Cybersecurity researchers have issued a stark warning regarding a sophisticated new iteration of the TrickMo Android banking trojan, which has been observed leveraging The Open Network (TON) blockchain for its command-and-control (C2) infrastructure. This innovative shift represents a significant escalation in the cat-and-mouse game between cybercriminals and security experts, as TON’s decentralized nature offers enhanced stealth and resilience to traditional detection and takedown efforts.
Emergence of a More Formidable Threat
The latest variant, meticulously tracked by Dutch mobile security firm ThreatFabric between January and February 2026, has been actively deployed in targeted campaigns against banking and cryptocurrency wallet users across France, Italy, and Austria. This geographic focus underscores the threat actors’ strategic interests in regions with robust digital economies and widespread adoption of mobile financial services.
"TrickMo relies on a runtime-loaded APK (‘dex.module’), used also by the previous variant, but updated with new features adding new network-oriented functionality, including reconnaissance, SSH tunnelling, and SOCKS5 proxying capabilities that allow infected devices to function as programmable network pivots and traffic-exit nodes," ThreatFabric detailed in a comprehensive report shared with The Hacker News. This evolution transforms compromised smartphones from mere data exfiltration points into integral components of a distributed, clandestine network infrastructure.
A History of Digital Deception: The TrickMo Legacy
TrickMo is not a nascent threat; it is the designation given to a device takeover (DTO) malware family that has plagued Android users since late 2019. Its initial emergence was documented by CERT-Bund and IBM X-Force, who highlighted its insidious capability to exploit Android’s accessibility services. This abuse allowed TrickMo to intercept and hijack crucial one-time passwords (OTPs), effectively bypassing multi-factor authentication mechanisms designed to protect sensitive financial transactions.
Over the years, TrickMo has steadily evolved, incorporating an increasingly formidable arsenal of features. Earlier versions were equipped with functionalities designed to phish for credentials through overlay attacks, log keystrokes to capture sensitive input, record screen activity, and even facilitate live screen streaming to attackers. Furthermore, its ability to intercept SMS messages provided a critical avenue for compromising authentication codes and account recovery processes. Collectively, these capabilities granted threat operators near-complete remote control over infected devices, making them potent tools for financial fraud and data theft. A notable enhancement observed in October 2024 further expanded its capabilities to include comprehensive screen capture, allowing attackers to visually record sensitive information displayed on the victim’s device.

The Architectural Leap: TrickMo C and the TON Integration
The current generation, dubbed TrickMo C, showcases a significant architectural overhaul, particularly in its distribution and command-and-control mechanisms. Distribution predominantly occurs via sophisticated phishing websites designed to mimic legitimate services, as well as through malicious dropper applications. These dropper apps, often disseminated through social media platforms like Facebook, cunningly masquerade as "adult-friendly" versions of popular applications such as TikTok. Once installed, the dropper serves as a conduit for retrieving a dynamically loaded APK, the "dex.module," from attacker-controlled infrastructure at runtime. The "dex.module" itself then attempts to impersonate legitimate services like Google Play Services to further evade detection and gain persistence on the device.
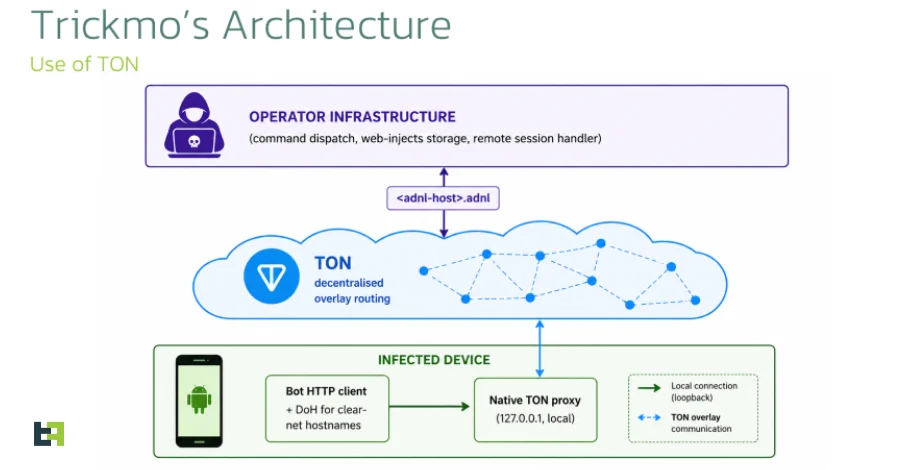
The most striking innovation in TrickMo C is its pivot to The Open Network (TON) for C2 communications. TON, a decentralized blockchain platform originally conceived by Telegram, offers a highly resilient and anonymous communication channel. ThreatFabric’s analysis reveals how this is achieved: "TrickMo carries an embedded native TON proxy that the host APK starts on a loopback port at process start. The bot’s HTTP client is wired through that proxy, so every outbound command-and-control request is addressed to an .adnl hostname and resolved through the TON overlay."
This method fundamentally alters the C2 landscape. By eschewing conventional DNS and public internet infrastructure in favor of .adnl endpoints routed via an embedded local TON proxy, the malware significantly reduces the efficacy of traditional network-blocking efforts and takedown attempts. The malicious traffic blends seamlessly with legitimate TON activity, making it exceedingly difficult for security solutions to differentiate and block. This move mirrors a broader trend in cybercrime towards leveraging decentralized technologies for operational security, posing a formidable challenge to national cybersecurity agencies and law enforcement.
Transforming Devices into Network Pivots and Exit Nodes
Beyond the stealthy C2, TrickMo C introduces a robust network-operative subsystem that dramatically expands the malware’s capabilities, shifting its role from a conventional banking trojan to a versatile tool for establishing managed footholds within victim networks. While previous iterations relied on a socket.io-based channel for accessibility-driven remote control, the new version equips attackers with a "remote shell-equivalent" for in-depth network reconnaissance.
The subsystem supports a range of network utilities, including curl, dnslookup, ping, telnet, and traceroute. This functionality allows the attacker to execute these commands directly from the compromised device’s network position. This means an attacker can map internal corporate networks or home networks that the device is currently connected to, identifying potential vulnerabilities, discovering other connected devices, and planning subsequent attacks from within the victim’s trusted environment. This capability elevates the threat from individual financial fraud to potential corporate espionage or broader network infiltration.
Perhaps even more concerning is the integration of a SOCKS5 proxy and SSH tunneling capabilities. The SOCKS5 proxy effectively transforms the compromised Android device into a network exit node, routing malicious traffic through the victim’s IP address. This is a critical feature for cybercriminals, as it allows them to defeat IP-based fraud-detection signatures employed by banking, e-commerce, and cryptocurrency exchange services. By making it appear as if fraudulent transactions or malicious activities originate from a legitimate user’s device and network, attackers can bypass critical security controls and maintain anonymity. The SSH tunneling further enhances this by providing encrypted and secure channels for data exfiltration and remote control, making detection and interception even more challenging.

Future Expansions: Dormant Capabilities and Emerging Threats
ThreatFabric’s analysis also uncovered two dormant features within TrickMo C: the bundling of the Pine hooking framework and the declaration of extensive NFC-related permissions. While these features are not currently implemented, their presence strongly suggests that the core developers are actively planning to expand the trojan’s capabilities in future versions.
The Pine hooking framework, if activated, could allow the malware to intercept and modify function calls within other applications, potentially enabling more sophisticated data theft or manipulation. The NFC permissions, when utilized, could open avenues for novel attack vectors, such as tapping into contactless payment systems or exploiting vulnerabilities in NFC-enabled devices. This foresight by the attackers indicates a long-term strategic vision for TrickMo, ensuring its continued relevance and potency in the evolving mobile threat landscape.
Implications for Users and the Cybersecurity Ecosystem
The emergence of this new TrickMo variant, with its advanced C2 mechanisms and network pivot capabilities, carries profound implications for individuals and the broader cybersecurity ecosystem.
For individual users, the risks are amplified. Beyond direct financial theft from banking and crypto wallets, compromised devices could serve as entry points for broader attacks on their home networks, potentially affecting other smart devices, personal computers, and sensitive data. The sophistication of the social engineering tactics used for distribution, particularly the impersonation of popular apps and Google Play Services, makes it harder for average users to discern legitimate applications from malicious ones.
For financial institutions and cryptocurrency platforms, the challenge of fraud detection becomes significantly more complex. Traditional IP-based anomaly detection systems are undermined when malicious traffic originates from legitimate user devices via SOCKS5 proxies. This necessitates a shift towards more advanced behavioral analytics, device fingerprinting, and real-time transaction monitoring that can identify anomalies even when the source IP appears benign.
The cybersecurity industry faces an urgent need to adapt. Detection tools must evolve to identify TON-based C2 communications and the subtle indicators of compromised devices acting as network pivots. This requires deep packet inspection, advanced threat intelligence sharing, and potentially leveraging AI and machine learning to detect unusual network activity patterns that might signify a TrickMo infection. Furthermore, the decentralized nature of TON poses significant challenges for traditional law enforcement and cybersecurity agencies seeking to perform takedowns or attribute attacks. International collaboration and novel investigative techniques will be crucial.

Recommendations for Defense and Mitigation
To counter the escalating threat posed by TrickMo C and similar advanced mobile malware, a multi-layered defense strategy is imperative:
-
For Users:
- Vigilance against Phishing: Exercise extreme caution with links received via SMS, email, or social media, even if they appear to come from trusted sources. Always verify URLs before clicking.
- Official App Stores Only: Download applications exclusively from official and reputable app stores (e.g., Google Play Store). Avoid third-party app stores or direct APK downloads from untrusted websites.
- Permission Scrutiny: Pay close attention to the permissions requested by apps during installation. Be wary of apps requesting excessive or unusual permissions (e.g., a simple game requesting accessibility services or SMS access).
- Software Updates: Keep the Android operating system and all installed applications updated to the latest versions to benefit from security patches.
- Mobile Security Solutions: Install and maintain a reputable mobile antivirus or security application that offers real-time protection against malware.
- Multi-Factor Authentication (MFA): Enable MFA on all critical accounts, especially banking and cryptocurrency services. While TrickMo aims to bypass OTPs, strong MFA using hardware tokens or authenticator apps (rather than SMS) adds layers of security.
- Regular Backups: Regularly back up important data to mitigate the impact of data loss or device compromise.
-
For Organizations:
- Mobile Device Management (MDM): Implement robust MDM solutions to enforce security policies on employee devices, including app whitelisting, configuration management, and remote wiping capabilities.
- Zero-Trust Architecture: Adopt a zero-trust security model, assuming that no user or device, whether inside or outside the network perimeter, should be implicitly trusted.
- Employee Training: Conduct regular cybersecurity awareness training to educate employees about phishing tactics, social engineering, and the dangers of sideloading applications.
- Network Segmentation: Implement network segmentation to limit the lateral movement of malware if a device within the corporate network becomes compromised.
- Advanced Threat Detection: Deploy advanced threat detection systems that leverage behavioral analytics and machine learning to identify unusual network traffic patterns, even from seemingly legitimate sources.
- Threat Intelligence Sharing: Participate in threat intelligence sharing initiatives to stay informed about emerging mobile threats and attack vectors.
The evolution of TrickMo to incorporate decentralized C2 and advanced network capabilities signifies a new era in mobile malware. As cybercriminals continue to innovate, a proactive, adaptive, and collaborative approach from users, industry, and law enforcement is paramount to safeguarding digital assets and privacy. The battle against sophisticated mobile threats is ongoing, and vigilance remains the strongest defense.