The problem manifested when a user inquired about returning a laptop purchased three weeks prior….

Advanced SparkCat Malware Resurfaces on App Stores, Posing Renewed Threat to Global Cryptocurrency Holders
Cybersecurity researchers have sounded the alarm over a sophisticated new version of the SparkCat malware,…
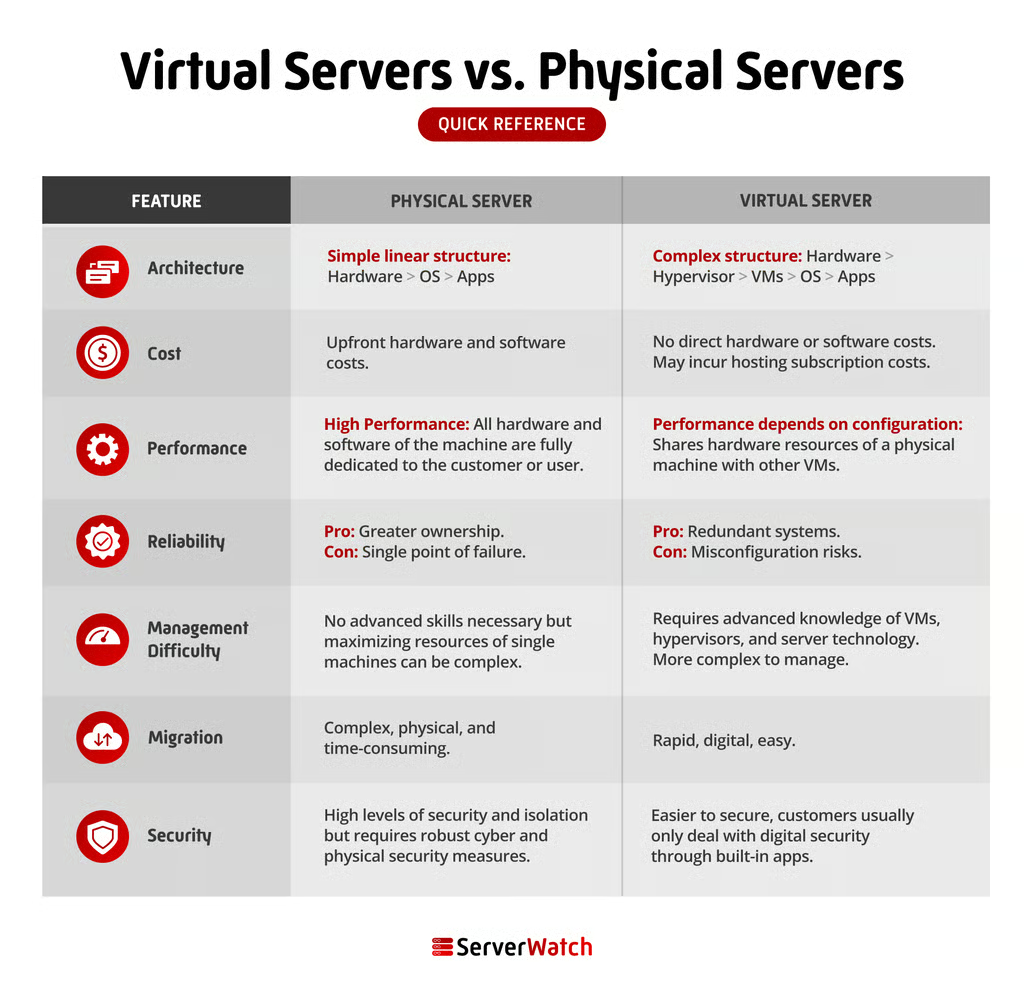
Understanding the Core Differences Between Virtual and Physical Servers
All digital data and systems, from cloud-based platforms and personal online accounts to corporate websites…

Securing the Modular Future: Architecting Trust and Identity in the Emerging Chiplet Ecosystem
As the semiconductor industry pivots from monolithic System-on-Chip (SoC) designs toward modular, heterogeneous chiplet architectures,…
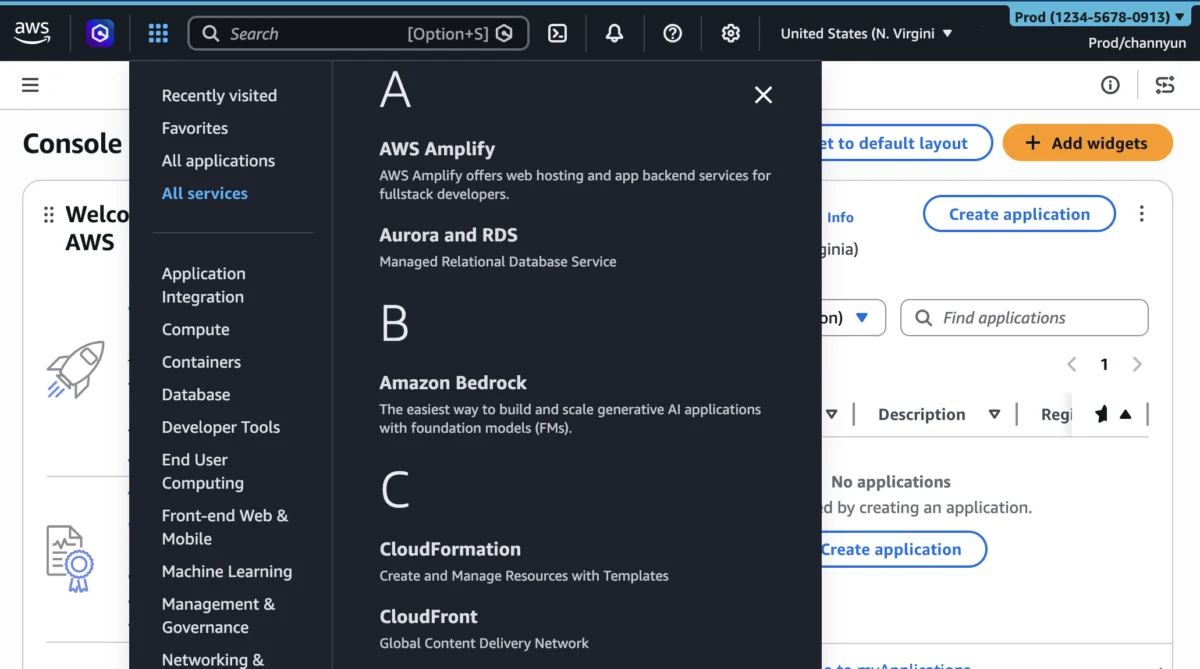
AWS Enhances Management Console with Advanced User Experience Customization for Regions and Services.
Amazon Web Services (AWS) today announced a significant expansion of its User Experience Customization (UXC)…

Samsung Galaxy Enhances Professional Videography with Direct External Storage Recording
The escalating demand for high-fidelity video capture on mobile devices has pushed the boundaries of…

Homey Pro Review: A Powerful Smart Home Hub with Significant Potential, But Device Compatibility is Key
The smart home landscape is continuously evolving, with new devices and hubs vying for a…

Microsoft’s Top Developers Warn Agentic AI Risks Hollowing Out Talent Pipeline
Two of Microsoft’s most influential developers have issued a stark warning to organizations enthusiastically embracing…

The Latest ThreatsDay Bulletin: Unpacking the Subtle Shifts in the Modern Cyber Landscape
The latest ThreatsDay Bulletin serves as an unfiltered, critical digest of the most pressing cyber…

The Top Virtual Machine Software for Windows: A Comprehensive Guide
Virtual machine (VM) software for Windows is a fundamental technology that empowers users to create…

