Cybersecurity researchers are sounding a critical alarm following the discovery of a sophisticated supply chain attack campaign, dubbed "mini Shai-Hulud," which has actively targeted SAP-related npm packages with credential-stealing malware. This incident, identified and reported on April 29, 2026, marks a significant escalation in the ongoing battle against software supply chain vulnerabilities, directly impacting the integrity of development environments tied to one of the world’s leading enterprise software providers. The coordinated disclosure from leading security firms including Aikido Security, SafeDep, Socket, StepSecurity, and Google-owned Wiz, paints a grim picture of an evolving threat landscape where critical developer infrastructure is increasingly under siege.
The "mini Shai-Hulud" Campaign Unveiled: A New Front in Supply Chain Warfare
The "mini Shai-Hulud" campaign represents a highly targeted and stealthy operation designed to compromise development environments, specifically those leveraging SAP’s extensive JavaScript and cloud application development ecosystem. The attack meticulously infiltrated several key npm packages associated with this ecosystem, injecting malicious code that activates during the installation process. This sophisticated approach leverages the trusted nature of popular software repositories, turning widely used development components into vectors for malicious activity.
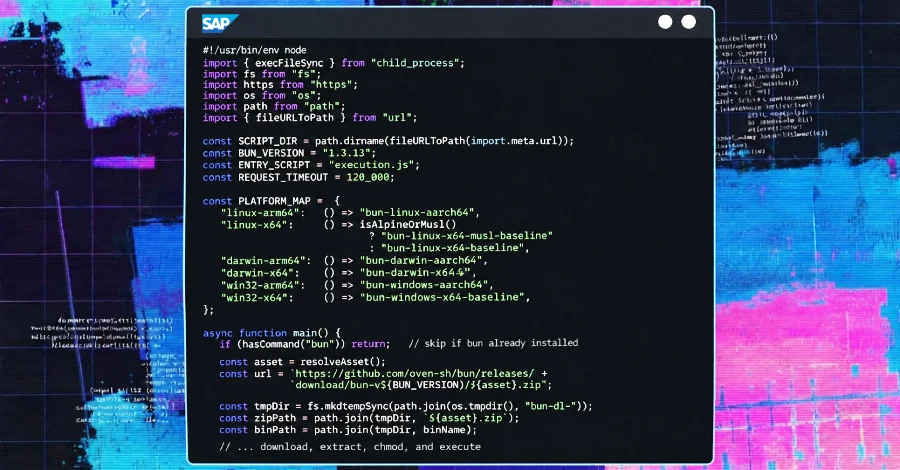
According to the joint reports, the compromised releases introduced new, uncharacteristic installation-time behavior. Instead of benign setup routines, the malicious versions integrated a preinstall script. This script acts as a runtime bootstrapper, initiating a covert download of a platform-specific Bun ZIP archive directly from GitHub Releases. Upon successful download, the archive is extracted, and the embedded Bun binary is immediately executed. This method allows the attackers to bypass typical security checks and execute arbitrary code within the developer’s environment, setting the stage for subsequent malicious operations. The use of PowerShell with -ExecutionPolicy Bypass on Windows further amplifies the risk, effectively disabling a crucial security safeguard and increasing the attack’s potency in affected developer and CI/CD environments.
A Deeper Look at the Modus Operandi: Credential Theft and Propagation
The core objective of the "mini Shai-Hulud" malware is multi-faceted, focusing primarily on comprehensive credential theft and self-propagation to maximize its reach and impact. The execution.js framework, deployed by the Bun JavaScript runtime, is engineered to harvest a wide array of sensitive information from compromised systems. This includes local developer credentials, GitHub and npm tokens—which are critical for accessing and modifying code repositories and package registries—as well as GitHub Actions secrets, vital for automated workflows. Furthermore, the malware targets cloud secrets from major providers such as Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform (GCP), and Kubernetes, granting potential access to vast enterprise cloud infrastructures.
The stolen data undergoes encryption before being exfiltrated to public GitHub repositories. Alarmingly, these repositories are not created by the attackers themselves but are generated on the victim’s own GitHub account, bearing the distinct description: "A Mini Shai-Hulud has Appeared." As of the initial reports, over 1,100 such repositories have been identified, serving as clandestine drop zones for the exfiltrated data. This method not only obfuscates the true origin of the exfiltration but also leverages the victim’s own reputation and infrastructure for malicious ends, complicating detection and remediation efforts.
Beyond data theft, the 11.6 MB payload boasts advanced self-propagation capabilities. Utilizing the stolen GitHub and npm tokens, the malware injects malicious GitHub Actions workflows directly into the victim’s repositories. These injected workflows are designed to steal additional repository secrets and, crucially, to publish further poisoned versions of npm packages back to the public registry. This creates a dangerous feedback loop, effectively transforming compromised developer accounts and CI/CD pipelines into launchpads for subsequent attacks, significantly expanding the campaign’s blast radius across the software supply chain.
Background: The Rising Tide of Software Supply Chain Attacks

This latest incident is a stark reminder of the escalating threat posed by software supply chain attacks. These attacks exploit vulnerabilities in the development and delivery process of software, rather than directly targeting end-users or corporate networks. By compromising a single component or dependency, attackers can inject malicious code into a vast number of downstream applications and systems. High-profile incidents like SolarWinds, Log4j, and numerous npm package compromises in recent years have highlighted the profound impact and far-reaching consequences of such attacks, making them a top concern for cybersecurity professionals globally.
The npm ecosystem, a cornerstone of modern JavaScript development, is particularly vulnerable due to its vastness, interconnectedness, and reliance on thousands of open-source packages. Developers frequently incorporate numerous third-party dependencies into their projects, often without granular scrutiny of each package’s origin or integrity. This creates an expansive attack surface, where a single compromised maintainer account or a cleverly crafted malicious package can infect thousands of projects.
SAP’s involvement further elevates the criticality of this attack. As a dominant provider of enterprise resource planning (ERP) software and business applications, SAP solutions are integral to the operations of countless global corporations. The compromise of SAP-related development tools, such as those within the Cloud Application Programming (CAP) model, can have catastrophic downstream effects, potentially exposing sensitive corporate data, disrupting critical business processes, and eroding trust in enterprise software. Developers using SAP CAP for building cloud-native applications are directly in the crosshairs, making the integrity of these foundational packages paramount.
The Threat Actor: Tracing "TeamPCP" and "Shai-Hulud"
Wiz’s analysis has strongly linked the "mini Shai-Hulud" campaign to previous operations attributed to the threat actor known as "TeamPCP." This attribution suggests a persistent and evolving adversary with a proven track record of sophisticated supply chain attacks. Prior "Shai-Hulud" waves have demonstrated the group’s capabilities in compromising developer accounts and injecting malicious code into widely used packages. This latest iteration, however, introduces several significant differences, indicating a refinement of tactics and an adaptation to contemporary development practices.
Notably, StepSecurity highlighted a key evolution: "This is one of the first supply chain attacks to target AI coding agent configurations as a persistence and propagation vector." This signals a forward-looking approach by the attackers, aiming to exploit the burgeoning integration of artificial intelligence into development workflows. By compromising AI coding agents or their configurations, the attackers could establish persistent access, manipulate code suggestions, or even automate the injection of malicious code, posing a new and complex challenge for securing the software development lifecycle. The continuous evolution of "TeamPCP’s" methods underscores the need for constant vigilance and adaptive security strategies within the developer community.
A Critical Flaw: Exploiting OIDC Trusted Publishing
Further in-depth analysis into the root cause of the "mini Shai-Hulud" campaign has uncovered critical configuration gaps within the npm OIDC (OpenID Connect) trusted publishing mechanism, combined with direct account compromises. The attackers initially gained unauthorized access to the RoshniNaveenaS account, which maintained three @cap-js packages. With this access, they pushed a modified workflow to a non-main branch within the repository. Crucially, this modified workflow was then used to extract an npm OIDC token, enabling the publication of malicious packages without proper provenance checks.
For the mbt package, the compromise is suspected to involve a static npm token, specifically the "cloudmtabot" token, though the exact channel of this compromise remains under investigation. The shift from static tokens to OIDC trusted publishing was intended to enhance security, as OIDC tokens are short-lived and issued dynamically, reducing the risk associated with long-lived, static secrets. However, the implementation proved to be flawed in this instance.
SafeDep’s analysis revealed the "critical configuration gap" in npm’s OIDC trusted publisher for @cap-js/sqlite. The configuration was overly permissive, trusting any workflow in cap-js/cds-dbs, rather than strictly adhering to the canonical release-please.yml on the main branch. This allowed a malicious actor, after compromising an account and pushing a workflow to a non-main branch, to manually reproduce the OIDC token exchange within a CI step. Provided the workflow had id-token: write permission and referenced the environment: npm, it could successfully request and obtain a short-lived npm token, which was then used to publish the poisoned packages. This demonstrates that even advanced security mechanisms like OIDC can be undermined by misconfigurations, highlighting the complexity of securing modern CI/CD pipelines.

Immediate Response and Mitigation Efforts
The swift and collaborative response from the cybersecurity research community and the affected package maintainers has been crucial in containing the "mini Shai-Hulud" campaign. The suspicious versions of the packages were published on April 29, 2026, between 09:55 UTC and 12:14 UTC. Upon discovery, the maintainers of the compromised SAP-related packages, including those under SAP/cloud-mta-build-tool and cap-js/cds-dbs, acted rapidly to address the incident. They promptly released new, safe versions that supersede the malicious releases, effectively removing the compromised code from the public npm registry.
While official statements from SAP, npm, or GitHub were not explicitly detailed in the initial reports, it is highly probable that these entities are working in close coordination. SAP would likely issue official security advisories to its developer community, providing specific guidance on identifying and mitigating the threat. npm would be responsible for ensuring the malicious packages are fully purged from its registry and potentially implementing stricter checks for package provenance. GitHub would likely assist in cleaning up the malicious repositories created by the exfiltration mechanism and advising affected users on securing their accounts and repositories.
For developers and organizations potentially impacted by this attack, immediate action is paramount. Critical mitigation steps include:
- Auditing Dependencies: Thoroughly review all project dependencies, especially those related to SAP’s JavaScript and CAP ecosystem, to identify any compromised versions. Update to the latest safe versions immediately.
- Revoking Credentials: All potentially exposed credentials, including local developer credentials, GitHub and npm tokens, and cloud provider secrets (AWS, Azure, GCP, Kubernetes), must be revoked and regenerated without delay.
- Repository Audit: Scrutinize GitHub repositories for the presence of "A Mini Shai-Hulud has Appeared" in descriptions, indicating potential data exfiltration. Investigate any unusual commits or new GitHub Actions workflows.
- CI/CD Environment Scrutiny: Conduct a comprehensive security audit of CI/CD pipelines and developer workstations for any signs of compromise or unauthorized activity.
- Strengthening OIDC Configuration: For organizations using npm OIDC trusted publishing, a review of configuration settings is crucial to ensure that trust policies are as restrictive as possible, granting publishing permissions only to explicitly defined, canonical workflows on main branches.
Broader Ramifications for the Software Development Ecosystem
The "mini Shai-Hulud" campaign serves as a potent reminder of the fragility of trust within the software supply chain and the evolving sophistication of cyber adversaries. The attack’s focus on enterprise-critical SAP development tools, combined with its advanced propagation and credential-stealing capabilities, underscores the severe financial, reputational, and operational risks organizations face. The incident highlights the need for a multi-layered approach to supply chain security, moving beyond perimeter defenses to embed security throughout the entire development lifecycle.
The explicit targeting of "AI coding agent configurations" as a vector signifies a new frontier in cyber warfare. As AI tools become more integrated into development processes, they will present novel attack surfaces that threat actors are already beginning to exploit. This necessitates a proactive approach to securing AI-powered development environments, ensuring that these powerful tools do not inadvertently become gateways for malicious activity.
In the wake of such incidents, the industry must collectively commit to enhancing security best practices. This includes widespread adoption of robust authentication mechanisms, strict access controls, automated security scanning of dependencies, software bill of materials (SBOM) generation, and continuous monitoring of development environments. The collaboration demonstrated by the cybersecurity research community in rapidly identifying and disclosing this threat is commendable, but the onus ultimately falls on every developer and organization to embed security as a foundational principle. The "mini Shai-Hulud" incident is not merely another attack; it is a critical warning that the battle for software supply chain integrity is intensifying, demanding heightened vigilance and robust defensive strategies from all stakeholders.