A pervasive and technically advanced cyber espionage campaign, attributed to the Russia-linked threat actor known as APT28 (also identified as Forest Blizzard or formerly Fancy Bear and Strontium), has been uncovered, revealing a widespread compromise of insecure MikroTik and TP-Link routers. This sophisticated operation, which began as early as May 2025, involved modifying router settings to transform these devices into malicious infrastructure, enabling large-scale DNS hijacking and Adversary-in-the-Middle (AiTM) attacks aimed at exfiltrating sensitive authentication credentials from government agencies and critical service providers worldwide.
The extensive exploitation campaign, which has been codenamed "FrostArmada" by Lumen’s Black Lotus Labs, represents a significant escalation in the tactics employed by state-sponsored threat actors. Microsoft, in its independent analysis, described the initiative as a concerted effort to leverage vulnerable small office/home office (SOHO) internet devices to surreptitiously redirect DNS traffic, thereby facilitating the passive collection of network data and enabling further compromise. The sheer scale and stealth of this operation underscore the evolving threat landscape, where even consumer-grade networking equipment can be weaponized for geopolitical objectives.
Anatomy of a Covert Operation: DNS Hijacking and AiTM Attacks
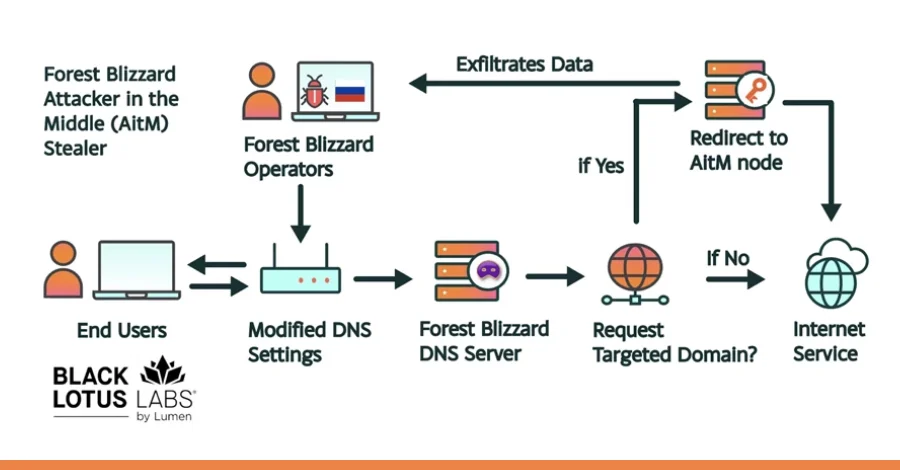
At the core of the FrostArmada campaign lies a meticulously crafted attack chain designed to be almost imperceptible to the end-user. The initial phase involves APT28 gaining unauthorized remote administrative access to vulnerable SOHO devices, primarily MikroTik and TP-Link routers. Once control is established, the threat actor modifies the default network configurations, specifically altering the DNS resolver settings. Instead of directing DNS queries to legitimate, secure servers, the compromised routers are configured to send all their DNS requests to actor-controlled servers.
This malicious reconfiguration has profound implications. When a user on a compromised network attempts to access a website or an application, particularly those requiring authentication like email services or login portals, their device’s DNS lookup for that domain is resolved by APT28’s malicious DNS server. This allows the threat actor to redirect the user’s traffic to an attacker-in-the-middle (AiTM) node, rather than the legitimate destination. At this AiTM node, a crucial phase of the attack unfolds: credentials, including passwords, OAuth tokens, and other sensitive authentication data for web and email-related services, are harvested and exfiltrated.

"Their technique modified DNS settings on compromised routers to hijack local network traffic to capture and exfiltrate authentication credentials," detailed a report from Black Lotus Labs. "When targeted domains were requested by a user, the actor redirected traffic to an attacker-in-the-middle (AitM) node, where those credentials were harvested and exfiltrated. This approach enabled a nearly invisible attack that required no interaction from the end user." This description highlights the insidious nature of the attack, which bypasses traditional endpoint security measures by compromising network infrastructure upstream of the target.
This campaign marks a significant technical evolution for APT28. Microsoft’s analysis specifically notes that this is the first documented instance where the adversarial collective has been observed leveraging DNS hijacking at scale to support AiTM attacks against Transport Layer Security (TLS) connections, particularly after exploiting edge devices. By interposing themselves between the user and the legitimate service, the attackers can effectively decrypt, inspect, and re-encrypt traffic, making the theft of credentials possible even over what users perceive as secure, encrypted connections. The ability to perform AiTM on TLS connections dramatically increases the potential impact and stealth of their espionage operations.
A Chronology of Espionage: From Initial Probes to Global Scale
The FrostArmada campaign did not emerge overnight but evolved through distinct phases, beginning with limited reconnaissance and gradually expanding into a global cyber espionage network. Initial activity was assessed to have commenced in May 2025, characterized by a more limited scope of router exploitation. This early phase likely involved testing the attack methodology, identifying vulnerable devices, and establishing initial command-and-control infrastructure.
By early August 2025, the campaign had escalated significantly, with widespread router exploitation and DNS redirection operations commencing in earnest. This period marked a rapid expansion of APT28’s compromised infrastructure, spreading across various geographical regions. The peak of the campaign’s activity was observed in December 2025, when Lumen’s Black Lotus Labs detected more than 18,000 unique IP addresses from no less than 120 countries communicating with APT28’s malicious infrastructure. This staggering number underscores the global reach and indiscriminate nature of the initial exploitation, aimed at building a vast network of compromised devices.
The primary targets of these efforts were predominantly government agencies, including ministries of foreign affairs and law enforcement bodies, as well as third-party email and cloud service providers. Geographically, the attacks spanned across North African, Central American, Southeast Asian, and European countries, indicating a broad strategic interest from the Russian state-sponsored group. Microsoft’s Threat Intelligence team further quantified the impact, identifying over 200 organizations and more than 5,000 consumer devices that were directly impacted by the threat actor’s malicious DNS infrastructure. This dual targeting of both organizational and individual devices suggests a layered approach to intelligence gathering, where consumer devices might serve as initial footholds or provide valuable contextual information.

Attribution and the Enduring Threat of APT28
The attribution of the FrostArmada campaign to APT28, also known as Forest Blizzard, is consistent across multiple leading cybersecurity intelligence firms and government agencies. This group, with its long and notorious history, has been linked to Russian military intelligence (GRU) and is renowned for its persistent and sophisticated cyber espionage activities targeting government, military, security, and critical infrastructure organizations globally. Other aliases for APT28 include Fancy Bear, Strontium, and Pawn Storm. Microsoft specifically attributed the activity to APT28 and its sub-group tracked as Storm-2754, indicating a clear organizational structure within the broader threat actor collective.
"For nation-state actors like Forest Blizzard, DNS hijacking enables persistent, passive visibility and reconnaissance at scale," stated Microsoft. "By compromising edge devices that are upstream of larger targets, threat actors can take advantage of less closely monitored or managed assets to pivot into enterprise environments." This statement highlights the strategic thinking behind targeting SOHO routers. These devices often lack the robust security features, frequent patching, and dedicated monitoring typical of enterprise-grade equipment, making them attractive weak points for initial compromise and lateral movement into more valuable networks.
The U.K. National Cyber Security Centre (NCSC) corroborated the findings, emphasizing the opportunistic yet highly strategic nature of the campaign. "It is believed that the DNS hijacking operations are opportunistic in nature, with the actor gaining visibility of a large pool of candidate target users then filtering down users at each stage in the exploitation chain to triage for victims of likely intelligence value," the NCSC reported. This suggests an initial broad sweep to identify potential targets, followed by a more refined selection process based on the intelligence value of the harvested credentials and data.
Vulnerabilities Exploited and Mitigating Risks
While the original report mentions "insecure" MikroTik and TP-Link routers, specific details emerged regarding the TP-Link exploitation. APT28 is believed to have exploited TP-Link WR841N routers for its DNS poisoning operations, likely taking advantage of CVE-2023-50224. This vulnerability, with a CVSS score of 6.5 (medium severity), is an authentication bypass flaw that could be exploited to extract stored credentials via specially crafted HTTP GET requests. The exploitation of such a vulnerability provides the initial access required to reconfigure the router’s DNS settings.

For MikroTik routers, a second cluster of servers was found to receive DNS requests via compromised routers, subsequently forwarding them to remote actor-owned servers. This cluster was also assessed to have engaged in interactive operations specifically targeting a smaller number of MikroTik routers located in Ukraine, suggesting a tailored approach for high-priority targets or regions. The specific vulnerabilities exploited in MikroTik devices were not detailed in the initial reports but generally point to unpatched firmware, weak default credentials, or other configuration flaws.
Joint Disruption and Broader Implications
In a significant collaborative effort, the infrastructure associated with the FrostArmada campaign has been disrupted and taken offline. This joint operation involved crucial cooperation between the U.S. Department of Justice, the Federal Bureau of Investigation (FBI), and other international partners, underscoring the global commitment to combating state-sponsored cyber threats. Such disruptions are vital in dismantling adversarial networks, preventing further espionage, and holding threat actors accountable.
The implications of the FrostArmada campaign extend beyond the immediate compromise and disruption. It serves as a stark reminder of the critical importance of supply chain security and the often-overlooked vulnerabilities in edge devices. Organizations and individuals alike must recognize that SOHO routers, while seemingly innocuous, represent a significant attack surface that can be leveraged by sophisticated adversaries. The ability of APT28 to maintain "persistent, passive visibility and reconnaissance at scale" highlights how compromising these upstream devices can provide an enduring intelligence advantage.
Furthermore, while the observed activity primarily focused on information collection, Microsoft warned of the broader potential. "Although we have only observed Forest Blizzard utilizing their DNS hijacking campaign for information collection, an attacker could use an AiTM position for additional outcomes, such as malware deployment or denial of service." This emphasizes the versatility of the AiTM technique, which could be repurposed for more destructive or disruptive cyber operations, posing an even greater threat to national security and critical infrastructure.
To mitigate such threats, cybersecurity experts strongly advise several preventative measures. These include regularly updating router firmware to the latest versions, which often contain patches for known vulnerabilities. Users should also change default administrative passwords to strong, unique credentials and disable remote management features if not absolutely necessary. Implementing network segmentation, monitoring DNS query logs for anomalies, and utilizing robust endpoint detection and response (EDR) solutions can also help detect and prevent such sophisticated attacks. The FrostArmada campaign serves as a critical wake-up call, urging a reevaluation of security postures, particularly concerning the foundational network devices that underpin our digital lives and critical operations. The ongoing battle against state-sponsored cyber espionage demands continuous vigilance, proactive defense, and international collaboration to safeguard digital sovereignty and security.