A Network Policy Server (NPS) empowers network administrators to establish and enforce comprehensive policies for network access, ensuring that only authorized users and devices can access critical network resources. This versatile tool plays a pivotal role in providing centralized authentication, authorization, and accounting (AAA) for users and devices connecting to an organization’s network. Fundamentally, NPS represents Microsoft’s robust implementation of a Remote Authentication Dial-In User Service (RADIUS) server and proxy within the Windows Server operating systems, making it an indispensable component for effective network management and robust security.
To fully grasp the significance of NPS, it is essential to first understand the underlying principles of RADIUS servers, followed by an exploration of NPS’s specific purpose, its multifaceted benefits, its integral role in modern networking, and finally, best practices for its optimal management.
The Paramount Importance of Network Security and Policy Management
In today’s hyper-connected world, where business operations, data exchange, and communication are increasingly reliant on technology and the internet, networks and servers have become prime targets for malicious cyber actors. This escalating threat landscape underscores the absolute necessity of implementing robust network security measures and meticulously managing network access policies. Without these foundational elements, organizations are exposed to significant risks, including data breaches, service disruptions, financial losses, and reputational damage. Effective policy management, facilitated by tools like NPS, is not merely a technical consideration but a strategic imperative for business continuity and data integrity.
Key reasons highlighting the importance of network security and policy management include:
- Data Protection: Safeguarding sensitive corporate and customer data from unauthorized access, theft, or alteration.
- Regulatory Compliance: Meeting stringent legal and industry-specific compliance requirements (e.g., GDPR, HIPAA, PCI DSS) that mandate secure data handling and access controls.
- Service Availability: Ensuring uninterrupted access to critical network resources and services for legitimate users, preventing costly downtime.
- Threat Mitigation: Proactively defending against a wide array of cyber threats, including malware, ransomware, phishing attacks, and denial-of-service (DoS) attacks.
- Resource Optimization: Managing network resources efficiently by controlling access and usage, preventing overuse and ensuring optimal performance.
- Auditing and Accountability: Maintaining detailed logs of network access and user activities for auditing purposes, incident investigation, and accountability.
Understanding the RADIUS Protocol: The Foundation of Network Access Control
The RADIUS (Remote Authentication Dial-In User Service) protocol is a networking protocol that provides comprehensive and centralized Authentication, Authorization, and Accounting (AAA) management for users accessing network services. Since its introduction in 1991, RADIUS has evolved into a de facto standard for network access servers responsible for managing user connections to networks. It plays a pivotal role in controlling and managing network access, forming the bedrock upon which many modern network security solutions are built.
-
Authentication: The first "A" in AAA, authentication, is the process of verifying a user’s identity. When a user attempts to access a network, they are typically required to provide credentials, such as a username and password, a smart card, or multi-factor authentication tokens. The RADIUS server meticulously checks these credentials against its established user database and security policies to confirm the user’s legitimacy. This rigorous verification process ensures that only authenticated and authorized individuals gain entry to the network, forming the initial barrier against unauthorized access.
-
Authorization: Once a user has been successfully authenticated, the next critical step is authorization. This process defines the specific privileges and permissions granted to an authenticated user, determining what actions they can perform and what network resources they can access. For instance, an IT administrator will likely have broader access rights compared to a standard end-user. RADIUS servers manage these intricate permission levels, ensuring that each user can only access resources commensurate with their defined authorization level. This granular control is vital for maintaining the integrity of network resources and preventing unauthorized modifications or data exposure.
-
Accounting: The final "A" in AAA stands for accounting, which involves the systematic tracking and logging of user activity and resource utilization within the network. This encompasses monitoring crucial metrics such as the duration of user connections, the specific services and applications accessed, and the volume of data transferred. This comprehensive accounting data is indispensable for various operational functions, including accurate billing for metered services, conducting thorough audits, identifying potential security anomalies, and gaining valuable insights into network usage patterns. This data can also be instrumental in capacity planning and performance tuning.
The Operational Mechanics of RADIUS Servers
RADIUS operates on a fundamental client-server model. In this architecture, the RADIUS client, which is typically a network access server (NAS) such as a VPN gateway, wireless access point, or dial-up server, initiates communication by forwarding user credentials and connection requests to the RADIUS server. The RADIUS server then meticulously processes these requests, evaluating them against its user database and predefined access policies to authenticate and authorize the user. Following this evaluation, the server dispatches a response back to the client, either granting or denying network access based on the policy outcomes.
Key features and functionalities of RADIUS servers include:
- Centralized AAA Management: Consolidating authentication, authorization, and accounting processes into a single, manageable entity.
- Support for Various Access Technologies: Compatibility with a wide range of network access methods, including Wi-Fi, VPNs, dial-up, and wired connections.
- Policy-Driven Access Control: Enabling the creation of granular policies to define access rules based on user groups, time of day, location, and other criteria.
- Extensibility and Integration: Often supports integration with directory services (like Active Directory) and other security systems.
- Standardized Protocol: Adherence to a well-defined industry standard, promoting interoperability between different vendor solutions.
The Core Purpose and Functionality of NPS
Within an organization’s network infrastructure, NPS serves as a critical element, primarily functioning as Microsoft’s sophisticated implementation of a RADIUS server and proxy. The overarching objective of NPS is to centralize and streamline the authentication, authorization, and accounting (AAA) of users and devices attempting to access a network. This consolidation significantly enhances both network security and administrative efficiency.

Centralized Authentication and Authorization:
NPS ensures that all users and devices are rigorously verified before being granted access to network resources, thereby bolstering overall security. Simultaneously, authorization mechanisms meticulously define the scope of access for authenticated entities, specifying precisely which network resources they are permitted to utilize. NPS manages these critical functions through several key mechanisms:
- Connection Request Policies: These policies determine whether a connection request is processed by NPS itself or forwarded to another RADIUS server. They can be configured based on various criteria, such as the client’s IP address or the type of connection.
- Network Policies: These policies are the core of NPS’s authorization capabilities. They define the conditions under which users and devices are granted or denied network access, as well as the specific network access parameters (e.g., connection type, VLAN assignment, bandwidth limits). Policies can be based on user group membership, time of day, the client’s IP address, the type of NAS, and even the health status of the client device if integrated with Network Access Protection (NAP).
Accounting and Compliance:
NPS plays a crucial role in network accounting by meticulously tracking and logging user activities and resource utilization. This detailed record-keeping is vital for auditing purposes, security monitoring, and ensuring compliance with regulatory standards. The data collected by NPS can provide irrefutable evidence of network access events, which is essential for:
- Auditing: Facilitating internal and external audits by providing a clear trail of who accessed what, when, and from where.
- Troubleshooting: Assisting in diagnosing network connectivity issues by examining access logs.
- Security Incident Response: Providing critical data for investigating security breaches and understanding the scope of an incident.
- Compliance Reporting: Helping organizations meet the stringent reporting requirements of various industry regulations by offering detailed usage and access logs.
Policy-Based Network Management:
NPS empowers administrators to create and enforce specific network access policies, allowing them to tailor network security and usage precisely to their organization’s unique needs and requirements. This policy-driven approach offers a high degree of control and flexibility:
- Granular Access Control: Administrators can define highly specific access rules, ensuring that only the right users have access to the right resources at the right times.
- Dynamic Policy Enforcement: Policies can be dynamically adjusted to respond to changing security threats or business needs.
- Integration with Identity Management: NPS seamlessly integrates with directory services like Active Directory, allowing policies to be based on user group memberships, simplifying management and ensuring consistency.
Tangible Benefits of Implementing NPS
The deployment of NPS within an organization’s network infrastructure yields a multitude of benefits that significantly enhance both security posture and operational efficiency, making it a highly valuable asset for optimizing network management practices.
- Enhanced Security: By centralizing authentication and authorization, NPS significantly reduces the attack surface and strengthens the overall security of the network. It ensures that only verified and authorized entities gain access, minimizing the risk of unauthorized intrusions and data breaches.
- Streamlined Administration: NPS simplifies the complex task of managing network access for numerous users and devices. Administrators can define and manage policies from a central location, eliminating the need for individual configurations on each access device. This consolidation leads to reduced administrative overhead and a lower risk of human error.
- Improved Compliance: The robust accounting and logging capabilities of NPS are instrumental in helping organizations meet stringent regulatory compliance requirements. Detailed audit trails provide the necessary evidence for compliance audits and demonstrate a commitment to secure data handling practices.
- Increased Scalability: NPS is designed to handle a large volume of authentication and authorization requests, making it suitable for organizations of all sizes, from small businesses to large enterprises. Its architecture allows for scaling to accommodate growing network demands.
- Cost Savings: By preventing security incidents, reducing administrative workload, and optimizing network resource utilization, NPS can contribute to significant cost savings for organizations. It helps avoid the financial repercussions of data breaches and downtime.
- Flexibility and Customization: NPS offers a high degree of flexibility, allowing administrators to create custom policies tailored to specific organizational needs. This adaptability ensures that the network access controls align perfectly with business objectives and security policies.
- Centralized Visibility and Control: NPS provides a unified view of network access attempts and policy enforcement, giving administrators better visibility and control over who is accessing the network and how.
The Three Distinct Roles of NPS
NPS effectively fulfills three critical and interconnected roles within a network environment, each contributing to its comprehensive network management capabilities.
-
NPS as a RADIUS Server:
In its primary role as a RADIUS server, NPS directly processes authentication and authorization requests originating from network access servers. When a user or device attempts to connect to the network—whether via Wi-Fi, VPN, or a wired connection—NPS receives these requests, verifies the presented credentials against its configured policies and potentially against external directories like Active Directory, and then makes a decision to grant or deny access. NPS can also provide specific network access parameters, such as IP addresses or VLAN assignments, back to the network access server. This role is crucial for securing remote access, wireless networks, and any network segment that requires centralized authentication. NPS’s ability to work with a wide variety of network access servers makes it a versatile solution for diverse network architectures. -
NPS as a RADIUS Proxy:
In more complex or geographically distributed network environments, NPS can function as a RADIUS proxy. In this capacity, NPS does not process authentication requests itself but rather forwards them to other RADIUS servers located elsewhere in the network. This is particularly useful for load balancing requests across multiple RADIUS servers, ensuring that no single server becomes a bottleneck. Furthermore, it enables failover mechanisms: if a primary RADIUS server becomes unavailable, NPS can automatically redirect requests to a secondary server, ensuring continuity of network access. This proxy functionality is invaluable for large organizations with multiple authentication servers or for federated authentication scenarios where requests need to be routed to external RADIUS servers. It facilitates seamless cross-network authentication and management, simplifying the administrative burden in intricate network topologies. -
NPS as a Network Policy Server:
This role highlights NPS’s core functionality in defining, managing, and enforcing network access policies. NPS acts as the central authority for determining the conditions under which users and devices are permitted or denied network access. This includes creating sophisticated policies based on a wide array of conditions, such as user group membership, time of day, the type of network connection, the client’s IP address range, and even the health status of the client device through integration with Microsoft’s Network Access Protection (NAP) framework. By leveraging these policies, administrators can implement granular access controls, ensuring that network access is granted only to compliant and authorized entities, thereby enhancing security and maintaining control over network resources. This role is fundamental to implementing a zero-trust security model within an organization’s network.
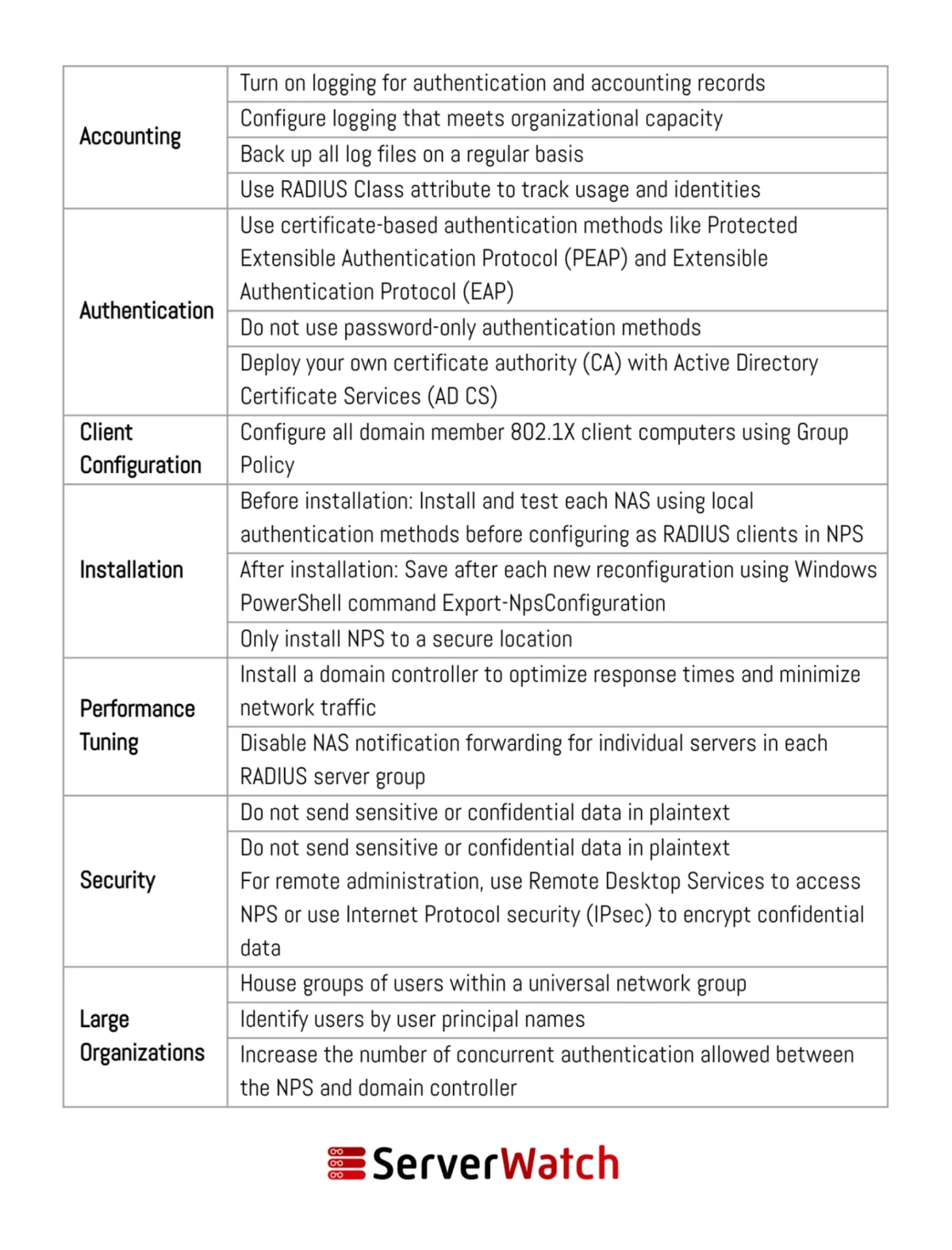
NPS Best Practices for Optimal Deployment and Management
Effective utilization of NPS hinges on adhering to specific network and server management best practices. These recommendations, often provided by Microsoft and industry experts, ensure that NPS operates efficiently, securely, and in alignment with an organization’s overarching network management objectives.
- Secure Communication Channels: Always configure NPS to use secure communication protocols, such as TLS/SSL, for RADIUS traffic to prevent eavesdropping and man-in-the-middle attacks. While RADIUS itself uses UDP ports, secure tunnels or IPsec can be employed to protect the communication.
- Strong Authentication Methods: Implement multi-factor authentication (MFA) wherever possible. While NPS supports various authentication protocols (EAP-TLS, PEAP, EAP-MSCHAPv2), combining them with an MFA solution significantly strengthens the authentication process.
- Principle of Least Privilege: Apply the principle of least privilege when configuring NPS policies. Grant users and devices only the necessary access rights and permissions required for their roles. Avoid overly broad policies that could inadvertently grant excessive access.
- Regular Policy Review and Updates: Network access policies are not static. Regularly review and update NPS policies to reflect changes in organizational structure, security threats, and business requirements. Outdated policies can become security vulnerabilities.
- Robust Logging and Monitoring: Configure NPS to generate detailed logs for authentication, authorization, and accounting events. Implement a centralized logging solution (e.g., SIEM) to monitor these logs for suspicious activity, policy violations, and potential security incidents in near real-time.
- RADIUS Client Configuration: Ensure that all RADIUS clients (network access servers) are accurately configured with the correct shared secrets and IP addresses. These shared secrets should be strong and unique for each client.
- Server Hardening: Treat the NPS server as a critical security component. Apply all relevant security patches and updates promptly. Implement host-based firewalls and restrict unnecessary services running on the NPS server.
- Backup and Disaster Recovery: Regularly back up NPS configurations and user databases. Develop and test a disaster recovery plan to ensure that NPS services can be restored quickly in the event of a hardware failure or other disaster.
- Segregate NPS Servers: For larger environments, consider segregating NPS servers into different network segments or using multiple NPS servers for redundancy and load balancing. This improves resilience and performance.
- Utilize NPS Templates: Leverage NPS policy templates where appropriate. These templates can provide a starting point for common scenarios and help ensure consistency in policy creation.
The Bottom Line: The Indispensable Role of NPS in Modern Network Management
Network Policy Server (NPS) has firmly established itself as an indispensable network and server tool, offering a powerful, flexible, and scalable solution for ensuring secure and efficient network operations. The strategic integration of NPS within an organization’s network infrastructure not only significantly enhances security by enforcing rigorous access policies but also dramatically simplifies administrative tasks, leading to more efficient management of network resources and a reduced administrative burden.
By diligently adhering to established best practices in the deployment and ongoing management of NPS, organizations can substantially mitigate the inherent risks associated with network security. This proactive approach ensures a more seamless and secure operational flow, protecting valuable data and maintaining business continuity in an ever-evolving threat landscape. As organizations continue to grow and their reliance on digital infrastructure intensifies, the role of NPS in maintaining a secure, controlled, and efficient network environment becomes increasingly critical.
For organizations looking to further optimize their NPS functionality and performance, exploring specialized tools for RADIUS server testing and monitoring can provide invaluable insights and proactive management capabilities. Leveraging expert-selected and reviewed tools can help identify potential issues before they impact network operations and ensure the continued robust performance of this vital security component.