A significant escalation in the GlassWorm cyber campaign has been identified by cybersecurity researchers, revealing a highly evolved multi-stage framework designed for extensive data theft and the deployment of a potent remote access trojan (RAT). This latest iteration employs a malicious Google Chrome extension, cunningly disguised as an "offline" version of Google Docs, to facilitate its illicit operations. The findings underscore a growing sophistication in threat actor tactics, particularly concerning software supply chain compromises and the exploitation of decentralized technologies for command-and-control infrastructure.
According to a detailed report published last week by Aikido security researcher Ilyas Makari, the advanced GlassWorm payload is capable of logging keystrokes, dumping sensitive cookies and session tokens, capturing screenshots, and executing commands received from a covert command-and-control (C2) server. Notably, this C2 communication mechanism leverages Solana blockchain memo fields, a novel technique designed to enhance stealth and resilience against traditional detection methods. This represents a critical evolution for a campaign that has consistently demonstrated adaptability and a persistent threat posture.
Understanding the GlassWorm Campaign: A History of Supply Chain Exploits
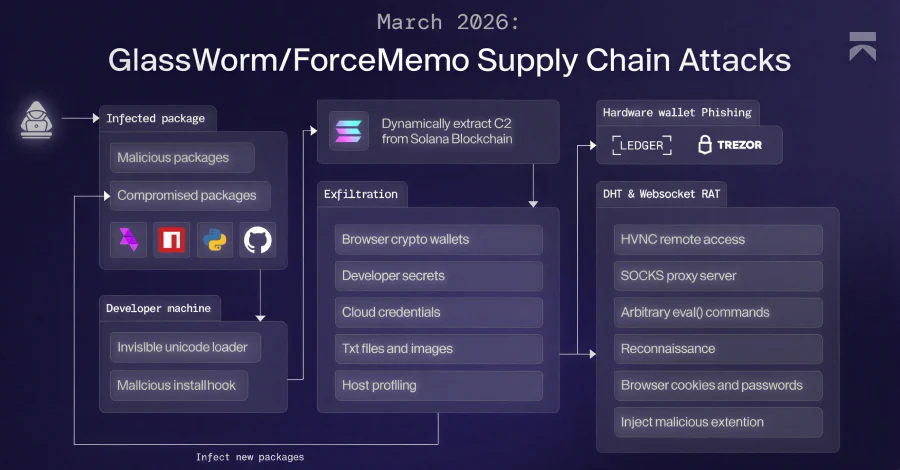
The moniker "GlassWorm" has been assigned to a persistent and evolving cyber campaign characterized by its initial foothold through the exploitation of popular developer ecosystems. Historically, GlassWorm operators have infiltrated systems by publishing rogue packages across widely used platforms such as npm, PyPI, GitHub, and the Open VSX marketplace. This method, known as a software supply chain attack, capitalizes on the implicit trust developers place in open-source repositories and development tools. Beyond merely introducing malicious packages, the GlassWorm threat actors have also been observed compromising the accounts of legitimate project maintainers, enabling them to push poisoned updates directly into trusted software, further expanding their reach and impact.
The choice of supply chain attacks as an initial vector is strategic. Modern software development heavily relies on a vast network of third-party libraries and components. A single compromised package can propagate malicious code across countless downstream projects and user systems, creating a wide attack surface. The increasing automation in development workflows, often involving automated dependency fetching and integration, inadvertently amplifies the risk, allowing malicious code to spread rapidly and silently. Cybersecurity reports over the past few years have consistently highlighted a dramatic increase in supply chain attacks, with some estimates suggesting a several-fold rise in incidents, making them one of the most critical threats facing the software industry.
Evasive Maneuvers and Multi-Stage Execution
The GlassWorm campaign exhibits remarkable operational security and evasion tactics. A key characteristic is its geographical filtering: the attacks are meticulously crafted to avoid infecting systems configured with a Russian locale. This geo-fencing technique is common among certain threat groups, often to avoid drawing attention from law enforcement in specific regions or to align with geopolitical objectives.
Once past initial checks, the malware employs sophisticated dead-drop resolvers for its command-and-control infrastructure. The first stage of the attack uses Solana blockchain transactions, specifically the memo field within these transactions, to fetch the primary C2 server address (identified as "45.32.150[.]251"). The Solana blockchain, a high-performance decentralized platform, offers an attractive medium for threat actors due to its distributed nature, which complicates tracing and takedown efforts, and the ability to embed small pieces of data (memos) within transactions without raising immediate suspicion from network monitoring tools designed for traditional C2 traffic. This initial C2 then serves to download operating system-specific payloads, tailoring the attack to the victim’s environment.
The second stage of the payload is a robust data-theft framework. This component is equipped with extensive capabilities for credential harvesting, systematic cryptocurrency wallet exfiltration, and detailed system profiling. All collected sensitive data is then meticulously compressed into a ZIP archive before being exfiltrated to an external server, identified as "217.69.3[.]152/wall." This data-theft framework also plays a crucial role in the attack chain by dynamically retrieving and launching the subsequent, and arguably most dangerous, final payloads.

Targeting Digital Assets: Hardware Wallet Phishing
Following the initial data transmission, the GlassWorm attack chain fetches two additional critical components. One of these is a specialized .NET binary designed specifically for hardware wallet phishing. This binary leverages the Windows Management Instrumentation (WMI) infrastructure to vigilantly detect USB device connections. Upon sensing a recognized hardware wallet—specifically Ledger or Trezor devices—being plugged into the system, it immediately triggers a sophisticated phishing window.
The phishing interfaces are crafted with alarming accuracy. For Ledger users, the malware displays a deceptive "fake configuration error" message, promptly followed by 24 numbered input fields, ostensibly for the user’s recovery phrase. Similarly, Trezor users encounter a fraudulent "Firmware validation failed, initiating emergency reboot" message, also accompanied by the identical 24-word input layout. Both deceptive windows prominently feature a "RESTORE WALLET" button, urging the victim to input their critical recovery phrase.
The malware doesn’t stop at merely presenting a fake interface. It actively interferes with legitimate processes, killing any authentic Ledger Live processes running on the Windows host to prevent users from interacting with the genuine application. Furthermore, it exhibits persistence by re-displaying the phishing window if the victim attempts to close it, making it difficult to escape the trap. The ultimate objective of this elaborate phishing scheme is to capture the victim’s wallet recovery phrase, which provides full access to their cryptocurrency funds, and transmit it to the attacker-controlled IP address "45.150.34[.]158." The implications of such an attack are severe, leading to irreversible financial losses and a significant erosion of trust in hardware security measures, which are often considered the gold standard for cryptocurrency protection. The cryptocurrency industry faces billions in losses annually due to scams, phishing, and malware, making this type of targeted attack particularly concerning.
The Omnipresent Eye: Websocket-Based JavaScript RAT and Malicious Chrome Extension
The second additional component fetched in the attack chain is a highly capable Websocket-based JavaScript Remote Access Trojan (RAT). This RAT is designed for extensive web browser data siphoning and the execution of arbitrary code on the compromised system. Its command-and-control details are initially retrieved using a Distributed Hash Table (DHT), a peer-to-peer network technology that offers redundancy and resilience. In the event that the DHT mechanism fails to return a value, the malware gracefully switches to its Solana-based dead drop resolver as a fallback, showcasing its multi-layered approach to C2 communication.
Once communication with the C2 server is established (fetched from "45.32.150[.]251" using a public Google Calendar event URL as another dead drop resolver, another clever evasion tactic), the RAT can issue a wide array of commands on the compromised system. These capabilities typically include, but are not limited to, file system manipulation (uploading, downloading, deleting files), process management (listing, killing, launching processes), gathering system information, executing arbitrary shell commands, and maintaining persistence on the infected machine.
Perhaps the most insidious aspect of this RAT is its ability to force-install a Google Chrome extension, deceptively named "Google Docs Offline," on both Windows and macOS systems. This malicious extension then becomes a direct conduit to a C2 server, receiving commands from the operator. Its capabilities are alarmingly comprehensive, allowing it to:
- Gather cookies and localStorage data, crucial for session hijacking.
- Extract the full Document Object Model (DOM) tree of the active browser tab, providing a complete structural and content snapshot of visited web pages.
- Exfiltrate bookmarks, revealing user interests and potential further targets.
- Capture screenshots, offering visual insights into user activity.
- Log keystrokes, capturing sensitive input like passwords and personal information.
- Steal clipboard content, which often contains copied sensitive data.
- Collect up to 5,000 browser history entries, mapping out user browsing habits.
- List all installed extensions, identifying potential security tools or other vulnerable software.
Beyond general surveillance, the extension performs targeted session monitoring. Researchers noted that it pulls "monitored site rules" from /api/get-url-for-watch and comes pre-configured to target Bybit (.bybit.com), a prominent cryptocurrency exchange. It specifically watches for secure-token and deviceid cookies associated with Bybit sessions. Upon detecting these specific cookies, it fires an auth-detected webhook to /api/webhook/auth-detected, containing the exfiltrated cookie material and relevant page metadata. Furthermore, the C2 server has the capability to supply redirection rules, forcing active browser tabs to attacker-controlled URLs, potentially leading to further phishing or drive-by download attacks. The choice to masquerade as "Google Docs Offline" exploits user familiarity and trust in widely used, legitimate software, making detection by unsuspecting users extremely difficult.
Expanding Horizons: GlassWorm Targets AI Development Ecosystems

The discovery of this advanced multi-stage framework coincides with yet another significant shift in GlassWorm’s tactical approach: its expansion into new development ecosystems. Threat actors have recently been observed publishing npm packages that impersonate the WaterCrawl Model Context Protocol (MCP) server, specifically the package "@iflow-mcp/watercrawl-watercrawl-mcp," to distribute their malicious payloads.
Koi security researcher Lotan Sery highlighted the gravity of this development, stating, "This is GlassWorm’s first confirmed move into the MCP ecosystem. And given how fast AI-assisted development is growing – and how much trust MCP servers are given by design – this won’t be the last." This infiltration into the MCP ecosystem signals a calculated move to target the rapidly expanding field of artificial intelligence and machine learning development, where complex models and proprietary data are frequently exchanged, making them high-value targets. The inherent trust placed in components within these cutting-edge development environments presents a fertile ground for sophisticated supply chain attacks.
Recommendations and Mitigation Strategies
In light of the persistent and evolving threat posed by GlassWorm, cybersecurity experts and platform providers are reiterating urgent advice for developers and general users alike. Developers are strongly cautioned to exercise extreme vigilance when installing Open VSX extensions, npm packages, and MCP servers. Critical steps include:
- Verify Publisher Names: Always cross-reference the publisher’s identity with official documentation or known reputable sources.
- Scrutinize Package Histories: Examine the package’s version history, commit logs, and contributor list for any suspicious anomalies or recent changes.
- Avoid Blind Trust: Never blindly trust download counts or popularity metrics as sole indicators of legitimacy, as these can be artificially inflated by threat actors.
- Implement Strict Access Controls: Use multi-factor authentication (MFA) for all developer accounts and repositories.
- Regular Security Audits: Incorporate automated security scanning and manual audits into development pipelines to detect malicious code.
Polish cybersecurity company AFINE has proactively responded to this threat by publishing an open-source Python tool named glassworm-hunter. This tool is designed to scan developer systems for payloads associated with the GlassWorm campaign. Researchers Paweł Woyke and Sławomir Zakrzewski emphasized its privacy-preserving design: "Glassworm-hunter makes zero network requests during scanning. No telemetry. No phone-home. No automatic update checks. It reads local files only. Glassworm-hunter update is the only command that touches the network. It fetches the latest IoC database from our GitHub and saves it locally." This tool provides a valuable, trustworthy resource for developers seeking to proactively identify and mitigate GlassWorm infections on their systems.
For general users, particularly those involved with cryptocurrency or sensitive online activities, the following recommendations are crucial:
- Browser Extension Vigilance: Be highly cautious about installing browser extensions. Only install those from trusted sources, and regularly review installed extensions for any unfamiliar or suspicious additions.
- Hardware Wallet Security: Never input your recovery phrase into any digital interface, especially if prompted unexpectedly. Hardware wallet recovery phrases should only be used directly on the device itself during a legitimate recovery process, and never typed into a computer.
- Software Updates: Keep operating systems, web browsers, and all installed software updated to patch known vulnerabilities.
- Phishing Awareness: Remain skeptical of unsolicited communications, unexpected prompts, and unusual behavior from applications or websites. Always verify the legitimacy of requests for sensitive information.
- Multi-Factor Authentication (MFA): Enable MFA on all online accounts, especially for cryptocurrency exchanges and financial services.
Broader Implications for Cybersecurity
The evolution of the GlassWorm campaign serves as a stark reminder of the dynamic and relentless nature of cyber threats. Its sophistication—from leveraging decentralized blockchains for C2 and Google Calendar as dead drops, to highly targeted hardware wallet phishing and comprehensive browser data exfiltration—highlights a trend where threat actors are continuously innovating to bypass conventional security measures. The expansion into AI development ecosystems further underscores the need for robust security frameworks across all technological frontiers. The erosion of trust in open-source components and widely used developer platforms presents a significant challenge for the entire digital ecosystem, necessitating a collaborative effort from developers, security researchers, and platform providers to build more resilient and trustworthy digital infrastructure. The fight against campaigns like GlassWorm demands not only reactive defense but also proactive measures and continuous education to safeguard digital assets and data in an increasingly interconnected world.