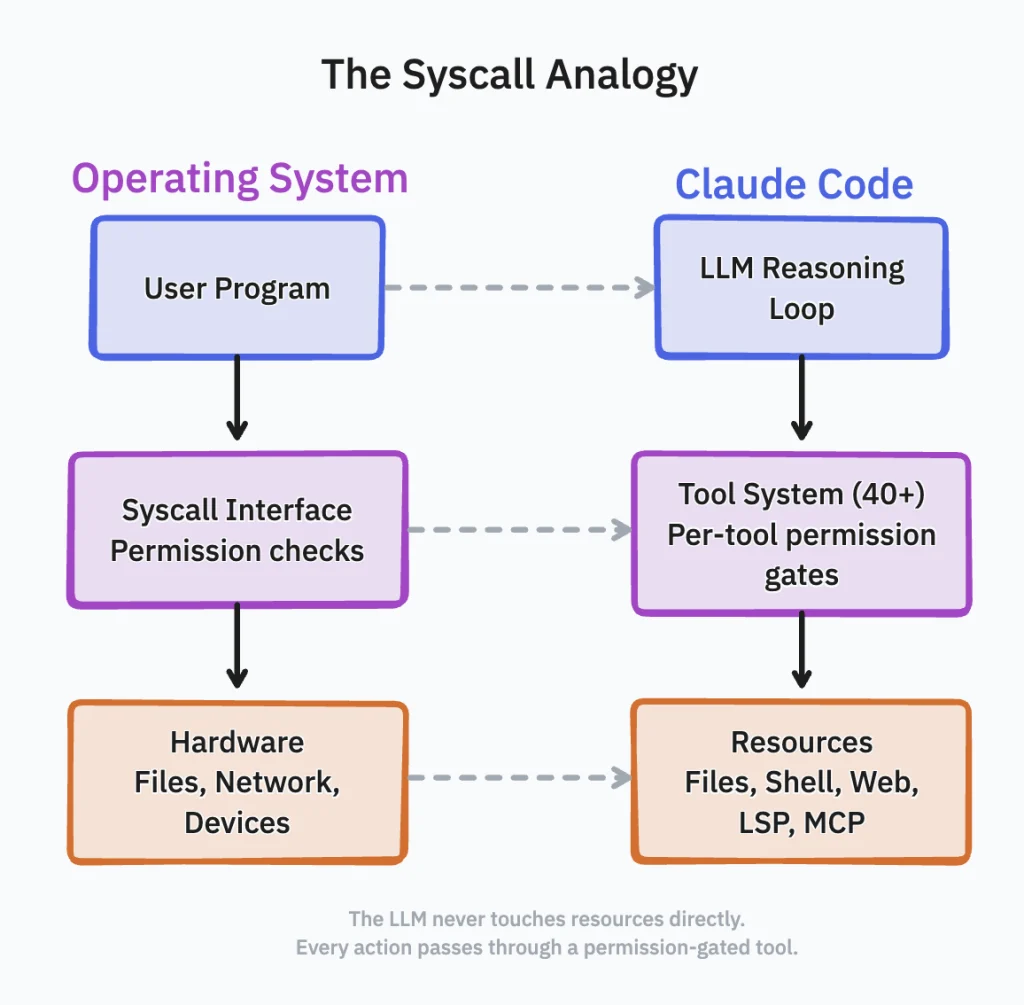
On Wednesday, a significant architectural revelation emerged from the AI development community when security researcher…
Tag: sophisticated
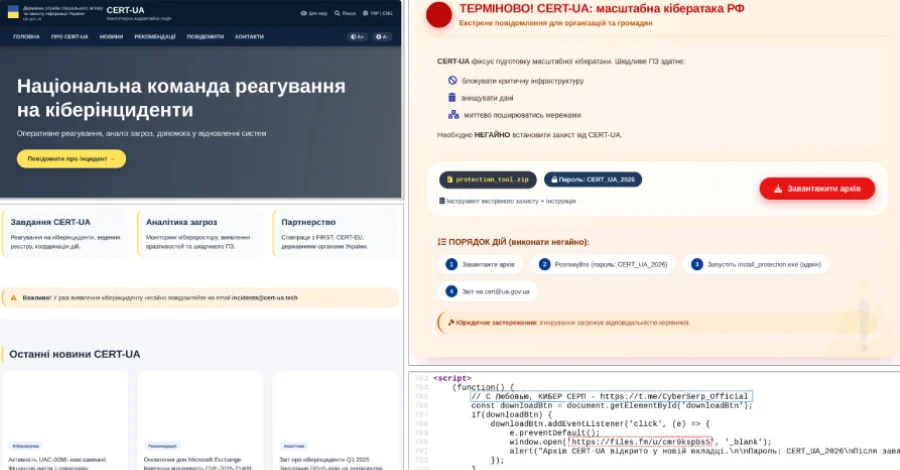
Ukrainian Cybersecurity Agency CERT-UA Impersonated in Sophisticated Phishing Campaign Distributing AGEWHEEZE RAT, AI Use Suspected
Kyiv, Ukraine – April 1, 2026 – The Computer Emergency Response Team of Ukraine (CERT-UA)…

High-Severity TrueConf Zero-Day Exploited in Sophisticated TrueChaos Campaign Targeting Southeast Asian Governments.
A critical high-severity security flaw identified within the TrueConf client video conferencing software has been…

Popular HTTP Client Axios Hit by Sophisticated Supply Chain Attack, Malicious Versions Deliver Cross-Platform Remote Access Trojan.
The widely-adopted HTTP client Axios has been at the center of a significant supply chain…
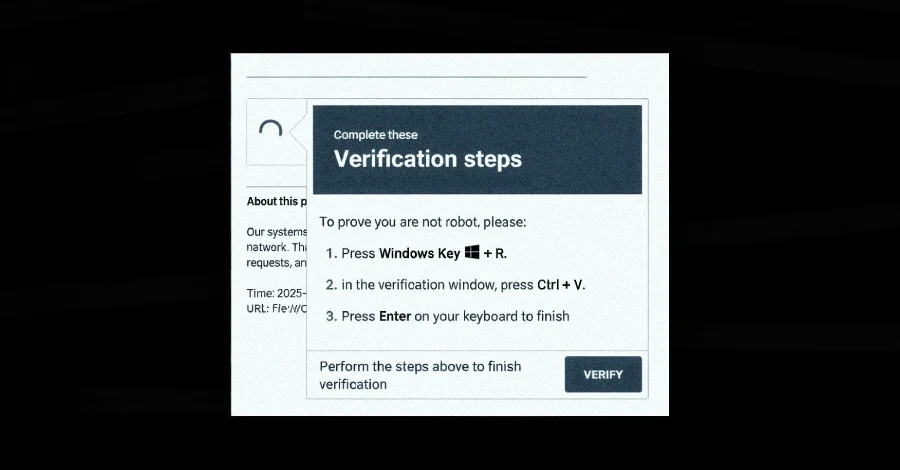
Sophisticated DeepLoad Malware Leverages AI-Assisted Evasion and ClickFix Social Engineering, While Kiss Loader Emerges Via Phishing Campaigns
A new and highly evasive malware loader, dubbed DeepLoad, has been identified in the wild,…

Sophisticated Phishing Campaigns Target TikTok Business Accounts and Deliver BianLian Malware via SVG Files
Threat actors are deploying highly sophisticated adversary-in-the-middle (AitM) phishing campaigns to compromise TikTok for Business…

TeamPCP Expands Sophisticated Supply Chain Campaign, Compromising Telnyx Python Package with Stealthy Audio Steganography Malware
The notorious threat actor group, TeamPCP, has further intensified its aggressive supply chain campaign, successfully…
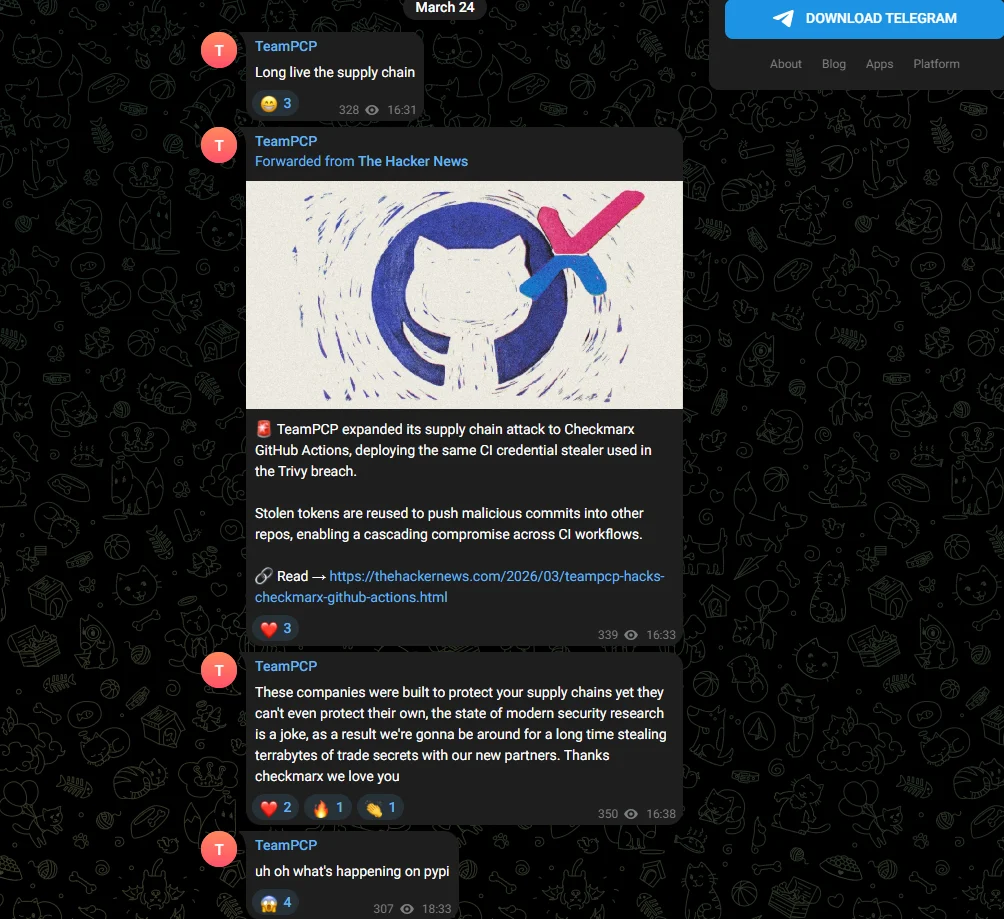
LiteLLM Python Package Compromised in Sophisticated TeamPCP Supply Chain Attack, Unveiling Credential Harvesters and Kubernetes Backdoors
The prominent Python package litellm, widely utilized for interfacing with various large language model (LLM)…
Sophisticated Malvertising Campaign Exploits Tax Season Searches, Deploys Kernel-Mode EDR Killer via Vulnerable Huawei Driver.
A sophisticated malvertising campaign, active since January 2026, has been observed meticulously targeting U.S.-based individuals…
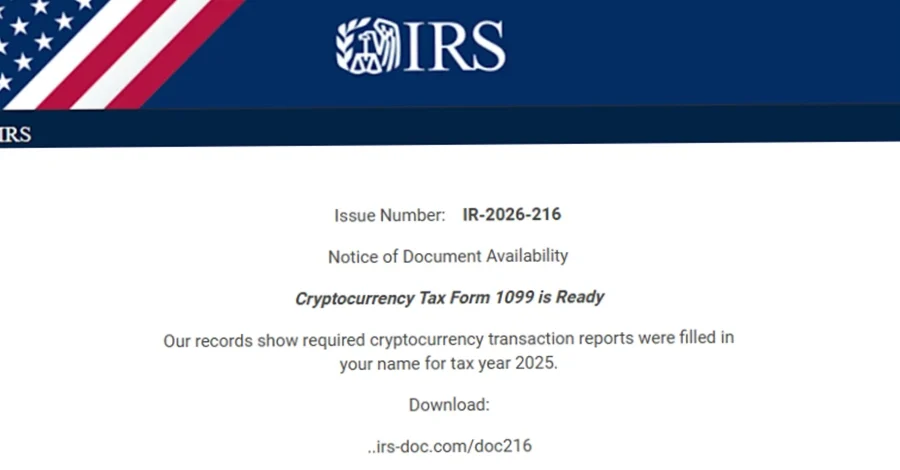
Microsoft Warns of Escalating Tax Season Cyberattacks Exploiting Urgency and Sophisticated Malware Delivery.
As the United States approaches its annual tax deadline, Microsoft has issued a critical warning…