A significant advancement in open-source security tooling has arrived with the launch of Betterleaks, a new secret-scanning utility developed by Zach Rice, the original creator of the widely adopted Gitleaks tool. This successor project introduces a fundamentally reworked detection methodology, enhanced validation flexibility, accelerated scanning speeds, and a more controlled development environment. Significantly, Betterleaks has secured sponsorship from Aikido, a rapidly growing security startup valued at over a billion dollars, which is actively investing in a diverse portfolio of open-source security initiatives.
The core problem Betterleaks aims to address is the pervasive risk of exposing sensitive credentials—such as API keys, passwords, and tokens—within software code. In the complex architecture of modern software, these secrets are indispensable for inter-service authentication, database access, and communication with external applications. Developers often embed these credentials directly into code during the early stages of development, typically within configuration files, scripts, or testing environments, with the intention of relocating them to more secure storage later. However, this practice can inadvertently lead to secrets being integrated into codebases that are subsequently shared more broadly than intended.
When code repositories are made public, logs are exported, or code is transferred between environments, these embedded credentials can become exposed. This exposure creates a critical vulnerability, as automated bots are constantly scanning public code-hosting platforms and other online sources for exploitable credentials. Once compromised, these secrets can grant malicious actors access to cloud infrastructure, enable the unauthorized provisioning of computing resources, facilitate data exfiltration, or be leveraged for a wide array of other damaging activities.
The escalating volume of code generation, particularly with the advent of AI-powered development tools, is exacerbating this risk. AI assistants can rapidly produce large quantities of code, often with reduced manual oversight, thereby increasing the likelihood that sensitive information will inadvertently seep into the open. Zach Rice, the architect behind both Gitleaks and Betterleaks, has observed this trend firsthand. He notes that developers sometimes over-rely on AI assistants, inserting real credentials for testing purposes and then overriding warnings from the AI to ignore these secrets, a practice Rice believes is widespread.
"And I guarantee you, most people are doing that, rather than taking the time to properly manage their secrets," Rice stated in an interview with The New Stack. This behavior is further reinforced by the rapid iteration cycles characteristic of AI-assisted development, sometimes referred to as "vibe coding," where generated code is accepted and refined with less rigorous scrutiny. Some security professionals have even described this phenomenon as "AI psychosis," where prolonged interaction with AI systems can lead to an unhealthy overreliance and a diminished capacity for critical evaluation of AI-generated output. Essentially, AI is increasingly acting as a supplementary cognitive tool, potentially at the expense of the user’s own critical thinking.
Rice elaborated on this dynamic, explaining, "If you’re in this loop of kind of instant gratification of code being churned out… You forget. You totally forget about those secrets that you told the AI agent not to worry about. I would say LLMs, for sure, increase the risk of secrets leaking."
The Genesis of Secret Scanning: A Look Back at Gitleaks
To fully appreciate the evolution leading to Betterleaks, it is pertinent to trace the origins of Gitleaks back to 2018. Rice initially conceived Gitleaks as a personal project, allowing him the freedom to shape its development from its inception. At that time, existing tools like TruffleHog, primarily written in Python, were already addressing the challenge of identifying exposed credentials in code. However, Rice saw an opportunity to reimagine the approach using the Go programming language, incorporating a user-configurable system and significantly improving performance.
"I wanted a tool that I could have some creative control over, and improve upon," Rice explained. He credits Dylan Ayrey, the creator of TruffleHog and founder of Truffle Security, as a key figure who first recognized secret scanning as a distinct and critical problem area within the security landscape. Rice viewed Gitleaks as a creative outlet for his programming pursuits.
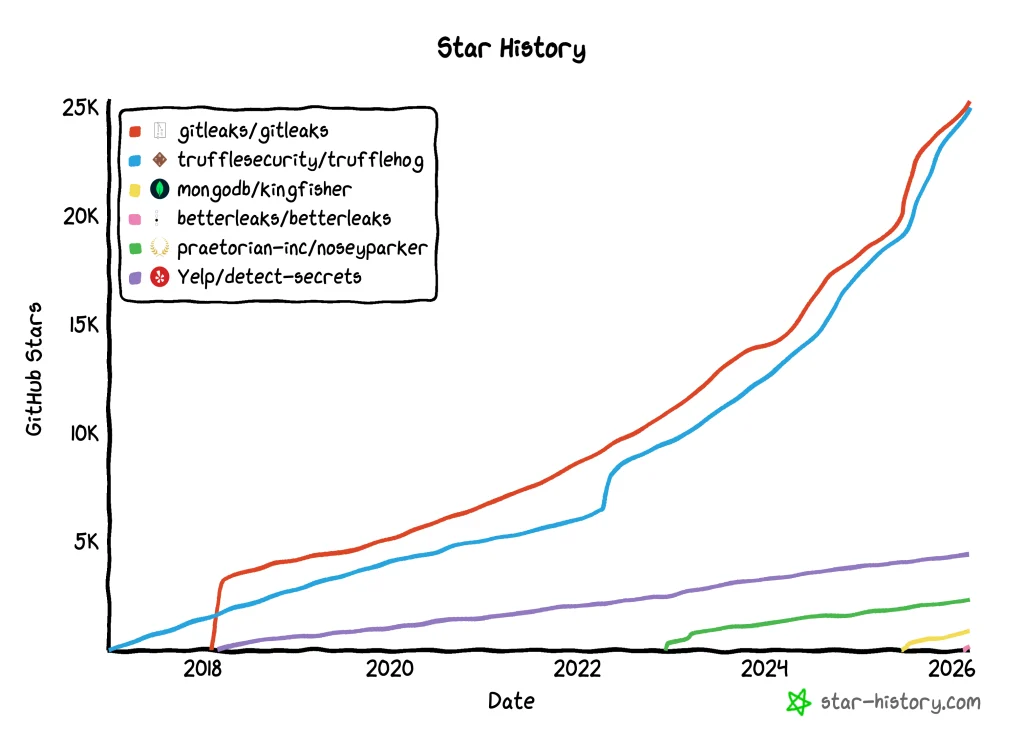
The public release of Gitleaks coincided with a growing awareness of the dangers associated with leaked credentials. The tool quickly gained traction, becoming a staple for numerous engineering teams. Its popularity is underscored by its impressive metrics on GitHub, boasting over 25,000 stars and 26 million downloads. Major technology companies, including GitLab and Red Hat, integrated Gitleaks into their internal systems and CI/CD pipelines to scan repositories for exposed secrets. Rice himself later joined GitLab as a senior software engineer, focusing on security tooling, though much of his Gitleaks development continued as a personal endeavor.
In 2023, Rice transitioned to Truffle Security, joining Ayrey. Truffle Security consolidated several prominent open-source secret-scanning projects, such as Nosey Parker, under a unified umbrella with the objective to "unite core stewardship" of these vital tools. This strategic move, however, altered the development trajectory of Gitleaks. Rice’s focus at Truffle shifted more towards TruffleHog, leading to a slowdown in Gitleaks’ development. While he continued to maintain the project, the pace of innovation was no longer what it had been, with much of the ongoing support provided outside of his regular work hours.
This shift in control and development focus was a key catalyst for the creation of Betterleaks. In the official launch announcement for Betterleaks, Rice candidly expressed his loss of comprehensive control over the Gitleaks repository and its associated name. "To be transparent, I don’t have full control over the Gitleaks repo and name anymore," Rice stated. "It sucks, but it also gives me the opportunity to start something fresh. Something… better?"
Betterleaks: A Seamless Transition and Enhanced Capabilities
Joining Aikido in early February as the Head of Secrets Scanning, Rice was tasked with a clear objective: to develop the preeminent open-source secrets scanner. Betterleaks is designed as a direct, "drop-in" replacement for Gitleaks. This means that existing command-line interfaces and configuration files from Gitleaks are expected to function seamlessly with Betterleaks, allowing teams to transition without undertaking significant reconfigurations.

A primary area of improvement in Betterleaks lies in its validation mechanism. Instead of embedding validation logic directly into the Go code, Betterleaks leverages the Common Expression Language (CEL). CEL is an open-source, high-performance, portable, and secure embedded expression language, making it an ideal choice for defining validation rules without complicating the core scanner. This approach provides security teams with significantly more flexibility in specifying what constitutes a genuine credential and what should be disregarded.
Rice is also introducing a novel approach to detecting secrets, moving beyond traditional methods that often rely on measuring the "entropy" or randomness of a string. Betterleaks employs a technique Rice refers to as token efficiency scanning, which is based on Byte-Pair Encoding (BPE) tokenization. The underlying principle is that natural language text and machine-generated credentials will break down differently when processed by a tokenizer, allowing for more nuanced identification of potential secrets.
Further enhancements are structural and performance-oriented. Betterleaks is written in pure Go, eliminating dependencies on CGO and specialized scanning engines like Hyperscan. This simplification ensures more consistent execution across diverse environments. The tool also includes default detection for credentials that have been encoded multiple times (doubly and triply encoded) and supports parallelized Git scanning for substantially faster repository analysis.
The roadmap for Betterleaks extends beyond these initial improvements. Future iterations are planned to encompass scanning a wider array of data sources beyond Git repositories and files, incorporate optional Large Language Model (LLM)-based classification utilizing anonymized data, support credential revocation where providers offer the necessary APIs, and provide detailed mapping of the potential impact of leaked credentials.
Rice’s strategic vision for Betterleaks prioritizes advancing the project’s capabilities without imposing undue burdens on existing Gitleaks users. While his primary focus is now on Betterleaks, he assures the community that Gitleaks will remain stable, with security patches and essential maintenance continuing.
"Hopefully it’s not going to cause too much of a backlash to the community — I love the Gitleaks community, and I don’t want to fracture that," Rice stated. "So if you want to continue using Gitleaks, feel free. It’s stable, and security patches and stuff like that, I’ll continue to do. But if you want the next generation of Gitleaks and the evolution, then switch to Betterleaks."
Positioned for the AI Agent Era
Unlike many open-source projects that evolve into commercial products, Betterleaks is firmly rooted in its open-source ethos. It is licensed under the MIT license, with Rice retaining ownership while Aikido acts as a sponsor. Aikido’s involvement is part of a broader strategic commitment to bolstering open-source security, which includes supporting other projects such as OpenGrep, Zen, Intel, and Safe Chain.
"Like what Aikido did with OpenGrep, we’re dedicated to providing really great open source projects for the security community," Rice explained. "A strong open source project is the backbone of a lot of the security products out there. Yes, it’s beneficial to other companies, but it’s also really beneficial to Aikido to have these stable projects."
Furthermore, Rice is not solely steering Betterleaks. Three seasoned contributors from the Gitleaks community have joined as co-maintainers: Richard Gomez, Director of Software Development at the Royal Bank of Canada; Braxton Plaxco, a Senior Information Security Analyst at Red Hat; and Ahrav Dutta, a Software Engineer at Amazon. This distributed stewardship model is intended to enhance project stability and reduce reliance on a single individual.
"Betterleaks is prime for the AI agent era… When code is generated, you can check it for secrets – and if it finds one, it’s flagged. That’s really it."
This collaborative approach reflects a forward-looking perspective on security tooling, emphasizing open development and adaptability to diverse environments, including those driven by AI. Rice noted that AI agents frequently utilize command-line tools for code navigation and analysis, and Betterleaks is being designed with this pattern in mind, enabling seamless integration into automated workflows, akin to established tools like Grep.
"Betterleaks is prime for the AI agent era," Rice concluded. "It’s really easy for AI agents to use. When code is generated, you can check it for secrets – and if it finds one, it’s flagged. That’s really it." The ultimate goal is to create a security scanner that not only identifies leaked credentials retrospectively but also actively participates in the code development process, whether that code is authored by humans or machines.