The long-standing ability for Android users to install applications from sources other than the official Google Play Store, a practice known as "sideloading," has been a defining characteristic distinguishing the operating system from its competitor, iOS. This inherent flexibility, however, is now at the center of a significant shift in Google’s policy, with the tech giant moving to implement more stringent controls over the installation of Android Package Kit (APK) files. While Google frames these measures as crucial for user safety and combating cyber threats, the move has ignited a fierce debate within the Android community, drawing criticism from developers, alternative app store operators, and privacy advocates who view it as an erosion of user freedom and a direct challenge to the ecosystem of independent app distribution.
The Shifting Landscape of Android App Distribution
Since its inception, Android has championed an open philosophy, allowing users and developers unparalleled freedom compared to the more curated environment of Apple’s ecosystem. This openness manifested most prominently in the ability to sideload APKs. These compressed archive files, containing an application’s code and resources, can be freely distributed across the internet, outside the confines of the Google Play Store. This parallel distribution channel has fostered a vibrant ecosystem of alternative app stores and repositories, including well-known platforms like APKMirror, UpToDown, GitHub, and F-Droid.
For users, sideloading offers a multitude of advantages. It provides access to applications not available on Google Play due to regional restrictions, policy violations (often for legitimate reasons not involving malware), or simply developer preference. It enables the installation of older versions of apps, which can be critical for compatibility with legacy devices or for users who prefer specific functionalities removed in newer updates. Furthermore, it is the primary method for installing Free and Open Source Software (FOSS) apps, many of which deliberately choose not to be listed on Google Play due to philosophical objections to proprietary terms or data collection practices. For developers, especially independent and niche creators, sideloading offers a pathway to distribute their applications without being subject to Google Play’s stringent review processes, often substantial revenue share (historically 30%, though now tiered), or specific content policies. This freedom has been instrumental in the growth of Android’s diverse app landscape, allowing for innovation that might otherwise be stifled.
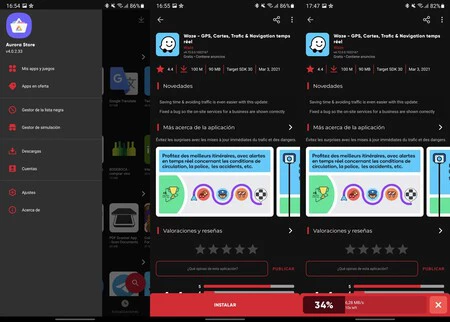
A prime example of an Android device ecosystem functioning without Google Play is Huawei’s. Following U.S. sanctions, Huawei was barred from using Google Mobile Services (GMS), including the Play Store. This forced the company to develop its own app distribution platform, AppGallery, and rely heavily on users’ ability to sideload apps or utilize third-party stores like Aurora Store, which can access applications directly from Google’s servers without requiring a Google account. This scenario clearly demonstrated that a robust Android experience can exist independently of Google Play, underscoring the importance of sideloading as a foundational aspect of Android’s architecture.
Google’s Stated Rationale: Combating Malware and Enhancing User Safety
Google’s primary justification for these impending restrictions is user security. The company argues that while sideloading offers freedom, it has increasingly become a vector for malware, phishing scams, and other cyber threats. Unverified APKs, downloaded from untrusted sources, can harbor malicious code designed to steal personal data, compromise financial accounts, deploy ransomware, or even take control of a device. The convenience of obtaining an app quickly can often lead users, particularly those less technically savvy, to inadvertently install harmful software.
Cybersecurity reports consistently highlight the prevalence of Android malware. While Google Play Protect and other internal vetting mechanisms have improved the security of the official store, malicious applications still occasionally slip through. Outside the Play Store, the risk escalates significantly. For instance, reports from cybersecurity firms like Check Point and Kaspersky frequently detail sophisticated malware campaigns that leverage sideloading to infect devices, often disguised as popular apps or utilities. These threats can range from adware that bombards users with unwanted ads to highly invasive spyware capable of siphoning off banking credentials, private messages, and location data. Google’s concern is that as the Android user base expands globally, so too does the potential for exploitation, making robust security measures increasingly critical.
To combat these risks, Google is reportedly implementing changes such as requiring developers to identify themselves and introducing a potential 24-hour waiting period for the installation of sideloaded APKs. The developer identification requirement aims to create an accountability trail, making it harder for malicious actors to operate anonymously. The 24-hour delay, while potentially frustrating for users, is envisioned as a "cooling-off" period, during which Google could theoretically perform additional background checks on the APK or allow users time to reconsider their installation, potentially aided by security warnings. This dual approach is designed to introduce friction into the sideloading process, thereby deterring both the distribution and casual installation of potentially harmful apps.
Chronology of Restrictions and Policy Changes
The evolution of sideloading on Android has been a gradual tightening of controls rather than an abrupt shift. In the early versions of Android, installing apps from "Unknown sources" was a relatively straightforward process, requiring only a single global toggle in settings.
- Pre-Android 8.0 (Oreo): A single "Unknown sources" toggle allowed all apps to install APKs. This was a broad permission that, once granted, applied system-wide, posing a significant security risk if a malicious app gained control.
- Android 8.0 (Oreo, 2017): Google introduced "Install unknown apps" permissions, making it more granular. Instead of a global toggle, users had to grant permission to specific apps (e.g., Chrome, a file manager) to install APKs. This was a crucial step in limiting the attack surface.
- Android 10 (2019) and beyond: Further refinements in scoped storage and runtime permissions continued to restrict how apps could access system resources and other apps’ data, indirectly making it harder for malicious sideloaded apps to cause widespread damage.
- Recent Developments (Late 2023 / Early 2024): The current discussions and leaks point to more direct measures targeting sideloading itself. Reports indicate that Google is exploring mechanisms for developer verification and the aforementioned 24-hour waiting period for installing APKs from non-Play Store sources. These proposed changes are not merely about permissions but about introducing systematic friction and accountability into the sideloading workflow, suggesting a more fundamental re-evaluation of Android’s openness. While specific Android version numbers for full implementation are not yet confirmed, these changes are expected to roll out in upcoming iterations of the operating system.
These incremental changes reflect Google’s ongoing effort to balance the platform’s foundational openness with the imperative to protect its vast user base from increasingly sophisticated cyber threats. Each step has been met with varying degrees of community reaction, but the latest proposals represent the most significant potential shift yet.
Reactions from the Ecosystem: Developers, Alternative Stores, and Privacy Advocates
The announcement of Google’s intensified restrictions has been met with a wave of concern and criticism from various stakeholders within the Android ecosystem. F-Droid, a prominent repository for FOSS Android applications, has already voiced strong complaints, citing concerns about the viability of its model if these restrictions are fully implemented. F-Droid, by its very nature, relies entirely on sideloading, as it deliberately avoids Google Play. Increased friction, such as developer identification and waiting periods, directly undermines its accessibility and user experience.
Other alternative app stores like APKMirror and UpToDown, while often mirroring apps found on Google Play, also serve as crucial archives for older app versions or geo-restricted content. They stand to lose significant user engagement if sideloading becomes cumbersome. These platforms thrive on ease of access; any added complexity could drive users back to the default Google Play Store, further consolidating its market dominance.
The developer community, particularly independent developers and those working on niche or experimental apps, views these changes with apprehension. The requirement for developer identification, while ostensibly for security, could create an additional barrier to entry, especially for those who prefer to remain pseudonymous or operate outside formal corporate structures. It could also lead to increased administrative burdens, potentially stifling the very innovation that the open Android ecosystem has historically fostered. Many developers feel that Google is attacking the very community that helped build Android into the world’s most popular mobile operating system.
Privacy advocates are also expressing concerns. They argue that by making sideloading more difficult, Google is effectively pushing users towards its centralized app store, thereby increasing its control over app distribution and potentially user data. This move could limit user choice and autonomy, moving Android closer to the "walled garden" model of iOS, which many Android users explicitly chose to avoid. The argument is that while security is important, it should not come at the cost of fundamental user freedom and the ability to choose how and where they obtain their software. The tension lies in whether these restrictions genuinely protect users or primarily serve to strengthen Google’s monopolistic position in the app market.
The Broader Implications: Competition, Innovation, and Regulatory Scrutiny
The implications of Google’s enhanced APK restrictions extend far beyond individual user experience; they touch upon fundamental issues of market competition, technological innovation, and regulatory oversight.
- Impact on Market Competition: The most significant implication is the reinforcement of Google Play’s already overwhelming dominance in the Android app distribution market. By making it harder to install apps from alternative sources, Google effectively diminishes the competitive viability of these platforms. This could reduce incentives for Google to innovate or lower its app store fees, as developers and users have fewer viable alternatives. This move could be seen as an anti-competitive practice, further solidifying Google’s control over the Android app economy.
- Antitrust Context: This policy shift occurs amidst a global wave of antitrust scrutiny against major tech companies, including Google, regarding their app store practices. Legislations like the European Union’s Digital Markets Act (DMA) specifically aim to curb the power of "gatekeepers" and promote fair competition, including mandating the allowance of third-party app stores and sideloading. Similar antitrust lawsuits and investigations are ongoing in the United States and other jurisdictions. Google’s move to restrict sideloading, even if justified by security, could be interpreted by regulators as a strategic maneuver to circumvent these growing anti-monopoly pressures, potentially attracting further legal challenges.
- Impact on Innovation: While Google aims to protect users, some argue that these restrictions could inadvertently stifle innovation. Many groundbreaking apps and experimental features first emerge outside official channels, where developers have more freedom to iterate and push boundaries without strict oversight. If sideloading becomes too burdensome, smaller developers or those with unconventional ideas might face higher hurdles, potentially limiting the diversity and creativity within the Android app ecosystem.
- User Experience and Choice: For advanced Android users who value customization and control, these changes represent a significant loss of freedom. The added friction of developer verification and waiting periods could be seen as an unnecessary barrier. For less tech-savvy users, while ostensibly providing more security, it might also remove a crucial avenue for accessing certain niche or regionally unavailable applications, inadvertently limiting their choices.
- The "Walled Garden" Debate: This move reignites the long-standing debate about the "walled garden" approach to mobile ecosystems. Android has historically prided itself on being an open platform, contrasting sharply with Apple’s tightly controlled iOS environment. Google’s increasing restrictions suggest a gradual but discernible shift towards a more curated and controlled experience, blurring the lines between the two dominant mobile operating systems. This philosophical change could alienate a segment of the Android user base that explicitly chose the platform for its openness.
Technical Mechanisms and Implementation Details
The precise technical implementation of these new restrictions remains to be fully detailed by Google. However, based on reports and industry practices, several mechanisms are likely candidates:
- Developer Verification: This could involve requiring developers to register and verify their identity through a system similar to Google Play Console accounts, potentially involving real-world identification (e.g., government ID, business registration). This would create a traceable link between an APK and its creator.
- APK Signature Verification and Attestation: Android already uses cryptographic signatures to verify the authenticity of APKs. Google could enhance this by requiring specific attestations or even a form of notarization for sideloaded apps, perhaps by submitting the APK for an automated security scan before installation.
- System-Level Delays: The proposed 24-hour delay would likely be enforced at the operating system level. When a user attempts to install a sideloaded APK, the system could queue the installation and prevent immediate execution, perhaps displaying a countdown timer or a pending status in the notification shade. This delay could also be used to trigger background security checks.
- Enhanced Warnings and User Education: Alongside technical barriers, Google is likely to intensify in-app warnings and user education efforts, explicitly cautioning users about the risks of sideloading and guiding them towards safer practices.
While these measures are designed to enhance security, they also present potential challenges for Google. Malicious actors are constantly evolving their tactics, and determined individuals will likely seek workarounds. The effectiveness of these restrictions will depend on Google’s ability to maintain a robust and adaptable security framework without alienating its core user base or drawing further regulatory ire.
Conclusion and Outlook
Google’s impending restrictions on APK sideloading represent a critical juncture for the Android ecosystem. The move underscores the inherent tension between maintaining an open platform and ensuring robust user security in an increasingly complex threat landscape. While Google’s stated aim of protecting users from malware is legitimate and necessary, the chosen methods raise serious questions about user freedom, market competition, and the future of independent app development on Android.
The debate is multifaceted: on one side, the undeniable need for stronger security measures to combat cybercrime and protect less tech-savvy users; on the other, the foundational principle of Android’s openness, which has fostered innovation and user choice. As Android continues its trajectory, its path will be closely watched by regulators, developers, and users alike, all eager to see how Google navigates this delicate balance. The ultimate outcome will shape not only the future of Android but also the broader landscape of mobile computing, influencing how users interact with their devices and how developers bring their creations to the world. The era of largely unrestricted sideloading appears to be drawing to a close, ushering in a new chapter for Android where security takes a more prominent, and perhaps more restrictive, role.