensuring consistency and simplifying management, even as the underlying identity data is replicated for resilience. This centralized management, combined with distributed availability, offers the best of both worlds: operational efficiency and unparalleled uptime.
Optimizing Performance and Meeting Data Residency Requirements
Beyond enhanced resilience, multi-Region support for IAM Identity Center delivers tangible benefits in terms of user experience and regulatory compliance. Global enterprises often operate with distributed workforces and applications, necessitating that identity services are geographically close to their users and data sources. By deploying AWS managed applications in preferred Regions, closer to the actual application users and their associated datasets, organizations can drastically improve performance and reduce latency. When workforce identities are replicated to these additional Regions, applications can access them locally, leading to faster authentication times and a more responsive user experience. This localized access is critical for applications where milliseconds matter, such as high-volume transaction systems or interactive user interfaces.
Furthermore, this feature is instrumental in addressing increasingly stringent data residency requirements. Many industries and jurisdictions mandate that certain types of data, including identity information, must reside within specific geographical boundaries. With multi-Region support, organizations gain the flexibility to deploy AWS managed applications in Regions that comply with these regulations. For instance, if a company operates in Europe and must ensure all identity data for its European workforce remains within the EU, it can now configure IAM Identity Center to replicate identities to an AWS Region within the EU, ensuring compliance while still serving its global workforce. This capability is particularly vital for sectors like finance, healthcare, and government, where regulatory adherence is not just a best practice but a legal imperative. By allowing companies to choose where their identity data is stored and processed, AWS empowers them to navigate complex global regulatory landscapes more effectively.
Technical Implementation: A Step-by-Step Guide for Adoption
Implementing multi-Region support for AWS IAM Identity Center involves a structured approach, beginning with prerequisites related to encryption and key management. The process leverages AWS Key Management Service (AWS KMS) and requires careful configuration within the IAM Identity Center console and external Identity Providers (IdPs).
Importance of Multi-Region AWS KMS Keys
A fundamental prerequisite for enabling multi-Region support is the use of customer-managed AWS KMS keys. AWS IAM Identity Center encrypts sensitive data at rest using these keys. When AWS introduced support for customer-managed KMS keys for encryption at rest in October 2025, it strongly recommended the adoption of multi-Region KMS keys. Unlike single-Region keys, multi-Region keys provide consistent key material across different AWS Regions while maintaining independent key infrastructure in each Region. This consistency is crucial for seamless replication and decryption of identity data across geographically dispersed IAM Identity Center instances.

Before initiating the replication of IAM Identity Center to an additional Region, organizations must first replicate their customer-managed AWS KMS key to that target Region. This replica key then needs to be configured with the necessary permissions for IAM Identity Center operations. The AWS KMS Developer Guide provides detailed instructions for creating these multi-Region replica keys, ensuring that the cryptographic foundation for the multi-Region identity infrastructure is robust and correctly established. This step underscores AWS’s commitment to security by design, ensuring that even as data is replicated, its encryption remains under the customer’s control.
Configuring IAM Identity Center for Multi-Region Operations
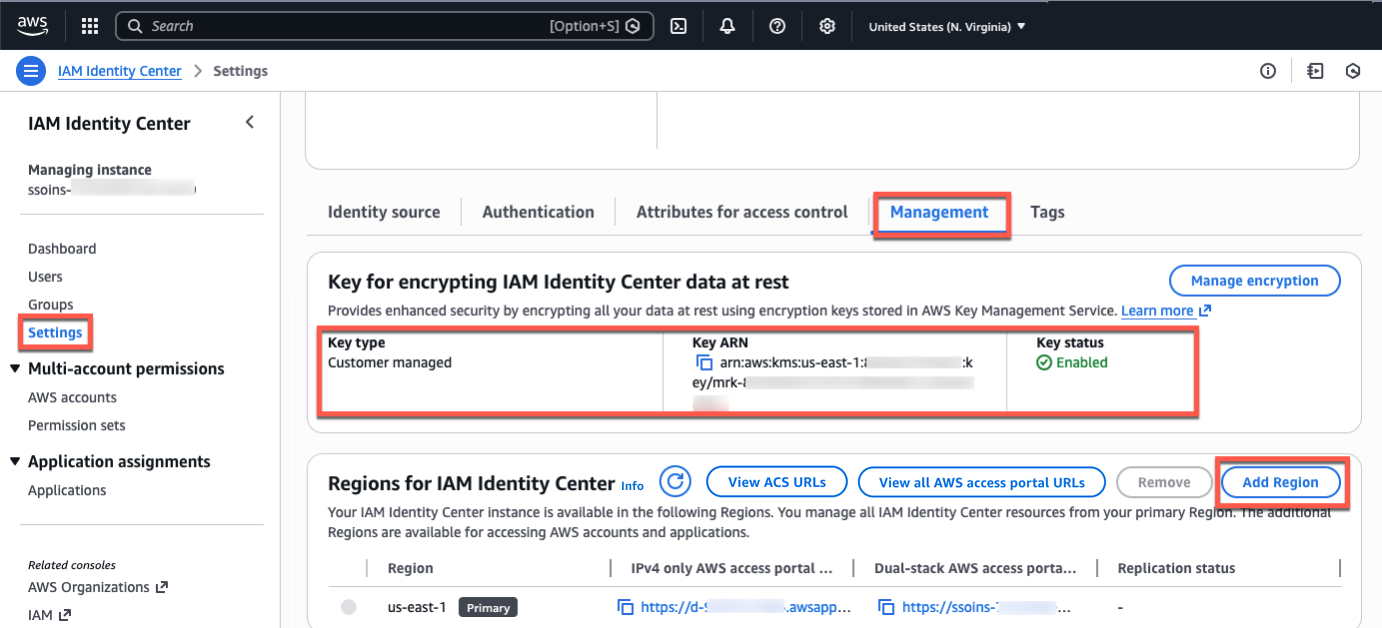
Once the multi-Region AWS KMS key is in place and properly configured, the next step involves enabling multi-Region support directly within the IAM Identity Center console. Administrators navigate to the IAM Identity Center console in their primary Region (e.g., US East (N. Virginia)), access the Settings section, and select the Management tab. Here, they must confirm that the configured encryption key is indeed a multi-Region customer-managed AWS KMS key.
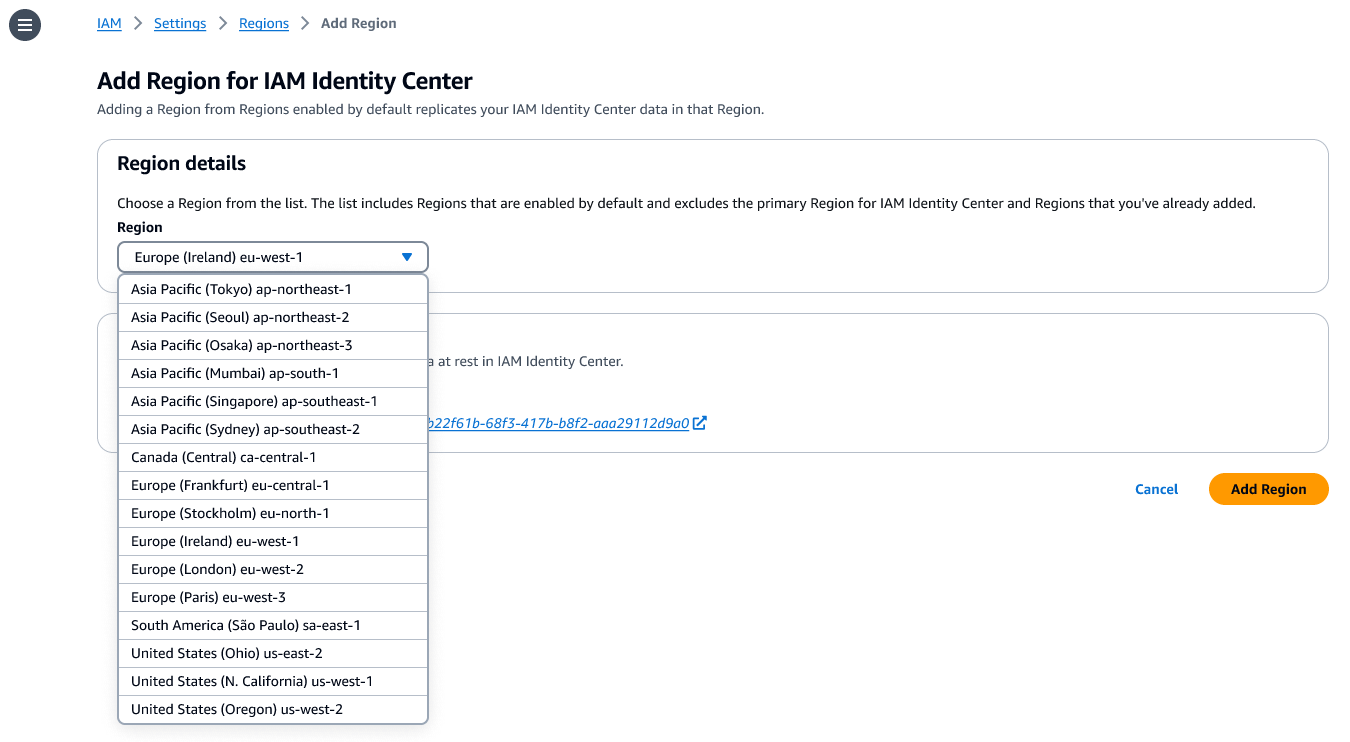
To add additional Regions, the administrator simply selects the Add Region option. During this selection process, strategic considerations come into play. Organizations must carefully evaluate their intended use cases, such as data compliance mandates or user experience optimization. For instance, if the goal is to run AWS managed applications that access datasets restricted to a specific Region for compliance, the chosen additional Region must be where those datasets reside. Similarly, if the primary objective is to improve user experience, selecting a Region geographically closer to the largest user base would be ideal. It is also critical to verify that any required AWS managed applications support the chosen Region and deployment in additional Regions, as compatibility can vary. After selecting the desired additional Region(s) and confirming the choice, the initial replication process commences. The duration of this initial replication is dependent on the overall size and complexity of the existing Identity Center instance, ranging from minutes to potentially longer for very large organizations. Upon completion, the newly added Region becomes active, and users can begin accessing their AWS accounts and applications through this new endpoint.
Integrating with External Identity Providers
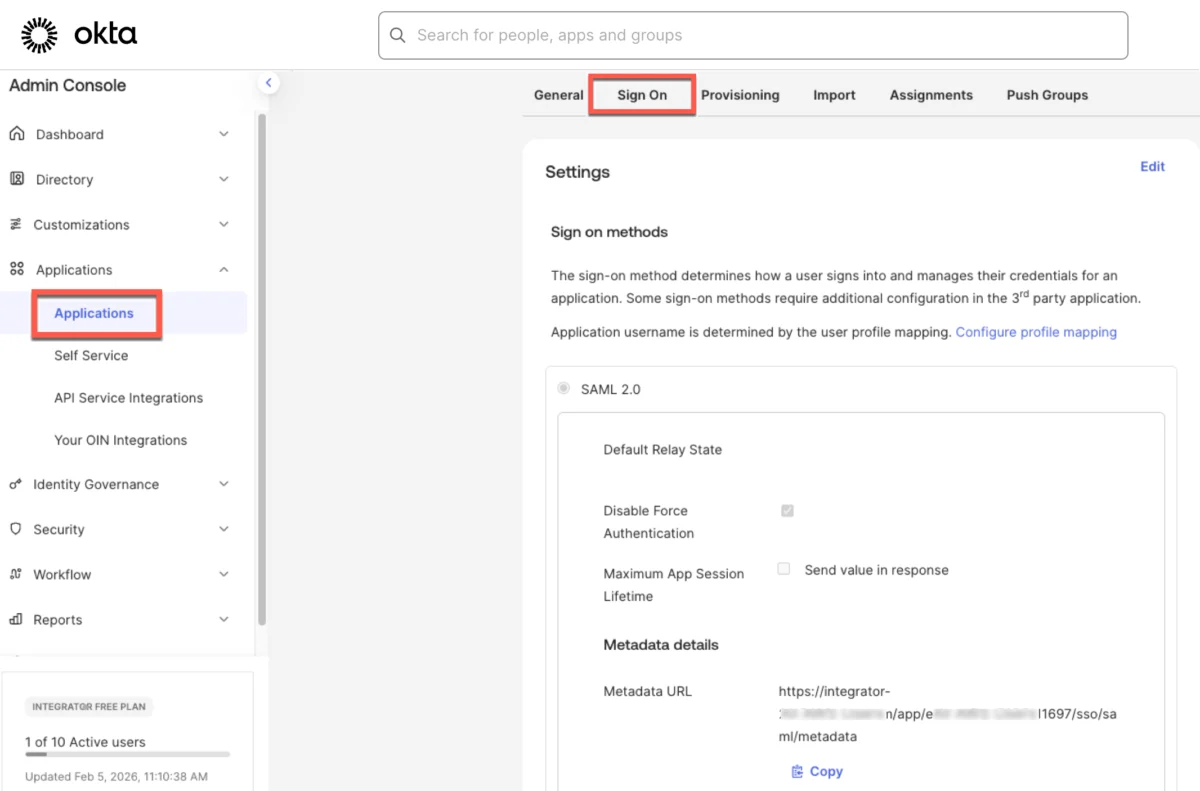
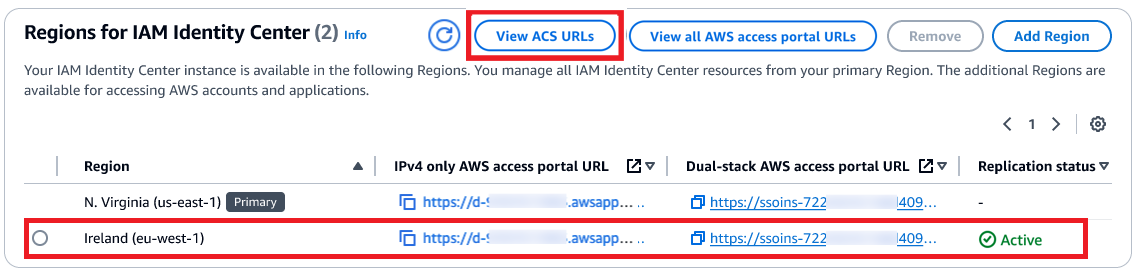
For organizations leveraging external Identity Providers (IdPs) such as Microsoft Entra ID (formerly Azure Active Directory) or Okta for SAML single sign-on (SSO) with AWS IAM Identity Center, an additional configuration step is required. When a user authenticates through their IdP, they are redirected to the AWS access portal. To ensure users can be redirected to the AWS access portal in the newly added Region, the additional Region’s Assertion Consumer Service (ACS) URL must be added to the IdP configuration.
This involves updating the SAML application configuration within the IdP’s administration console. For example, in Okta, administrators would navigate to the AWS IAM Identity Center application settings and add the new ACS URL obtained from the IAM Identity Center console. This ensures that the IdP is aware of all available AWS access portal endpoints across different Regions. To facilitate user discovery and access, organizations can also create "bookmark applications" within their IdP. These bookmark apps function much like a browser bookmark, containing only the URL to the AWS access portal in the additional Region, providing a clear path for users to access the correct regional endpoint. Workforce users can then access their applications or accounts using existing methods, including the AWS access portal, direct application links, or via the AWS Command Line Interface (AWS CLI), which now inherently understands the multi-Region context. The IAM Identity Center User Guide provides comprehensive details on which AWS managed applications support deployment in additional Regions, enabling administrators to plan their multi-Region strategy effectively.
Broader Context: The Evolution of Identity Management in AWS
The introduction of multi-Region support for AWS IAM Identity Center represents a significant milestone in the evolution of cloud identity management. Historically, managing identities and access across diverse cloud environments presented considerable challenges, often involving complex, custom integrations or reliance on single-Region identity stores, which introduced inherent risks. AWS IAM Identity Center was designed to centralize access management for AWS accounts and applications, simplifying the experience for both administrators and end-users. Its initial single-Region deployment, while powerful, meant that large global enterprises had to implement elaborate architectural patterns or accept certain trade-offs to achieve regional redundancy for identity services.
This new feature addresses those architectural complexities head-on. It aligns with the broader industry trend towards "zero trust" security models, where identity is a primary control plane, and access decisions are made based on the least privilege principle and continuous verification. By distributing the identity infrastructure across multiple Regions, organizations enhance their overall security posture, reducing the attack surface associated with a single, centralized identity endpoint. Furthermore, it supports the growing adoption of hybrid cloud and multi-cloud strategies, where enterprises seek flexible, resilient, and compliant solutions that can span on-premises and various cloud environments. This update positions AWS IAM Identity Center as an even more compelling solution for organizations undergoing large-scale cloud transformations, particularly those in highly regulated industries that demand robust and geographically distributed identity governance.
Industry Impact and Strategic Implications
The implications of AWS IAM Identity Center’s multi-Region support are far-reaching for a wide array of industries and organizations. For global enterprises with operations spanning continents, this feature translates directly into reduced operational overhead. Managing identity and access for a geographically dispersed workforce becomes significantly simpler and more resilient, eliminating the need for complex custom solutions or fragmented identity stores. This simplification frees up IT resources to focus on innovation rather than maintenance.
In highly regulated sectors such as financial services, healthcare, and government, the ability to meet stringent data residency and business continuity requirements with an out-of-the-box AWS solution is transformative. It lowers the barrier to cloud adoption for these industries, enabling them to leverage the scalability and agility of AWS while adhering to their compliance obligations. For example, a financial institution can now confidently extend its AWS footprint globally, knowing that its identity infrastructure can meet regional regulatory demands and withstand major outages without compromising service availability or data integrity.
From a security perspective, distributing the identity infrastructure across multiple Regions enhances the overall resilience against various types of attacks, including denial-of-service attempts targeting a specific Region. It also supports better isolation of incidents, meaning an issue in one Region is less likely to impact global access. Industry analysts anticipate that this feature will accelerate the migration of sensitive workloads to AWS, particularly for organizations that previously hesitated due to concerns about identity resilience and compliance. AWS officials emphasize that this enhancement underscores their commitment to providing enterprise-grade capabilities that meet the most demanding requirements of their global customer base, aligning with a strategic vision of cloud as a secure, compliant, and highly available platform for all types of workloads.
Availability and Cost Considerations
AWS IAM Identity Center multi-Region support is now generally available across the 17 enabled-by-default commercial AWS Regions. This broad availability ensures that a significant portion of AWS’s global customer base can immediately begin leveraging these advanced capabilities. For a comprehensive list of Regional availability and a future roadmap, customers are encouraged to consult the AWS Capabilities by Region resource.
Crucially, the multi-Region support feature itself is offered at no additional cost. This means organizations can enhance their identity resilience and performance without incurring extra charges specifically for the replication functionality. However, standard AWS KMS charges will apply for storing and using customer-managed keys in each Region where they are replicated. These charges are typically usage-based and transparent, allowing organizations to manage costs effectively. This pricing model reinforces AWS’s commitment to making essential enterprise-grade features accessible to a wide range of customers, further driving cloud adoption and optimization. Organizations are encouraged to explore this new capability through the AWS Identity Center console, delve into the IAM Identity Center User Guide for detailed instructions, and provide feedback via AWS re:Post for Identity Center or their usual AWS Support channels. This feedback loop is vital for AWS to continue refining and expanding its identity services to meet evolving customer needs.
Key Considerations for Implementation
While the benefits of multi-Region support are substantial, organizations should be aware of several key considerations during implementation and ongoing management:
- Careful Planning: Thorough planning is essential, including selecting appropriate secondary Regions based on geographical proximity to users, data residency requirements, and existing AWS infrastructure footprint.
- KMS Key Management: Ensuring proper replication and permissioning of multi-Region customer-managed KMS keys is critical. Any misconfiguration can lead to access issues.
- IdP Configuration Updates: Administrators must meticulously update their external Identity Provider configurations with the new ACS URLs for additional Regions to ensure seamless user redirection.
- Application Compatibility: Verify that all AWS managed applications intended for multi-Region deployment are indeed supported in the chosen secondary Regions and can integrate effectively with the distributed identity infrastructure.
- Testing: Comprehensive testing of failover scenarios and user access flows in the secondary Region is crucial before full production deployment to validate resilience and functionality.
- Monitoring and Alerting: Implement robust monitoring and alerting for IAM Identity Center and its dependencies (like KMS) across all configured Regions to quickly detect and respond to any issues.
- Security Best Practices: Continue to adhere to AWS security best practices, including least privilege access, regular auditing, and strong authentication methods, across all identity components.
This strategic expansion by AWS solidifies IAM Identity Center’s position as a robust, enterprise-ready solution for managing workforce identities, enabling organizations to build more resilient, compliant, and high-performing cloud environments in an increasingly interconnected and regulated world.