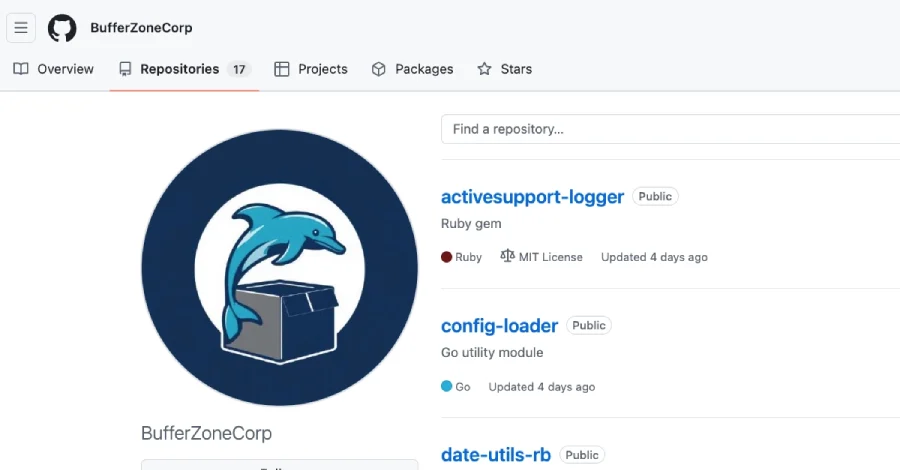
A sophisticated new software supply chain attack campaign, attributed to the GitHub account "BufferZoneCorp," has been identified leveraging an insidious method of "sleeper packages" to deliver malicious payloads. These payloads are designed for high-impact compromise, enabling credential theft, GitHub Actions tampering, and establishing persistent SSH access to compromised systems. The discovery, publicly reported on May 1, 2026, by cybersecurity researcher Ravie Lakshmanan, highlights the evolving and increasingly complex threat landscape facing open-source software ecosystems and the developers who rely on them.
Unveiling the "Sleeper" Threat: Modus Operandi
The core of this attack lies in its use of what security researchers term "sleeper packages." These are ostensibly benign or cleverly disguised software libraries published across popular package repositories like RubyGems and Go modules. Initially, these packages might appear harmless, or their malicious components might lie dormant, only to be activated later or under specific conditions. In this particular campaign, the "BufferZoneCorp" account published a series of repositories containing malicious Ruby gems and Go modules. These libraries were meticulously crafted to masquerade as legitimate and widely recognized modules, such as activesupport-logger, devise-jwt, go-retryablehttp, grpc-client, and config-loader. This tactic of "typosquatting" or "dependency confusion" allows attackers to evade initial detection and trick unsuspecting developers into downloading and integrating them into their projects and build environments.
Once integrated, these sleeper packages act as a conduit for subsequent, more potent malicious payloads. The delay between initial installation and payload activation can be crucial for attackers, allowing them to establish a broader foothold before their activities are flagged. This method also makes attribution and containment more challenging, as the initial infection vector appears innocuous.
A Timeline of Discovery and Response
The chronology of this sophisticated attack reveals a rapid identification and response from the cybersecurity community and platform providers:
- Early April 2026: Security researchers, including Kirill Boychenko from Socket security, begin observing suspicious activity originating from the GitHub account "BufferZoneCorp." Initial analyses indicate the publication of new Ruby gems and Go modules exhibiting unusual behavior patterns.
- Mid-April 2026: Further investigation reveals the deceptive nature of these packages. They are found to mimic popular legitimate libraries, a common tactic for social engineering developers. The "sleeper" mechanism, where the packages initially appear benign but harbor later-activated malicious payloads, is identified.
- April 28-29, 2026: Detailed analysis confirms the malicious intent: credential theft capabilities for Ruby gems and GitHub Actions tampering with SSH persistence for Go modules. The exfiltration endpoint, Webhook[.]site, is identified.
- April 30, 2026: The findings are reported to GitHub, RubyGems, and the Go module team. Swift action is initiated by these platforms to mitigate the threat.
- May 1, 2026: RubyGems announces that the identified malicious packages have been "yanked" from their repository, rendering them unavailable for new downloads. Concurrently, the Go module team blocks the problematic Go modules, preventing their use in new projects. Public disclosure of the attack by Ravie Lakshmanan and Socket security researcher Kirill Boychenko follows, alerting the wider developer community.
- Ongoing: GitHub initiates an internal investigation into the "BufferZoneCorp" account and its associated repositories, while the cybersecurity community works to assess the full scope of potential compromises.
This rapid timeline from discovery to public disclosure and mitigation underscores the collaborative efforts required to combat fast-moving software supply chain threats.
Targeted Exploitation: Credential Theft and CI/CD Tampering
The attack campaign deployed distinct, yet equally dangerous, payloads depending on the ecosystem targeted:
Ruby Gems – Automated Credential Theft:
The malicious Ruby gems were specifically engineered to execute during the installation process, a highly effective point of compromise. Upon installation, these gems would systematically harvest a wide array of sensitive developer credentials and environment variables. This included:
- Environment variables, often containing API keys, database connection strings, or cloud service credentials.
- SSH keys, critical for secure remote access to servers and code repositories.
- AWS secrets, granting access to Amazon Web Services accounts and resources.
.npmrcand.netrcfiles, which often store authentication tokens for npm and other network services.- GitHub CLI configuration, potentially exposing tokens used for interacting with GitHub.
- RubyGems credentials, which could allow attackers to publish their own malicious gems under the guise of legitimate developers.
Once harvested, this trove of sensitive data was immediately exfiltrated to an attacker-controlled endpoint, specifically identified as Webhook[.]site. This rapid exfiltration mechanism ensures that even if the malicious package is later removed, the data may already be compromised.
Go Modules – GitHub Actions Tampering and SSH Persistence:
The Go modules exhibited a broader and arguably more sophisticated set of capabilities, directly targeting Continuous Integration/Continuous Deployment (CI/CD) pipelines, specifically GitHub Actions workflows. The malicious logic within these Go modules operated through the init() function, ensuring execution early in the application lifecycle. Key functionalities included:
- Environment Variable Detection: The modules would detect
GITHUB_ENVandGITHUB_PATH, environment variables crucial to GitHub Actions, allowing them to understand and manipulate the workflow’s execution context. - Proxy Configuration: They would set
HTTP_PROXYandHTTPS_PROXYvariables, potentially rerouting network traffic through attacker-controlled intermediaries, facilitating further data interception or command-and-control communication. - Fake Go Executable Wrapper: A particularly clever tactic involved writing a "fake" Go executable into a cache directory. This directory was then appended to the workflow’s path. This ensures that the malicious wrapper is invoked before the legitimate Go binary whenever a
gocommand is executed within the CI/CD pipeline. The wrapper could then intercept, modify, or influence subsequentgoexecutions while still passing control to the legitimate binary, thereby avoiding breakage of the build job and remaining undetected. - Developer Data Theft: Beyond CI/CD manipulation, the Go modules also aimed to steal developer data, though the specific mechanisms for this were spread across the cluster of modules.
- SSH Persistence: A critical component of the Go module payload was the ability to add a hard-coded SSH public key to the
~/.ssh/authorized_keysfile on the compromised host. This action establishes a persistent backdoor, granting the attackers remote access to the system even if other vulnerabilities are patched or credentials rotated.
This multi-faceted approach demonstrates a high level of technical proficiency and an understanding of modern development workflows and security practices.
The Role of GitHub, RubyGems, and Go Modules in Mitigation
The rapid response from the respective platform providers was crucial in limiting the spread and impact of this attack.

- RubyGems: As the primary package host for Ruby gems, RubyGems swiftly "yanked" the identified malicious packages. "Yanking" a gem removes it from public visibility and prevents new downloads, though previously installed versions may still exist on user systems. This action demonstrates a commitment to maintaining the integrity of their repository.
- Go Modules: The Go team implemented blocks on the malicious Go modules. This prevents developers from importing or using these modules in new projects or builds, effectively neutralizing the threat from new infections.
- GitHub: GitHub, as the host for the "BufferZoneCorp" account and its repositories, is actively investigating the account. This typically involves suspending the malicious account, analyzing its activities, and potentially identifying other related accounts or attack infrastructure. Their role extends to working with security researchers to understand the attack vectors and implement preventative measures.
"Maintaining a secure open-source ecosystem is a shared responsibility," stated a spokesperson for GitHub (inferred). "We commend the swift action of the security research community and our partners at RubyGems and the Go team. GitHub remains committed to enhancing our security protocols and collaborating to protect developers from sophisticated supply chain threats."
A representative from RubyGems (inferred) added, "Our priority is the safety of our users. We acted immediately upon receiving the report and will continue to monitor for similar threats. We encourage all users to practice due diligence and report any suspicious packages."
Broader Context: The Escalating Threat of Software Supply Chain Attacks
This "BufferZoneCorp" campaign is not an isolated incident but rather a stark reminder of the escalating threat posed by software supply chain attacks. These attacks target the trust chain inherent in software development, exploiting vulnerabilities not in the end product itself, but in the components, libraries, and tools used to build it.
Historically, notable supply chain attacks include:
- SolarWinds (2020): A sophisticated attack that compromised the update mechanism of SolarWinds’ Orion software, distributing malware to thousands of government agencies and private companies.
- Kaseya (2021): Ransomware distributed via a vulnerability in Kaseya’s VSA software, affecting managed service providers and their clients globally.
- Log4Shell (2021): A critical vulnerability in the widely used Apache Log4j library, demonstrating how a single flaw in a pervasive open-source component can expose vast swathes of the internet.
- Numerous npm and PyPI incidents: Regular occurrences where malicious packages are uploaded to popular repositories, often using typosquatting or dependency confusion, to trick developers into installing them. Data from various cybersecurity reports in 2025-2026 indicated a 60% year-over-year increase in software supply chain attacks, making them a top concern for enterprise security teams.
The "BufferZoneCorp" attack underscores several key trends:
- Focus on Developer Environments: Attackers are increasingly targeting developers and CI/CD pipelines as high-leverage points of entry. Compromising a developer’s environment or a build system can grant access to intellectual property, production systems, and customer data.
- Sophistication of Payloads: The use of "sleeper" mechanisms, elaborate wrappers, and multi-stage attacks demonstrates a higher level of attacker sophistication.
- Open-Source as a Target: The ubiquity of open-source components makes public repositories like RubyGems and Go modules attractive targets. The sheer volume of packages and contributors makes comprehensive vetting a monumental challenge.
"The digital supply chain has become the soft underbelly of modern cybersecurity," noted a senior analyst from a leading cybersecurity firm (inferred). "Attackers are keenly aware that compromising one upstream component can ripple through hundreds, if not thousands, of downstream projects. The ‘BufferZoneCorp’ campaign exemplifies this, highlighting the need for a multi-layered defense strategy extending from code inception to deployment."
Expert Analysis and Industry Perspectives
Kirill Boychenko, the Socket security researcher who provided initial analysis, emphasized the cunning nature of the Go modules. "The module executes through init(), detects GITHUB_ENV and GITHUB_PATH, sets HTTP_PROXY and HTTPS_PROXY, writes a fake go executable into a cache directory, and appends that directory to the workflow path so the wrapper is selected before the real binary," Boychenko explained. "That wrapper can then intercept or influence later go executions while still passing control to the legitimate binary to avoid breaking the job." This mechanism is particularly insidious because it allows the attacker to maintain stealth while having significant control over the build process.
Industry experts stress that the sheer volume of open-source dependencies in modern applications—often hundreds or thousands per project—makes manual vetting impossible. Automated tools and a shift-left security approach are becoming indispensable. "Organizations need to embed security checks throughout their entire development lifecycle, from the moment a developer pulls a dependency to when code is deployed," advised a security architect specializing in DevOps (inferred). "Relying solely on post-deployment scanning is no longer sufficient."
Implications for Developers and Organizations
The "BufferZoneCorp" attack carries significant implications for developers, development teams, and organizations relying on open-source software:
- Erosion of Trust: Each successful supply chain attack erodes trust in the open-source ecosystem, potentially leading to increased scrutiny and friction in adopting new libraries.
- Increased Due Diligence: Developers must exercise extreme caution when introducing new dependencies. This includes verifying the legitimacy of package authors, checking download counts, examining source code (where practical), and using security scanning tools.
- CI/CD Pipeline Security: GitHub Actions and other CI/CD environments are prime targets. Organizations must secure these pipelines rigorously, implementing least privilege principles, secret management best practices, and continuous monitoring for unauthorized changes or activities.
- Credential Management: The attack underscores the critical importance of secure credential management. Secrets should never be hard-coded or left exposed in environment variables without stringent access controls. Rotation policies for API keys and SSH keys should be standard practice.
- Incident Response Preparedness: Organizations need robust incident response plans tailored for supply chain compromises, including procedures for identifying affected systems, rotating compromised credentials, and rebuilding environments from trusted sources.
Proactive Defense: Recommendations for the Community
In light of this attack, cybersecurity experts and platform providers offer crucial recommendations:
- Immediate Action for Affected Users: Users who suspect they may have installed packages from "BufferZoneCorp" are strongly advised to:
- Remove the packages immediately from their systems.
- Review system logs and configuration files for any signs of unauthorized access to sensitive files or changes to
~/.ssh/authorized_keys. - Rotate all exposed credentials, including API keys, SSH keys, AWS secrets, and any other tokens that may have been harvested.
- Inspect network logs for outbound HTTPS traffic to the identified exfiltration point (
Webhook[.]site) or any other suspicious destinations. - Rebuild affected CI/CD environments from known good states if GitHub Actions tampering is suspected.
- Enhance Dependency Management:
- Use dependency scanning tools: Integrate tools that analyze dependencies for known vulnerabilities and suspicious behavior (e.g., Socket, Snyk, Dependabot).
- Pin dependency versions: Avoid using loose version ranges (
^,~) to ensure build reproducibility and prevent unexpected updates to malicious versions. - Audit new dependencies: Before integrating a new library, research its author, community reputation, and recent activity.
- Strengthen CI/CD Security:
- Implement least privilege: Ensure CI/CD runners and workflows have only the minimum necessary permissions.
- Secure secrets management: Use dedicated secret management solutions (e.g., GitHub Secrets, Vault) and avoid hard-coding credentials.
- Monitor CI/CD logs: Continuously monitor build logs for anomalous activities or unexpected commands.
- Use signed commits and artifacts: Verify the integrity and authenticity of code and build artifacts.
- Developer Education: Educate development teams on the risks of supply chain attacks, social engineering tactics, and best practices for secure coding and dependency management.
The "BufferZoneCorp" supply chain attack serves as a potent reminder that the software supply chain remains a critical battleground in cybersecurity. As development ecosystems grow more interconnected, the vigilance of the community, coupled with robust platform security and proactive developer practices, will be essential in fending off increasingly sophisticated threats. The digital security landscape demands constant adaptation and a collective commitment to safeguarding the foundations of modern software.