A new and highly evasive malware loader, dubbed DeepLoad, has been identified in the wild, utilizing an advanced combination of AI-assisted obfuscation, sophisticated process injection techniques, and the deceptive ClickFix social engineering tactic to infiltrate systems and steal credentials. This discovery comes as cybersecurity researchers also detail the emergence of Kiss Loader, another potent threat propagated through cunning phishing emails and leveraging legitimate services for its multi-stage attack. The simultaneous unveiling of these two distinct yet equally dangerous loaders underscores a significant escalation in the sophistication and stealth capabilities of cybercriminal operations targeting individuals and organizations worldwide.
DeepLoad represents a particularly concerning evolution in malware design, primarily due to its innovative use of artificial intelligence to generate highly randomized and difficult-to-detect code. According to a comprehensive report released by ReliaQuest researchers Thassanai McCabe and Andrew Currie, DeepLoad’s methods allow it to circumvent traditional security measures with remarkable efficacy. "It likely uses AI-assisted obfuscation and process injection to evade static scanning, while credential theft starts immediately and captures passwords and sessions even if the primary loader is blocked," the researchers stated in their findings shared with The Hacker News on March 30, 2026. This immediate and persistent credential harvesting capability makes DeepLoad an exceptionally high-value threat for adversaries seeking unauthorized access to sensitive accounts and corporate networks.
The ClickFix Deception: A Gateway for DeepLoad
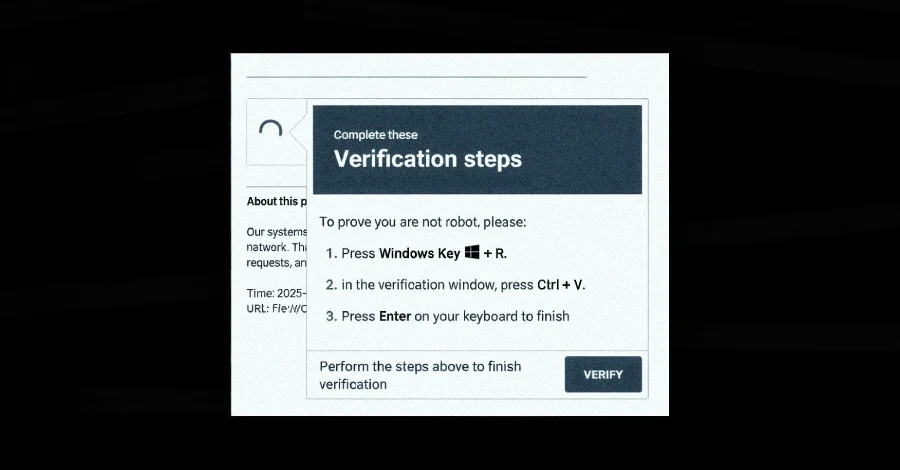
The initial point of compromise for DeepLoad campaigns hinges on the increasingly prevalent ClickFix social engineering tactic. This method preys on user trust and a lack of technical understanding by presenting a seemingly innocuous system issue, often a pop-up warning or a fake error message, that prompts the victim to perform a series of manual steps. Crucially, the lure tricks users into pasting malicious PowerShell commands directly into the Windows Run dialog box. This seemingly simple action, under the guise of "fixing" a non-existent problem, bypasses many automated defenses that might flag executable downloads or suspicious script executions.
The effectiveness of ClickFix lies in its ability to leverage the user as an unwitting accomplice. Instead of relying on traditional drive-by downloads or exploit kits, it manipulates human behavior to initiate the infection chain. Once the user executes the provided command, it invokes "mshta.exe," a legitimate Windows utility designed to process HTML applications. In this context, mshta.exe is weaponized to download and execute an obfuscated PowerShell loader, marking the true beginning of the DeepLoad infection. This technique, part of a broader "Living Off The Land" (LotL) strategy, is a growing trend among advanced threat actors who aim to blend malicious activity with normal system operations, making detection exceedingly difficult for conventional security tools.
DeepLoad’s Multi-Layered Evasion and Stealth Tactics
What sets DeepLoad apart is its profound commitment to stealth and evasion. The PowerShell loader itself is a testament to this, meticulously crafted to conceal its true purpose amidst a deluge of "meaningless variable assignments." This technique is believed to be a product of artificial intelligence, allowing the threat actors to generate unique, polymorphic code on the fly, rendering signature-based detection mechanisms largely ineffective. The AI-driven obfuscation dynamically alters the malware’s signature with each iteration, presenting a moving target for antivirus and endpoint detection solutions. Experts suggest that the increasing accessibility of AI tools is significantly lowering the barrier for entry into sophisticated cybercrime, enabling even less experienced threat actors to deploy highly evasive payloads.
Beyond its initial obfuscation, DeepLoad employs a suite of advanced techniques to remain undetected within a compromised system:

- Process Blending: The malware goes to great lengths to impersonate legitimate Windows processes. It hides its core payload within an executable named "LockAppHost.exe," a genuine Windows process responsible for managing the lock screen. By masquerading as a benign system component, DeepLoad avoids raising red flags with process monitoring tools that might otherwise identify anomalous executions.
- Forensic Trail Eradication: To obscure its tracks, DeepLoad proactively disables PowerShell command history. This crucial step prevents forensic analysts from easily reconstructing the initial execution chain or identifying subsequent malicious commands run via PowerShell. Furthermore, instead of relying on PowerShell’s built-in commands, DeepLoad directly invokes native Windows core functions to launch processes and modify memory. This circumvents common monitoring hooks that specifically target PowerShell-based activity, allowing it to operate with a higher degree of stealth.
- Dynamic Payload Generation: ReliaQuest researchers highlighted another ingenious evasion tactic: "To evade file-based detection, DeepLoad generates a secondary component on the fly by using the built-in PowerShell feature Add-Type, which compiles and runs code written in C#." This dynamic compilation process creates a temporary Dynamic Link Library (DLL) file that is dropped into the user’s Temp directory. Because this DLL is compiled anew with a randomized file name each time it’s executed, it effectively sidesteps file name-based detections and makes it challenging for security solutions to create persistent signatures.
- Asynchronous Procedure Call (APC) Injection: DeepLoad utilizes APC injection (MITRE ATT&CK T1055.004) to execute its main payload. This technique involves launching a trusted Windows process in a suspended state, injecting malicious shellcode into its memory, and then resuming the process’s execution. The key advantage here is that the decoded payload is never written to disk, leaving minimal artifacts for forensic analysis and making memory-based detection a necessity. APC injection is a hallmark of sophisticated malware, indicating a high level of technical expertise on the part of the threat actors.
DeepLoad’s Malicious Capabilities and Persistence
Once deeply embedded within a system, DeepLoad immediately focuses on its primary objective: credential theft. It is engineered to extract browser passwords from the infected host, targeting commonly used web browsers. Beyond this initial harvest, it also drops a malicious browser extension. This extension is designed to intercept credentials as they are entered on login pages, providing a continuous stream of sensitive data to the attackers. Crucially, this extension persists across user sessions, meaning it continues to operate even after a system reboot, unless explicitly removed by the user or security software.
The malware also demonstrates impressive lateral movement and persistence capabilities:
- Removable Media Propagation: DeepLoad is configured to automatically detect the connection of removable media devices, such as USB drives. Upon detection, it copies malware-laced files onto the drive, cleverly disguised with enticing names like "ChromeSetup.lnk," "Firefox Installer.lnk," and "AnyDesk.lnk." These
.lnk(shortcut) files are designed to appear as legitimate installers or applications. When a user double-clicks these shortcuts on another machine, the infection chain is triggered, facilitating rapid spread across different systems and networks. - WMI for Covert Re-infection: Perhaps one of DeepLoad’s most insidious features is its use of Windows Management Instrumentation (WMI) for covert re-infection and persistence. "DeepLoad used Windows Management Instrumentation (WMI) to reinfect a ‘clean’ host three days later with no user action and no attacker interaction," ReliaQuest explained. WMI serves a dual purpose: it breaks the parent-child process chains that many detection rules are built to catch, making it harder to trace the origin of malicious activity. More alarmingly, it creates a WMI event subscription that quietly re-executes the attack at a later time, ensuring persistence even if initial components are removed or quarantined. This capability highlights the threat actors’ intent to establish long-term footholds within compromised environments.
The overarching goal of DeepLoad, as analyzed by researchers, is to deploy multi-purpose malware capable of executing a wide array of malicious actions across the entire cyber kill chain. By avoiding writing persistent artifacts to disk, expertly blending into legitimate Windows processes, and rapidly spreading to other machines, DeepLoad poses a significant challenge to modern cybersecurity defenses.
The Emergence of Kiss Loader via Phishing Campaigns
Concurrently, G DATA researchers have detailed the discovery of another formidable malware loader, Kiss Loader. This loader is distributed through a more traditional yet still highly effective vector: meticulously crafted phishing emails containing Windows Internet Shortcut files (.URL) as attachments. These shortcut files, when clicked, initiate a complex multi-stage attack.
The infection chain for Kiss Loader unfolds as follows:
- Phishing Lure: Victims receive phishing emails designed to trick them into opening an attached
.URLfile. These emails often leverage social engineering themes related to invoices, delivery notifications, or urgent business matters to entice interaction. - WebDAV Resource Abuse: Upon execution, the
.URLfile does not directly download the malware. Instead, it connects to a remote WebDAV (Web Distributed Authoring and Versioning) resource, often hosted on legitimate cloud services like TryCloudflare domains. This abuse of trusted services adds a layer of legitimacy and makes it harder for network security solutions to block the initial communication. - Secondary Shortcut and Decoy: The WebDAV resource serves a secondary shortcut, which is cleverly disguised as a PDF document. This step reinforces the social engineering aspect, making the user believe they are simply opening a document.
- WSH Script Execution: Once this secondary shortcut is executed, it launches a Windows Script Host (WSH) script. The WSH script is then responsible for running a JavaScript component.
- Batch Script and Persistence: The JavaScript component proceeds to retrieve and execute a batch script. This batch script performs several critical functions: it displays a decoy PDF document to the user, maintaining the illusion that a legitimate file has been opened; it sets up persistence in the Windows Startup folder, ensuring the malware restarts with the system; and finally, it downloads the Python-based Kiss Loader.
- Venom RAT Deployment: In the ultimate stage of the attack, the Python-based Kiss Loader decrypts and executes Venom RAT, an advanced variant of the well-known AsyncRAT. AsyncRAT is a powerful open-source Remote Access Trojan (RAT) capable of extensive system control, data exfiltration, keylogging, webcam access, and more. Similar to DeepLoad, Kiss Loader also utilizes APC injection to run Venom RAT, further highlighting the prevalence and effectiveness of this stealth technique among contemporary threat actors.
At present, the full scope of attacks deploying Kiss Loader remains unclear, and researchers are investigating whether it is being offered under a malware-as-a-service (MaaS) model, which would significantly broaden its distribution. G DATA’s analysis indicates that the threat actor behind Kiss Loader claims to be from Malawi, providing a potential geographical lead for law enforcement and threat intelligence agencies.
Broader Implications and Expert Commentary

The emergence of DeepLoad and Kiss Loader signifies a worrying trend in the cybersecurity landscape. The increasing sophistication of malware loaders, characterized by AI-assisted obfuscation, extensive use of "living off the land" techniques, and advanced process injection methods, presents formidable challenges for defensive measures.
"These new loaders represent a significant leap in evasive capabilities," comments Dr. Anya Sharma, a leading cybersecurity analyst at TechGuard Solutions. "The integration of AI into obfuscation techniques means that traditional signature-based detections are becoming obsolete at an alarming rate. Security solutions must evolve towards more advanced behavioral analysis, machine learning-driven anomaly detection, and robust endpoint detection and response (EDR) capabilities to stand a chance against these adaptive threats."
The reliance on social engineering, particularly tactics like ClickFix, also underscores the enduring vulnerability of the human element. "No matter how advanced our technology becomes, if users are tricked into executing malicious code, the first line of defense is breached," states Michael Chen, a cybersecurity awareness specialist. "Continuous, practical cybersecurity training and simulated phishing exercises are no longer optional; they are critical components of any robust defense strategy."
The abuse of legitimate Windows utilities and cloud services by both loaders is another critical concern. This "living off the land" approach makes it incredibly difficult for security teams to differentiate between legitimate system activity and malicious operations, increasing the burden on incident response and forensic analysis.
"Organizations need to implement stringent application whitelisting, least privilege access policies, and granular monitoring of PowerShell activity and WMI events," advises Sarah Jones, a principal security architect. "Breaking the parent-child process chain is a clever evasion, but with the right telemetry and analytics, these anomalies can still be detected."
The potential for malware-as-a-service (MaaS) models for loaders like Kiss Loader further democratizes cybercrime, making sophisticated attack tools accessible to a wider range of threat actors. This lowers the barrier to entry for launching effective campaigns, leading to a potential surge in attack volume and diversity.
In response to these escalating threats, cybersecurity professionals emphasize a multi-faceted approach:
- Enhanced Threat Intelligence: Organizations must prioritize up-to-date threat intelligence feeds that provide insights into emerging TTPs (Tactics, Techniques, and Procedures) used by threat actors.
- Advanced Endpoint Security: Deployment of next-generation EDR and XDR (Extended Detection and Response) solutions that focus on behavioral analysis, AI-driven threat hunting, and memory inspection.
- Proactive Vulnerability Management: Regular patching and configuration hardening to minimize attack surfaces.
- User Education and Awareness: Continuous training programs to educate employees on social engineering tactics, phishing identification, and safe computing practices.
- Network Segmentation: Implementing network segmentation to limit lateral movement in the event of a breach.
- Identity and Access Management (IAM): Strong authentication mechanisms, including multi-factor authentication (MFA), to protect accounts even if credentials are stolen.
The ongoing cyber arms race between attackers and defenders continues to intensify. DeepLoad and Kiss Loader serve as stark reminders that threat actors are constantly innovating, leveraging the latest technological advancements – including AI – and exploiting human vulnerabilities to achieve their objectives. Remaining vigilant, adaptive, and proactive in cybersecurity defenses is paramount for protecting digital assets in this evolving threat landscape.