In a sophisticated and persistent cyber campaign, the Belarus-aligned threat actor known as Ghostwriter, also…
Tag: Security
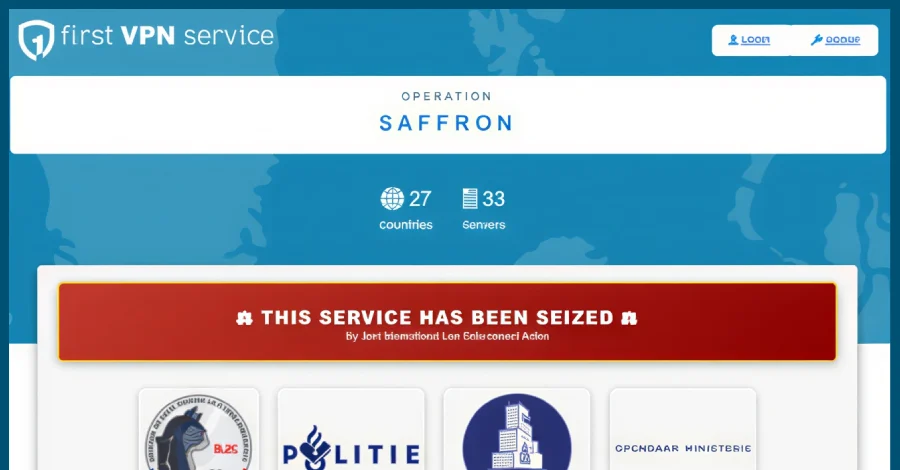
Global Law Enforcement Dismantles First VPN Service, Severing a Critical Artery for Ransomware and Cybercrime Operations
In a sweeping display of international cooperation, law enforcement agencies across Europe and North America…

2025: The Year AI Redefined Software Supply Chain Security, Ushering in Unprecedented Risks
The year 2025 marked a seismic shift in the digital landscape, not only by witnessing…
Canadian Man Arrested in International Cybercrime Takedown, Charged with Operating Kimwolf DDoS Botnet
The U.S. Department of Justice (DoJ) announced on Thursday, May 22, 2026, the successful apprehension…

Cisco Addresses Maximum-Severity Flaw in Secure Workload, Warns of Broader Exploitation Risks
Cisco has initiated the rollout of urgent security updates to address a critical, maximum-severity vulnerability…
Exploiting Trust: The Pervasive Threat of Supply Chain and Identity Attacks in Modern Cybersecurity
This week, the cybersecurity landscape once again demonstrated a subtle yet profound shift in attacker…
New Linux Malware "Showboat" Linked to China-Backed Cyber Espionage Targets Middle Eastern Telecommunications Sector
Cybersecurity researchers have unveiled details of a sophisticated new Linux malware, dubbed Showboat, which has…
Microsoft Discloses Critical Actively Exploited Privilege Escalation and Denial-of-Service Flaws in Defender, Prompting Urgent Federal Action.
Microsoft has issued an urgent disclosure concerning two critical vulnerabilities within its widely deployed Defender…

GitHub Confirms Major Internal Breach Stemming from Poisoned VS Code Extension and Widespread Supply Chain Attack
GitHub officially confirmed on Wednesday, May 21, 2026, that a significant breach of its internal…
Microsoft Unveils RAMPART and Clarity: Pioneering Open-Source Tools to Fortify AI Agent Security
Microsoft has announced the release of two groundbreaking open-source tools, RAMPART and Clarity, designed to…

