Kyiv, Ukraine – April 1, 2026 – The Computer Emergency Response Team of Ukraine (CERT-UA) has unveiled details of a cunning and alarming phishing campaign that saw the national cybersecurity agency itself impersonated to disseminate a potent remote administration tool (RAT) known as AGEWHEEZE. This incident, occurring between March 26 and 27, 2026, highlights the escalating sophistication of cyber threats targeting Ukraine’s critical infrastructure and public sectors, with strong indications of artificial intelligence (AI) being leveraged by the perpetrators.
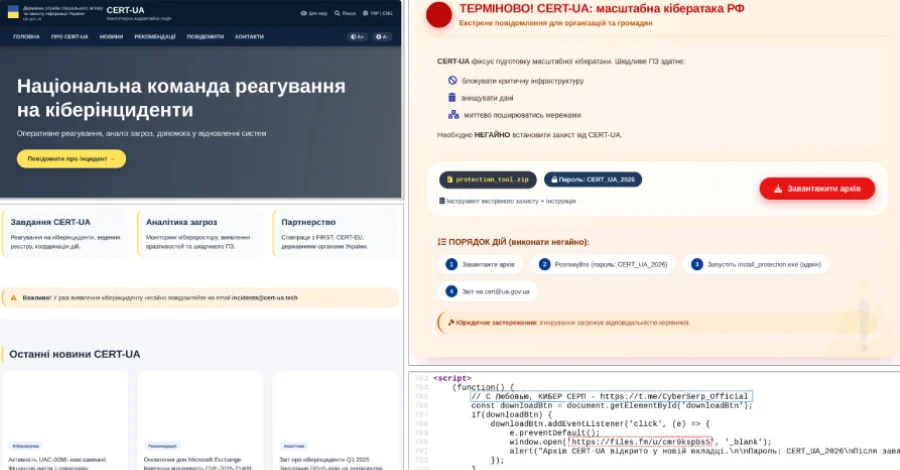
The threat actors, officially designated as UAC-0255, orchestrated a meticulously crafted attack, sending deceptive emails designed to mimic official CERT-UA communications. These emails urged recipients to install "specialized software," a common social engineering tactic that exploits trust in legitimate entities. The payload, a password-protected ZIP archive hosted on Files.fm, was titled "CERT_UA_protection_tool.zip," further lending a veneer of authenticity to the malicious download. The primary objective was to trick unsuspecting users into executing malware disguised as a security utility provided by the very agency tasked with protecting them. Some of these fraudulent communications originated from the email address "incidents@cert-ua[.]tech," a domain carefully chosen to appear credible.
Chronology of Deception and Discovery
The timeline of the attack unfolded rapidly over two days in late March 2026. On March 26 and 27, the UAC-0255 group initiated their email campaign, targeting a broad spectrum of Ukrainian organizations. These included vital state organizations, healthcare facilities, security companies, educational institutions, financial institutions, and software development firms – sectors critical to national stability and operations. The choice of targets underscores a strategic intent to potentially disrupt essential services, exfiltrate sensitive data, or establish a persistent foothold within various networks.
CERT-UA’s rapid detection and subsequent public disclosure of the campaign on April 1, 2026, demonstrated the agency’s vigilance and commitment to informing the public. Their swift action likely mitigated wider damage, allowing targeted organizations to take immediate preventative measures. The investigation revealed that the attack’s overall success was fortunately limited, with the agency noting that "no more than a few infected personal devices belonging to employees of educational institutions of various forms of ownership were identified." This outcome speaks to the effectiveness of CERT-UA’s internal monitoring and response capabilities, as well as potentially increased cybersecurity awareness among some segments of the Ukrainian populace. Specialists from CERT-UA provided crucial methodological and practical assistance to the affected parties, aiding in containment and recovery efforts.

Technical Deep Dive into AGEWHEEZE
At the heart of this campaign lies AGEWHEEZE, a remote access trojan (RAT) engineered with advanced capabilities. Developed in Go, a programming language increasingly favored by malware authors for its cross-platform compatibility and ease of deployment, AGEWHEEZE establishes communication with an external command-and-control (C2) server located at "54.36.237[.]92" via WebSockets. The use of WebSockets is noteworthy as it allows for persistent, bi-directional communication over a single connection, potentially making it harder to detect and block compared to traditional HTTP-based C2 channels.
Once deployed, AGEWHEEZE grants the attackers extensive control over the compromised system. Its functionalities are comprehensive, typical of a sophisticated RAT designed for espionage and sabotage. These capabilities include:
- Command Execution: The ability to execute arbitrary commands on the infected machine, allowing for further payload deployment, system configuration changes, or data manipulation.
- File Operations: Comprehensive control over files, including uploading, downloading, deleting, and modifying, facilitating data exfiltration or the introduction of additional malicious components.
- Clipboard Manipulation: Access to the user’s clipboard, enabling the theft of copied sensitive information such as passwords, cryptocurrency wallet addresses, or confidential documents.
- Mouse and Keyboard Emulation: The capacity to simulate user input, allowing attackers to remotely control the machine as if they were physically present, bypassing certain security measures or performing actions that require user interaction.
- Screenshots: Capturing screenshots of the desktop, providing visual intelligence on user activities and sensitive data displayed on the screen.
- Process and Service Management: The ability to list, start, stop, and terminate processes and services, which can be used to disable security software, launch malicious processes, or maintain stealth.
To ensure persistence and long-term access, AGEWHEEZE employs multiple techniques, demonstrating a robust design aimed at enduring system reboots and user attempts to remove it. These methods include creating scheduled tasks, modifying the Windows Registry to automatically launch at startup, or adding itself to the Startup directory, all standard but effective methods for maintaining a foothold. The multi-pronged approach to persistence makes the malware resilient and challenging to completely eradicate without expert intervention.
UAC-0255 and the Enigmatic "Cyber Serp"
The threat actor behind this campaign, UAC-0255, has been linked to a group identifying itself as "Cyber Serp." This collective operates a Telegram channel, "CyberSerp_Official," which was established in November 2025 and boasts over 700 subscribers. In their Telegram posts, Cyber Serp claims to be "cyber-underground operatives from Ukraine," a self-description that adds a layer of complexity and potential misdirection to their true origins and motivations.

Intriguingly, Cyber Serp has openly claimed responsibility for sending the phishing emails to an astonishing 1 million ukr[.]net mailboxes, asserting that over 200,000 devices were compromised. While CERT-UA’s assessment suggests a much lower success rate, the sheer scale of the claimed outreach indicates a significant operational capability. In a peculiar statement, Cyber Serp also declared, "We are not bandits – the average Ukrainian citizen will never suffer as a result of our actions." This assertion, despite their engagement in illicit activities, attempts to frame their actions with a certain moral ambiguity, possibly to garner sympathy or deflect severe condemnation. Such rhetoric is not uncommon among certain hacktivist or cybercriminal groups, aiming to justify their operations under a specific ideology or perceived greater good.
This is not the first time Cyber Serp has claimed a high-profile cyberattack. Just a month prior to the CERT-UA impersonation, the group took responsibility for an alleged breach of Ukrainian cybersecurity company Cipher. Cyber Serp claimed to have obtained a complete dump of Cipher’s servers, including client databases and source code for their proprietary CIPS products. Cipher, in its official response, acknowledged that an employee’s credentials at one of its technology partners had been compromised. However, they maintained that their core infrastructure remained operational and secure, asserting that the infected user’s access was limited to a single project that did not contain sensitive data. This incident, regardless of the full extent of its impact, established Cyber Serp as a recurring and audacious threat actor within the Ukrainian cyber landscape, consistently targeting sensitive organizations.
The Troubling Shadow of Artificial Intelligence
One of the most concerning revelations from CERT-UA’s investigation is the strong indication that the bogus website "cert-ua[.]tech" was likely generated with the assistance of artificial intelligence (AI) tools. This suspicion is reinforced by the presence of a peculiar comment within the HTML source code: "С Любовью, КИБЕРСЕРП," which translates from Cyrillic to "With Love, CYBER SERP." This digital signature, embedded within the code, not only attributes the site to Cyber Serp but also implicitly points towards a modern development workflow potentially incorporating AI.
The integration of AI into phishing campaigns represents a significant leap in the capabilities of threat actors. AI can drastically lower the bar for creating highly convincing phishing lures, bespoke landing pages, and even crafting email content that perfectly mimics the tone and style of legitimate organizations. For instance, large language models (LLMs) can generate grammatically flawless and contextually relevant phishing emails at scale, making it much harder for recipients to spot irregularities. AI can also assist in generating website layouts, content, and even code snippets, accelerating the development of convincing fake sites. This allows threat actors, even those with limited technical skills, to produce sophisticated deceptive infrastructure with unprecedented speed and efficiency. The psychological impact of AI-generated content is also profound; as AI-driven phishing becomes more prevalent, the average user’s ability to discern genuine communications from malicious ones will be severely challenged, eroding trust in digital communication channels.
Broader Implications and the Ukrainian Cyber Landscape

This attack serves as a stark reminder of the persistent and evolving cyber threats faced by Ukraine, particularly in the context of ongoing geopolitical tensions. Impersonating a national cybersecurity agency like CERT-UA is a particularly insidious tactic, as it undermines the very trust essential for effective national cybersecurity defense. When citizens and organizations cannot reliably distinguish communications from their protectors, it creates confusion, fear, and opens doors for widespread compromise.
The targeting of a diverse range of sectors—from government and healthcare to education and finance—illustrates a comprehensive strategy to infiltrate various pillars of Ukrainian society. A successful breach in any of these areas could yield intelligence, financial gain, or facilitate disruptive operations. For state organizations, it risks compromising national security data; for medical centers, patient information and operational integrity; for financial institutions, economic stability; and for educational institutions, intellectual property and the personal data of students and staff.
While CERT-UA reported limited success in this specific campaign, the incident underscores several critical implications:
- Erosion of Trust: Impersonating official cybersecurity bodies damages public trust, making future legitimate alerts and advisories less effective.
- Scalability of Attacks: The alleged targeting of 1 million mailboxes, whether fully successful or not, demonstrates the potential for mass-scale attacks facilitated by modern tools and potentially AI.
- Sophistication of Adversaries: UAC-0255/Cyber Serp’s use of Go-based malware, WebSockets, multiple persistence mechanisms, and suspected AI generation points to a highly capable and adaptive threat actor.
- Ongoing Cyber Warfare: The incident is part of a broader pattern of cyber activity targeting Ukraine, often attributed to state-sponsored actors or ideologically motivated groups. The "Cyber Serp" group’s self-identification as "cyber-underground operatives from Ukraine" adds a layer of complexity, making attribution and motivation analysis more challenging.
Recommendations and Future Outlook
In response to such evolving threats, organizations and individuals must adopt a multi-layered security approach. Key preventative measures include:
- Enhanced Email Security: Implementing advanced email filtering, anti-phishing solutions, and DMARC, SPF, and DKIM protocols to authenticate legitimate senders and detect spoofed emails.
- Employee Training: Regular and updated cybersecurity awareness training, focusing on identifying phishing attempts, recognizing suspicious links and attachments, and verifying the authenticity of communications from official sources, especially those purporting to be security advisories.
- Multi-Factor Authentication (MFA): Enabling MFA for all accounts, particularly for accessing sensitive systems, significantly reduces the impact of compromised credentials.
- Endpoint Detection and Response (EDR): Deploying EDR solutions to monitor endpoints for malicious activity, detect RATs like AGEWHEEZE, and enable rapid incident response.
- Proactive Threat Intelligence: Subscribing to and acting upon threat intelligence from agencies like CERT-UA to stay informed about emerging threats and indicators of compromise (IoCs).
- Regular Software Updates: Ensuring all operating systems and applications are regularly patched and updated to fix known vulnerabilities that malware might exploit.
The incident involving UAC-0255 and AGEWHEEZE serves as a critical case study in the current cyber threat landscape. The suspected involvement of AI in generating attack infrastructure signifies a new frontier in cyber warfare, where the lines between human and machine-driven malicious activity blur. As cyber adversaries continue to innovate, the imperative for robust defenses, continuous vigilance, and international collaboration in cybersecurity has never been greater, particularly for nations like Ukraine that remain at the forefront of geopolitical cyber conflicts. The ability of CERT-UA to swiftly identify and disclose this campaign, despite being its target, reinforces its crucial role in protecting Ukraine’s digital sovereignty.