A sophisticated and persistent phishing campaign, active since at least April 2025, has been systematically targeting a wide array of organizations across multiple vectors, leveraging legitimate Remote Monitoring and Management (RMM) software to establish resilient and enduring remote access to compromised hosts. This evolving threat underscores a troubling trend in cyber warfare where adversaries increasingly "live off the land" by weaponizing trusted tools to bypass conventional security defenses.
Dubbed VENOMOUS#HELPER by cybersecurity firm Securonix, this malicious activity has, to date, impacted over 80 organizations, with a significant majority located within the United States. The campaign exhibits notable overlaps with previously identified clusters, including those meticulously tracked by Red Canary and Sophos, the latter having designated a related activity with the moniker STAC6405. While definitive attribution regarding the threat actor(s) behind VENOMOUS#HELPER remains elusive, cybersecurity analysts posit that the operational patterns and objectives strongly align with those of a financially motivated Initial Access Broker (IAB) or, more ominously, a precursor operation paving the way for ransomware deployment. The sustained nature of the campaign, spanning over a year, indicates a well-resourced and highly adaptive adversary.
The Strategic Abuse of Legitimate RMM Tools
The core ingenuity of the VENOMOUS#HELPER campaign lies in its strategic exploitation of reputable RMM software, specifically customized versions of SimpleHelp and ConnectWise ScreenConnect. These tools, designed for legitimate IT administration and remote support, are installed by unsuspecting victims who believe they are interacting with official documents or services. This method presents a significant challenge for traditional security mechanisms, as the installed software is inherently legitimate and signed by reputable vendors, making it difficult for signature-based antivirus and standard endpoint controls to flag as malicious.
As Securonix researchers Akshay Gaikwad, Shikha Sangwan, and Aaron Beardslee detailed in a comprehensive report shared with The Hacker News, "In this case, customized SimpleHelp and ScreenConnect RMMs are used to bypass defenses as they are legitimately installed by the unsuspecting victim." This approach effectively turns an organization’s own legitimate infrastructure against itself, blurring the lines between authorized and unauthorized activity and significantly complicating detection and response efforts.

Beyond merely exploiting the legitimacy of these tools, the VENOMOUS#HELPER operators demonstrate a sophisticated understanding of operational resilience. The deployment of both SimpleHelp and ConnectWise ScreenConnect within compromised environments is a clear indicator of an attempt to forge a "redundant dual-channel access architecture." This strategic redundancy ensures continued operational capability even if one of the RMM tools is detected, blocked, or removed by security teams. Should an organization successfully identify and mitigate the SimpleHelp connection, the attackers retain a fallback through ScreenConnect, enabling them to maintain persistence and continue their activities without significant disruption. This multi-pronged approach to access underscores the threat actors’ commitment to long-term presence within target networks.
Anatomy of the Phishing Attack: Social Engineering and Evasion
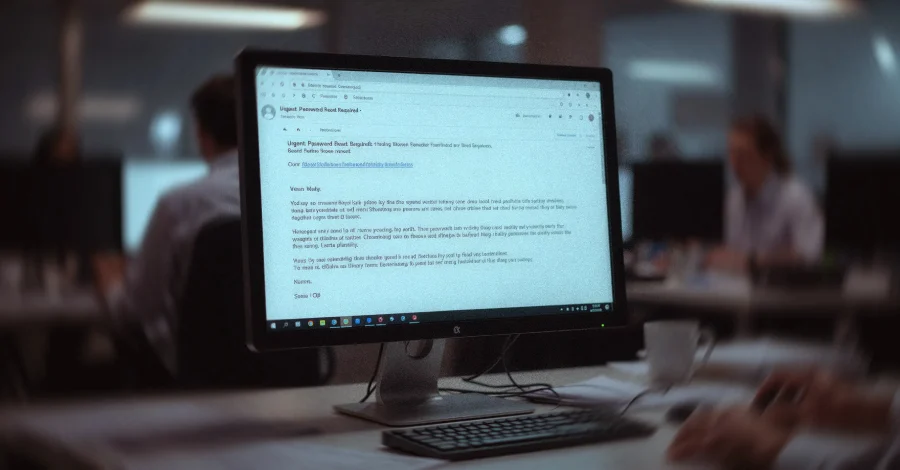
The initial vector for the VENOMOUS#HELPER campaign is a meticulously crafted phishing email, designed to impersonate the U.S. Social Security Administration (SSA). This choice of impersonation is particularly potent, as communications from governmental financial institutions often carry a high degree of perceived authority and urgency, compelling recipients to act without critical scrutiny. The emails typically instruct recipients to verify their email address or download a purported SSA statement by clicking on an embedded link.
The path to compromise is engineered with several layers of evasion. The initial link within the phishing email does not lead directly to a malicious payload. Instead, it directs victims to a legitimate, albeit compromised, Mexican business website (e.g., "gruta.com[.]mx"). This tactic is crucial for bypassing sophisticated email spam filters and security gateways that are designed to flag suspicious or unknown domains. By routing victims through a seemingly innocuous and trusted domain, the attackers effectively mask their true intent and increase the likelihood of the email reaching the recipient’s inbox and the link being clicked.
Once the victim clicks the initial link, they are subsequently redirected to a second attacker-controlled domain (e.g., "server.cubatiendaalimentos.com[.]mx") from which the "SSA statement" – in reality, an executable file – is downloaded. Investigations suggest that the attackers likely gained unauthorized access to a single cPanel user account on a legitimate hosting server to stage this binary, further demonstrating their ability to leverage compromised infrastructure to host their malicious components and maintain a low profile.
Malware Deployment, Persistence, and Privilege Escalation

The downloaded "SSA statement" is a JWrapper-packaged Windows executable. JWrapper is a legitimate tool used for cross-platform Java application deployment, and its use here adds another layer of obfuscation, making the executable appear as a benign application installer rather than a direct malware dropper. The moment an unsuspecting victim executes this file, believing it to be a document, the intricate process of compromise begins.
The malware immediately installs itself as a Windows service, a common technique for establishing persistence. Crucially, it configures itself with Safe Mode persistence, ensuring that even if the system is rebooted into Windows Safe Mode (often used for troubleshooting and malware removal), the malicious service can still execute. To further guarantee its operation, the malware incorporates a "self-healing watchdog" mechanism. This component actively monitors the SimpleHelp service, and if it detects that the service has been terminated or crashed, it automatically restarts it, making manual termination by a user or basic security tool largely ineffective without a comprehensive understanding of the threat.
Beyond persistence, the deployed RMM client actively conducts reconnaissance on the compromised host. It periodically enumerates registered security products using the rootSecurityCenter2 Windows Management Instrumentation (WMI) namespace. This occurs approximately every 67 seconds, allowing the attackers to identify active antivirus software, firewalls, and other security solutions present on the system. This information is invaluable for adapting their tactics or identifying blind spots. Concurrently, the malware polls for user presence every 23 seconds, enabling the operators to gauge user activity and potentially time their actions to avoid detection or escalate privileges when a user is actively logged in.
To achieve fully interactive desktop access, the SimpleHelp remote access client proceeds to acquire SeDebugPrivilege via the AdjustTokenPrivileges API call. SeDebugPrivilege allows a process to debug other processes running on the system, which is a critical step towards gaining deeper control. This is followed by the use of "elev_win.exe," a legitimate executable associated with the SimpleHelp software itself, to elevate its privileges to SYSTEM level. Achieving SYSTEM privileges grants the threat actor complete control over the compromised machine, allowing them to bypass most security restrictions. With this elevated access, the operator gains the ability to read the victim’s screen, inject keystrokes, and access any user-context resources, effectively taking full control of the endpoint as if they were physically present.
This initial, elevated remote access via SimpleHelp is then leveraged to download and install ConnectWise ScreenConnect. This installation is not merely a redundancy but a strategic move to offer a robust fallback communication mechanism. Should the SimpleHelp channel be detected, blocked, or rendered inoperable, the ScreenConnect installation ensures the attackers retain their foothold and control over the compromised system, highlighting their long-term objectives and resilience.
Implications for Targeted Organizations and the Broader Threat Landscape

The consequences for organizations impacted by VENOMOUS#HELPER are severe. As the Securonix researchers succinctly put it, "The victim organization is left in a state where the attacker can return at any time, execute commands silently in the user’s desktop session, transfer files bidirectionally, and pivot to adjacent systems, while standard antivirus and signature-based controls see nothing but legitimately signed software from a reputable U.K. vendor." This level of persistent, undetected access allows threat actors ample time to conduct extensive reconnaissance, exfiltrate sensitive data, deploy further malicious payloads such as ransomware, or establish deeper footholds for future attacks.
The financially motivated nature of this campaign, whether an IAB or ransomware precursor, suggests that the ultimate goal is monetary gain. Initial Access Brokers specialize in compromising networks and then selling that access to other cybercriminal groups, including ransomware gangs. A ransomware precursor operation, on the other hand, directly lays the groundwork for a future ransomware attack, often involving data exfiltration before encryption to maximize leverage for extortion. Given the prevalence of ransomware attacks and the lucrative nature of selling network access, the threat posed by VENOMOUS#HELPER is substantial. The targeting of over 80 organizations, predominantly in the U.S., suggests a broad, opportunistic approach aimed at maximizing potential revenue.
Mitigation and Defense Strategies
Defending against sophisticated campaigns like VENOMOUS#HELPER requires a multi-layered and proactive security posture that moves beyond traditional signature-based detection. Organizations must prioritize:
- Enhanced Email Security: Implementing advanced email security solutions with robust anti-phishing, spoofing detection, and URL analysis capabilities is paramount. These solutions should be capable of identifying and blocking malicious links even when they initially point to legitimate, compromised domains.
- User Awareness Training: Regular and comprehensive security awareness training is critical. Employees must be educated about the evolving tactics of phishing, particularly those involving impersonation of trusted entities like the SSA. Training should emphasize verifying sender identities, scrutinizing URLs, and reporting suspicious emails.
- Endpoint Detection and Response (EDR): EDR solutions are essential for detecting anomalous behavior on endpoints, even when legitimate tools are being abused. EDR can identify unusual process executions, privilege escalation attempts, suspicious network connections originating from legitimate software, and other indicators of compromise that signature-based tools might miss.
- Application Whitelisting/Control: Implementing strict application whitelisting or application control policies can prevent unauthorized software from executing. While RMM tools are legitimate, organizations should consider policies that only allow approved versions of these tools to run, potentially blocking custom or unsanctioned instances.
- Network Segmentation and Monitoring: Segmenting networks limits an attacker’s ability to pivot once initial access is gained. Continuous network monitoring for unusual outbound connections from RMM tools, especially to non-corporate IP addresses, can help detect malicious activity.
- Principle of Least Privilege: Enforcing the principle of least privilege for all user accounts and applications minimizes the impact of a compromise. Even if an attacker gains initial access, limited privileges can significantly hinder their ability to escalate and move laterally.
- Threat Hunting: Proactive threat hunting, utilizing EDR data and threat intelligence, allows security teams to search for subtle indicators of compromise that automated systems might overlook, such as the specific WMI queries or API calls used by VENOMOUS#HELPER.
- Incident Response Planning: A well-defined and regularly tested incident response plan is crucial for containing, eradicating, and recovering from attacks rapidly. This includes clear procedures for isolating compromised systems, revoking access, and restoring data.
The VENOMOUS#HELPER campaign serves as a stark reminder of the escalating sophistication of cyber threats. The strategic abuse of legitimate RMM software, coupled with multi-stage phishing and robust persistence mechanisms, presents a formidable challenge for cybersecurity professionals. As threat actors continue to innovate, leveraging trusted tools and refining social engineering tactics, the emphasis for organizations must shift towards advanced behavioral detection, proactive threat intelligence, and a security culture that empowers every employee to be a vigilant first line of defense. The battle against such adaptive adversaries demands continuous evolution in defensive strategies and a collaborative effort across the cybersecurity community to share intelligence and best practices.