A Network Policy Server (NPS) serves as a critical infrastructure component for organizations seeking to establish and rigorously enforce policies governing network access. Its fundamental role is to ensure that only authenticated and authorized users and devices can connect to and utilize network resources, thereby playing a pivotal role in centralized authentication, authorization, and accounting (AAA) for all network participants. Essentially, NPS is Microsoft’s robust implementation of a Remote Authentication Dial-In User Service (RADIUS) server and proxy within the Windows Server operating system, making it an indispensable tool for comprehensive network management and security.
The Imperative of Network Security and Policy Management in the Digital Age
In an era defined by increasing reliance on digital infrastructure for business operations, data exchange, and global communication, networks and their underlying servers have become primary targets for malicious actors. The escalating sophistication of cyber threats necessitates the implementation of robust network security measures and meticulous policy management. Without these safeguards, organizations face significant risks, including data breaches, service disruptions, financial losses, and reputational damage.
The importance of network security and policy management can be distilled into several key areas:
- Protection Against Unauthorized Access: Strong security protocols prevent unauthorized individuals or entities from gaining access to sensitive data or critical network functions.
- Data Confidentiality and Integrity: Ensuring that data remains confidential and unaltered is paramount. Unauthorized access or modification can have severe consequences.
- Service Availability: Maintaining the continuous availability of network services is crucial for business continuity. Cyberattacks can cripple operations by rendering networks inaccessible.
- Regulatory Compliance: Many industries are subject to strict regulations regarding data protection and network security. Effective policy management is essential for meeting these compliance requirements.
- Resource Optimization: Clearly defined policies ensure that network resources are utilized efficiently and appropriately, preventing overuse and bottlenecks.
- Auditing and Accountability: Comprehensive logging and accounting mechanisms provide a clear audit trail, enabling the identification of security incidents and the accountability of users.
Understanding the RADIUS Protocol: The Foundation of NPS
To fully appreciate the function and importance of NPS, it is essential to first understand the RADIUS protocol. RADIUS (Remote Authentication Dial-In User Service) is a widely adopted networking protocol that provides comprehensive and centralized AAA management for users accessing network services. Developed in 1991, RADIUS has become a de facto standard for network access servers, playing a pivotal role in controlling and managing access to networks.
The RADIUS protocol operates on three core principles, collectively known as AAA:
Authentication: Verifying Identity
Authentication is the foundational step in the AAA process, involving the verification of a user’s identity. When a user or device attempts to connect to a network, they are required to present credentials, such as a username and password, a digital certificate, or multi-factor authentication tokens. The RADIUS server then compares these provided credentials against its authorized user database. Successful validation confirms the user’s legitimate identity, ensuring that only verified individuals can proceed to the next stage of access.
Authorization: Defining Access Privileges
Once a user has been successfully authenticated, the next critical step is authorization. This process determines the specific resources and services that an authenticated user is permitted to access and the actions they can perform within the network. For instance, an IT administrator will typically have broader access privileges than a standard employee. RADIUS servers manage these granular permissions, ensuring that users are only granted access to resources commensurate with their role and responsibilities. This principle of least privilege is fundamental to a secure network architecture.
Accounting: Tracking Network Usage
The final component of AAA is accounting, which involves meticulously tracking and recording user activity and resource consumption on the network. This includes monitoring connection times, the specific services accessed, data transfer volumes, and the overall duration of network sessions. The accounting data generated by RADIUS servers is invaluable for various purposes, including billing, capacity planning, auditing network usage patterns, and forensic analysis in the event of a security incident.
The Functionality of RADIUS Servers
RADIUS operates on a client-server model. In this architecture, the RADIUS client is typically a network access device, such as a wireless access point, a VPN server, a dial-up server, or a network switch. When a user attempts to connect through one of these devices, the client intercepts the connection request and forwards the user’s credentials and connection details to the RADIUS server.
The RADIUS server then processes this request, consulting its authentication databases and policy configurations. Based on this evaluation, it either grants or denies access and communicates its decision back to the RADIUS client. If access is granted, the server may also provide specific configuration parameters to the client, dictating the terms of the user’s session.
Key features and functionalities of RADIUS servers include:
- Centralized AAA Management: Consolidating authentication, authorization, and accounting functions into a single server simplifies management and enhances security.
- Protocol Support: RADIUS supports various authentication methods, including PAP, CHAP, EAP, and MS-CHAP, offering flexibility in credential verification.
- Policy Enforcement: RADIUS servers allow administrators to define intricate policies that dictate access based on user groups, time of day, location, and other attributes.
- Scalability: RADIUS-based systems can be scaled to accommodate large numbers of users and devices, making them suitable for enterprises of all sizes.
- Interoperability: As an industry standard, RADIUS is supported by a wide range of hardware and software vendors, promoting interoperability within diverse network environments.
The Purpose and Role of Network Policy Server (NPS)
Within an organization’s network infrastructure, a Network Policy Server (NPS) serves as a critical element, primarily functioning as Microsoft’s robust implementation of a RADIUS server and proxy. The primary objective of NPS is to centralize and streamline the authentication, authorization, and accounting (AAA) processes for all users and devices attempting to access the network. This centralization significantly enhances both network security and management efficiency.
NPS plays a multifaceted role in modern network management:
Centralized Authentication and Authorization: The First Line of Defense
Centralized authentication ensures that every user and device attempting to connect to the network undergoes a rigorous verification process before being granted access. This is the first and most crucial step in preventing unauthorized access and protecting network resources. Authorization, which follows successful authentication, defines precisely what resources and services an authenticated entity is permitted to use.

NPS manages these critical functions by:
- Validating Credentials: NPS verifies user identities against Active Directory or other credential stores.
- Enforcing Access Policies: Based on predefined policies, NPS determines whether to grant or deny access to the network.
- Granular Permissions: NPS allows for the creation of detailed authorization policies, granting specific levels of access to different user groups or individual users.
- Dynamic Access Control: NPS can dynamically adjust access privileges based on various conditions, such as the network security posture of a connecting device.
Accounting and Compliance: Ensuring Transparency and Accountability
The accounting function within NPS is vital for auditing and monitoring network usage. It involves the systematic tracking and logging of all user activities and resource consumption. This data is indispensable for maintaining compliance with regulatory standards and for understanding network behavior.
NPS aids in ensuring compliance by:
- Detailed Logging: NPS records comprehensive details of connection attempts, successful authentications, authorization decisions, and session termination.
- Audit Trails: The generated logs provide an irrefutable audit trail, essential for demonstrating compliance with regulations like HIPAA, GDPR, or PCI DSS.
- Usage Analysis: Accounting data allows administrators to analyze network usage patterns, identify potential security threats, and optimize resource allocation.
- Reporting: NPS can generate reports on network access and usage, facilitating compliance audits and providing insights for network management.
Policy-Based Network Management: Tailoring Access to Organizational Needs
Policy-based network management, a core capability of NPS, empowers administrators to define and enforce specific network access policies. These policies are the rules that govern how users and devices connect to and interact with the network, allowing for tailored security and usage parameters aligned with an organization’s unique requirements.
NPS facilitates the creation of these policies by enabling administrators to:
- Define Conditions: Policies can be based on a wide array of conditions, including user group membership, time of day, day of the week, location, device health status, and the type of network access being requested.
- Set Connection Settings: Administrators can specify connection properties such as encryption methods, idle timeout values, and bandwidth limitations.
- Grant or Deny Access: Policies can be configured to grant access, deny access, or prompt for further authentication based on the defined conditions.
- Integration with Network Access Protection (NAP): NPS can integrate with Microsoft’s Network Access Protection (NAP) framework to enforce health policies, ensuring that only compliant and secure devices can join the network.
Key Benefits of Implementing NPS
The adoption of NPS within an organization’s network infrastructure yields a multitude of benefits that significantly enhance both security posture and operational efficiency. These advantages make NPS an invaluable component for organizations aiming to optimize their network management practices and fortify their digital defenses.
- Enhanced Security: By centralizing authentication and authorization, NPS drastically reduces the attack surface and prevents unauthorized access to sensitive network resources. The enforcement of granular policies ensures that users only have access to what they need, minimizing the risk of internal threats and accidental data exposure.
- Streamlined Administration: NPS consolidates AAA functions into a single, manageable platform. This eliminates the need for disparate authentication systems and simplifies the process of user onboarding, policy updates, and access control management.
- Improved Network Performance: Effective policy management through NPS can prevent network congestion by controlling bandwidth usage and prioritizing critical traffic. This leads to a more stable and responsive network experience for all users.
- Cost Savings: By reducing the risk of security breaches and improving operational efficiency, NPS contributes to significant cost savings. Preventing data loss, avoiding downtime, and streamlining administrative tasks all translate to tangible financial benefits.
- Scalability and Flexibility: NPS is designed to scale with the needs of an organization. It can support a growing number of users and devices and adapt to evolving network requirements and security protocols.
- Compliance Adherence: The robust accounting and logging capabilities of NPS are crucial for meeting the stringent compliance requirements of various industries. It provides the necessary audit trails and reporting to demonstrate adherence to regulatory standards.
- Centralized Control: NPS provides a single point of control for all network access policies, giving administrators a clear overview and the ability to implement changes uniformly across the network.
- Support for Wireless and VPN Access: NPS is particularly effective in managing secure access for wireless networks (Wi-Fi) and Virtual Private Networks (VPNs), which are common entry points for external access.
The Three Distinct Roles of NPS
NPS is a versatile tool that fulfills three primary roles within a network environment, each contributing to its comprehensive network management capabilities:
1. NPS as a RADIUS Server
In its most fundamental role, NPS functions as a RADIUS server. It is responsible for processing authentication and authorization requests originating from network access servers. When a user or device attempts to connect to the network, the access server forwards the request to NPS. NPS then evaluates the request against its configured user accounts, security groups, and network policies. Based on this evaluation, it determines whether to grant or deny access and communicates this decision back to the access server. This function is critical for securing various network access points, including VPNs, wireless access points, and dial-up connections, ensuring that only legitimate users gain entry to the network.
2. NPS as a RADIUS Proxy
In more complex or distributed network architectures, NPS can operate as a RADIUS proxy. In this capacity, NPS does not perform the actual authentication and authorization itself but instead forwards these requests to other RADIUS servers located elsewhere in the network. This is particularly useful when an organization has multiple RADIUS servers, perhaps serving different geographical locations or different types of network services. As a proxy, NPS can also perform load balancing, distributing incoming requests across multiple RADIUS servers to prevent any single server from becoming a bottleneck. Furthermore, it can facilitate failover mechanisms, ensuring that if one RADIUS server becomes unavailable, requests are automatically rerouted to a functioning server, thus maintaining service continuity.
3. NPS as a Network Policy Server
This role is arguably the most defining function of NPS. As a network policy server, NPS is the engine that manages and enforces the rules governing network access. It allows administrators to create sophisticated policies that dictate precisely under what conditions users and devices are granted or denied network access. These policies can be highly granular, taking into account factors such as user group membership, the time of day, the specific wireless network being accessed, or even the security compliance status of a connecting device. This capability provides administrators with a powerful tool for precisely controlling network access, ensuring that security policies are consistently applied and that the network operates according to the organization’s specific security and operational requirements.
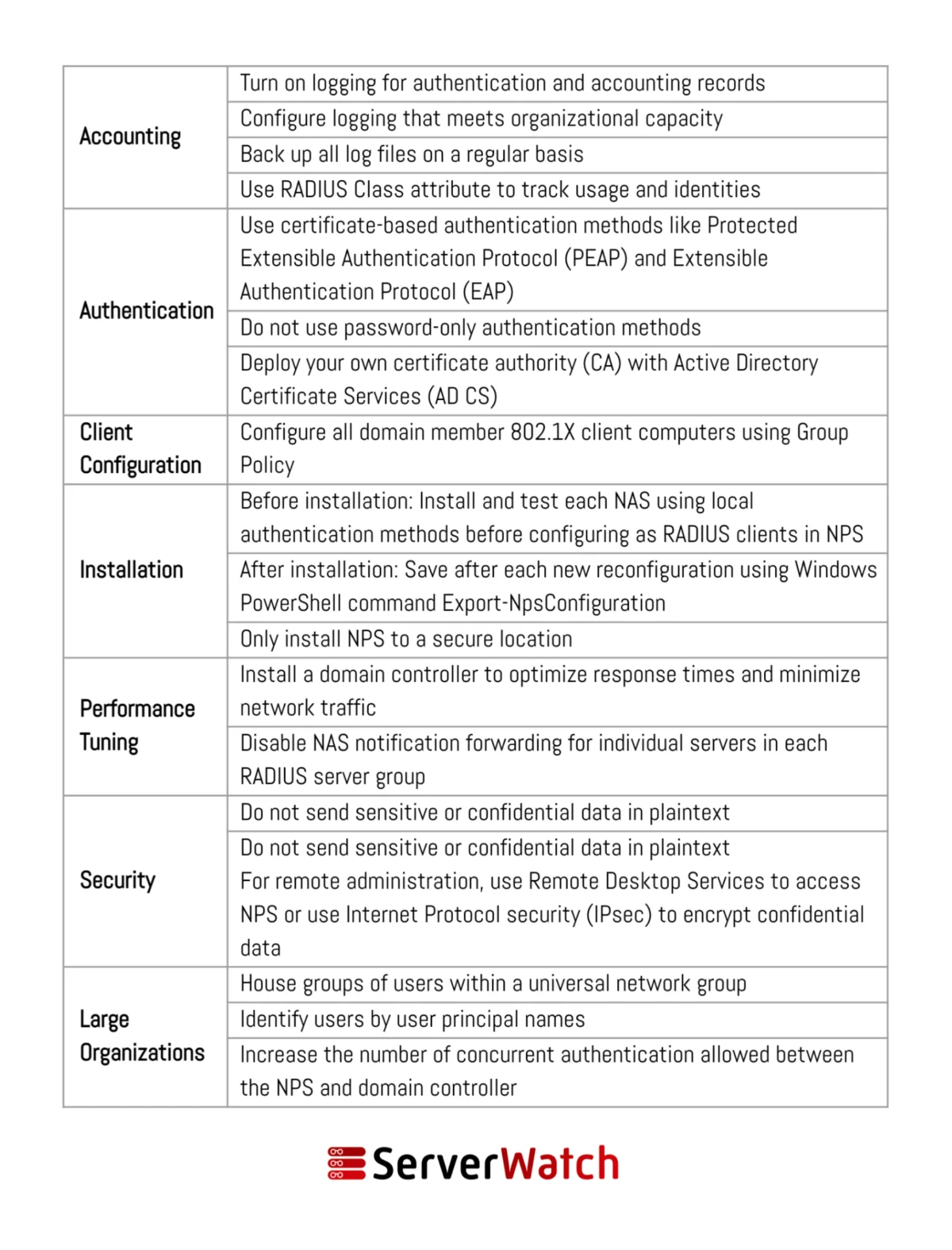
Implementing NPS: Best Practices for Optimal Performance and Security
To ensure that NPS operates efficiently, securely, and in alignment with an organization’s network management objectives, adhering to certain best practices is crucial. These recommendations, often provided by Microsoft and industry experts, are designed to maximize the benefits of NPS while minimizing potential risks.
- Secure NPS Communication: Employ strong encryption protocols, such as IPsec, to secure communication between NPS servers and RADIUS clients. This prevents the interception and tampering of authentication and accounting data.
- Regularly Update NPS: Keep the NPS server software and underlying operating system up-to-date with the latest security patches and updates. This is vital for addressing newly discovered vulnerabilities.
- Implement Strong Authentication Methods: Move beyond basic password authentication. Utilize multi-factor authentication (MFA) whenever possible to significantly enhance security by requiring multiple forms of verification. EAP-TLS with smart cards or certificates is a highly secure option.
- Leverage Active Directory Integration: Integrate NPS with Active Directory for centralized user and group management. This simplifies policy creation and ensures that access controls are consistent with existing directory structures.
- Define Clear and Granular Policies: Develop well-defined network access policies that are specific to different user groups, device types, and access scenarios. Avoid overly broad policies that could inadvertently grant excessive permissions.
- Utilize Connection Request Policies: Configure connection request policies to route authentication requests appropriately, especially in environments with multiple NPS servers or when using NPS as a proxy.
- Monitor NPS Logs Regularly: Establish a routine for regularly reviewing NPS event logs. This proactive monitoring can help detect suspicious activity, identify policy misconfigurations, and troubleshoot access issues. Consider forwarding logs to a centralized Security Information and Event Management (SIEM) system for enhanced analysis and correlation.
- Implement RADIUS Client Registration: Ensure that all RADIUS clients (access points, VPN servers, etc.) are properly registered with the NPS server, including sharing strong, unique RADIUS shared secrets.
- Consider Redundancy and High Availability: For critical network services, implement redundant NPS servers or configure NPS in a clustered configuration to ensure continuous availability in case of server failure.
- Perform Regular Audits and Testing: Periodically audit NPS configurations and policies to ensure they remain relevant and effective. Conduct penetration testing and vulnerability assessments to identify potential weaknesses.
- Document NPS Configuration: Maintain comprehensive documentation of all NPS configurations, policies, and network topology. This documentation is invaluable for troubleshooting, disaster recovery, and onboarding new administrators.
The Bottom Line: NPS as an Indispensable Tool for Modern Network Management
The Network Policy Server (NPS) has undeniably emerged as an indispensable tool in the arsenal of modern network administrators. It provides a robust, flexible, and highly effective solution for ensuring the security and efficiency of network operations. By integrating NPS into an organization’s network infrastructure, businesses can achieve significant improvements in security through the rigorous enforcement of access policies. Simultaneously, it streamlines administrative tasks, leading to a more efficient and manageable network environment.
In the face of evolving cyber threats and the ever-increasing complexity of digital networks, the ability to precisely control who and what can access network resources is paramount. NPS delivers this control, empowering organizations to build more secure, resilient, and compliant network infrastructures. By diligently adhering to best practices in its deployment and management, organizations can significantly mitigate the risks associated with network security and ensure a seamless, uninterrupted operational flow, thereby safeguarding their valuable data and maintaining the trust of their users and customers.
For organizations looking to further enhance their NPS functionality and performance, exploring specialized tools can be beneficial. A review of the best free RADIUS server testing and monitoring tools, selected and reviewed by experts, can provide valuable insights into optimizing NPS operations and ensuring its continuous effectiveness.