Cybersecurity researchers have unveiled details of a formidable new Linux backdoor, christened PamDOORa, which is actively being marketed on the notorious Rehub Russian cybercrime forum. Offered by a threat actor operating under the alias "darkworm," this potent post-exploitation toolkit initially commanded a price of $1,600, a figure later reduced to $900, suggesting either a strategic adjustment to market demand or an intensified effort to accelerate sales. The emergence of PamDOORa underscores a critical evolution in the threat landscape targeting Linux systems, leveraging the core Pluggable Authentication Module (PAM) framework to achieve persistent access, harvest credentials, and evade detection through sophisticated anti-forensic techniques.
The discovery, brought to light by Flare.io researcher Assaf Morag, highlights PamDOORa’s design as a PAM-based module specifically engineered for post-exploitation scenarios. Its primary objective is to facilitate persistent SSH access to compromised systems, enabling attackers to maintain a foothold through a unique combination of a "magic password" and a specific TCP port. Beyond merely providing covert access, the backdoor exhibits a highly dangerous capability: it systematically harvests authentication credentials from all legitimate users who attempt to log in through the compromised system, effectively creating a trove of valuable data for subsequent malicious activities. Morag’s technical report emphasized the tool’s alleged persistence on Linux systems, specifically those running on x86_64 architectures, indicating a broad applicability across common server environments.

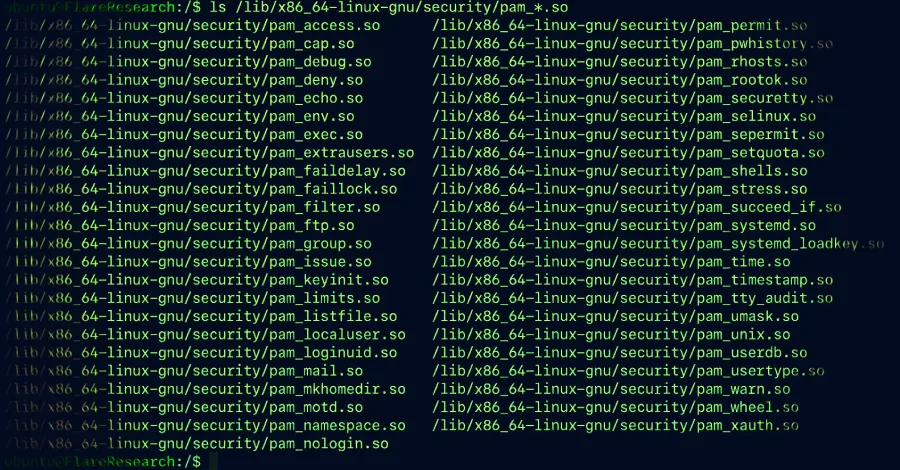
This revelation positions PamDOORa as the second significant Linux backdoor discovered within the past year to exploit the PAM stack, following the identification of "Plague" in August 2025. The increasing focus on PAM as an attack vector by cybercriminals is not coincidental. PAM is an integral security framework deeply embedded within Unix and Linux operating systems. It provides system administrators with unparalleled flexibility to integrate or update various authentication mechanisms – ranging from traditional passwords to advanced biometrics – into existing applications without requiring extensive code modifications. This modularity, while a strength for legitimate system management, paradoxically creates a powerful avenue for malicious actors.
The inherent risks associated with PAM modules stem from their privileged execution context. Typically, PAM modules operate with root privileges, meaning any compromised, misconfigured, or maliciously crafted module can introduce severe security vulnerabilities. These vulnerabilities can pave the way for unauthorized access, credential harvesting, and the establishment of stealthy persistence within a system. Industry experts have long warned about these dangers. As early as September 2024, Group-IB, a leading Singaporean security vendor, underscored the precarious balance between PAM’s modularity and its potential for exploitation. They noted, "Despite its strengths, the Pluggable Authentication Module’s (PAM) modularity introduces risks, as malicious modifications to PAM modules can create backdoors or steal user credentials, especially since PAM does not store passwords but transmits values in plaintext." Group-IB further highlighted how modules like pam_exec, which permits the execution of external commands, could be manipulated by attackers to gain illicit access or establish lasting control by injecting malicious scripts directly into PAM configuration files.
Group-IB’s detailed analysis from 2024 provided a clear illustration of how PAM configuration for SSH authentication could be tampered with to execute a script via pam_exec. This method effectively grants a malicious actor a privileged shell on the host, a critical step in facilitating stealthy and persistent control over the system. PamDOORa appears to build upon these known exploitation techniques, integrating them into a more refined and feature-rich implant.

The latest findings from Flare.io elaborate on PamDOORa’s advanced capabilities, which extend beyond mere credential theft. The backdoor is equipped with sophisticated anti-forensic mechanisms designed to systematically tamper with authentication logs. This log manipulation is crucial for threat actors, as it allows them to meticulously erase any traces of their malicious activities, making detection and subsequent incident response significantly more challenging for defenders. By scrubbing logs, PamDOORa aims to prolong its presence on a compromised system, maximizing the window for data exfiltration and further exploitation.
While there is currently no public evidence indicating that PamDOORa has been deployed in widespread real-world attacks, the existence and active advertisement of such a tool on cybercrime forums present an imminent and significant threat. The typical infection chain for malware like PamDOORa would likely involve the adversary first obtaining root access to the target host through alternative means. This initial compromise could be achieved through various vectors, including the exploitation of unpatched vulnerabilities (zero-days or known vulnerabilities), brute-force attacks against weak SSH credentials, supply chain attacks, or the deployment of other forms of malware. Once root access is secured, the attacker would then deploy the PamDOORa PAM module, effectively installing the backdoor to capture credentials and establish enduring SSH access. This makes PamDOORa primarily a post-exploitation tool, designed to solidify an attacker’s presence rather than initiating the breach itself.
Assaf Morag of Flare.io further clarified the comparative analysis between PamDOORa and other existing PAM-based backdoors, including Plague. He informed The Hacker News that while PamDOORa shares a fundamental approach with its predecessors – altering PAM behavior to enable credential capture – "small differences in the design" indicate that it does not directly overlap with any previously identified backdoors. Morag cautioned, however, that a definitive conclusion could only be reached through a direct binary comparison of the malware samples. This nuanced distinction suggests that PamDOORa is not merely a rehashed version but potentially a new, independently developed or significantly modified iteration of PAM-targeting malware, reflecting ongoing innovation within the cybercrime ecosystem.

The fluctuating price point of PamDOORa on the Rehub forum offers a glimpse into the volatile economics of the dark web malware market. The initial asking price of $1,600 on March 17, 2026, dropping to $900 by April 9, could be interpreted in several ways. It might signal a lack of immediate buyer interest, compelling "darkworm" to lower the price to stimulate sales amidst competition from other vendors offering similar or alternative tools. Alternatively, the price reduction could indicate an intent to rapidly accelerate sales, perhaps to capitalize on a fleeting opportunity, generate quick capital, or minimize exposure by moving the product swiftly. Regardless of the specific motivation, the commercial availability of such a sophisticated tool at a relatively accessible price point lowers the barrier to entry for less skilled cybercriminals, potentially broadening the scope of its deployment.
Morag underscored the evolutionary nature of PamDOORa, stating, "PamDOORa represents an evolution over existing open-source PAM backdoors." He elaborated that while the individual techniques employed – such as PAM hooks, credential capture, and log tampering – are well-documented within the cybersecurity community, their integration into a "cohesive, modular implant with anti-debugging, network-aware triggers, and a builder pipeline places it closer to operator-grade tooling than the crude proof-of-concept scripts found in most public repositories." This assessment is critical, as it highlights PamDOORa’s advanced development, suggesting it is a professional-grade tool designed for serious and persistent cyber operations rather than amateur experimentation.
The implications of PamDOORa’s emergence are far-reaching, particularly for organizations heavily reliant on Linux infrastructure, including cloud service providers, large enterprises, and critical infrastructure operators. The ability of such a backdoor to establish persistent, stealthy access and exfiltrate credentials poses a severe risk to data integrity, operational continuity, and overall security posture. Detection is made harder by the anti-forensic capabilities, meaning standard security logging and monitoring might fail to flag the compromise.

To mitigate the threat posed by PamDOORa and similar PAM-based backdoors, cybersecurity professionals must adopt a multi-layered defense strategy. This includes rigorous access control policies, ensuring the principle of least privilege is applied across all user accounts. Regular and comprehensive audits of PAM configurations (/etc/pam.d/) are essential to identify any unauthorized modifications or suspicious modules. Implementing robust File Integrity Monitoring (FIM) solutions for critical system files, especially those related to authentication and system binaries, can alert administrators to tampering attempts. Furthermore, the deployment of advanced Endpoint Detection and Response (EDR) or Extended Detection and Response (XDR) solutions tailored for Linux environments can provide deeper visibility into system processes and behaviors, helping to detect anomalous activities that might indicate a PAM compromise. Multi-factor authentication (MFA) remains a crucial defense, though it is important to note that a sophisticated PAM backdoor designed to intercept authentication after MFA might still pose a risk if not properly configured and monitored. Continuous vulnerability management, prompt patching of known vulnerabilities, and comprehensive security awareness training for all users are also indispensable components of a resilient cybersecurity framework against evolving threats like PamDOORa. The ongoing development and sale of such tools on cybercrime forums necessitate constant vigilance and proactive defense strategies from the global cybersecurity community.