A Network Policy Server (NPS) empowers network administrators to establish and enforce granular policies that govern network access, ensuring that only authenticated and authorized users and devices can connect to critical network resources. This versatile component plays a pivotal role in centralizing the processes of authentication, authorization, and accounting (AAA) for all entities that seek to join a network. Essentially, NPS represents Microsoft’s robust implementation of a Remote Authentication Dial-In User Service (RADIUS) server and proxy within the Windows Server operating system, making it an indispensable tool for comprehensive network management and security. To fully grasp the significance of NPS, it is crucial to first understand the foundational RADIUS protocol, followed by an exploration of NPS’s specific purpose, its manifold benefits, its strategic role within modern networking architectures, and essential best practices for its effective management.
The Paramount Importance of Network Security and Policy Management in the Digital Age
In an era characterized by an ever-increasing reliance on digital infrastructure for business operations, the seamless exchange of data, and global communication, networks and servers have become prime targets for malicious actors. This heightened threat landscape underscores the absolute necessity of implementing stringent network security measures and meticulously managing access policies. The consequences of inadequate security can range from significant financial losses due to data breaches and operational downtime to severe reputational damage and legal liabilities.
The primary drivers behind the critical importance of network security and policy management include:
- Protection Against Cyber Threats: Robust security protocols and policies are the first line of defense against a myriad of cyber threats, including malware, ransomware, phishing attacks, and denial-of-service (DoS) attacks. These threats can cripple operations, compromise sensitive data, and lead to substantial recovery costs.
- Data Confidentiality and Integrity: Ensuring that sensitive corporate and customer data remains confidential and unaltered is paramount. Effective policies prevent unauthorized access and modifications, thereby safeguarding intellectual property, personal information, and proprietary business intelligence.
- Regulatory Compliance: Numerous industries are subject to strict regulatory frameworks (e.g., GDPR, HIPAA, PCI DSS) that mandate specific security and data handling practices. Proper network policy management is essential for meeting these compliance requirements and avoiding hefty fines and legal repercussions.
- Maintaining Business Continuity: Unauthorized access or disruption to network services can lead to significant downtime, impacting productivity, customer service, and revenue streams. Well-defined policies contribute to network stability and resilience, ensuring business continuity.
- Efficient Resource Management: By controlling who can access what resources and when, administrators can optimize network performance and prevent the overutilization or misuse of bandwidth and other critical assets.
- User Accountability: The accounting component of AAA ensures that all network activities are logged, providing an audit trail that can be used to identify the source of security incidents, troubleshoot issues, and enforce acceptable use policies.
Demystifying the RADIUS Protocol: The Foundation of Network Access Control
The RADIUS (Remote Authentication Dial-In User Service) protocol, established in 1991, serves as a standardized, network-based protocol that offers centralized Authentication, Authorization, and Accounting (AAA) management for users who access and utilize network services. Its widespread adoption has made it a de facto standard for network access servers, playing a pivotal role in controlling and managing who can connect to a network and what they can do once connected.
Authentication: Verifying Identity
The first "A" in AAA, Authentication, is the critical process of verifying a user’s or device’s identity. When an entity attempts to connect to a network, it is required to present credentials, typically a username and password, but increasingly also through certificates or multi-factor authentication methods. The RADIUS server then scrutinizes these credentials against its established database and security policies to confirm the legitimacy of the request. This fundamental step ensures that only known and validated entities are granted entry into the network.
Authorization: Defining Access Privileges
Following successful authentication, the next crucial step is Authorization. This process delineates the specific permissions and privileges an authenticated user or device possesses within the network. For instance, a network administrator will likely have broader access rights than a standard end-user or a guest connection. RADIUS servers meticulously manage these permissions, ensuring that each entity can only access the resources and services appropriate to its assigned authorization level, thereby enforcing the principle of least privilege.
Accounting: Tracking Network Usage
The final "A" in AAA is Accounting, which involves the comprehensive tracking and logging of user activities and resource consumption on the network. This includes details such as connection duration, the specific services and resources accessed, and the volume of data transferred. This granular accounting information is invaluable for a multitude of purposes, including billing, auditing network usage, identifying bandwidth hogs, performing security forensics, and gaining insights into overall network traffic patterns.
The Operational Mechanics of RADIUS Servers
RADIUS operates on a well-defined client-server model. The RADIUS client, typically a network access server such as a Virtual Private Network (VPN) concentrator, a wireless access point, or a dial-up server, intercepts user connection requests and forwards them, along with the user’s credentials, to the RADIUS server. The RADIUS server then processes these requests, consulting its internal databases and predefined policies to authenticate and authorize the user. Upon completion of this process, the server sends a response back to the client, either granting or denying network access.
Key functionalities of RADIUS servers include:
- Centralized AAA Management: Consolidating user authentication, authorization, and accounting in a single point simplifies management and enhances security.
- Protocol Agnosticism (for clients): RADIUS clients can communicate with RADIUS servers regardless of the specific access technology being used (e.g., Wi-Fi, VPN, dial-up).
- Policy Enforcement: RADIUS servers can enforce granular access policies based on user groups, time of day, location, and other contextual factors.
- Extensibility: The RADIUS protocol can be extended with vendor-specific attributes to support advanced features and custom configurations.
The Strategic Purpose of Network Policy Server (NPS)
Within the intricate network infrastructure of many organizations, NPS serves as a linchpin, primarily functioning as Microsoft’s sophisticated implementation of a RADIUS server and proxy. The overarching objective of NPS is to centralize and streamline the entire spectrum of authentication, authorization, and accounting processes for both users and devices attempting to access a network. This centralization significantly enhances network security, streamlines administrative oversight, and improves overall management efficiency.
Centralized Authentication and Authorization: The First Pillars of Security
Centralized authentication is the bedrock of network security, ensuring that every entity attempting to gain access to network resources undergoes a rigorous verification process. This prevents unauthorized access and mitigates the risk of credential theft. Authorization, intricately linked to authentication, then defines the precise boundaries of what an authenticated entity is permitted to do within the network. NPS excels in managing these critical functions, establishing a secure and efficient network environment by:

- Uniform Credential Verification: All access requests are directed through NPS, ensuring a consistent and robust method of verifying user identities, whether they are connecting via VPN, Wi-Fi, or other network access points.
- Role-Based Access Control (RBAC): NPS facilitates the implementation of RBAC, allowing administrators to assign specific access rights and permissions based on user roles and responsibilities. This ensures that users only have access to the information and systems necessary for their job functions.
- Network Access Protection (NAP) Integration: NPS can integrate with Microsoft’s Network Access Protection (NAP) framework to enforce health policies. This means that devices must meet specific security requirements (e.g., up-to-date antivirus, patches) before being granted network access, further bolstering the security posture.
Accounting and Compliance: Ensuring Accountability and Adherence
The accounting functionality of NPS is indispensable for robust network governance and regulatory compliance. By meticulously tracking and logging user activities and resource consumption, NPS provides a vital audit trail. This is crucial for:
- Auditing and Monitoring: Detailed logs allow for the review of network access patterns, helping to identify any suspicious activities, security breaches, or policy violations.
- Regulatory Adherence: Many compliance standards require detailed logging of system access and data usage. NPS provides the necessary data to demonstrate compliance with regulations like HIPAA, GDPR, and PCI DSS.
- Resource Optimization: Analyzing accounting data can reveal patterns of network usage, enabling administrators to identify areas for optimization, capacity planning, and cost management.
- Troubleshooting: When network issues arise, accounting logs can provide valuable insights into user activity and system performance leading up to the problem, aiding in swift resolution.
Policy-Based Network Management: Tailoring Access to Organizational Needs
Policy-based network management, a core strength of NPS, empowers administrators to create and enforce specific, granular network access policies. This allows for a highly customized approach to network security and usage, tailored precisely to an organization’s unique requirements. NPS facilitates this by enabling the creation of policies based on a wide array of conditions, including:
- User Group Membership: Granting or denying access based on Active Directory group memberships.
- Time of Day: Restricting access during non-business hours or specific periods.
- Device Type or Health: Allowing access only from corporate-issued devices or those that meet health compliance standards.
- Location: Implementing geo-location-based access controls.
- Connection Method: Differentiating access rights based on whether a user is connecting remotely via VPN or locally.
This sophisticated policy engine ensures that network access is not a one-size-fits-all approach but rather a dynamic and controlled process that aligns with business objectives and security mandates.
The Multifaceted Benefits of Implementing NPS
The integration of NPS into an organization’s network infrastructure yields a comprehensive suite of advantages that significantly bolster both security and operational efficiency. These benefits collectively position NPS as an indispensable asset for any organization striving to optimize its network management practices and enhance its security posture.
- Enhanced Security: By centralizing authentication and authorization, NPS significantly reduces the attack surface and mitigates the risk of unauthorized access. Its ability to enforce granular policies ensures that only legitimate users and compliant devices can access network resources.
- Simplified Administration: Consolidating AAA functions into a single platform simplifies the management of user access and network policies. Administrators can define and manage policies from a central location, reducing the complexity and manual effort involved.
- Improved Network Performance: Effective policy enforcement can prevent network congestion caused by unauthorized or excessive usage, leading to improved performance for legitimate users and critical applications.
- Scalability: NPS is designed to scale with the needs of an organization, capable of handling a large number of authentication requests and supporting complex network environments.
- Cost-Effectiveness: As a feature of Windows Server, NPS offers a cost-effective solution for implementing robust AAA services, often eliminating the need for separate, third-party RADIUS solutions.
- Compliance Support: The robust accounting and logging capabilities of NPS directly support adherence to various industry regulations and compliance mandates, reducing the risk of penalties.
- Increased User Productivity: By ensuring secure and reliable access to necessary resources, NPS contributes to a more productive work environment for end-users.
The Three Distinct Roles of NPS in Network Management
NPS is a remarkably versatile tool, capable of fulfilling three primary and distinct roles within a network infrastructure, each contributing to its comprehensive network management capabilities.
1. NPS as a RADIUS Server: The Core Authentication Hub
In its most fundamental role, NPS functions as a RADIUS server. This means it is directly responsible for processing authentication and authorization requests originating from network access servers. When a user or device attempts to connect, NPS intercepts this request, verifies the provided credentials against its configured policies (often integrated with Active Directory), and determines the appropriate level of access. NPS can seamlessly integrate with a wide array of network access servers, including VPN servers, wireless access points (WAPs), dial-up servers, and even network switches supporting 802.1X authentication. This makes it a highly adaptable solution for securing various network connection types and critically enhances network security by centralizing and streamlining the authentication process.
2. NPS as a RADIUS Proxy: Orchestrating Distributed Access
When operating as a RADIUS proxy, NPS acts as an intermediary, intelligently forwarding authentication and configuration requests to other RADIUS servers within the network. This role is particularly invaluable in large, complex, or geographically distributed network environments where a single RADIUS server might not be sufficient or practical. NPS can also provide sophisticated load balancing capabilities, distributing authentication requests across multiple RADIUS servers to prevent overload and ensure optimal performance. Furthermore, it can implement failover mechanisms, redirecting requests to alternative servers if a primary server becomes unavailable, thereby ensuring high availability and continuity of network access. This proxy functionality enables NPS to manage authentication requests across disparate networks or sub-networks, facilitating seamless cross-network authentication and policy enforcement.
3. NPS as a Network Policy Server: The Enforcement Engine
In its capacity as a network policy server, NPS takes on the crucial responsibility of defining, managing, and enforcing network access policies. It acts as the ultimate arbiter, determining the conditions under which users and devices are granted or denied access to the network and its resources. This role allows for the creation of highly specific policies that can be triggered by various conditions, such as the user’s group membership, the time of day, the type of device being used, or even the security posture of the connecting device. This provides administrators with an exceptionally high degree of granular control over network access, ensuring that policies are not only defined but also rigorously enforced. In conjunction with NAP, NPS can enforce device health policies, ensuring that only compliant and secure devices can connect to the network, thereby significantly enhancing the overall security posture.
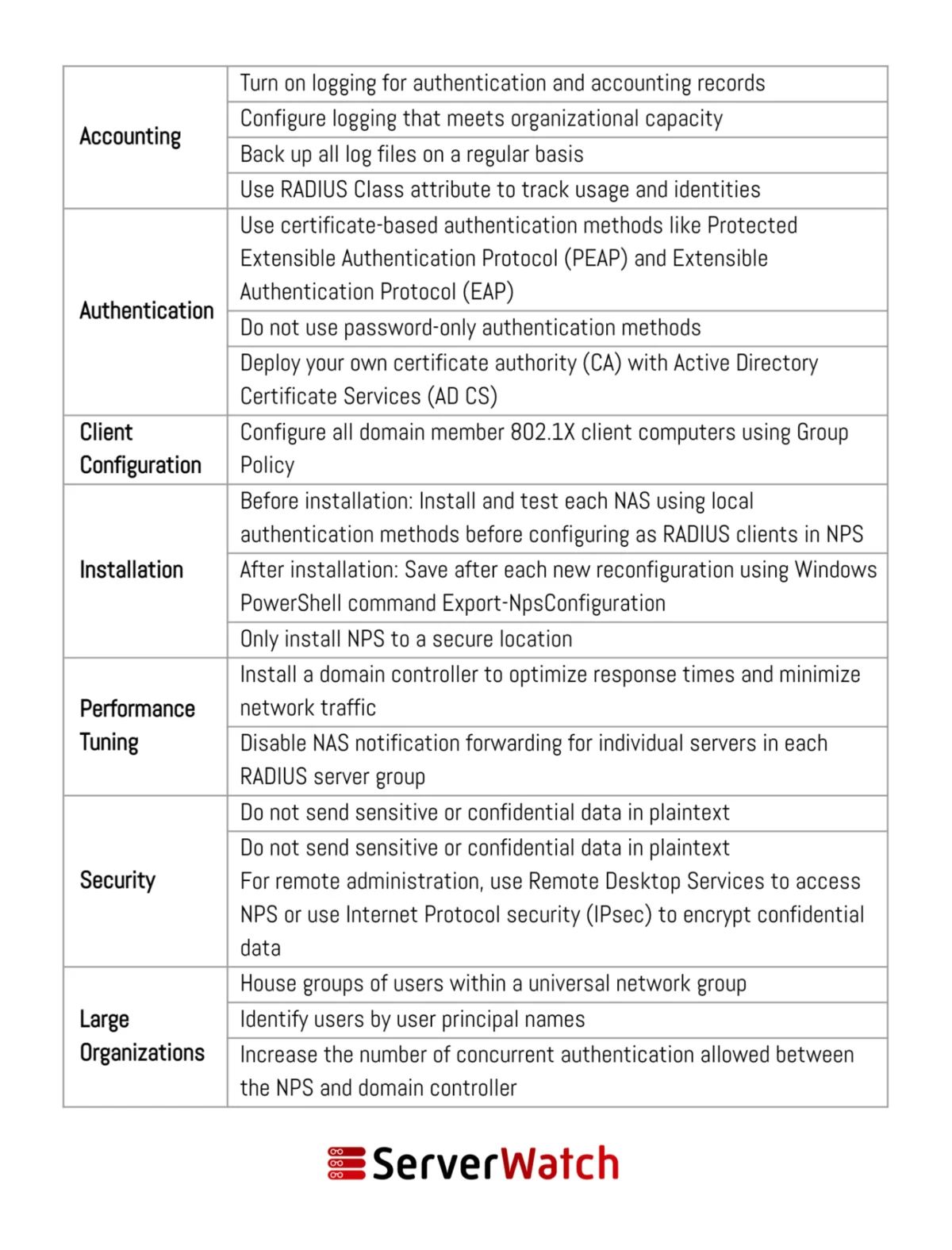
Implementing NPS: Essential Best Practices for Optimal Performance and Security
To harness the full potential of NPS and ensure its efficient, secure, and reliable operation, adherence to specific network and server management best practices is crucial. These guidelines are recommended by Microsoft and industry experts to align NPS functionality with an organization’s network management objectives and security mandates.
- Segregate NPS Infrastructure: Deploy NPS servers on a dedicated network segment, separate from general user access, to enhance security and prevent potential compromise of the authentication infrastructure.
- Secure RADIUS Communication: Utilize strong encryption methods, such as PEAP (Protected Extensible Authentication Protocol) or EAP-TLS, for RADIUS communication to protect credentials from interception.
- Implement Network Policies Logically: Design and implement network policies in a clear, organized, and logical manner, starting with the most restrictive policies and progressively adding more permissive ones. Document all policies thoroughly.
- Regularly Review and Audit Logs: Establish a routine for reviewing NPS event logs and accounting data. This is critical for identifying suspicious activity, troubleshooting issues, and ensuring compliance. Consider centralizing log management for easier analysis.
- Use Strong Passwords and Multi-Factor Authentication: Enforce strong password policies for all network users and leverage multi-factor authentication (MFA) for an additional layer of security, especially for remote access.
- Keep NPS Updated: Ensure that the Windows Server operating system and the NPS role are kept up-to-date with the latest security patches and updates from Microsoft to mitigate known vulnerabilities.
- Monitor NPS Performance: Implement performance monitoring tools to track CPU usage, memory consumption, and the number of authentication requests processed by the NPS server. This helps in identifying potential bottlenecks and ensuring optimal performance.
- Test Policies Thoroughly: Before deploying new or modified network policies into a production environment, test them rigorously in a controlled lab environment to ensure they function as intended and do not inadvertently block legitimate access.
- Leverage NPS as a Proxy Strategically: Utilize the RADIUS proxy role in distributed environments to manage load, improve resilience, and centralize policy enforcement across multiple network segments or remote sites.
- Integrate with Active Directory: Fully leverage Active Directory integration for user and group management to simplify policy creation and ensure consistent authentication against a centralized directory.
- Plan for High Availability: For critical network services, consider deploying NPS in a cluster configuration or implementing failover mechanisms to ensure continuous availability of authentication services.
The Bottom Line: NPS as an Indispensable Component of Modern Network Management
The Network Policy Server (NPS) has firmly established itself as an indispensable tool in the modern IT landscape, offering a powerful, flexible, and secure solution for managing network access and enforcing critical security policies. Its integration into an organization’s network infrastructure is not merely an optional enhancement but a fundamental requirement for maintaining a secure, efficient, and compliant operational environment.
By centralizing the complex processes of authentication, authorization, and accounting, NPS significantly bolsters network security, drastically reducing the risks associated with unauthorized access and cyber threats. Simultaneously, it streamlines administrative tasks, freeing up IT personnel to focus on more strategic initiatives rather than being bogged down by manual access control management. The ability to define and enforce granular policies ensures that network resources are utilized effectively and appropriately, contributing to improved performance and resource optimization.
Adhering to the outlined best practices for deploying and managing NPS is paramount. By doing so, organizations can not only maximize the benefits of this robust platform but also significantly mitigate the inherent risks associated with network security. This proactive approach ensures a seamless operational flow, protects sensitive data, and supports the overall business objectives of the organization. In essence, NPS is a cornerstone of modern network management, providing the essential controls and visibility needed to navigate the complexities of today’s interconnected world securely and efficiently.