The recently uncovered Apple iOS exploit kit, known as Coruna, leverages a kernel exploit that is an updated iteration of the same sophisticated exploit utilized in the infamous Operation Triangulation campaign of 2023. This critical linkage, brought to light by new investigative findings from cybersecurity firm Kaspersky, underscores a worrying trend in the evolution and proliferation of advanced mobile exploitation tools. The revelation suggests a continuous development pipeline for these formidable capabilities, moving from highly targeted state-sponsored espionage to a broader, more indiscriminate deployment against a wider range of victims.
When Coruna first emerged into the public consciousness, the initial evidence was insufficient to definitively tie its intricate code to Operation Triangulation. Security researchers, while noting shared vulnerabilities, typically require more concrete proof to establish shared authorship or a direct lineage. However, Boris Larin, a principal security researcher at Kaspersky GReAT (Global Research and Analysis Team), clarified the firm’s definitive conclusions. "Coruna is not a patchwork of public exploits; it is a continuously maintained evolution of the original Operation Triangulation framework," Larin stated. He further emphasized the alarming trajectory of this framework, noting, "The inclusion of checks for recent processors like the M3 and newer iOS builds shows that the original developers have actively expanded this codebase. What began as a precision espionage tool is now deployed indiscriminately." This transformation signals a significant escalation in the accessibility and scope of highly potent mobile exploitation capabilities, posing an elevated risk to millions of unpatched iOS users globally.
The Genesis of Coruna: Discovery and Initial Campaigns
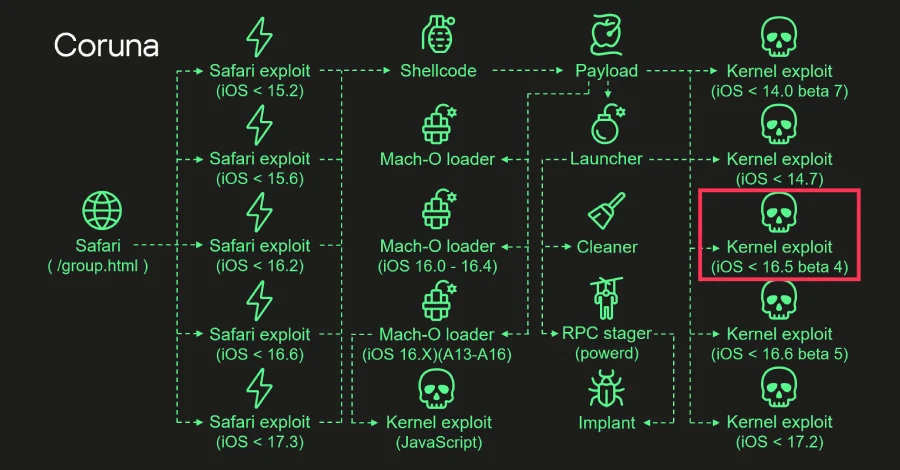
Coruna first garnered widespread attention earlier this month when it was publicly documented by security researchers from Google and iVerify. Their initial reports detailed Coruna’s capability to target a broad spectrum of Apple iPhone models, specifically those running iOS versions ranging from 13.0 up to 17.2.1. This wide compatibility immediately raised red flags, indicating a tool designed for extensive reach rather than narrow targeting.
While its public documentation is recent, the operational deployment of Coruna dates back further. Intelligence suggests that the kit was initially leveraged by a client of an unnamed surveillance company as early as the beginning of the previous year. This initial use case aligns with the typical pattern of advanced exploit kits, which often originate in the private sector for intelligence gathering or law enforcement purposes before potentially being acquired or adapted by other malicious actors.
However, Coruna’s use has since expanded dramatically beyond its perceived initial scope. It has been notably employed by a suspected Russia-aligned nation-state actor in a series of sophisticated watering hole attacks targeting entities and individuals within Ukraine. These attacks typically involve compromising legitimate websites frequented by specific targets, injecting malicious code that then attempts to exploit vulnerabilities on visitors’ devices. In parallel, Coruna has also been observed in a mass exploitation campaign. This broader operation involved a cluster of fake Chinese gambling and cryptocurrency websites, cunningly designed to lure victims and subsequently deliver a data-stealing malware known as PlasmaLoader, also identified as PLASMAGRID. This dual-pronged approach – highly targeted nation-state espionage alongside broader criminal exploitation – underscores the versatility and dangerous adaptability of the Coruna framework.
The Operation Triangulation Connection: A Technical Deep Dive
The core of Kaspersky’s latest findings lies in the direct technical link between Coruna and Operation Triangulation. Both campaigns utilize kernel exploits for two specific security vulnerabilities: CVE-2023-32434 and CVE-2023-38606. These vulnerabilities were initially exploited as zero-days within Operation Triangulation, a campaign that Kaspersky itself meticulously uncovered in 2023. Operation Triangulation was heralded as one of the most sophisticated iPhone hacks ever recorded, involving the exploitation of four distinct zero-day vulnerabilities in Apple’s mobile operating system to gain deep access to target devices.
Kaspersky’s analysis definitively indicates that the kernel exploits employed in both Triangulation and Coruna share a common authorship. This assertion is based on profound code similarities and architectural parallels. Furthermore, Coruna significantly expands upon its predecessor, incorporating an additional four kernel exploits, bringing its total to five full iOS exploit chains and an impressive arsenal of 23 individual exploits. This expanded capability not only demonstrates the continuous maintenance and evolution of the framework but also indicates a persistent effort to identify and integrate new vulnerabilities as they emerge or are discovered.

The Russian security vendor’s report details how all these exploits, both old and new, are built upon the same foundational kernel exploitation framework, sharing significant portions of common code. This shared codebase is a crucial indicator of shared development and continuous evolution rather than disparate, independently developed tools. Specific technical indicators reinforcing this connection include support for Apple’s latest processors, such as the A17, M3, M3 Pro, and M3 Max. Moreover, the code contains explicit checks for various iOS versions, including iOS 17.2 and iOS version 16.5 beta 4. The latter is particularly telling, as iOS 16.5 beta 4 was the specific build that patched all four vulnerabilities exploited as part of Operation Triangulation, suggesting the framework was designed to bypass or account for these fixes. The inclusion of checks for iOS 17.2, on the other hand, points to the integration of newer exploits designed to target more contemporary versions of Apple’s operating system.
Anatomy of a Coruna Attack
The initial entry vector for a Coruna attack typically begins with a user visiting a compromised website, often through the Safari web browser. Upon arrival, a "stager" component embedded within the website initiates a fingerprinting process. This involves rapidly identifying critical details about the user’s browser, operating system version, and device hardware. This information is then used to serve the most appropriate and effective exploit tailored specifically for the detected environment.
Once the stager successfully matches an exploit to the target device, it paves the way for the execution of a sophisticated payload. This payload is engineered to trigger the kernel exploit, which represents the deepest and most privileged level of access within the operating system. Gaining kernel-level access allows the attackers to bypass many of Apple’s robust security mechanisms and exert significant control over the device.
Kaspersky’s technical breakdown elucidates the subsequent steps: "After downloading the necessary components, the payload begins executing kernel exploits, Mach-O loaders, and the malware launcher. The payload selects an appropriate Mach-O loader based on the firmware version, CPU, and presence of the iokit-open-service permission." Mach-O loaders are critical components responsible for loading and executing Mach-O format binaries, which are the native executable file format for macOS and iOS. The selection of the correct loader ensures compatibility and effective execution of subsequent malicious stages.
The "launcher" component acts as the primary orchestrator for all post-exploitation activities. Its key responsibilities include leveraging the compromised kernel access to drop and execute the final implant – in the case of the mass exploitation campaigns, this would be the PlasmaLoader malware. Beyond payload delivery, the launcher also performs crucial forensic cleanup operations. It meticulously removes exploitation artifacts and other traces of the attack, making it significantly harder for victims or forensic investigators to detect the compromise and trace its origins. This commitment to stealth and persistence is a hallmark of highly advanced threat actors.
The Broader Landscape: Proliferation of Advanced Exploits
The evolution of Coruna from a precision espionage tool to a framework deployed indiscriminately by various actors highlights a concerning trend in the cybersecurity landscape. The increasing accessibility of sophisticated exploit kits, often developed initially by well-resourced nation-states or private surveillance firms, poses a severe challenge to global digital security. As Boris Larin aptly put it, "Originally developed for cyber-espionage purposes, this framework is now being used by cybercriminals of a broader kind, placing millions of users with unpatched devices at risk. Given its modular design and ease of reuse, we expect that other threat actors will begin incorporating it into their attacks."
This "democratization" of advanced hacking tools means that groups with fewer resources or less technical sophistication can now wield capabilities previously reserved for elite actors. This dramatically broadens the threat surface, making it more difficult for individuals and organizations to defend against attacks. It also complicates attribution, as the use of widely available (even if leaked or adapted) tools can obscure the true identity of the attackers.
The DarkSword Leak: A Parallel Concern
Further compounding these concerns is the recent development involving another potent iPhone exploit kit, DarkSword. Coincidentally, around the same time as the Coruna findings emerged, a new version of the DarkSword kit was leaked on GitHub. This public disclosure immediately raised alarm bells across the cybersecurity community, as reported by TechCrunch and CyberScoop. The leak effectively equips a much wider array of threat actors with advanced capabilities to compromise iOS devices, turning what was once an elite hacking tool into a potentially mass exploitation framework.

The implications of such leaks are profound. They lower the barrier to entry for cybercrime and state-sponsored espionage, enabling more actors to conduct highly effective attacks. The public availability of DarkSword, much like the broader deployment of Coruna, signifies a critical inflection point where advanced mobile exploitation is no longer a niche capability but a more accessible, pervasive threat. This trend places immense pressure on device manufacturers like Apple to rapidly identify and patch vulnerabilities, and on users to maintain rigorous update hygiene.
Mitigating the Risk: User and Industry Actions
In the face of such rapidly evolving and sophisticated threats, proactive measures are paramount. For individual users, the most critical defense remains consistent and timely software updates. Apple regularly releases security patches for iOS to address newly discovered vulnerabilities, including zero-days. By updating devices promptly to the latest stable iOS version (currently 17.4.1), users can ensure they are protected against known exploits like those leveraged by Coruna. Delaying updates leaves devices vulnerable to attacks that have already been mitigated by the vendor.
Beyond updates, users should exercise extreme caution when browsing the web, particularly avoiding suspicious links, unsolicited emails, and unfamiliar websites. The reliance of Coruna on watering hole attacks and compromised websites underscores the importance of a vigilant approach to online interactions. Using reputable ad-blockers and privacy-focused browser settings can also help mitigate some risks associated with malicious web content.
From an industry perspective, continuous investment in threat intelligence, vulnerability research, and collaborative information sharing is essential. Cybersecurity firms like Kaspersky play a vital role in identifying these threats, analyzing their technical intricacies, and disseminating critical intelligence to the public and to vendors. Apple, for its part, continues its robust efforts in securing the iOS ecosystem, constantly improving its security architecture and responding swiftly to reports of zero-day exploits. However, the cat-and-mouse game between attackers and defenders is perpetual, demanding relentless innovation and vigilance from all stakeholders.
Expert Commentary and Future Outlook
The findings surrounding Coruna and its ties to Operation Triangulation serve as a stark reminder of the escalating arms race in mobile security. The modular design and ease of reuse identified by Kaspersky’s Boris Larin suggest that similar frameworks, or components thereof, will likely be integrated into future attacks by a diverse range of malicious actors. This indicates a future where sophisticated mobile exploitation will not be an anomaly but a more common tactic.
The convergence of nation-state capabilities and cybercriminal methodologies, as exemplified by Coruna’s dual deployment, blurs the lines of attribution and defense. It demands a holistic security strategy that accounts for both highly targeted, state-level threats and broad, financially motivated criminal campaigns. Cybersecurity professionals anticipate an increased focus on proactive threat hunting, behavioral analysis to detect post-exploitation activities, and robust endpoint detection and response (EDR) solutions for mobile devices.
Conclusion
The confirmation that the Coruna iOS exploit kit is an evolved form of the Operation Triangulation framework marks a significant and troubling development in mobile cybersecurity. It highlights a continuous, well-resourced effort by sophisticated actors to maintain and enhance advanced exploitation capabilities for Apple devices. The shift from precision espionage to more indiscriminate deployment, coupled with the parallel concern of tools like DarkSword being leaked, paints a grim picture of a future where advanced mobile exploits are increasingly accessible and prevalent. For users, the message is clear: regular software updates are not merely a convenience but a critical line of defense. For the cybersecurity community and device manufacturers, the challenge is to stay ahead of an ever-evolving threat landscape, requiring continuous innovation, collaboration, and rapid response to protect the digital lives of millions.