Security teams globally have invested considerable resources over the years into establishing robust identity and access controls for human users and traditional service accounts. However, a new and formidable category of digital actor has surreptitiously permeated the operational fabric of most enterprise environments, operating entirely beyond the purview of these established security frameworks. This emerging entity is the autonomous AI coding agent, exemplified by Anthropic’s Claude Code, which is now being deployed across engineering organizations at an unprecedented scale, presenting a novel and significant cybersecurity challenge.
Claude Code operates with remarkable autonomy, engaging in a wide array of actions that bypass conventional security oversight. It can read local files, execute shell commands, initiate calls to external APIs, and establish connections to third-party integrations known as MCP servers. Crucially, it performs all these actions with the full, inherited permissions of the developer who launched it, directly on that developer’s local machine. This on-device operation means that its activities occur before any network-layer security tool can detect or intervene. Consequently, Claude Code leaves no audit trail that the existing security infrastructure, designed for network traffic and server-side events, is equipped to capture, creating a critical blind spot for enterprise security and compliance.
Recognizing this profound and burgeoning threat, Beyond Identity has introduced Ceros, an innovative AI Trust Layer specifically engineered to address this gap. Ceros is designed to operate directly on the developer’s machine, in close conjunction with AI agents like Claude Code. It provides real-time visibility into agent activities, enforces granular runtime policies, and generates a cryptographically verifiable audit trail of every action the AI agent undertakes. This walkthrough delves into the intricacies of Ceros, explaining how it redefines the security posture for AI agents in the enterprise.
The Unseen Frontier: AI Agents and the Emerging Security Blind Spot
To fully appreciate the necessity of a solution like Ceros, it is imperative to understand why existing security tools are inherently incapable of addressing the unique challenges posed by autonomous AI coding agents. The vast majority of enterprise security tooling—including Security Information and Event Management (SIEM) systems, Intrusion Detection/Prevention Systems (IDS/IPS), Data Loss Prevention (DLP) solutions, and network monitors—are strategically positioned at the network edge or within API gateways. These tools are designed to observe and analyze traffic after it has left the local machine, or interactions that occur at well-defined API endpoints.
This architectural reality creates a fundamental flaw in securing AI agents. By the time a SIEM ingests an event, or a network monitor flags unusual outbound traffic, Claude Code has already executed its actions on the local device. Files have been read, shell commands have completed, and sensitive data may have already been accessed or moved. The critical window for intervention has passed, rendering post-facto detection largely reactive and often too late to prevent harm.
Compounding this problem is Claude Code’s sophisticated behavioral profile, which leverages a technique known as "living off the land." Rather than introducing its own unique binaries or processes that might trigger endpoint detection and response (EDR) alerts, Claude Code utilizes the tools and permissions already present and authorized on the developer’s machine. This includes standard operating system utilities, installed libraries, and developer-specific access tokens. Its communications often manifest as normal external model calls, blending seamlessly with legitimate network traffic, making it exceedingly difficult for traditional anomaly detection systems to differentiate between benign developer activity and potentially malicious AI agent actions.

Furthermore, Claude Code executes complex sequences of actions that are not explicitly programmed by a human, but rather dynamically generated by the underlying Large Language Model (LLM) in response to developer prompts. This non-deterministic behavior makes static rule-based security approaches largely ineffective. Most alarmingly, it operates with the full, inherited permissions of the developer who launched it. This often includes access to sensitive credentials, connections to production systems, and repositories of confidential data that developers may legitimately store or access on their local machines. The implications of an autonomous AI agent, even one intended for beneficial purposes, gaining unfettered access to such critical assets without a clear audit trail or real-time control are profound, ranging from intellectual property theft and data exfiltration to unauthorized code deployment and supply chain vulnerabilities.
The result is a glaring security gap that network-layer tools are structurally unable to close: everything Claude Code does on the local machine before any request leaves the device. This on-device operational space is precisely where Ceros establishes its presence and exerts control.
The Genesis of the Problem: A Chronology of AI Agent Adoption and Security Lag
The trajectory of AI integration into development workflows has been rapid, evolving from basic code completion tools and static analysis aids to sophisticated, autonomous agents like Claude Code. Initially, developers welcomed AI assistants for their ability to streamline repetitive tasks and provide instant suggestions, boosting productivity. However, as AI models grew in capability and gained the ability to interpret complex instructions, chain actions, and interact with the local environment, the concept of the "AI agent" emerged.
Anthropic’s Claude Code, like similar offerings from other AI providers, represents a significant leap. Launched and rapidly adopted, these agents promised to revolutionize software development by automating entire workflows, from debugging and refactoring to generating new code components and interacting with external services. The speed of this adoption, driven by immense productivity gains, outpaced the development of specialized security protocols.
Historically, enterprise security architecture has been built around known entities: human users, servers, and applications. Identity and access management (IAM) systems were designed to authenticate and authorize these entities based on defined roles and responsibilities. The security implications of an autonomous digital entity that operates with human-level permissions, makes its own decisions, and lives entirely on the endpoint were not part of the initial design considerations for these frameworks. This chronological disparity—rapid AI agent innovation preceding adaptive security measures—created the current security vacuum. Security frameworks, designed for a pre-AI agent world, naturally lagged behind this rapid innovation, leaving organizations vulnerable to risks that were unforeseen just a few years prior.
Ceros: Bridging the On-Device Security Chasm
Beyond Identity’s Ceros is specifically engineered to fill this critical security void, acting as an "AI Trust Layer" that operates symbiotically with AI agents directly on the developer’s machine. Its design prioritizes minimal disruption to developer workflows, recognizing that ease of adoption is paramount for effective enterprise-wide security.

Installation is streamlined to a mere thirty seconds, requiring just two commands in the terminal:
curl -fsSL https://agent.beyondidentity.com/install.sh | bash
ceros claudeThe first command installs the Ceros Command Line Interface (CLI). The second command launches Claude Code through the Ceros wrapper. This initiates a brief, secure enrollment process: a browser window opens, prompts for an email address, and sends a six-digit verification code. After successful verification, Claude Code starts up and functions exactly as it did before. From the developer’s perspective, the workflow remains unchanged, embodying the principle of "invisible security" – a key factor for achieving widespread adoption in fast-paced engineering environments.
For larger, organization-wide deployments, administrators can configure Ceros to automatically prompt developers for enrollment upon their initial launch of Claude Code. This automation ensures that security becomes an integrated, frictionless part of the development process, rather than an impedance.
Crucially, upon enrollment and before Claude Code generates a single token or executes any action, Ceros captures comprehensive device context in under 250 milliseconds. This includes vital security parameters such as the operating system version, kernel version, disk encryption status, Secure Boot state, and the status of endpoint protection software. It also meticulously captures the complete process ancestry of how Claude Code was invoked, including binary hashes of every executable in the chain. Furthermore, Ceros integrates with Beyond Identity’s robust platform to tie the session to a verified human identity, authenticated and cryptographically signed with a hardware-bound key. This initial, deep contextual capture provides an immutable baseline for trust and accountability.
Unveiling the Invisible: Deep Dive into Ceros’s Visibility Features
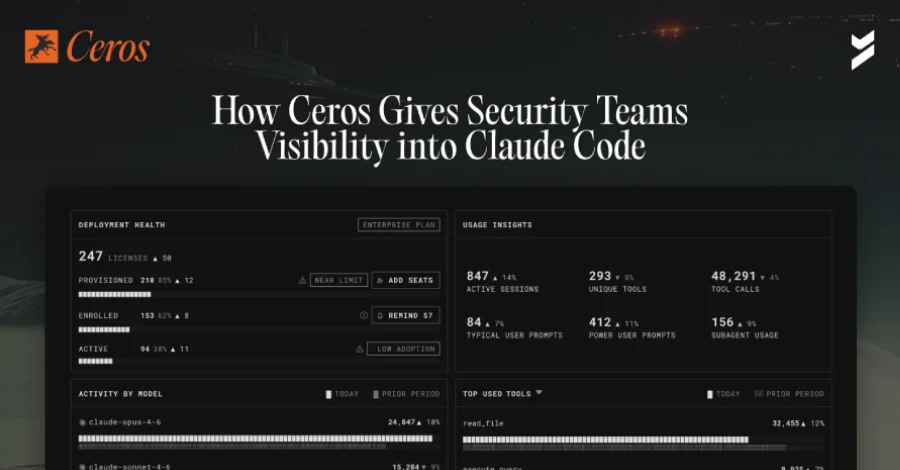
After enrolling devices and allowing Claude Code to operate normally for a few days, navigating to the Ceros admin console offers an unprecedented level of insight for security teams: a complete and granular record of every action Claude Code has performed across their environment.
The Conversations View presents a detailed log of every session between a developer and Claude Code across all enrolled devices, meticulously indexed by user, device, and timestamp. Clicking into any specific conversation reveals the full, unredacted back-and-forth dialogue between the developer and the AI agent. However, the true revelation lies in what is displayed between the prompts and responses: the "tool calls."
When a developer issues a seemingly innocuous request to Claude Code, such as "what files are in my directory?", the underlying Large Language Model (LLM) does not simply "know" the answer. Instead, it intelligently instructs the AI agent to execute a specific tool on the local machine—in this instance, the bash ls -la command. This shell command then runs directly on the developer’s device, inheriting the developer’s permissions. This seemingly casual question thus triggers real, direct execution on a real machine, with all the associated security implications. The Conversations view surfaces every single one of these tool invocations across every session, providing security teams with data they have, until now, never been able to observe.

The Tools View further dissects the operational landscape of AI agents. It features two distinct tabs. The Definitions tab enumerates every tool available to Claude Code within the enrolled environment. This includes built-in functionalities like Bash for shell access, ReadFile and WriteFile for local file system interaction, Edit for code modification, and SearchWeb for internet queries. Crucially, it also lists every MCP (Managed Code Provider) server that developers have connected to their agents. Each entry provides the tool’s full schema, which encompasses the precise instructions given to the LLM about the tool’s capabilities and how to invoke it. This provides a comprehensive map of the AI agent’s potential actions.
The Calls tab then demonstrates what was actually executed. It goes beyond mere existence to show which tools were invoked, with what specific arguments, and what output was returned. Security teams can drill down into any individual tool call to see the exact command that ran, the arguments passed to it, and the complete output received back from the system. This level of forensic detail provides unprecedented clarity into the operational behavior of AI agents, moving from theoretical capabilities to concrete actions.
Perhaps the most significant "discovery moment" for many security teams often occurs within The MCP Server view. MCP servers represent the conduits through which Claude Code connects to external tools and services, including databases, Slack, email systems, internal APIs, and even critical production infrastructure. Developers frequently add these connections with productivity in mind, often without a full appreciation of the security ramifications. Each MCP server represents a new, potentially unreviewed, data access path for the AI agent. The Ceros dashboard meticulously displays every MCP server connected to Claude Code across all enrolled devices, noting when it was first observed, which devices it appears on, and whether it has been officially approved by security. For a vast majority of organizations, the chasm between what security teams assumed was connected and what is actually connected by AI agents proves to be a significant and often alarming revelation.
Proactive Governance: Enforcing Policy and Mitigating Risk with Ceros
Visibility, while essential for identifying risks, is insufficient without the ability to govern and prevent them. The Policies section of Ceros is where the platform transitions from mere observability to active enforcement, providing a concrete framework for compliance.
Policies within Ceros are evaluated dynamically at runtime, critically, before the intended action executes. This distinction is paramount for compliance and risk mitigation: the control mechanism operates at the precise moment of the action, preventing unauthorized activity rather than merely reconstructing it after the fact.
One of the highest-impact policies most organizations implement first is MCP server allowlisting. Administrators can define a definitive list of approved MCP servers and set a default policy to block all other connections. From that moment forward, any Claude Code instance attempting to establish a connection to an unapproved MCP server will be blocked before the connection is successfully established, and the attempted action is logged for audit purposes. This proactive measure significantly reduces the attack surface presented by casually adopted external integrations.
Tool-level policies offer administrators granular control over which tools Claude Code can invoke and under what specific conditions. For example, a policy can entirely block the Bash tool for engineering teams whose agents do not require direct shell access. Conversely, it can permit file read operations strictly within a designated project directory while simultaneously blocking attempts to read sensitive paths, such as ~/.ssh/ or /etc/. The sophistication of the Ceros policy engine allows it to evaluate not only which tool is being called but also what arguments are being passed to that tool. This crucial capability differentiates between a genuinely useful security policy and mere "policy theater," ensuring that controls are meaningful and effective.

Furthermore, device posture requirements enable organizations to gate Claude Code sessions based on the security state of the developer’s machine. A policy can mandate that disk encryption must be enabled and endpoint protection software must be actively running before an AI agent session is permitted to commence. Ceros continuously reassesses device posture throughout the entire session, not just at the initial login. If, for instance, endpoint protection is disabled while Claude Code is actively in use, Ceros detects this change and acts on it based on the predefined policy, potentially terminating the session or escalating alerts.
Audit-Ready Assurance: The Cryptographic Activity Log
The Activity Log within Ceros is where the platform’s direct relevance to compliance teams becomes undeniable. Every entry in this log is not merely a record; it is a comprehensive forensic snapshot of the environment at the exact moment Claude Code was invoked and throughout its session.
A single log entry is rich with contextual data. It contains the device’s full security posture at that specific moment, the complete process ancestry illustrating every process in the chain that invoked Claude Code, binary signatures of every executable involved in that ancestry, the OS-level user identity meticulously tied to a verified human via Beyond Identity’s platform, and a detailed record of every action Claude Code took during the session.
This depth of detail is critical for compliance, particularly as auditors increasingly demand irrefutable proof of log immutability. Standard log files, which can often be edited or tampered with by administrators, fail to satisfy this stringent requirement. Ceros addresses this by cryptographically signing every entry with a hardware-bound key before it leaves the machine. This ensures that once an entry is recorded, it cannot be modified or altered after the fact, providing an undeniable chain of custody.
For compliance frameworks that mandate tamper-evident audit records, such as SOC 2’s Common Criteria 8.1 (CC8.1), FedRAMP’s Audit and Accountability (AU-9), HIPAA’s comprehensive audit control requirements, and PCI-DSS v4.0’s Requirement 10, Ceros provides the precise evidence artifact necessary to satisfy the control. When an auditor requests evidence of monitoring and access controls applied to AI agents, the answer is a simple export from the Ceros dashboard covering the full audit period. This export, cryptographically signed, complete with user attribution and granular device context on every entry, stands as incontrovertible proof of compliance.
Standardizing AI Tooling: Managed MCP Deployment
For organizations seeking to move beyond merely blocking unapproved tools and towards actively standardizing the tools available to Claude Code, Ceros offers managed MCP deployment directly from the admin console.

Administrators gain the capability to push a predefined set of approved MCP servers to every developer’s Claude Code instance from a single, centralized interface. This eliminates the need for individual developer configuration or manual setup. The approved MCP server automatically appears in the developer’s agent upon its next launch, seamlessly integrating approved tools into the workflow.
Combined with the MCP server allowlisting policy, this feature establishes a complete and robust governance model. Administrators can precisely define what tools and connections are required, what is permitted (within policy constraints), and what is definitively blocked. Developers then operate within this clearly defined, secure envelope, experiencing minimal friction while maintaining maximum productivity. This standardization is crucial for maintaining a consistent security posture across a large and diverse engineering organization.
Future Vision: The Ceros Dashboard and Holistic AI Risk Posture
Looking ahead, Beyond Identity is set to introduce The Dashboard, a forthcoming feature designed to provide a single, holistic view of the AI risk posture across the entire enrolled organization. Where the session-level views offer granular insights into what a single developer’s agent has done, The Dashboard will provide a fleet-wide perspective. It will display key metrics such as the number of devices provisioned for Ceros, those successfully enrolled, and the number of active Claude Code instances.
Crucially, The Dashboard will incorporate automatic flagging mechanisms to identify adoption gaps, indicating instances where AI agents might be running outside the Ceros enrollment path and therefore operating beyond organizational controls. This centralized overview will empower security leaders to understand, at a glance, the overall security landscape pertaining to their AI agent deployments, enabling proactive management and strategic decision-making. Organizations are encouraged to sign up to be notified when The Dashboard ships, anticipating its strategic value in enterprise AI governance.
Industry Implications and Expert Commentary
The advent of autonomous AI agents like Claude Code marks a paradigm shift in enterprise cybersecurity. Cybersecurity analysts have long warned about the evolving threat landscape, but the rapid integration of AI agents introduces an entirely new class of "insider threat," albeit one that is algorithmic rather than human. Experts like those at Gartner and Forrester have emphasized the growing need for adaptive security architectures that extend beyond traditional network perimeters to embrace endpoint and identity-centric controls, especially as AI becomes an integral part of developer workflows.
The shift from network-centric to endpoint-centric AI security is not merely a technical adjustment; it represents a fundamental re-evaluation of security strategy. New attack vectors emerge where a compromised developer workstation could lead to an AI agent being leveraged for sophisticated data exfiltration, intellectual property theft, or even direct manipulation of production systems, all while masquerading as legitimate developer activity. The need for adaptive security strategies capable of monitoring and controlling non-human actors at the point of execution is paramount. Ceros directly addresses these concerns, providing a foundational layer of trust and control that is indispensable in the age of agentic AI.

Conclusion
The security gap created by the widespread adoption of AI coding agents like Anthropic’s Claude Code is not situated at the traditional network edge, nor can it be adequately addressed by existing API gateway solutions. It resides precisely on the developer’s local machine, where the AI agent operates autonomously and often invisibly, before any conventional security tool can perceive or intercept its actions.
Ceros by Beyond Identity effectively closes this critical gap by operating where the agent lives. It captures every action an AI agent undertakes before execution, providing unparalleled visibility, enforcing granular runtime policies, and, perhaps most importantly, producing cryptographically signed evidence. This evidence is not only invaluable for security incident response but is also directly relevant and auditable for compliance teams.
For security professionals grappling with the implications of deploying Claude Code and seeking to bolster their audit posture and control mechanisms, the initial and most crucial step is achieving comprehensive visibility. Without the ability to see what these autonomous agents are truly doing, effective governance remains an impossibility. Until now, there has been no tooling capable of providing this level of insight into Claude Code’s on-device activities.
Ceros is available now, offering a free starting point for security teams to enroll a device and gain unprecedented visibility into their Claude Code activity. Further information and access can be found at beyondidentity.ai. Beyond Identity, the creator of Ceros, is SOC 2 and FedRAMP compliant, ensuring a high standard of security and reliability, and its solutions are deployable as cloud SaaS, self-hosted, or fully air-gapped on-premises, catering to diverse enterprise needs.