A significant security vulnerability, now successfully patched, in the widely adopted third-party Android software development kit (SDK) known as EngageLab SDK, could have exposed millions of cryptocurrency wallet users to severe data theft and unauthorized access. The flaw, detailed in a comprehensive report by the Microsoft Defender Security Research Team, allowed malicious applications on the same device to circumvent Android’s robust security sandbox, thereby gaining illicit access to sensitive private user data. This discovery underscores the profound risks inherent in the mobile application supply chain and the cascading impact even a single flawed component can have on a vast ecosystem.
The Vulnerability Unpacked: Intent Redirection Explained
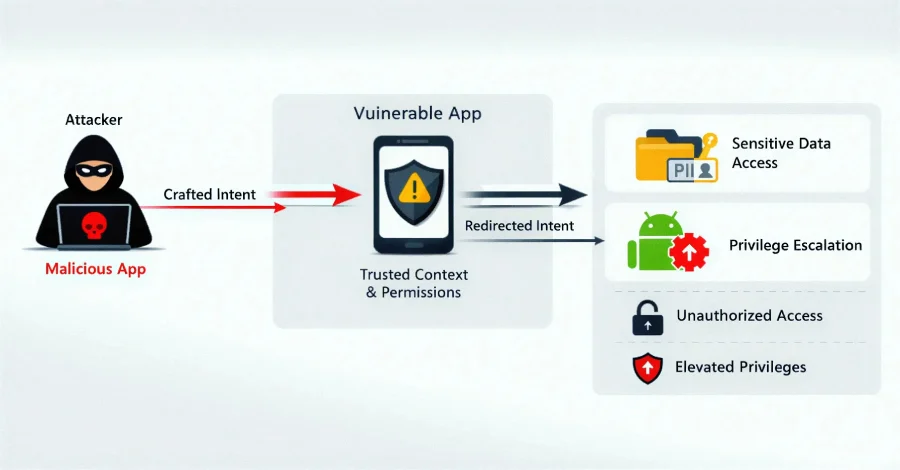
At the heart of this critical security lapse was an "intent redirection vulnerability," identified specifically in EngageLab SDK version 4.5.4. To understand the gravity of this flaw, it’s essential to grasp the fundamental role of "intents" within the Android operating system. Intents are specialized messaging objects that serve as a crucial inter-component communication mechanism, allowing various parts of an application or even different applications to request actions from one another. For instance, an intent might be used to launch a new activity, start a service, or broadcast a system-wide message. They are the backbone of interaction and functionality within the Android environment, enabling seamless user experiences and complex application features.
Intent redirection, in a malicious context, occurs when an attacker manipulates the contents of an intent that a vulnerable application sends. By exploiting this weakness, a malicious app can leverage the legitimate app’s "trusted context" – essentially, its granted permissions and established access – to achieve unauthorized objectives. This could include gaining access to protected components of other applications, exfiltrating sensitive data stored by those applications, or even escalating privileges within the Android environment, effectively breaking out of the security sandbox designed to isolate applications from one another. The Android security sandbox is a cornerstone of the operating system’s protection model, ensuring that each application runs in its own isolated process with limited access to system resources and other apps’ data. Bypassing this sandbox is a high-impact exploit, as it negates one of Android’s primary security assurances.
In this specific scenario, an attacker could install a seemingly innocuous malicious app on a user’s device through various vectors, such as sideloading, phishing, or even through compromised app stores. Once present on the device, this malicious app could then interact with an installed application that had integrated the vulnerable EngageLab SDK. By crafting a specially malformed intent, the attacker’s app could trick the legitimate app into redirecting its actions or exposing internal directories and data that should otherwise remain private and inaccessible. This could lead to a compromise of highly sensitive information, particularly pertinent for applications handling financial data or digital assets.
EngageLab SDK: A Critical Component in Millions of Apps
The EngageLab SDK is not an obscure, niche library; it is a widely deployed third-party software development kit that offers a crucial push notification service. According to its official documentation and marketing materials, the SDK is designed to enable developers to deliver "timely notifications" based on user behavior that has already been tracked and analyzed. Once integrated into a mobile application, the SDK provides a robust framework for sending personalized notifications, facilitating real-time engagement, and enhancing user retention. This functionality is vital for many modern applications, from e-commerce platforms and social media apps to financial services and, notably, cryptocurrency wallets, which rely heavily on instant alerts for transaction confirmations, price changes, and security notifications.
The widespread adoption of EngageLab SDK across various application categories significantly amplified the potential impact of this vulnerability. Microsoft’s investigation revealed that a substantial number of applications utilizing the SDK were deeply embedded within the cryptocurrency and digital wallet ecosystem. This finding immediately raised red flags due to the high-value nature of the assets managed by these applications. The tech giant’s report indicated that affected cryptocurrency wallet apps alone accounted for more than 30 million installations globally. When considering other non-wallet applications built using the same vulnerable SDK, the total installation count soared past an alarming 50 million. This scale of integration meant that a single flaw in one upstream library could, theoretically, jeopardize the digital security and financial assets of tens of millions of users worldwide.
Chronology of Discovery and Resolution
The timeline of this vulnerability’s discovery, disclosure, and remediation highlights the complexities and collaborative efforts involved in securing the vast mobile ecosystem. While the exact date of initial discovery by the Microsoft Defender Security Research Team was not publicly specified, their detailed report was published on April 9, 2026, bringing the issue to wider attention. However, the critical first step in the resolution process—responsible disclosure—occurred significantly earlier.

Microsoft, adhering to industry best practices for vulnerability management, privately informed EngageLab of the identified flaw in April 2025. This responsible disclosure period is crucial, allowing the affected vendor sufficient time to develop and distribute a patch before the vulnerability is made public, thus minimizing the window for malicious exploitation. Following this disclosure, EngageLab diligently worked to address the vulnerability, culminating in the release of a patched version, EngageLab SDK 5.2.1, in November 2025. This updated version contained the necessary fixes to mitigate the intent redirection vulnerability present in older iterations, particularly version 4.5.4.
Subsequent to the patch’s availability, Microsoft’s security team continued its monitoring and analysis. Upon public disclosure in April 2026, Google, the steward of the Android ecosystem, took decisive action. While specific names of the vulnerable applications were not revealed in Microsoft’s report to protect user privacy and avoid potential targeting, it was confirmed that all detected applications using vulnerable versions of the EngageLab SDK were promptly removed from the Google Play Store. This swift removal served as a critical safeguard, preventing new installations of compromised apps and protecting users who might not have updated their existing applications. This multi-stage process—discovery by a security researcher, responsible disclosure to the vendor, vendor patch development, and platform-level enforcement—exemplifies the collaborative model essential for maintaining digital security on a global scale.
The Cryptocurrency Connection: A High-Stakes Target
The particular focus on cryptocurrency and digital wallet applications in Microsoft’s report is not coincidental. The burgeoning digital asset economy, while offering immense opportunities, has also become a prime target for cybercriminals due to the inherent value and often irreversible nature of cryptocurrency transactions. Mobile cryptocurrency wallets, in particular, are attractive targets because they directly hold private keys, mnemonic phrases, and other sensitive credentials that grant direct access to users’ digital funds.
An intent redirection vulnerability in such applications could have catastrophic consequences. Imagine an attacker gaining access to a wallet application’s internal directories. This could potentially expose backup files, unencrypted private keys, transaction histories, or even allow the malicious app to initiate transactions on behalf of the user by exploiting the wallet’s trusted context. While Microsoft stated there was no evidence of the vulnerability being actively exploited in a malicious context prior to its public disclosure, the potential for such an attack was immense. The financial incentive for exploiting cryptocurrency wallets far exceeds that of typical data breaches, making these applications high-value targets for sophisticated threat actors.
The 30 million installations figure for affected cryptocurrency wallets alone underscores the immense scale of potential financial risk. A successful exploit could have led to widespread theft of digital assets, eroding user trust in mobile crypto platforms and potentially destabilizing parts of the burgeoning Web3 ecosystem. This incident serves as a stark reminder that even seemingly minor flaws in underlying software components can have outsized implications when integrated into applications managing significant financial value.
Microsoft’s Role and Responsible Disclosure
The diligent work of the Microsoft Defender Security Research Team was instrumental in uncovering and mitigating this widespread threat. Microsoft, a titan in the technology industry, has increasingly positioned itself as a leading entity in cybersecurity research, dedicating significant resources to identifying vulnerabilities not just in its own products but across the broader digital landscape. Their security research teams frequently publish detailed analyses of newly discovered threats, vulnerabilities, and attack techniques, contributing valuable intelligence to the global cybersecurity community.
The process of "responsible disclosure" employed by Microsoft is a cornerstone of ethical hacking and vulnerability management. Instead of immediately publishing the details of the flaw, which could inadvertently aid malicious actors, Microsoft first engaged directly with EngageLab. This private communication channel allowed EngageLab to develop and roll out a fix without public pressure or immediate threat of widespread exploitation. The seven-month period between disclosure (April 2025) and patch release (November 2025) demonstrates a reasonable timeframe for a vendor to respond, develop, test, and deploy an update for a complex software component integrated into millions of applications.
Once the patch was available and Google had taken steps to remove vulnerable apps from its Play Store, Microsoft then proceeded with public disclosure. This phased approach ensures that users and developers are informed about the threat only after a remedy is available, empowering them to take necessary actions to protect themselves. Microsoft’s report not only detailed the technical aspects of the vulnerability but also emphasized the broader lessons about third-party SDK dependencies, urging developers to be vigilant about their software supply chain security.

The Broader Implications for Mobile Security and Supply Chains
This incident extends beyond a single SDK or a particular set of applications; it illuminates a fundamental challenge in modern software development: the increasing reliance on third-party components and the complexities of the supply chain. As Microsoft aptly noted in its report, "Apps increasingly rely on third-party SDKs, creating large and often opaque supply-chain dependencies." This creates an environment where a flaw in a single component, developed by a different entity, can have far-reaching security implications across numerous independent applications and millions of end-users.
The "supply chain attack" vector, where attackers target less-secure components in a larger system to compromise the end product, is becoming increasingly prevalent. Developers often integrate SDKs for convenience, speed, and specialized functionality (like push notifications, analytics, or advertising) without fully understanding the underlying code’s security posture or the full extent of permissions and access it might require. This can lead to a false sense of security, as the app developer might trust the SDK vendor implicitly, or simply lack the resources to conduct exhaustive security audits of every third-party library.
Furthermore, the issue highlights the critical importance of secure coding practices and robust security architectures within SDK development itself. When SDKs expose "exported components" or rely on "trust assumptions that aren’t validated across app boundaries," they create avenues for exploitation. In Android, exported components are those that can be accessed by other applications, and if not properly secured with permissions or intent filters, they can become attack surfaces. The EngageLab SDK vulnerability exploited precisely this kind of weakness, demonstrating how a component designed for inter-app communication could be repurposed by a malicious actor to achieve unauthorized access.
For developers, the lesson is clear: comprehensive security audits of all third-party dependencies are not optional but essential. This includes regularly checking for updates, understanding the permissions requested by SDKs, and isolating SDK functionality where possible. Implementing a robust Software Bill of Materials (SBOM) can help track all components within an application, making it easier to identify and address vulnerabilities when they are disclosed.
For users, this incident reinforces the importance of downloading applications only from official and trusted sources like the Google Play Store, exercising caution with requested permissions, and keeping applications updated to their latest versions. While Google’s removal of vulnerable apps is a strong protective measure, users with sideloaded apps or those who defer updates might remain at risk.
Protecting Digital Assets: Lessons Learned
The EngageLab SDK vulnerability serves as a potent case study on the interconnectedness of the mobile app ecosystem and the continuous need for vigilance. While there was no evidence of active exploitation, the potential for harm, particularly in the high-value sector of digital asset management, was significant.
The primary recommendation remains steadfast: developers who integrate the EngageLab SDK into their applications must update to version 5.2.1 or later as soon as possible. This is a critical step to ensure that their applications are no longer susceptible to the intent redirection flaw. Beyond this specific patch, the broader lessons learned from this incident should guide future development and user behavior:
- Prioritize Supply Chain Security: Developers must implement rigorous vetting processes for all third-party SDKs and libraries, conducting regular security assessments and maintaining an up-to-date SBOM.
- Practice Principle of Least Privilege: SDKs, like all application components, should operate with the minimum necessary permissions to perform their intended function. Overly permissive SDKs increase the attack surface.
- Regular Updates: Both developers and end-users must prioritize timely updates. Developers should integrate the latest secure versions of SDKs, and users should ensure their apps and operating systems are always up-to-date to receive critical security patches.
- Enhanced Monitoring and Threat Intelligence: Security research teams, like Microsoft’s, play an indispensable role in identifying and disclosing vulnerabilities. Collaborative efforts between researchers, vendors, and platform providers are crucial for a resilient digital environment.
- User Awareness: Educating users about the risks of downloading apps from untrusted sources, understanding app permissions, and the importance of timely updates remains a vital layer of defense.
In an era where digital assets are becoming increasingly integrated into daily life, and mobile devices serve as primary interfaces for managing these assets, the security of the underlying software infrastructure is paramount. The EngageLab SDK vulnerability underscores that security is not just about the final application, but about every component in its vast and complex supply chain. Continuous vigilance, proactive security measures, and a commitment to responsible disclosure and timely patching are the cornerstones of protecting the digital future.