Amazon Web Services (AWS) has announced a significant new feature for its industry-leading object storage service, Amazon Simple Storage Service (Amazon S3), allowing users to create general purpose buckets within their own account regional namespace. This innovation directly addresses long-standing challenges associated with S3’s traditional global bucket naming convention, simplifying bucket creation and management, and ensuring the predictable availability of desired bucket names across multiple AWS Regions. The new capability empowers organizations to streamline their cloud storage strategies, enhance security, and improve operational efficiency without incurring additional costs.
The Evolving Landscape of Cloud Storage and S3’s Enduring Role
Since its launch in 2006, Amazon S3 has become the de facto standard for object storage in the cloud, underpinning countless applications, data lakes, backups, archives, and content delivery networks globally. As of early 2024, S3 stores trillions of objects and processes millions of requests per second, demonstrating its unparalleled scalability, durability, and availability. Its foundational role in the AWS ecosystem has fostered an environment where enterprises, startups, and developers alike rely on S3 for diverse data storage needs, from critical operational data to vast analytical datasets.
However, a persistent challenge for S3 users, particularly those operating at scale or within large organizational structures, has been the global uniqueness requirement for general-purpose bucket names. Traditionally, an S3 bucket name had to be unique across all AWS accounts and all AWS Regions worldwide. While this design ensured a simple, globally resolvable endpoint for every bucket, it also introduced several complexities:
- Naming Conflicts: As S3 adoption surged, finding a desired, simple, and intuitive bucket name became increasingly difficult. Users often resorted to appending random strings, project codes, or numerical identifiers to ensure uniqueness, leading to unwieldy and hard-to-remember bucket names.
- Bucket Squatting: The global namespace presented a theoretical, albeit rare, risk of "bucket squatting," where an actor could register a desirable bucket name, preventing its use by legitimate organizations.
- Operational Overhead: For large enterprises managing hundreds or thousands of AWS accounts and deploying applications across multiple regions, coordinating bucket names to avoid conflicts required significant planning and often custom tooling, hindering automation and developer velocity.
- Infrastructure as Code (IaC) Challenges: While IaC tools like AWS CloudFormation allowed for templating, generating truly unique and predictable bucket names across different accounts and regions without manual intervention or complex logic remained an intricate task.
This new "account regional namespace" feature is a direct response to these pain points, reflecting AWS’s continuous commitment to refining its core services based on extensive customer feedback and evolving cloud adoption patterns. It marks a significant step towards abstracting away global naming complexities for general-purpose S3 buckets, mirroring similar account-level namespace approaches already present in specialized S3 offerings like S3 Directory Buckets (zonal namespace) or S3 Table/Vector buckets (account-level namespace).
A Deep Dive into the Account Regional Namespace Mechanism
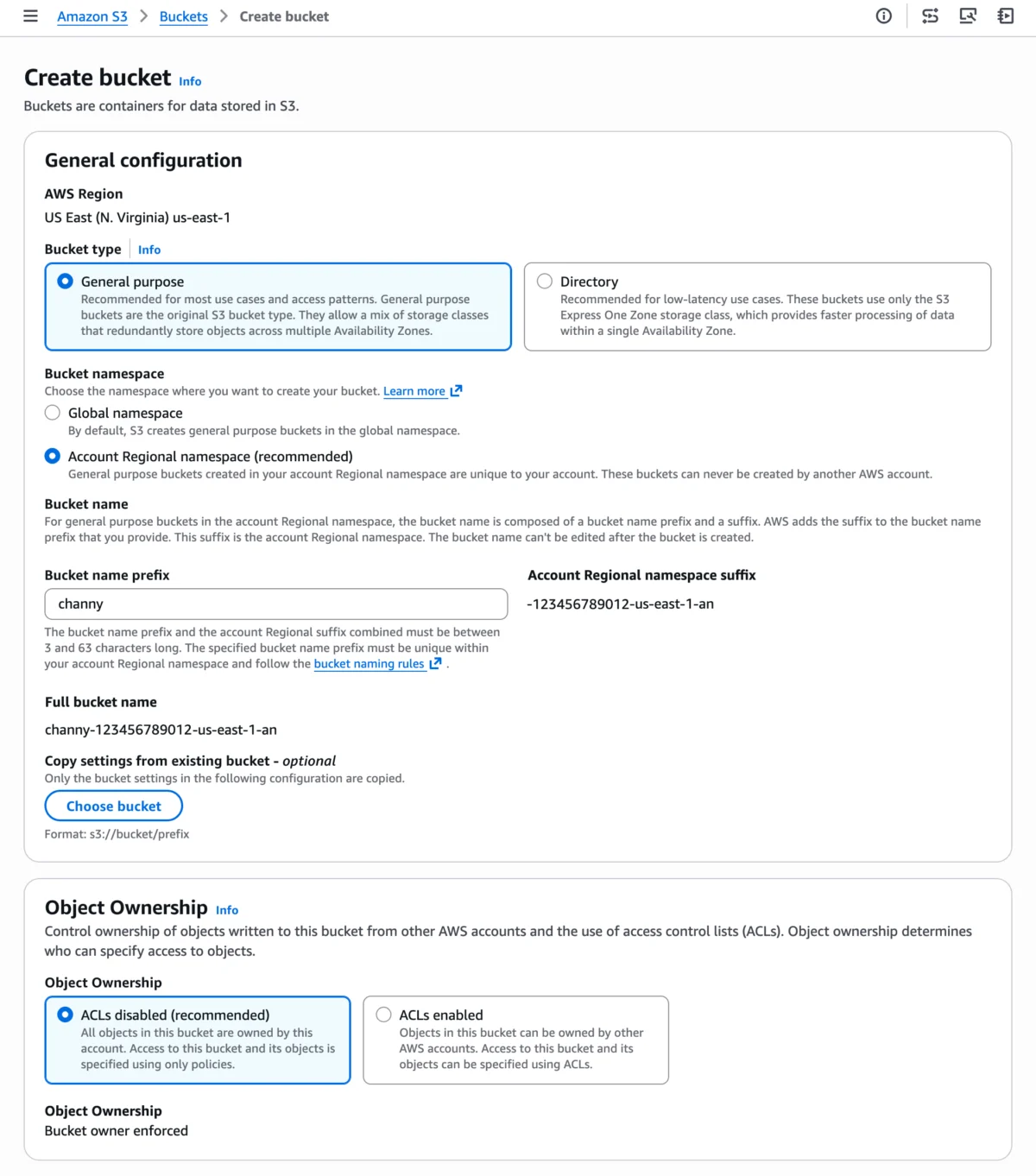
The core of this new feature lies in its intelligent use of a unique suffix appended to user-defined bucket names. When a user opts for the "Account regional namespace" option during bucket creation, S3 automatically appends their AWS account’s unique identifier, the AWS Region, and a fixed suffix (-an) to the chosen bucket name prefix. For example, a user creating a bucket with the prefix myapplication-logs in account 123456789012 within the us-east-1 region would result in the bucket name myapplication-logs-123456789012-us-east-1-an.

This mechanism guarantees several critical advantages:
- Assured Uniqueness: Within an individual AWS account and a specific region, the chosen bucket name prefix combined with the automatic suffix is inherently unique. This eliminates the possibility of naming conflicts with buckets owned by other AWS accounts or in different regions.
- Predictable Naming: Developers and operations teams can now use simpler, more descriptive bucket name prefixes, confident that the full bucket name will be consistently generated and available. This greatly improves readability and manageability of resources.
- Enhanced Security Boundary: The account-regional suffix acts as a strong identifier, ensuring that only the owning AWS account can create or manage buckets with that specific suffix. Any attempt by another account to create a bucket using a suffix belonging to a different account will be automatically rejected, adding an intrinsic layer of security against naming impersonation.
The feature maintains full compatibility with all existing functionalities of general-purpose S3 buckets, including versioning, lifecycle policies, access control lists (ACLs), bucket policies, replication, and encryption. The only operational difference lies in the naming convention, where the combined length of the user-defined prefix and the automatically appended suffix must adhere to the standard S3 bucket naming length constraints of 3 to 63 characters. This ensures seamless integration into existing workflows and applications that interact with S3.
Empowering Governance and Security with IAM and AWS Organizations
Beyond simplifying naming, the account regional namespace feature introduces robust capabilities for governance and security enforcement, particularly crucial for large enterprises. AWS Identity and Access Management (IAM) policies and AWS Organizations Service Control Policies (SCPs) can now leverage a new condition key: s3:x-amz-bucket-namespace.
This condition key allows security and governance teams to:
- Mandate Namespace Adoption: Organizations can implement SCPs at the AWS Organization level or IAM policies at the account level to enforce that all new general-purpose S3 buckets must be created using the account regional namespace. This prevents users from inadvertently creating globally unique buckets that might deviate from organizational naming standards or introduce potential conflicts.
- Standardize Deployments: By enforcing the use of the account regional namespace, enterprises can ensure a consistent and predictable naming schema across all their AWS accounts and regions. This standardization is vital for auditing, compliance, and automated resource management.
- Reduce Human Error: The explicit enforcement through policies minimizes the risk of human error in bucket naming, which could otherwise lead to misconfigurations or security vulnerabilities. It acts as a guardrail, guiding users towards the preferred and most secure naming practice.
For instance, an SCP could be configured to deny any s3:CreateBucket action unless the s3:x-amz-bucket-namespace condition key is set to account-regional. This level of granular control underscores AWS’s commitment to providing tools that support the stringent governance requirements of enterprise customers.
Streamlined Development and Infrastructure as Code Integration
AWS has ensured that the new account regional namespace feature is easily accessible and integrable across its suite of development and management tools, catering to various user preferences and automation needs.

- Amazon S3 Console: Users can select "Account regional namespace" directly within the "Create bucket" wizard in the Amazon S3 console, providing a straightforward graphical interface for adoption.
- AWS Command Line Interface (CLI): The AWS CLI supports the new feature via the
--bucket-namespace account-regionalparameter when executing theaws s3api create-bucketcommand, allowing for script-based automation. - AWS SDKs: Developers can leverage AWS SDKs, such as the AWS SDK for Python (Boto3), to programmatically create buckets within the account regional namespace. The provided Python example demonstrates how to dynamically resolve the AWS account ID and region using the AWS Security Token Service (STS)
GetCallerIdentityAPI, ensuring that the generated bucket name is correct and compliant. - AWS CloudFormation: This is where the feature truly shines for Infrastructure as Code (IaC) practitioners. CloudFormation offers two powerful mechanisms:
- Pseudo Parameters: By combining CloudFormation pseudo parameters like
AWS::AccountIdandAWS::Regionwith the!Subfunction, templates can dynamically construct the full account regional bucket name. For example,BucketName: !Sub "my-app-data-$AWS::AccountId-$AWS::Region-an"provides explicit control over the full name. BucketNamePrefixProperty: A particularly elegant solution for IaC is theBucketNamePrefixproperty. When this property is used in conjunction withBucketNamespace: "account-regional", CloudFormation automatically appends the correct account ID, region, and-ansuffix to the provided prefix. This abstraction greatly simplifies CloudFormation templates, making them cleaner, more portable, and less prone to errors. For instance,BucketNamePrefix: 'my-app-data'combined with the namespace property will automatically yield the correctly formatted bucket name.
- Pseudo Parameters: By combining CloudFormation pseudo parameters like
These integration points ensure that organizations can seamlessly incorporate the new naming convention into their existing CI/CD pipelines, automated provisioning workflows, and overall cloud infrastructure management strategies, significantly boosting developer productivity and reducing deployment complexities.
Broader Impact and Strategic Implications
The introduction of the account regional namespace for general-purpose S3 buckets carries significant implications for various stakeholders within the cloud ecosystem:
- For Enterprise Architects and Operations Teams: This feature simplifies multi-account and multi-region strategies. Architects can design standardized naming conventions that are guaranteed to work across diverse business units and geographical deployments. Operations teams benefit from reduced friction in managing storage resources, especially during incident response or audits, as bucket names become inherently tied to their respective accounts and regions.
- For Security and Compliance Professionals: The ability to enforce the namespace via IAM and SCPs provides a powerful control plane for data governance. It helps prevent shadow IT, ensures adherence to internal policies, and simplifies compliance audits by standardizing resource identifiers. This contributes to a stronger overall security posture.
- For Developers: Developers are freed from the mental overhead of constantly checking for global uniqueness or inventing convoluted naming schemes. They can focus on application logic, knowing that their chosen bucket prefixes will predictably resolve to valid, unique bucket names. This reduces development cycle times and improves code clarity.
- For AWS’s Competitive Edge: By addressing a fundamental pain point in its flagship storage service, AWS reinforces S3’s position as the leading cloud object storage solution. Continuous innovation in core services like S3 helps maintain customer loyalty and attracts new users, showcasing AWS’s responsiveness to customer needs and its commitment to simplifying complex cloud operations.
- Indirect Cost Savings: While the feature itself is free, the efficiencies gained through simplified naming, reduced operational overhead, faster deployments, and decreased likelihood of errors translate into tangible indirect cost savings for organizations. Less time spent on managing naming conflicts means more time for value-added activities.
Limitations and Future Outlook
It is important to note the specific limitations articulated by AWS. The account regional namespace applies only to newly created general-purpose S3 buckets. Existing global buckets cannot be renamed or migrated to this new namespace. Organizations wishing to fully adopt the new naming convention for existing data will need to implement a migration strategy, which typically involves creating new buckets with the desired account regional names and transferring data.
Furthermore, this feature specifically targets general-purpose buckets. Other specialized S3 bucket types, such as S3 Directory Buckets for high-performance access or S3 Table and Vector buckets designed for specific data analytics and AI workloads, already operate within account-level or zonal namespaces due to their distinct architectural requirements. This distinction clarifies that the new feature fills a specific gap for the most common S3 usage patterns.
Availability and Call to Action
The account regional namespace for general-purpose buckets is now widely available across 37 AWS Regions, including the AWS China and AWS GovCloud (US) Regions. This extensive rollout ensures that a vast majority of AWS customers can immediately leverage this feature to enhance their storage management practices. AWS encourages users to explore this new capability through the Amazon S3 console, AWS CLI, SDKs, or AWS CloudFormation. Feedback can be provided via AWS re:Post for Amazon S3 or through existing AWS Support channels, demonstrating AWS’s continued emphasis on a collaborative development process with its user community. This strategic enhancement to Amazon S3 is poised to significantly improve the user experience for cloud storage, particularly for large-scale, multi-account, and multi-region deployments.