Amazon Web Services (AWS) today announced the general availability of AWS Security Hub Extended, a pivotal expansion of its comprehensive security management service designed to simplify and unify full-stack enterprise security across a sprawling digital estate. This new offering significantly broadens AWS Security Hub’s reach beyond native AWS services, integrating a curated selection of leading third-party security solutions to provide a single, streamlined experience for procurement, deployment, and ongoing security operations. The move underscores AWS’s strategic commitment to addressing the complex and fragmented security challenges faced by modern enterprises operating across cloud, hybrid, and on-premises environments.
The introduction of Security Hub Extended follows the re-imagined AWS Security Hub, which was initially unveiled at re:Invent 2025. That previous iteration focused on unifying AWS security services such as Amazon GuardDuty and Amazon Inspector, offering near real-time analytics and intelligent risk prioritization within the AWS ecosystem. Building upon this foundation, Security Hub Extended now extends this principle of unification to the entire enterprise security landscape, encompassing critical domains like endpoint protection, identity and access management, email security, network defense, data loss prevention, browser security, cloud native protection, AI security, and comprehensive security operations.
The Evolution of AWS Security Hub: From Native Integration to Enterprise Ecosystem
The journey of AWS Security Hub reflects the evolving demands of cloud security. When AWS Security Hub was first introduced, its primary objective was to provide a centralized view of security alerts and compliance status across various AWS accounts and services. It aggregated findings from AWS services like Amazon GuardDuty (threat detection), Amazon Inspector (vulnerability management), AWS Config (configuration compliance), and AWS Firewall Manager, normalizing them into a standardized format. This initial offering was a significant step towards reducing the operational burden for security teams managing large AWS deployments.
At re:Invent 2025, AWS further enhanced Security Hub, introducing a "re-imagined" platform that emphasized advanced analytics and sophisticated risk prioritization capabilities. This update empowered security professionals to move beyond mere aggregation, enabling them to automatically and continuously analyze security findings in combination, thereby identifying and responding to critical risks with greater precision and speed. The focus was on enabling a proactive security posture within the AWS cloud environment, leveraging the power of machine learning and automation to surface the most impactful threats.
However, the reality for most large enterprises is a multi-vendor, often hybrid-cloud security architecture. Organizations rarely rely solely on a single cloud provider’s native security tools, necessitating integration with existing endpoint detection and response (EDR) solutions, identity providers, secure web gateways, and data security platforms. This fragmentation leads to operational inefficiencies, increased costs, and potential security blind spots. Recognizing this pervasive challenge, AWS has now taken the logical next step with Security Hub Extended, positioning it not just as a cloud security orchestrator, but as a central nervous system for the entire enterprise security estate. This strategic expansion signals AWS’s ambition to become a central pillar in enterprise security operations, extending its reach far beyond its own cloud boundaries.
Bridging the Gap: A Comprehensive Security Portfolio Beyond AWS
The core value proposition of AWS Security Hub Extended lies in its ability to bridge the gap between cloud-native security and the broader enterprise security landscape. By acting as the seller of record for a curated selection of AWS Partner solutions, AWS simplifies what has traditionally been a cumbersome and resource-intensive process for enterprises. This curated approach ensures that the integrated solutions meet AWS’s standards for effectiveness and interoperability, while also providing customers with a streamlined procurement and management experience.

Strategic Partner Collaborations and Their Scope
The list of initial partners for Security Hub Extended reads like a who’s who of leading cybersecurity vendors, each specializing in critical areas of enterprise protection. This strategic selection ensures comprehensive coverage across diverse threat vectors and attack surfaces:
- Endpoint Security: Solutions like CrowdStrike bring advanced endpoint detection and response (EDR) capabilities, protecting user devices, servers, and workloads from sophisticated malware and exploits.
- Identity and Access Management (IAM): Partners such as Okta and SailPoint address the complexities of managing user identities and access privileges, crucial for preventing unauthorized access and ensuring compliance. Britive also plays a role in this space, often focusing on just-in-time access and privileged access management.
- Email Security: Proofpoint offers robust protection against phishing, malware, and business email compromise (BEC) attacks, which remain primary vectors for cybercriminals.
- Network and Zero Trust Security: Zscaler provides cloud-native zero trust access solutions, securing network traffic and application access regardless of user location. Splunk, a Cisco company, also contributes with its powerful SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) capabilities, which are fundamental for network visibility and threat response.
- Data Security: Cyera focuses on data security posture management, helping organizations discover, classify, and protect sensitive data across their environments.
- Browser Security: Island offers enterprise browser solutions that enhance security and control for end-user web access.
- Application and Code Security: Oligo and Upwind specialize in runtime application security and cloud-native application protection, respectively, securing applications throughout their lifecycle.
- AI Security: 7AI represents a forward-looking inclusion, addressing the emerging security challenges and opportunities presented by artificial intelligence deployments.
- Security Operations and Automation: Opti and Noma contribute to optimizing security operations, often through automation and specialized tooling.
This diverse array of partners allows enterprises to construct a robust, multi-layered security architecture that spans traditional IT infrastructure, modern cloud environments, and emerging technologies like AI, all managed from a centralized hub. The curation process by AWS is critical here, as it removes the burden of vetting and integrating disparate solutions, a process that can often take months or even years for large organizations.
The Operational and Financial Advantages of Unified Procurement
One of the most significant pain points for Chief Information Security Officers (CISOs) and procurement teams is the sheer complexity of managing multiple security vendors. Industry reports consistently indicate that large enterprises often grapple with an average of 75 or more security tools, each with its own licensing model, contract terms, billing cycle, and support structure. This vendor sprawl leads to:
- Increased Administrative Overhead: Managing numerous procurement cycles, contract negotiations, and vendor relationships consumes valuable time and resources that could otherwise be dedicated to security strategy and implementation.
- Billing Complexity: Receiving separate bills from dozens of vendors complicates financial tracking and budgeting.
- Inconsistent Support: Navigating different support channels for various products can delay incident resolution.
- Integration Challenges: Ensuring interoperability and data exchange between disparate security tools is a constant technical challenge.
AWS Security Hub Extended directly addresses these challenges by consolidating the procurement and billing process. With AWS acting as the seller of record, customers benefit from:
- Pre-negotiated Pay-as-You-Go Pricing: This eliminates the need for individual contract negotiations and large upfront investments, offering financial flexibility and aligning costs with actual consumption.
- A Single Consolidated Bill: All charges for both AWS Security Hub and the integrated partner solutions appear on a single monthly AWS bill, drastically simplifying financial management.
- No Long-Term Commitments: The pay-as-you-go model provides agility, allowing organizations to adapt their security posture without being locked into multi-year contracts.
- Unified Level 1 Support: For AWS Enterprise Support customers, this means a single point of contact for initial troubleshooting and support across both AWS services and the partner solutions, significantly streamlining incident management.
This simplification translates into tangible benefits: reduced operational costs, faster time to deployment for new security capabilities, and a re-allocation of resources from administrative tasks to strategic security initiatives.
Technical Underpinnings: OCSF and the Single Pane of Glass
The technical backbone enabling this unified experience is the Open Cybersecurity Schema Framework (OCSF). OCSF is an open-source standard designed to normalize security findings from various products and services into a common, structured format. Before OCSF, security teams spent considerable effort transforming data from different vendors into a usable format for their Security Information and Event Management (SIEM) systems or other analytical tools. This often led to data loss, inconsistencies, and delays in threat detection and response.

With Security Hub Extended, all participating AWS and partner solutions emit their security findings in the OCSF schema. This automatic normalization is critical because it allows Security Hub to aggregate and correlate these findings seamlessly, regardless of their origin. For security analysts, this means:
- Consistent Data: A standardized view of security events across the entire enterprise.
- Improved Correlation: The ability to identify complex attack patterns that might involve multiple systems and security layers, such as an endpoint alert (from CrowdStrike) followed by an identity compromise (from Okta) and subsequent data exfiltration (monitored by Cyera).
- Faster Response: With normalized and correlated data, security teams can more quickly understand the scope and impact of an incident, leading to more efficient and effective response actions.
- Enhanced Automation: The consistent schema facilitates the development of automated playbooks and workflows for incident response, further reducing manual effort.
The result is a genuine "single pane of glass" experience within the AWS Security Hub console. This unified view empowers security teams to gain immediate and direct access to all security findings, enabling them to quickly identify and respond to risks that span traditional boundaries between cloud infrastructure, endpoints, identities, and applications.
Market Context: Addressing the Enterprise Security Landscape Challenges
The launch of Security Hub Extended comes at a time when the cybersecurity landscape is more challenging than ever. Organizations face an relentless barrage of sophisticated threats, a severe shortage of skilled cybersecurity professionals, and increasing regulatory pressure. In this environment, the need for integrated, efficient, and comprehensive security solutions is paramount.
Combating Vendor Sprawl and Complexity
The issue of vendor sprawl is not merely an inconvenience; it’s a significant security risk. A multitude of disconnected tools often leads to:
- Security Gaps: Unmanaged integrations or overlooked areas between tools can create blind spots for attackers to exploit.
- Alert Fatigue: Overwhelming numbers of uncontextualized alerts from various systems can lead to legitimate threats being missed.
- Increased Attack Surface: Each new tool introduces its own management interface, potential vulnerabilities, and configuration complexities.
AWS Security Hub Extended directly confronts these issues by offering a consolidated platform. By curating partners and streamlining the operational aspects, AWS aims to provide a more cohesive and resilient security posture for its customers. This strategy aligns with a broader industry trend towards security consolidation and platforms that offer end-to-end visibility and control.
Strategic Positioning in the Cybersecurity Market
This initiative also positions AWS more competitively in the broader enterprise security market. While AWS has always offered robust native cloud security services, the move into managing and selling third-party security solutions positions it closer to becoming a comprehensive security platform provider, akin to traditional cybersecurity vendors that offer integrated suites. This could potentially attract enterprises that prefer a single vendor relationship for a significant portion of their security needs, reducing the complexity of dealing with numerous specialized providers.
For the participating partners, integration with Security Hub Extended offers a significant opportunity to reach a vast customer base through AWS’s trusted platform, benefiting from simplified procurement and billing that removes common barriers to adoption. This creates a powerful ecosystem effect, where AWS acts as an enabler for both customers seeking integrated solutions and partners looking to expand their market reach.
Deployment and Accessibility: Streamlined Adoption
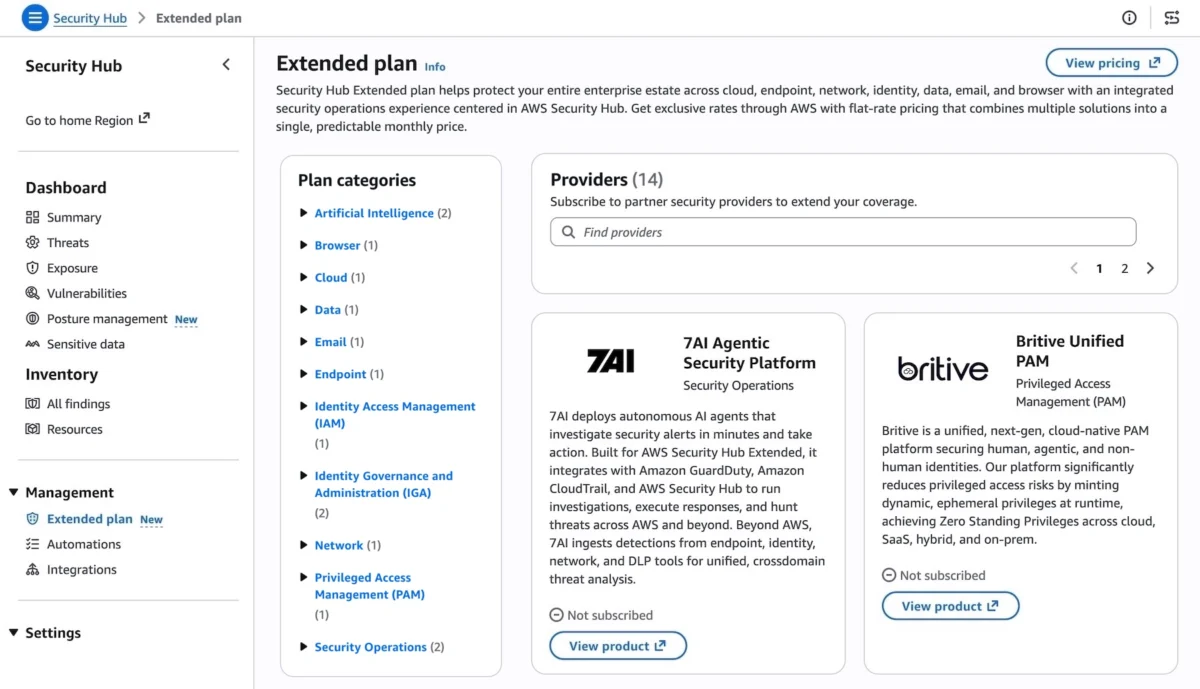
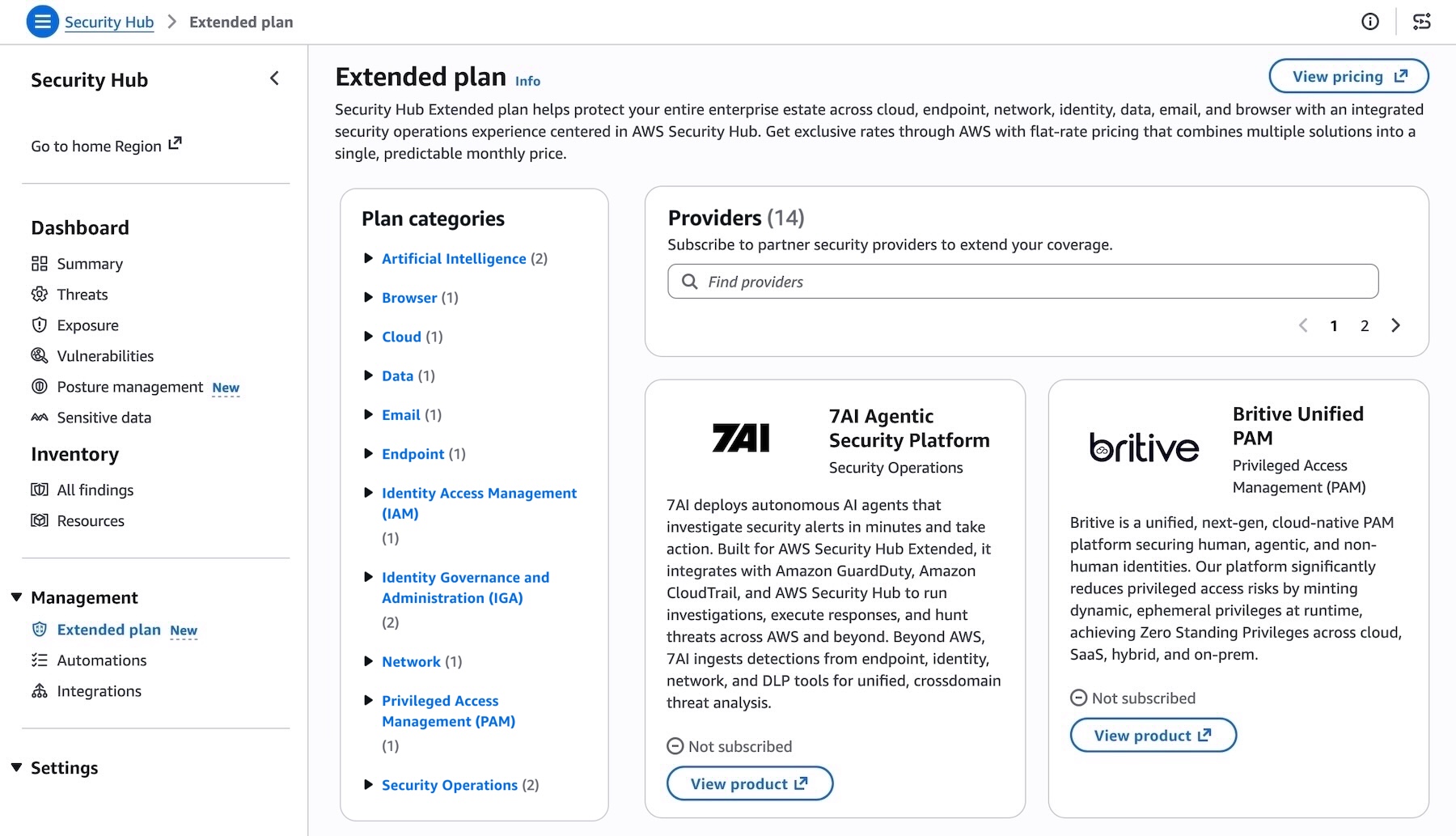
AWS has ensured that adopting Security Hub Extended is as straightforward as its core services. Customers can access the partner solutions directly within the Security Hub console by selecting "Extended plan" under the "Management" menu. From there, they can review details of each partner offering and subscribe. The onboarding experience is automated, with each partner guiding the customer through their specific setup process. Once onboarded, consumption-based metering is automatic, and customers are billed monthly as part of their Security Hub bill. This seamless integration from discovery to billing is a crucial differentiator, removing friction points that often deter organizations from adopting new security technologies.
Analyst and Industry Reactions
Early reactions from industry analysts are expected to be largely positive, highlighting the pragmatic approach AWS has taken to address a genuine customer pain point. Analysts will likely emphasize the strategic importance of OCSF in enabling true integration and the operational efficiencies gained from consolidated procurement and billing. The move is seen as a maturation of AWS’s security strategy, evolving from purely cloud-native protection to a more holistic, enterprise-wide security management offering that acknowledges the hybrid realities of modern IT environments. This initiative is anticipated to drive further adoption of AWS Security Hub as the central security control plane for many organizations.
Conclusion: A Glimpse into the Future of Enterprise Security
The AWS Security Hub Extended plan represents a significant leap forward in enterprise security management. By unifying native AWS security services with a curated selection of leading third-party solutions, AWS is providing a powerful platform that simplifies procurement, streamlines operations, and enhances the overall security posture of organizations. It tackles the pervasive challenges of vendor sprawl, operational complexity, and fragmented visibility head-on, offering a path towards a more integrated, efficient, and resilient security future. This strategic move solidifies AWS’s position not just as a leading cloud provider, but as a critical enabler for comprehensive enterprise cybersecurity, helping organizations navigate the complexities of the digital threat landscape with greater confidence and control.
The AWS Security Hub Extended plan is now generally available in all AWS commercial Regions where Security Hub is available. Customers can utilize flexible pay-as-you-go or flat-rate pricing models, requiring no upfront investments or long-term commitments. Further information on pricing can be found on the AWS Security Hub pricing page. Organizations are encouraged to explore the capabilities within the Security Hub console and provide feedback through AWS re:Post for Security Hub or their usual AWS Support contacts.