A perplexing paradox has emerged within the rapidly evolving 2026 threat landscape, confounding Chief Information…
Tag: Security

Anthropic Unveils Claude Mythos Preview to Select Partners Amidst Growing AI Security Concerns
In a strategic move to proactively address the evolving landscape of artificial intelligence security, AI…
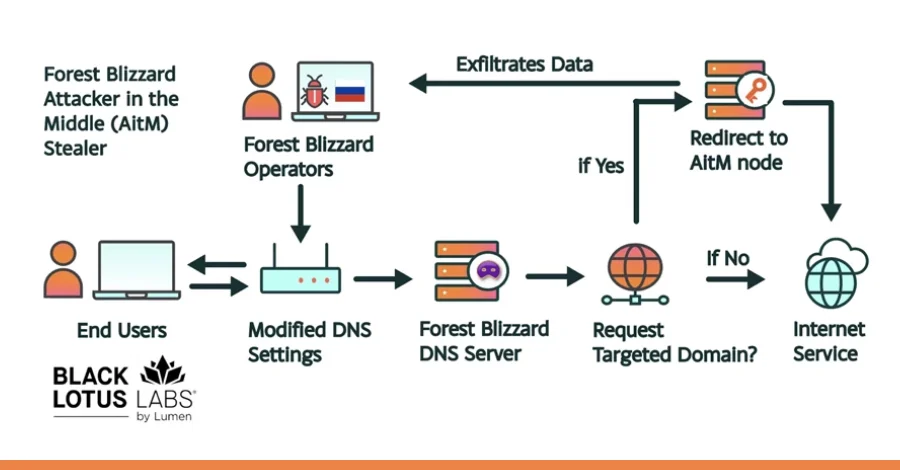
Russia-Linked APT28 Unleashes Sophisticated DNS Hijacking Campaign Targeting Global Government and Enterprise Networks.
A pervasive and technically advanced cyber espionage campaign, attributed to the Russia-linked threat actor known…
New RowHammer Attacks Unleashed Against High-Performance GPUs Threaten Privilege Escalation and Full System Compromise, Bypassing IOMMU Protections.
A groundbreaking academic investigation has unveiled a new generation of RowHammer attacks specifically engineered to…
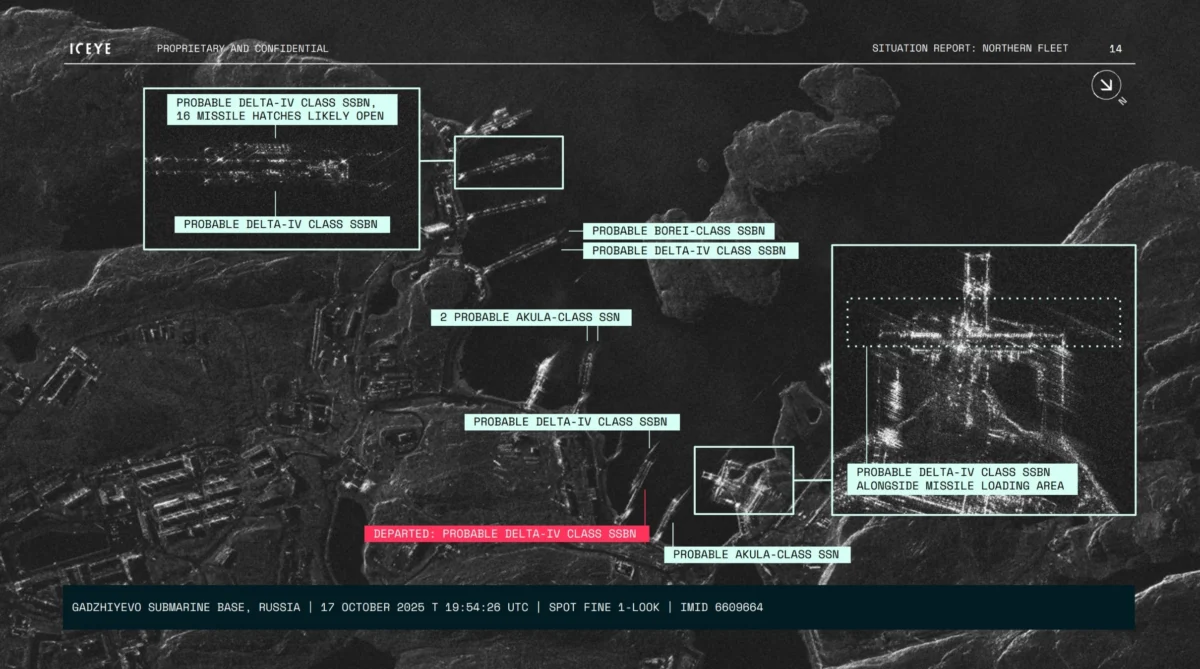
Iceye Leverages Worlds Largest SAR Constellation to Expose Shadow Maritime Activities and Bolster Global Security
In the pitch-black environment of an Arctic winter, where the sun may not rise for…

Threat Actors Actively Exploit Maximum-Severity Code Injection Vulnerability in Open-Source AI Platform Flowise, Posing Widespread Risk.
Threat actors are actively exploiting a maximum-severity security flaw, identified as CVE-2025-59528, within Flowise, a…

Iran-Nexus Threat Actors Intensify Cyber Warfare in Middle East with Sophisticated Password Spraying and Ransomware Campaigns
An Iran-nexus threat actor is currently suspected of orchestrating a widespread password-spraying campaign meticulously targeting…

AWS Unleashes AI-Powered Frontier Agents for DevOps and Security, Bolstering Global Cloud Operations
Amazon Web Services (AWS) has announced the general availability of its highly anticipated AWS DevOps…
North Korean State-Sponsored Hackers Exploit GitHub for Command-and-Control in Multi-Stage Attacks Against South Korean Entities
Threat actors, strongly suspected of being associated with the Democratic People’s Republic of Korea (DPRK),…

Qilin and Warlock Ransomware Operations Leverage Vulnerable Drivers to Neutralize Security Tools
In a significant escalation of cyber warfare tactics, threat actors linked to the notorious Qilin…

