GitHub officially confirmed on Wednesday, May 21, 2026, that a significant breach of its internal…
Tag: Cybercrime
Microsoft Unveils RAMPART and Clarity: Pioneering Open-Source Tools to Fortify AI Agent Security
Microsoft has announced the release of two groundbreaking open-source tools, RAMPART and Clarity, designed to…
Grafana Labs Navigates GitHub Breach Amidst Broader TeamPCP Supply Chain Offensive
Grafana Labs, the company behind the popular open-source visualization software, announced on May 19, 2026,…
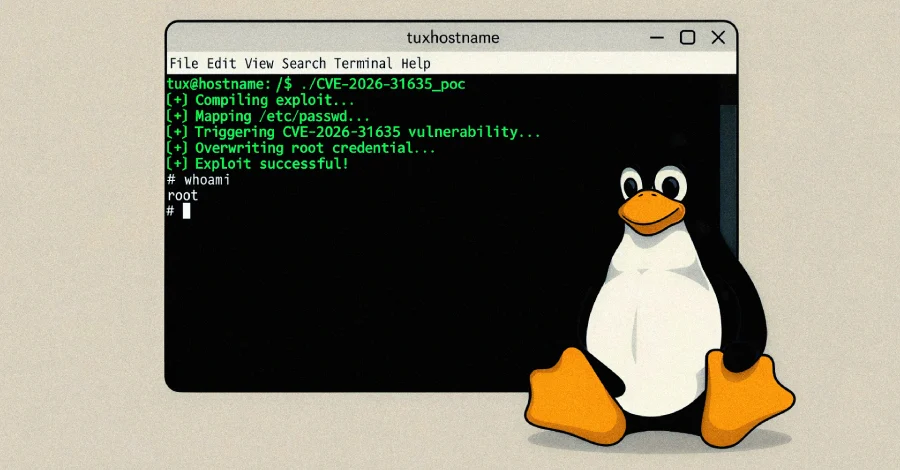
DirtyDecrypt PoC Released for Linux Kernel CVE-2026-31635 LPE Vulnerability
The DirtyDecrypt vulnerability, tracked as CVE-2026-31635 with a CVSS score of 7.5, was independently discovered…
Trapdoor: A Sophisticated Multi-Stage Ad Fraud and Malvertising Operation Targets Android Users
Cybersecurity researchers have unveiled a new, highly sophisticated ad fraud and malvertising campaign, dubbed "Trapdoor,"…

SEPPMail Secure E-Mail Gateway Vulnerabilities Enable RCE and Mail Traffic Access
Major security flaws have been publicly disclosed in SEPPMail Secure E-Mail Gateway, a widely adopted…
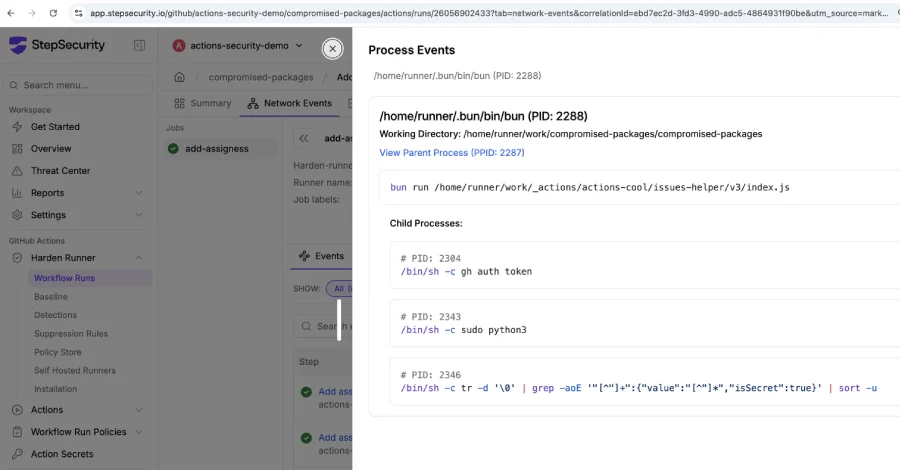
Major GitHub Actions Supply Chain Compromise Discovered, Threat Actors Exploit ‘Imposter Commits’ to Harvest CI/CD Credentials.
On May 19, 2026, a critical software supply chain attack came to light, revealing that…
Escalating Cyber Threats Mark New Week with Zero-Day Exploits, Supply Chain Attacks, and AI-Powered Infostealers
The digital landscape opened this week under a siege of escalating threats, characterized by the…
INTERPOL’s Groundbreaking Operation Ramz Uncovers Major Cybercrime Networks, Leads to 201 Arrests Across Middle East and North Africa
In a significant stride against the rapidly evolving landscape of global cybercrime, INTERPOL has successfully…
Microsoft Grapples with New Zero-Day Disclosures: BitLocker Bypass and Privilege Escalation Unveiled Amidst Researcher Dissatisfaction
A prominent, anonymous cybersecurity researcher, operating under the aliases Chaotic Eclipse and Nightmare-Eclipse, has once…

