A severe security vulnerability, identified as CVE-2026-33626, within LMDeploy, an open-source toolkit designed for the compression, deployment, and serving of Large Language Models (LLMs), has fallen victim to active exploitation in the wild a mere 13 hours following its public disclosure. This rapid weaponization underscores an accelerating trend where threat actors are leveraging newly revealed flaws, particularly those impacting emerging AI infrastructure, almost instantaneously. The incident serves as a stark reminder of the critical need for immediate patching and heightened vigilance in an increasingly complex cybersecurity landscape.
The Genesis of the LMDeploy Vulnerability: CVE-2026-33626
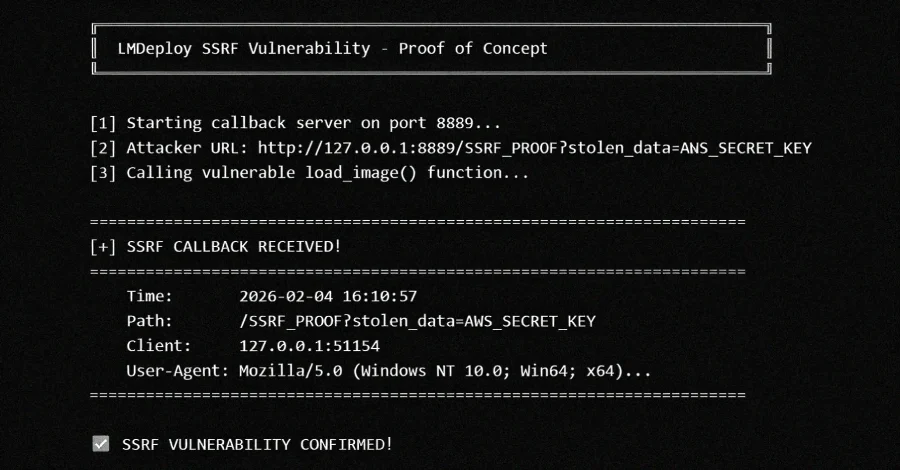
The vulnerability, assigned a CVSS score of 7.5, is categorized as a Server-Side Request Forgery (SSRF) flaw. SSRF vulnerabilities are particularly insidious as they allow an attacker to induce the server-side application to make HTTP requests to an arbitrary domain of the attacker’s choosing, potentially including internal resources. In the context of LMDeploy, this specific flaw resides within the toolkit’s vision-language module.
According to an advisory issued by the project maintainers on GitHub last week, the core issue lies within the load_image() function in lmdeploy/vl/utils.py. This function, intended to fetch image URLs, was found to be fetching arbitrary URLs without adequately validating internal or private IP addresses. This critical oversight creates a direct conduit for attackers to access cloud metadata services, internal networks, and other sensitive resources that would otherwise be shielded from external access.
All versions of the LMDeploy toolkit up to and including 0.12.0, specifically those with vision language support, are susceptible to this flaw. The discovery and responsible reporting of this bug are credited to Igor Stepansky, a security researcher affiliated with Orca Security.
Profound Implications of Successful SSRF Exploitation
The successful exploitation of an SSRF vulnerability like CVE-2026-33626 can lead to a cascade of severe consequences for affected organizations. Attackers can leverage this access to:
- Steal Cloud Credentials: By making requests to cloud metadata services (such as AWS IMDS – Instance Metadata Service), attackers can exfiltrate temporary credentials and API keys, granting them unauthorized access to cloud resources.
- Access Internal Services: The vulnerability allows attackers to bypass perimeter defenses and interact with internal services that are not exposed to the public internet, potentially compromising databases, internal APIs, or other critical infrastructure.
- Port Scan Internal Networks: Attackers can use the compromised server as a proxy to perform port scanning across the internal network, mapping out the network topology and identifying other vulnerable systems.
- Facilitate Lateral Movement: Gaining a foothold within the internal network through SSRF provides opportunities for attackers to move laterally to other systems, escalate privileges, and expand their compromise.
- Exfiltrate Sensitive Data: Depending on the internal services accessible, attackers could potentially steal proprietary data, customer information, or intellectual property.
A Chronology of Rapid Exploitation: The LMDeploy Case Study

The speed at which CVE-2026-33626 moved from public disclosure to active exploitation is a striking illustration of the current threat landscape. Cloud security firm Sysdig provided a detailed analysis, revealing that it detected the first exploitation attempt against its honeypot systems within a staggering 12 hours and 31 minutes of the vulnerability’s publication on GitHub. This near-instantaneous response highlights the sophisticated and automated nature of modern cyberattacks.
The initial exploitation attempt originated from the IP address 103.116.72[.]119. Sysdig’s observations paint a vivid picture of the attacker’s methodology. Rather than simply validating the bug and moving on, the adversary engaged in a focused, eight-minute session, meticulously utilizing the vision-language image loader as a generic HTTP SSRF primitive. During this brief window, the attacker systematically port-scanned the internal network situated behind the model server.
The targets of this internal reconnaissance included a range of critical services:
- AWS Instance Metadata Service (IMDS): A primary target for SSRF attacks, aiming to steal cloud credentials.
- Redis: A popular in-memory data store, often containing sensitive session data or application caches.
- MySQL: A widely used relational database, potentially housing vast amounts of critical data.
- A secondary HTTP administrative interface: Indicating an attempt to find alternative access points or management panels.
- An out-of-band (OOB) DNS exfiltration endpoint: Suggesting a method to covertly transmit stolen data or reconnaissance results outside the compromised network.
These actions, detected on April 22, 2026, at 03:35 a.m. UTC, unfolded over 10 distinct requests across three phases. Intriguingly, the attacker was observed switching between various vision language models (VLMs), such as internlm-xcomposer2 and OpenGVLab/InternVL2-8B. This tactic was likely employed to obfuscate their activities and avoid triggering suspicion or detection based on repetitive access patterns to a single model. The sophisticated nature of this multi-phased attack, executed within such a short timeframe after disclosure, underscores the advanced capabilities of contemporary threat actors.
The Accelerating "Collapse" in AI Infrastructure Security
The incident with LMDeploy is not an isolated event but rather a symptom of a broader, concerning pattern that security researchers have observed over the past six months. Sysdig highlights that critical vulnerabilities in AI infrastructure components—including inference servers, model gateways, and agent orchestration tools—are being weaponized within hours of their advisory publication. This rapid exploitation occurs irrespective of the size or extent of their install base, indicating a generalized and aggressive targeting strategy.
A significant factor contributing to this "collapse" in the time between disclosure and exploitation is the rise of Generative AI (GenAI). As Sysdig aptly puts it, a detailed advisory like GHSA-6w67-hwm5-92mq, which explicitly names the affected file, parameter, root-cause explanation, and even provides sample vulnerable code, effectively acts as an "input prompt" for any commercial LLM to generate a potential exploit. This paradigm shift drastically reduces the time and expertise required for malicious actors to develop working exploits, accelerating the entire attack lifecycle. The implications are profound: organizations no longer have the luxury of extended patch cycles; remediation must be near-instantaneous.
Broader Cybersecurity Landscape: Concurrent Threats
The LMDeploy incident unfolds amidst a backdrop of other significant cybersecurity threats actively being exploited, illustrating the pervasive nature of current risks:

WordPress Plugin Vulnerabilities: High-Severity Flaws in Widespread Use
Threat actors have also been observed actively exploiting critical vulnerabilities in two widely used WordPress plugins:
- Ninja Forms – File Upload (CVE-2026-0740): This vulnerability carries an alarming CVSS score of 9.8, indicating maximum severity. Wordfence, a prominent WordPress security firm, reported active exploitation of this flaw. The vulnerability allows for arbitrary file uploads to susceptible sites, which can directly lead to arbitrary code execution (RCE) and complete site takeover. Given the extensive use of Ninja Forms for creating custom forms, the potential impact on millions of websites is substantial.
- Breeze Cache (CVE-2026-3844): Also rated with a critical CVSS score of 9.8, this flaw in the Breeze Cache plugin similarly enables unauthenticated arbitrary file uploads via its
fetch-gravatar-from-remotefunctionality. An attacker leveraging this vulnerability can upload malicious files to a compromised WordPress instance, leading to RCE and full control over the affected website. The widespread adoption of caching plugins like Breeze to optimize website performance means a large number of sites are at risk if not promptly updated.
These WordPress exploits highlight the ongoing challenge of securing content management systems, where third-party plugins, while offering extended functionality, often introduce significant attack vectors if not rigorously secured and maintained.
Global Campaign Targeting Internet-Exposed Modbus PLCs: Industrial Control Systems Under Siege
Adding another layer of concern, unknown attackers have been linked to a global campaign specifically targeting internet-exposed, Modbus-enabled programmable logic controllers (PLCs). This campaign, active from September to November 2025, spanned an alarming 70 countries and implicated 14,426 distinct targeted IP addresses. The majority of these targeted IPs were located in critical infrastructure hubs across the U.S., France, Japan, Canada, and India. A subset of these malicious requests was geolocated to sources in China, suggesting a potentially state-sponsored or highly organized operation.
Cato Networks researchers, who uncovered this campaign, reported that the activity exhibited a blend of large-scale automated probing with more selective patterns. These selective patterns suggested deeper device fingerprinting, overt disruption attempts, and the identification of potential manipulation paths—especially concerning when PLCs are directly reachable from the public internet. The researchers also noted that many source IPs involved in the attacks had low or zero public reputation scores, consistent with the use of fresh or rotating scanning hosts designed to evade detection.
The targeting of Modbus PLCs is particularly alarming because these devices are fundamental components of industrial control systems (ICS) and operational technology (OT) environments, governing everything from manufacturing plants and energy grids to water treatment facilities. A successful compromise could lead to severe physical damage, widespread service disruptions, and even endanger human lives. This campaign underscores the critical vulnerability of industrial infrastructure to cyberattacks and the urgent need for robust security measures that isolate OT networks from the public internet.
Expert Commentary and Industry Reactions
Security experts consistently emphasize that these events collectively paint a picture of an increasingly aggressive and opportunistic threat landscape. "The speed of exploitation for LMDeploy is a stark wake-up call for AI developers and users," states a cybersecurity analyst. "Gone are the days when a detailed advisory allowed for weeks of patching. Now, it’s a matter of hours. This necessitates a fundamental shift in how organizations approach vulnerability management, especially for cutting-edge technologies."

The role of open-source projects like LMDeploy is also under scrutiny. While open-source fosters innovation and transparency, it also means vulnerabilities, once discovered, become public knowledge for a global audience, including malicious actors. Project maintainers face immense pressure to develop and deploy fixes immediately.
Mitigation and Best Practices: A Multi-Layered Defense
In light of these escalating threats, organizations must adopt a proactive and multi-layered approach to cybersecurity:
For LMDeploy Users and AI Infrastructure:
- Immediate Patching: All users of LMDeploy with vision language support must immediately update their installations to the patched version as soon as it becomes available. This is the single most critical step.
- Network Segmentation: Implement robust network segmentation to isolate AI inference servers and other critical infrastructure from the broader corporate network and the internet. This limits lateral movement opportunities.
- Principle of Least Privilege: Configure cloud credentials and service accounts with the absolute minimum permissions required for operation.
- Input Validation: Developers must rigorously validate all external inputs, especially URLs and file paths, to prevent SSRF and other injection attacks.
- Proactive Monitoring: Deploy advanced security monitoring solutions (e.g., SIEM, EDR, cloud security posture management) capable of detecting unusual network activity, internal scanning, and unauthorized access attempts to cloud metadata services.
- Regular Security Audits: Conduct frequent security audits and penetration tests on AI applications and their underlying infrastructure.
For WordPress Users:
- Timely Updates: Keep all WordPress core installations, themes, and plugins updated to their latest versions. Enable automatic updates where feasible and secure.
- Reputable Sources: Only install themes and plugins from reputable developers and marketplaces.
- Security Plugins: Utilize comprehensive WordPress security plugins for firewalls, malware scanning, and vulnerability detection.
- Regular Backups: Maintain regular, off-site backups of website data and databases.
For Industrial Control Systems (ICS) and Modbus PLCs:
- Reduce Internet Exposure: Critical ICS/OT devices, especially PLCs, should never be directly exposed to the public internet. Implement strict network segmentation and use secure gateways or industrial demilitarized zones (IDMZs).
- Secure Remote Access: If remote access is required, use strong authentication, VPNs, and multi-factor authentication.
- Secure Configurations: Implement secure configurations for all PLCs, disabling unnecessary services and changing default credentials.
- Continuous Monitoring: Monitor OT networks for unusual traffic patterns, unauthorized access attempts, and changes to device configurations.
- Vulnerability Management: Develop a robust vulnerability management program for OT assets, understanding that patching cycles may differ from IT environments.
Conclusion
The rapid exploitation of the LMDeploy vulnerability, coupled with ongoing campaigns against WordPress sites and critical industrial control systems, serves as an urgent call to action for organizations across all sectors. The shrinking window between vulnerability disclosure and active exploitation, significantly accelerated by Generative AI capabilities, demands an unprecedented level of agility and proactive security posture. As technology continues to evolve at a breakneck pace, so too must the strategies and defenses employed to safeguard digital assets and critical infrastructure from an increasingly sophisticated and relentless adversary.