A significant breach has once again impacted Checkmarx, a prominent application security testing (AST) vendor, with the company confirming that a malicious, modified version of its Jenkins AST plugin was published to the official Jenkins Marketplace. This incident, disclosed on May 11, 2026, marks the latest in a series of sophisticated supply chain attacks orchestrated by the notorious cybercrime group, TeamPCP, raising urgent concerns about the resilience of software development ecosystems and the persistent threat actors targeting critical infrastructure components. The compromise necessitates immediate action from organizations utilizing the affected plugin, highlighting the escalating challenges in securing the increasingly interconnected software supply chain.
Details of the Jenkins AST Plugin Compromise
The core of the current incident revolves around the Checkmarx Jenkins AST plugin, a vital tool that integrates Checkmarx’s comprehensive application security scanning capabilities directly into the continuous integration and continuous delivery (CI/CD) pipelines managed by Jenkins. Jenkins, as one of the most widely adopted open-source automation servers, serves as the backbone for countless development and deployment workflows globally. Its plugins extend its functionality, making them attractive targets for adversaries seeking to inject malicious code into the heart of software development.
Checkmarx issued a public advisory over the weekend, urging users to verify their plugin versions. Specifically, the company stated, "If you are using Checkmarx Jenkins AST plugin, you need to ensure that you are using the version 2.0.13-829.vc72453fa_1c16 that was published on December 17, 2025 or previously." This directive implies that any version published after December 17, 2025, and prior to the latest legitimate release, could potentially be the compromised variant. The cybersecurity firm did not immediately disclose the specific malicious version number or the precise mechanism through which the tainted plugin found its way onto the Jenkins Marketplace, a central repository for Jenkins plugins.
As of the time of reporting, Checkmarx has moved swiftly to publish a new, verified version, 2.0.13-848.v76e89de8a_053, on both its GitHub repository and the Jenkins Marketplace. However, its incident update initially indicated that it was "in the process of publishing a new version of this plugin," suggesting a rapid response to mitigate the threat and replace the compromised artifact. The lack of immediate detail regarding the attack vector underscores the complexity and potential stealth of such supply chain infiltrations, where adversaries often exploit overlooked vulnerabilities or compromised credentials within development or deployment environments.
The Broader Campaign: TeamPCP’s Persistent Assaults on Checkmarx
This discovery is not an isolated event but rather the latest installment in a relentless campaign by TeamPCP against Checkmarx. The cybercrime group has demonstrated a sophisticated understanding of software development pipelines and an alarming persistence in exploiting vulnerabilities within these environments. Just a couple of weeks prior to the Jenkins plugin incident, TeamPCP was linked to a series of high-profile compromises targeting Checkmarx’s development assets. These included the infiltration of its KICS (Kubernetes Infrastructure as Code Security) Docker image, two Visual Studio Code (VS Code) extensions, and a GitHub Actions workflow. The objective of these earlier breaches was consistent: to inject credential-stealing malware designed to harvest sensitive developer secrets.
The cascading effect of TeamPCP’s activities became evident when the compromise of Checkmarx’s assets subsequently led to the brief compromise of the Bitwarden CLI npm package. Bitwarden, a popular open-source password manager, saw its command-line interface (CLI) tool briefly serving a similar stealer, capable of siphoning a wide array of developer credentials and sensitive information. This interconnectedness highlights the perilous nature of supply chain attacks, where a breach in one component can ripple through the entire ecosystem, affecting numerous downstream users and services.
TeamPCP’s campaign against the software supply chain has been active since at least March 2026, characterized by a sprawling strategy that leverages the inherent trust embedded within development processes. By targeting development tools, repositories, and automation platforms, the group aims to propagate its malware widely and expand its illicit reach, potentially gaining access to intellectual property, sensitive data, or financial assets of organizations that rely on the compromised software.
Chronology of Attacks and Technical Insights
The timeline of TeamPCP’s campaign against Checkmarx and its ripple effects paints a concerning picture:

- March 2026: TeamPCP initiates its widespread campaign, exploiting trust in the software supply chain. Initial attacks against Checkmarx are identified, targeting its GitHub repositories and potentially internal systems.
- Late March / Early April 2026: Compromise of Checkmarx’s KICS Docker image, two VS Code extensions, and a GitHub Actions workflow. These components are weaponized with credential-stealing malware.
- Mid-April 2026: The compromise of Checkmarx’s development infrastructure leads to the brief infiltration of the Bitwarden CLI npm package, subsequently distributing credential-stealing malware to its users.
- December 17, 2025: The last known safe version of the Checkmarx Jenkins AST plugin (2.0.13-829.vc72453fa_1c16) is published, according to Checkmarx’s advisory, establishing a critical baseline for users.
- Between December 17, 2025, and Early May 2026: The malicious version of the Jenkins AST plugin is surreptitiously introduced and published to the Jenkins Marketplace.
- May 11, 2026: Checkmarx publicly confirms the compromise of its Jenkins AST plugin, advising users to downgrade or update to a verified version. Simultaneously, security researchers begin to share details of the intrusion.
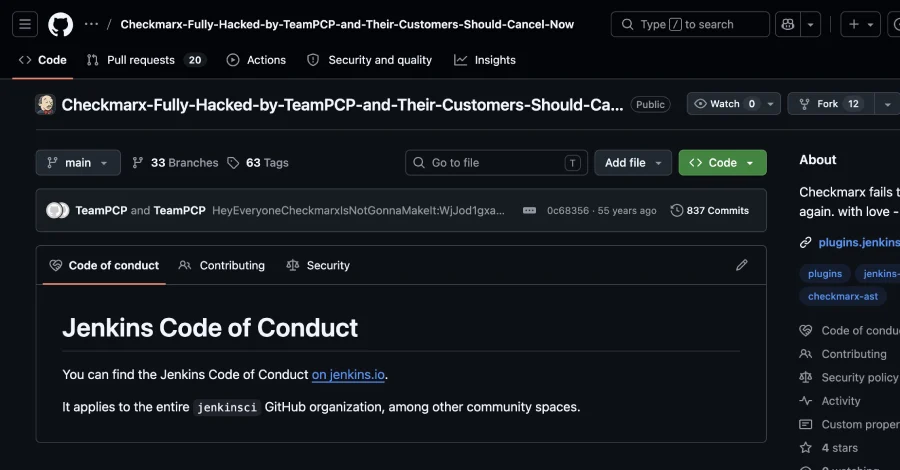
Security researcher Adnan Khan and intelligence firm SOCRadar provided crucial insights into the technical aspects of the Jenkins plugin compromise. They reported that TeamPCP allegedly gained unauthorized access to the plugin’s GitHub repository. Following this access, the group defaced the repository, renaming it to "Checkmarx-Fully-Hacked-by-TeamPCP-and-Their-Customers-Should-Cancel-Now." This aggressive act of defacement was accompanied by an updated repository description that read: "Checkmarx fails to rotate secrets again. with love – TeamPCP."
This brazen messaging suggests that the attack might not solely be for financial gain but also carries an element of public shaming or demonstrating superior hacking capabilities. More importantly, the explicit mention of "fails to rotate secrets again" points to a critical vulnerability in Checkmarx’s post-incident remediation strategies following the earlier March breaches.
Implications for Software Supply Chain Security
The recurrence of breaches impacting Checkmarx, especially within such a short timeframe, raises serious questions about the efficacy of current cybersecurity practices within the software development ecosystem. Supply chain attacks, which target vulnerabilities in the software development and delivery process, are among the most insidious threats facing organizations today. By compromising a trusted component, attackers can distribute malware to a vast number of downstream users without directly attacking each one.
The compromise of a Jenkins plugin is particularly concerning because Jenkins is deeply embedded in the CI/CD pipeline, a critical juncture where code is built, tested, and deployed. A malicious plugin can:
- Inject Backdoors: Introduce vulnerabilities or backdoors directly into the compiled software artifacts.
- Steal Credentials: Access and exfiltrate sensitive credentials, API keys, and other secrets used during the build process.
- Tamper with Builds: Modify build scripts, introduce malicious dependencies, or alter compiled code without detection.
- Disrupt Operations: Cause outages or instability by corrupting build processes.
The incident underscores the urgent need for organizations to adopt more robust DevSecOps practices, emphasizing security at every stage of the software development lifecycle. This includes rigorous vetting of all third-party components, implementing multi-factor authentication for all development accounts, employing least privilege access controls, and continuously monitoring for unusual activity in CI/CD environments and code repositories.
Expert Analysis and Recommendations
SOCRadar’s analysis of the repeated breaches is particularly damning: "The fact that TeamPCP is back inside Checkmarx systems just weeks later points to one of two possibilities: either the initial remediation was incomplete and credentials were not fully rotated, or the group retained a foothold that wasn’t identified during the March response." This assessment highlights a fundamental challenge in incident response: the difficulty of completely eradicating persistent threat actors who may establish multiple entry points or maintain hidden access.
The cybersecurity community universally stresses the importance of thorough post-breach forensics and comprehensive remediation efforts. A "second Checkmarx incident happening this soon suggests the group is actively watching for re-entry points, testing the depth of past remediations, and capitalizing on any gaps," SOCRadar added. This indicates that TeamPCP is not merely opportunistic but highly strategic and persistent, actively probing for weaknesses and exploiting any oversight in security measures.
For users of the Checkmarx Jenkins AST plugin, the immediate recommendation is to verify their plugin version against the advisory. Organizations should:
- Audit Plugin Versions: Immediately check the installed version of the Checkmarx Jenkins AST plugin.
- Downgrade or Update: If a malicious version is identified, downgrade to the specified safe version (2.0.13-829.vc72453fa_1c16 or earlier) or update to the newly released legitimate version (2.0.13-848.v76e89de8a_053).
- Scan for Compromise: Perform thorough scans of their CI/CD environments and any artifacts built during the period the malicious plugin was active, looking for signs of compromise, backdoors, or credential exfiltration.
- Rotate Credentials: Assume that any credentials accessible within the affected Jenkins environment during the compromise period may have been exposed and initiate a comprehensive credential rotation.
- Enhance Monitoring: Implement enhanced logging and monitoring for all CI/CD activities, especially those related to plugin installations, updates, and repository access.
- Implement Zero Trust: Adopt zero-trust principles, verifying every access request and minimizing implicit trust, even within internal networks and development pipelines.
Conclusion and Outlook
The repeated successful attacks by TeamPCP against a leading security vendor like Checkmarx serve as a stark reminder that no organization, regardless of its security posture, is immune to sophisticated and persistent threat actors. The incident underscores the critical importance of a multi-layered security approach, continuous vigilance, and robust incident response capabilities, particularly in the complex and interconnected realm of software supply chains. As development environments become increasingly automated and integrated, securing every link in the chain becomes paramount. The cybersecurity industry, developers, and users alike must collectively adapt and evolve their defenses to counter the escalating threat landscape posed by groups like TeamPCP, ensuring that the foundational trust in software development remains intact. The ongoing saga between Checkmarx and TeamPCP will undoubtedly serve as a crucial case study in the evolving battle for supply chain integrity.