The Office of Inspector General (OIG) of the U.S. National Aeronautics and Space Administration (NASA) has recently shed light on an elaborate, multi-year spear-phishing campaign orchestrated by a Chinese national who successfully posed as a U.S. researcher to illicitly obtain highly sensitive information from critical American institutions. This sophisticated operation targeted not only NASA but also various government entities, prominent universities, and private companies, all in flagrant violation of stringent U.S. export control laws designed to protect national security.
The Modus Operandi: A Sophisticated Impersonation Scheme
For a period spanning nearly five years, from January 2017 to December 2021, the accused individual, identified as Chinese national Song Wu, exploited the collaborative nature of scientific research and engineering development. He meticulously crafted an identity that allowed him to masquerade as legitimate U.S. engineers and researchers. According to the OIG’s recent disclosure, released on Thursday, April 24, 2026, "For years, NASA employees and research collaborators thought they were simply sharing software with colleagues. Instead, they were emailing sensitive defense technology to a Chinese national who was impersonating U.S. engineers." This statement underscores the insidious nature of the campaign, which relied heavily on social engineering and the trust inherent in professional networks.
The scheme involved a systematic approach to identifying and engaging targets. Song Wu and his co-conspirators, whose identities remain largely undisclosed in public records, conducted extensive background research on their intended victims. This research likely included scrutinizing professional profiles on platforms like LinkedIn, academic publications, conference attendance lists, and organizational charts to understand relationships and identify individuals with access to valuable information. By presenting himself as a peer, Song was able to initiate contact, build rapport, and subsequently request proprietary software and source code, ostensibly for collaborative research or development purposes.
Unmasking the Deception: A Chronology of Discovery
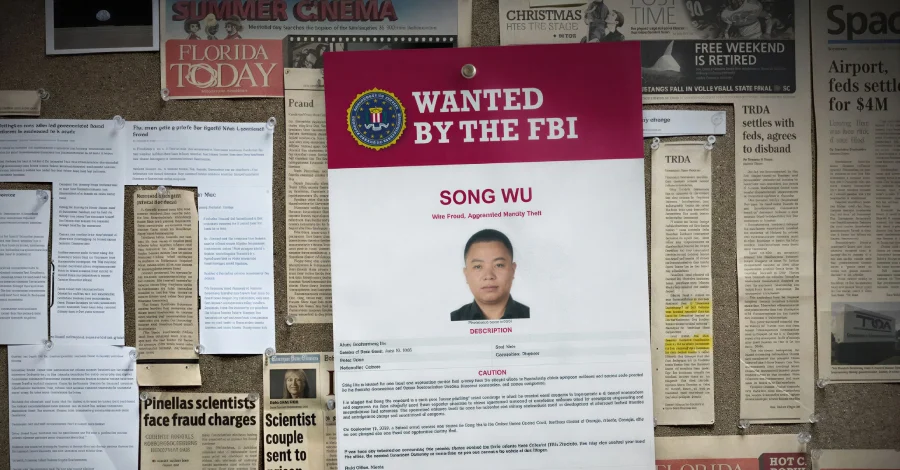
The intricate web of deception began to unravel, leading to formal charges against Song Wu in September 2024. The U.S. Department of Justice (DoJ) announced a comprehensive indictment against him, detailing the multi-year phishing scheme and the targeting of dozens of U.S. professors, researchers, and engineers across various critical sectors. While the OIG’s recent report highlights the specifics of NASA’s involvement, the DoJ’s earlier announcement painted a broader picture of the campaign’s reach.
The timeline of the investigation suggests a painstaking effort by U.S. intelligence and law enforcement agencies to piece together the fragments of this complex digital espionage operation. Initial suspicions likely arose from unusual patterns in information requests or anomalies detected in network traffic or email communications. The OIG’s statement indicates that the successful exfiltration of sensitive data occurred in "a handful of cases," suggesting that while the campaign was widespread, not all attempts yielded results. However, even a few successful breaches of highly controlled defense technology represent a significant national security compromise. The investigation culminated in the unsealing of the indictment against Song Wu, who was charged with multiple counts of wire fraud and aggravated identity theft.

The Stakes: Export Control Laws and National Security Imperatives
The information sought by Song Wu and his collaborators was not merely academic; it constituted sensitive defense technology governed by strict U.S. export control laws, primarily the International Traffic in Arms Regulations (ITAR) and the Export Administration Regulations (EAR). These regulations are designed to prevent the proliferation of advanced technologies and military capabilities to foreign adversaries. ITAR controls items and services specifically designed or modified for military applications, listed on the U.S. Munitions List (USML), while EAR covers "dual-use" items – commercial products with potential military applications.
The specific types of information targeted included "modeling software used for aerospace design and weapons development." This type of software is crucial for simulating aerodynamic performance, structural integrity, material science, and propulsion systems for advanced aircraft, missiles, and other defense platforms. For instance, advanced computational fluid dynamics (CFD) software used in hypersonic missile design, or finite element analysis (FEA) software crucial for designing resilient aerospace structures, could be invaluable to a foreign power seeking to accelerate its own military-industrial capabilities. The FBI explicitly stated that the specialized software targeted "could be used for industrial and military applications, including the development of advanced tactical missiles and aerodynamic design and assessment of weapons." The unauthorized transfer of such technology directly undermines U.S. military advantage and national security.
Profile of the Accused and Affiliated Entity: Aviation Industry Corporation of China (AVIC)
According to the 2024 indictment, Song Wu was an engineer at the Aviation Industry Corporation of China (AVIC). AVIC is a massive Chinese state-owned aerospace and defense conglomerate, established in 2008 through the merger of several existing state-owned aviation enterprises. It is one of China’s largest and most strategically important industrial groups, employing hundreds of thousands of people and serving as the primary developer and manufacturer of military and civil aircraft for the People’s Liberation Army (PLA) and the global market. AVIC’s portfolio spans fighter jets, bombers, transport aircraft, helicopters, drones, avionics, engines, and missile systems.
AVIC’s central role in China’s military modernization makes it a highly motivated entity for acquiring foreign technology, particularly from leading aerospace nations like the United States. Its long-standing ambition to close the technological gap with Western counterparts often places it at the center of intellectual property disputes and allegations of espionage. The indictment suggests that Song Wu’s actions were not merely those of a rogue employee but rather part of a broader, coordinated effort to advance AVIC’s capabilities, thereby enhancing China’s overall aerospace and defense prowess. The use of an engineer directly affiliated with AVIC further solidifies the view that this was state-sponsored economic espionage.
Wider Ramifications: Economic Espionage and U.S.-China Dynamics
This incident is not isolated but rather indicative of a broader pattern of state-sponsored economic espionage targeting U.S. intellectual property, with China frequently cited by U.S. intelligence agencies as the most significant perpetrator. The U.S. government estimates that intellectual property theft costs the American economy hundreds of billions of dollars annually, leading to job losses, reduced innovation, and erosion of competitive advantage.

The context of U.S.-China relations is critical here. While the two nations are deeply intertwined economically, they are also engaged in intense strategic competition, particularly in technology and defense. The U.S. views China’s military modernization, fueled in part by intellectual property theft, as a direct challenge to global stability and American leadership. Cases like Song Wu’s highlight the asymmetric warfare waged in the cyber domain, where sophisticated phishing campaigns become tools of geopolitical strategy. This kind of espionage allows countries like China to bypass billions of dollars in research and development costs and shave years off their technological timelines, thereby gaining an unfair competitive advantage.
Official Responses, Warnings, and the Pursuit of Justice
Both the NASA OIG and the FBI have issued stern warnings to U.S. researchers, academics, and industry professionals regarding the persistent threat of foreign espionage. The OIG emphasized that despite the growing sophistication of phishing campaigns, "there are common clues that can betray scammers and expose their export fraud schemes." In Song Wu’s specific case, investigators noted several red flags, including "multiple requests for the same software" and a lack of clear justification for why he needed it. Furthermore, the OIG advised vigilance against unusual payment methods, abrupt changes in payment terms or sources, and unconventional transfer methods designed to mask identity and evade shipping restrictions.
The FBI has taken the significant step of adding Song Wu to its "U.S. Most Wanted List" for cyber criminals, signifying the severity of his alleged crimes and the U.S. government’s commitment to bringing him to justice. The fact that he remains at large underscores the challenges inherent in prosecuting individuals residing in countries that do not have extradition treaties with the U.S. or that may be unwilling to cooperate on politically sensitive cases. The U.S. Department of Justice continues to utilize various legal tools, including indictments and sanctions, to disrupt and deter such activities, even when the accused remains outside U.S. jurisdiction. These actions serve as a powerful message to foreign adversaries that their attempts at illicit technology acquisition will be identified and condemned.
Preventative Measures and Future Outlook
In response to these pervasive threats, U.S. government agencies, universities, and private companies are continuously enhancing their cybersecurity protocols and employee training programs. Key preventative measures include:
- Enhanced Cybersecurity: Implementing advanced email filtering, multi-factor authentication, and robust intrusion detection systems.
- Employee Education: Regular training on identifying phishing attempts, social engineering tactics, and the importance of adhering to export control regulations. Employees are often the first line of defense.
- Due Diligence: Thorough vetting of external collaborators, especially those requesting access to sensitive data or software.
- Technical Controls: Implementing strict access controls, monitoring data transfers, and employing data loss prevention (DLP) solutions.
- Reporting Suspicious Activity: Fostering a culture where employees feel empowered and obligated to report any unusual or suspicious requests.
The case of Song Wu serves as a stark reminder of the persistent and evolving threat of economic and cyber espionage. The U.S. government, through agencies like NASA OIG, FBI, and DoJ, is committed to safeguarding its technological lead and national security interests. However, the onus also falls on individual researchers and organizations to exercise extreme vigilance. As long as advanced technology remains a critical component of global power and economic competitiveness, the efforts to illegally acquire it will continue, demanding an equally persistent and sophisticated defense. The pursuit of individuals like Song Wu, even when they remain beyond immediate reach, sends a clear signal that the U.S. will not tolerate the theft of its intellectual property and will continue to work towards accountability for those who threaten its national and economic security.