As the United States approaches its annual tax deadline, Microsoft has issued a critical warning regarding a surge in sophisticated cyber campaigns designed to exploit the time-sensitive nature and inherent trust associated with tax-related communications. These fresh campaigns are leveraging the urgency of the tax season to harvest sensitive credentials and deploy malicious software, posing a significant threat to both individual taxpayers and financial professionals.
The latest wave of email-based attacks meticulously crafts phishing messages that masquerade as legitimate communications from tax authorities or related services. Common lures include deceptive refund notices, urgent requests for payroll forms, crucial filing reminders, and seemingly authentic inquiries from tax professionals. The primary objective behind these elaborate deceptions is to trick recipients into interacting with malicious attachments, scanning embedded QR codes, or clicking on suspicious links, thereby initiating a compromise chain.
The Annual Influx of Tax Season Cyber Threats
The period leading up to the U.S. tax deadline consistently marks a peak for cybercriminal activity. The confluence of high-stakes financial transactions, a deluge of legitimate tax-related correspondence, and the inherent pressure to comply with filing requirements creates a fertile ground for exploitation. Attackers capitalize on users’ heightened state of vigilance and their expectation of receiving official communications regarding their taxes. This annual phenomenon highlights a recurring pattern where seasonal events with significant personal or financial implications become prime targets for cybercriminals seeking to capitalize on human psychology and operational urgency. The Internal Revenue Service (IRS) itself has for years issued perennial warnings about a variety of tax scams, from phone calls demanding immediate payment to phishing emails seeking personal data, underscoring the persistent nature of this threat landscape.
According to a report published last week by the Microsoft Threat Intelligence and Microsoft Defender Security Research teams, these campaigns are strategically diversified in their targeting. While many efforts are directed at individuals with the aim of personal and financial data theft, a substantial portion specifically targets accountants, financial advisors, and other professionals who routinely handle sensitive financial documents, possess access to critical financial data, and are accustomed to a high volume of tax-related emails during this intense period. This dual targeting strategy maximizes the potential for impact, as compromising a professional can yield access to a multitude of client data, creating a ripple effect of potential victims.
Sophisticated Lures and Multifaceted Attack Vectors
The sophistication of these campaigns extends beyond mere impersonation. Attackers are employing a variety of techniques to ensure the success of their nefarious operations. Some campaigns redirect unsuspecting users to meticulously crafted phishing pages, often designed and deployed through "Phishing-as-a-service" (PhaaS) platforms. These platforms provide cybercriminals with ready-made toolkits and infrastructure, significantly lowering the technical barrier to entry for launching large-scale phishing operations. PhaaS offerings frequently include customizable templates, automated credential harvesting, and even evasion techniques to bypass basic security measures, making it easier for even less-skilled actors to execute sophisticated attacks.
Beyond credential harvesting, a more insidious outcome of these campaigns is the deployment of legitimate remote monitoring and management (RMM) tools. Software such as ConnectWise ScreenConnect, Datto, and SimpleHelp, typically used by IT departments for legitimate system maintenance and support, are being weaponized by attackers. Once deployed, these RMM tools grant the attackers persistent, unauthorized access to compromised devices. This access enables them to perform a wide range of malicious activities, including extensive data exfiltration, further credential harvesting from the compromised network, lateral movement within an organization’s infrastructure, and the deployment of additional malware, including ransomware, at a later stage. The use of legitimate tools makes detection more challenging, as their activity might blend in with normal network traffic, often bypassing traditional security alerts.

The February 2026 IRS Impersonation Campaign: A Case Study in Scale
A particularly notable large-scale phishing campaign was observed on February 10, 2026, which underscored the breadth and impact of these tax-related threats. This single campaign affected over 29,000 users across 10,000 distinct organizations, demonstrating a formidable reach. Geographically, approximately 95% of the targets were located within the United States, aligning perfectly with the U.S. tax season theme. The attack strategically focused on industries with a high concentration of sensitive financial data and a propensity for tax-related communications, including financial services (accounting for 19% of targets), technology and software companies (18%), and retail and consumer goods enterprises (15%).
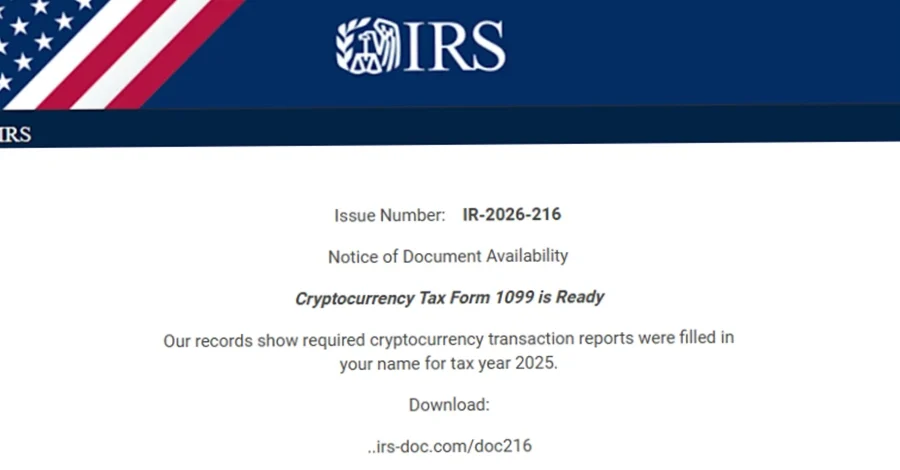
The emails in this campaign masterfully impersonated the IRS, employing a highly effective social engineering tactic. They falsely claimed that "potentially irregular tax returns" had been filed under the recipient’s Electronic Filing Identification Number (EFIN), a unique nine-digit number assigned by the IRS to authorized e-file providers. This specific detail created an immediate sense of alarm and urgency, compelling recipients to take action. To review these fabricated "returns," users were instructed to download a purportedly legitimate "IRS Transcript Viewer."
The technical execution of this campaign was equally sophisticated. The malicious emails were distributed via Amazon Simple Email Service (SES), a legitimate cloud-based email sending service, which helped them evade basic spam filters and lend an air of legitimacy to the sender. Upon clicking the prominent "Download IRS Transcript View 5.1" button embedded within the emails, users were redirected to a domain named smartvault[.]im. This domain was meticulously crafted to impersonate SmartVault, a well-known and trusted document management and sharing platform widely used by tax professionals and businesses. The use of a domain so closely mimicking a legitimate service further enhanced the credibility of the scam.
To further bolster their evasion capabilities, the phishing site leveraged Cloudflare, a legitimate web infrastructure and security company, to deflect bots and automated security scanners. This sophisticated technique ensured that only human users, who would then be more susceptible to the social engineering tactics, were served the main payload. The payload itself was a maliciously packaged version of ScreenConnect, an RMM tool. Once executed, this compromised ScreenConnect instance granted the attackers comprehensive remote access to the victim’s systems. This unfettered access facilitated extensive data theft, systematic credential harvesting from the compromised device and network, and enabled further post-exploitation activities, potentially including the deployment of ransomware or other advanced persistent threats.
The Alarming Rise of Remote Monitoring and Management (RMM) Tool Abuse
The weaponization of legitimate RMM tools is not an isolated incident but part of a broader, concerning trend in the cybersecurity landscape. A recent report published by Huntress highlighted an alarming 277% year-over-year surge in the abuse of RMM tools by threat actors. This dramatic increase underscores a significant shift in attacker methodologies, moving away from overtly malicious custom malware towards repurposing trusted, everyday software.
Elastic Security Labs researchers Daniel Stepanic and Salim Bitam have articulated the primary reason for this trend: "As these tools are used by legitimate IT departments, they are typically overlooked and considered ‘trusted’ in most corporate environments." This inherent trust allows RMM tools to often bypass traditional security controls and fly under the radar of detection systems that are primarily configured to flag known malicious executables. Attackers exploit this blind spot, transforming legitimate administrative access into covert channels for illicit operations. Their recommendation is clear: "Organizations must stay vigilant, auditing their environments for unauthorized RMM usage." This calls for a proactive approach, where IT teams not only monitor for unusual activity but also actively scrutinize the deployment and usage patterns of RMM software, even if it is considered part of the approved software stack.
Expert Perspectives and Official Warnings

Cybersecurity experts uniformly agree that the tax season represents a critical period for heightened vigilance. Dr. Anya Sharma, a lead researcher in cyber threat intelligence at GlobalSec Institute, commented, "The tax season is a predictable goldmine for cybercriminals because it combines high stakes with a predictable surge in digital communication. The sophistication we’re seeing, particularly with the weaponization of legitimate RMM tools and the use of PhaaS platforms, demonstrates a professionalization of cybercrime that demands a more proactive and layered defense strategy from individuals and organizations alike."
The IRS, while not commenting directly on Microsoft’s latest report, consistently reiterates its core message to taxpayers: "The IRS will never initiate contact with taxpayers by email, text messages, or social media channels to request personal or financial information." This long-standing advisory serves as a fundamental principle for identifying fraudulent communications. Any unsolicited email purporting to be from the IRS or a related tax authority should immediately be treated with extreme suspicion.
Comprehensive Defense Strategies for Individuals and Organizations
To mitigate the escalating risks posed by these tax season cyberattacks, a multi-faceted approach to cybersecurity is imperative.
For organizations, particularly those in financial services, technology, and any sector handling sensitive client data, the following measures are crucial:
- Enforce Multi-Factor Authentication (MFA): Implement MFA for all user accounts, especially those with access to sensitive systems or data. This adds a critical layer of security, making it significantly harder for attackers to gain access even if they manage to harvest credentials.
- Implement Conditional Access Policies: Utilize policies that restrict access to corporate resources based on factors like user location, device compliance, and application sensitivity. This can prevent unauthorized access from suspicious sources or unmanaged devices.
- Robust Email and Web Security: Deploy advanced email filtering solutions capable of detecting sophisticated phishing attempts, including those using legitimate services like Amazon SES. Web security gateways should actively monitor and scan visited websites to block access to known malicious domains and phishing sites.
- Security Awareness Training: Conduct regular, mandatory security awareness training for all employees, with a particular focus on recognizing phishing attempts, understanding the risks of clicking suspicious links or opening attachments, and the dangers of QR code scams. Training should be updated to reflect current threat trends, such as RMM abuse.
- Monitor RMM Tool Usage: Implement strict policies and technical controls to monitor and audit the installation and usage of RMM tools. Any unauthorized deployment or unusual activity associated with these tools should trigger immediate alerts and investigation.
- Incident Response Planning: Develop and regularly test a comprehensive incident response plan to ensure a swift and effective reaction in the event of a breach.
- Data Backup and Recovery: Maintain secure, isolated backups of critical data to facilitate recovery in the event of data theft or ransomware attacks.
For individual taxpayers, vigilance and caution are paramount:
- Verify Sender Identity: Always independently verify the sender of any unexpected or suspicious email, especially those related to taxes. Do not click on links within the email; instead, navigate directly to the official website of the IRS or your tax preparer.
- Be Skeptical of Urgency: Phishing emails often create a false sense of urgency. Be wary of messages demanding immediate action or threatening penalties.
- Avoid Attachments and Unknown Links: Never open attachments or click links from unsolicited emails.
- Use Strong, Unique Passwords and MFA: Employ strong, unique passwords for all online accounts, particularly financial and email services, and enable multi-factor authentication wherever possible.
- Keep Software Updated: Ensure your operating system, web browsers, and antivirus software are always up to date to protect against known vulnerabilities.
- Report Suspicious Activity: Report suspicious emails to your email provider and to the IRS ([email protected]).
The Broader Implications of Persistent Cyber-Enabled Fraud
The relentless nature of these tax season campaigns and the increasing sophistication of attacker methodologies, particularly the abuse of legitimate tools, have broader implications beyond immediate financial losses. They erode public trust in digital communications and official governmental outreach, making it harder for legitimate organizations to disseminate important information. The economic costs associated with data breaches, identity theft, and recovery efforts are substantial, impacting businesses, individuals, and the economy at large. Furthermore, the privacy implications are profound, as the theft of personal financial data can lead to long-term identity fraud and personal distress.
In conclusion, the ongoing tax season in the U.S. serves as a stark reminder of the persistent and evolving nature of cyber threats. The warnings from Microsoft, coupled with the observed large-scale campaigns and the alarming trend in RMM tool abuse, underscore the critical need for continuous vigilance, robust security measures, and ongoing user education. Proactive defense and an informed public are the most effective bulwarks against these sophisticated and financially damaging cyber-enabled frauds.