When a smartphone camera captures an image, it does more than just record light and color; it embeds a rich tapestry of metadata, an invisible digital fingerprint known as Exif (Exchangeable Image File Format) data. This often-overlooked information can include granular details about the device used, camera settings, and crucially, the precise geographical coordinates of where the photograph was taken. While seemingly innocuous, sharing photos without awareness of this embedded data can inadvertently expose highly sensitive personal information, including one’s exact home address, raising significant privacy concerns for individuals in the digital age.
Understanding EXIF Data: The Hidden Metadata of Digital Photography
EXIF data is a standard that specifies formats for images, sound, and ancillary tags used by digital cameras, scanners, and other systems handling image and sound files recorded by digital cameras. First introduced in 1995 by the Japan Electronic Industries Development Association (JEIDA), EXIF was designed to standardize the technical information associated with digital photographs. Its purpose was to allow photographers and photo editing software to understand how a picture was taken, mimicking the handwritten notes that professional photographers once kept for film exposures.
Over the years, as digital photography evolved from dedicated cameras to ubiquitous smartphone integration, the scope of EXIF data expanded dramatically. Early digital cameras primarily recorded technical details like shutter speed, aperture, ISO sensitivity, focal length, and the date and time of capture. With the advent of GPS technology in consumer electronics, particularly smartphones, the capability to embed precise geographical coordinates directly into the EXIF data became a standard feature. This innovation, while immensely useful for organizing photos by location or reliving memories on a map, introduced a new dimension of privacy vulnerability.
Today, a typical smartphone photo’s EXIF data can contain:

- Device Information: Make and model of the smartphone/camera.
- Camera Settings: Aperture, shutter speed, ISO, flash status, white balance.
- Timestamp: Date and time the photo was taken.
- Geolocation Data: GPS coordinates (latitude, longitude, altitude), sometimes including compass direction.
- Image Orientation: How the photo was held (portrait or landscape).
- Software Information: The software used to process or edit the image.
- Copyright Information: Optionally, the photographer’s name or copyright details.
This extensive dataset, embedded automatically at the moment of capture, remains with the image file unless explicitly removed or modified.
The Double-Edged Sword: Utility Versus Privacy Risk
For many, EXIF data serves a valuable purpose. Professional photographers rely on it to analyze their techniques, recreate specific shots, or manage their vast archives. Photo enthusiasts use it to learn from others’ work by examining the settings used for compelling images. For individuals, geolocation data allows for effortless organization of travel photos, creating a visual diary mapped to specific places. Image recognition software can also leverage EXIF data to enhance search and categorization capabilities, as seen in advanced photo gallery applications.
However, the convenience and utility of EXIF data come with a significant privacy cost, especially concerning geolocation. The ease with which this data can be extracted means that an innocent share can inadvertently disclose private information to unintended recipients. Imagine sharing a photograph of a new pet taken inside your home with a casual online acquaintance. If that photo contains embedded GPS coordinates, that acquaintance now has your exact home address. This scenario is not theoretical; it represents a tangible risk with potentially severe consequences.
Privacy advocates frequently highlight the dangers posed by readily available geolocation data. These risks include:
- Stalking and Harassment: Malicious actors can use location data to track individuals, learn their routines, and identify their residences or workplaces.
- Property Crime: Disclosing your home location while you’re on vacation (as indicated by photos from a distant location) could alert criminals to an empty house.
- Corporate Espionage: Photos taken within sensitive corporate environments, even if seemingly innocuous, could reveal the location of proprietary operations or facilities.
- Personal Safety: Children and vulnerable individuals are particularly at risk if their location data is exposed through shared images.
- Digital Footprint and Profiling: Over time, a collection of geotagged photos can create a detailed map of an individual’s movements, habits, and frequented locations, which could be used for profiling by marketers or, more nefariously, by surveillance entities.
The "innocent share" is often the gateway to these privacy breaches. A photo posted on social media, sent through a messaging app, or uploaded to a public forum can be analyzed for its EXIF data, potentially revealing much more than the user intended. Tools and websites exist that can easily extract and display all EXIF information from an uploaded image, with some even mapping the GPS coordinates onto a public map service. One such service, AnyExif, allows users to quickly inspect their photos, revealing details like the phone model and, if saved, the precise coordinates, processing data locally to maintain user privacy during the check.
A Growing Concern: Data Privacy in the Digital Age
The issue of EXIF data and geolocation privacy is part of a broader global conversation about data privacy and digital rights. With billions of smartphones in circulation and trillions of photos shared annually, the sheer volume of potentially sensitive metadata circulating online is staggering. Reports consistently show that a significant portion of internet users are concerned about their online privacy, yet many remain unaware of the specific data points embedded in their digital photos.
According to various industry reports, global smartphone penetration surpassed 80% of the world’s population in 2023, with an estimated 4.3 billion active users. Each of these devices is capable of capturing and storing EXIF data. Social media platforms, which thrive on user-generated content, have become primary conduits for sharing photos. Platforms like Instagram, Facebook, and Snapchat collectively host billions of images, with new uploads occurring every second. While many major social media and messaging platforms have implemented measures to strip EXIF data, especially geolocation, upon upload or sharing, these safeguards are not universal, nor are they always guaranteed across all sharing methods or applications. For instance, direct file transfers or uploads to cloud storage services often retain all original EXIF data.
The regulatory landscape is also evolving in response to these concerns. Laws like the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the United States emphasize user control over personal data. While these regulations don’t specifically target EXIF data, they underscore the principle that individuals should be informed about what data is collected about them and have the right to control its dissemination. This legislative push, coupled with increasing public awareness campaigns by privacy advocates, has put pressure on technology companies to offer more robust privacy controls.
Industry Responses and User Empowerment
Recognizing the privacy implications, both operating system developers and application providers have begun to offer tools and features to manage EXIF data. However, the implementation and accessibility of these features vary significantly.

Operating System Level Controls:
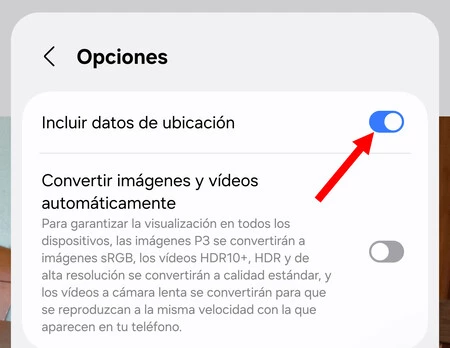
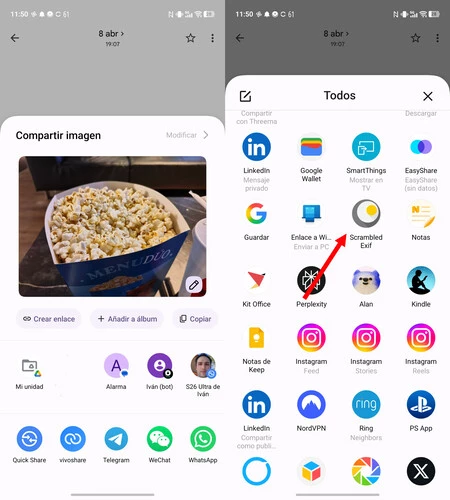
- Android: The Android ecosystem, characterized by its fragmentation across numerous manufacturers (OEMs), offers varying levels of EXIF management. While some OEM gallery apps, like Samsung’s, include a straightforward option to remove location data when sharing a photo (often found in the "Options" menu during the sharing process), this is not a universal feature. Stock Android, as seen in Google Photos, has historically lacked a default option to strip EXIF data during sharing, though users can manually remove location information from individual photos within the app’s info panel. This inconsistency necessitates a more proactive approach from users. Third-party applications like
Scrambled Exiffor Android act as an intermediary, creating a "safe bridge" that automatically strips all identifying metadata from an image before it is shared through any chosen application. This provides a crucial layer of security for users who frequently share photos and want to ensure their privacy. - iOS: Apple’s Photos app offers a more integrated and user-friendly approach to managing location data. When sharing an image from the Photos app, users can tap the "Options" button at the top of the sharing sheet. Here, they can easily toggle off "Location" to prevent the exact GPS coordinates from being included with the shared photo. This feature is a testament to Apple’s long-standing emphasis on user privacy and provides a simple, built-in solution for iPhone users.
Application Level Safeguards:
Major messaging and social media platforms have, in recent years, taken steps to address EXIF data privacy. Applications such as WhatsApp, Telegram, Instagram, and TikTok typically remove geolocation and other sensitive EXIF data by default when images are uploaded or sent through their services. This is a vital safeguard, as these platforms are primary channels for photo sharing. However, users should not assume this is always the case for every application or every sharing method. For instance, sending a photo via email as an attachment or uploading it to certain cloud storage services might retain the full EXIF dataset. It is always prudent to verify the privacy settings of any application before sharing sensitive content.
Privacy experts consistently emphasize that while platform-level safeguards are welcome, ultimate responsibility lies with the user. "The digital world requires a new form of literacy," states a prominent cybersecurity analyst. "Understanding what data your devices generate and how it’s shared is as important as knowing how to use the device itself. Assume nothing and verify everything when it comes to personal data." This sentiment underscores the need for greater digital education and user empowerment.
Practical Steps for Safeguarding Your Location Data
Given the complexities and varied implementations of EXIF data management, users must adopt proactive habits to protect their privacy:
- Disable Location Services for Your Camera App: The most effective preventative measure is to stop your camera app from recording location data in the first place. This can be done in your smartphone’s system settings under "App Permissions" or "Location Services." Find your camera app and set its location access to "Never" or "Ask next time." While this prevents future photos from being geotagged, it will not remove location data from photos already taken.
- Utilize Built-in Sharing Options: Before sharing a photo, especially on iOS or through some Android gallery apps (like Samsung’s), check for "Options," "Settings," or "Details" within the sharing interface. Look for toggles related to "Location," "Metadata," or "EXIF data" and disable them.
- Employ Third-Party EXIF Stripping Apps: For Android users, apps like
Scrambled Exifprovide a reliable and consistent way to remove metadata from photos before sharing. Make it a habit to route your shares through such an app if your device’s native options are insufficient or inconsistent. - Inspect Your Photos: Periodically use tools like
AnyExif(which processes data locally for privacy) or dedicated EXIF viewer apps to inspect your photos. This helps you understand exactly what data is embedded in your images and reinforces the importance of conscious sharing. - Be Mindful of Direct File Transfers: When sending photos directly via email attachments, Bluetooth, or cloud storage synchronization, assume that all EXIF data, including location, will be preserved. Consider using a dedicated EXIF remover beforehand or sending photos through platforms known to strip metadata.
- Educate Yourself and Others: Share this knowledge with friends and family. A collective awareness of these digital privacy nuances can significantly enhance overall online safety.
The Broader Implications: A Call for Digital Literacy
The issue of EXIF data is a microcosm of the larger challenges surrounding data privacy in an increasingly connected world. Beyond just location, the device model, timestamp, and other technical details within EXIF data contribute to one’s digital footprint. This footprint, when aggregated and analyzed, can reveal patterns of behavior, personal preferences, and even vulnerabilities.
As technology continues to advance, the line between convenience and privacy will become even blurrier. Features like advanced facial recognition, AI-powered image analysis, and increasingly sophisticated metadata collection mechanisms will continue to emerge. Therefore, fostering digital literacy – the ability to find, evaluate, create, and communicate information on digital platforms – is paramount. This includes understanding the inherent data trails left by our digital activities, making informed choices about privacy settings, and advocating for stronger data protection policies.
In conclusion, every photo we capture and share carries an invisible payload of data. While this metadata can be beneficial, the inclusion of precise geolocation information poses a tangible risk to personal privacy and safety. By understanding what EXIF data is, recognizing its potential implications, and adopting proactive measures to manage it, individuals can reclaim control over their digital footprint and navigate the complexities of the online world with greater security and confidence. The power to protect one’s privacy in the digital realm often begins with a conscious decision before tapping the "share" button.

