A Network Policy Server (NPS) is an essential component for any organization seeking to establish and maintain robust control over its network access. This versatile Microsoft Windows Server feature acts as the linchpin for centralized authentication, authorization, and accounting (AAA), ensuring that only legitimate users and compliant devices can connect to and utilize network resources. In essence, NPS is Microsoft’s implementation of a Remote Authentication Dial-In User Service (RADIUS) server and proxy, playing a critical role in safeguarding network integrity and operational efficiency.
The growing complexity and interconnectedness of modern business operations, driven by an ever-increasing reliance on digital infrastructure for communication, data exchange, and service delivery, have made networks and their underlying servers prime targets for cyber threats. This heightened threat landscape necessitates a proactive and meticulously managed approach to network security. Effective policy management, spearheaded by tools like NPS, is no longer a luxury but a fundamental requirement for business continuity and data protection. The ability to precisely define who can access what, when, and under what conditions is paramount.
Understanding the critical role of NPS begins with an appreciation of the foundational principles of network access control, specifically the RADIUS protocol, and the inherent importance of network security and policy management in today’s digital ecosystem.
The Importance of Network Security and Policy Management
In an era where digital assets are often the most valuable and vulnerable, robust network security and diligent policy management are not merely best practices; they are indispensable pillars of modern enterprise operations. The pervasive nature of the internet and the increasing sophistication of cyber adversaries mean that networks, and the critical servers that power them, are constantly under siege.
Key reasons underscore the critical importance of network security and policy management:
- Protection Against Cyber Threats: Robust security measures act as the first line of defense against a barrage of threats, including malware, ransomware, phishing attacks, and distributed denial-of-service (DDoS) assaults. Effective policy management ensures that access is granted only to trusted entities, significantly reducing the attack surface.
- Data Confidentiality and Integrity: Sensitive corporate data, intellectual property, and customer information must be protected from unauthorized access, modification, or deletion. Policy enforcement ensures that data remains confidential and its integrity is maintained.
- Regulatory Compliance: Numerous industries are subject to stringent data protection regulations (e.g., GDPR, HIPAA, PCI DSS). Effective network security and policy management are crucial for meeting these compliance mandates, avoiding hefty fines, and maintaining customer trust.
- Operational Continuity: Network disruptions caused by security breaches or misconfigurations can lead to significant downtime, resulting in lost productivity, revenue, and reputational damage. Well-defined policies and secure access protocols minimize these risks.
- Resource Optimization: Policy-based access control allows organizations to allocate network resources efficiently, ensuring that bandwidth and processing power are available to authorized users and critical applications.
- Auditing and Accountability: Detailed logging and accounting capabilities, facilitated by systems like NPS, provide an audit trail of network access and usage, enabling organizations to track user activities, investigate security incidents, and ensure accountability.
The RADIUS Protocol: A Foundation for Network Access
At the heart of network access control lies the RADIUS (Remote Authentication Dial-In User Service) protocol. Developed in the early 1990s, RADIUS has evolved into an industry standard for managing network access. It operates on a client-server model to provide comprehensive and centralized Authentication, Authorization, and Accounting (AAA) for users connecting to network services.
RADIUS addresses the need for a scalable and manageable way to control who can access network resources. Before RADIUS, managing user credentials and access permissions across a growing network could be a daunting and inefficient task. RADIUS standardizes this process, enabling network administrators to centralize these critical functions.
The three core components of the RADIUS protocol are:
-
Authentication: This is the process of verifying a user’s identity. When a user attempts to connect to a network service, such as a Wi-Fi network or a VPN, they are typically prompted to provide credentials, most commonly a username and password. The RADIUS client (e.g., a wireless access point) forwards these credentials to the RADIUS server. The server then compares the provided information against its user database. If the credentials match, the user is authenticated. This fundamental step ensures that only legitimate individuals are granted entry into the network.
-
Authorization: Once a user’s identity has been confirmed through authentication, authorization determines the level of access and the specific resources they are permitted to use on the network. This process is crucial for segmenting network access and enforcing the principle of least privilege. For instance, a marketing intern might be granted access to specific shared drives and internet browsing, while a senior IT administrator would have broader permissions, including access to server management consoles. RADIUS servers evaluate policies to dictate these access rights, ensuring that users can only interact with network elements appropriate to their role and responsibilities.
-
Accounting: The final "A" in AAA, accounting, involves the systematic tracking and logging of user activity on the network. This includes details such as connection times, duration of sessions, services accessed, and the amount of data transferred. This information is invaluable for several reasons:
- Billing and Chargeback: For organizations that offer network services on a metered basis, accounting data is essential for accurate billing.
- Auditing and Compliance: Accounting logs serve as a critical audit trail, helping organizations demonstrate compliance with regulatory requirements and internal security policies.
- Network Usage Analysis: Understanding how network resources are being utilized can inform capacity planning, identify potential bottlenecks, and detect unusual activity that might indicate a security breach.
- Troubleshooting: Accounting data can aid in diagnosing network issues and understanding the context of user access problems.
What RADIUS Servers Do
RADIUS operates on a client-server architecture. The RADIUS client is typically a network access device, such as a wireless access point, a VPN concentrator, or a dial-up server. When a user attempts to connect through one of these devices, the client acts as an intermediary, sending the user’s authentication and connection request to the RADIUS server.
The RADIUS server then processes this request. It consults its user database and a set of predefined policies to determine whether to grant or deny access. Upon making a decision, the RADIUS server sends a response back to the RADIUS client. This response either permits the connection and provides any necessary configuration information (like an IP address or session timeout) or denies access.
Key features of RADIUS servers include:
- Centralized AAA Management: Eliminates the need to configure authentication and authorization on individual network devices.
- Scalability: Can support a large number of users and network access devices.
- Protocol Support: Widely adopted and supported across various network equipment vendors.
- Extensibility: Can be integrated with other security systems and databases.
- Security: Uses encryption for communication between clients and servers, protecting credentials in transit.
The Purpose of NPS

Microsoft’s Network Policy Server (NPS) extends the functionality of Windows Server by providing a fully scalable RADIUS server and RADIUS proxy. Its primary purpose is to centralize and standardize the crucial AAA processes for users and devices attempting to connect to a network. This centralization is key to enhancing both the security posture and the administrative efficiency of an organization’s network infrastructure.
NPS aims to achieve this through several key functionalities:
-
Centralized Authentication and Authorization: NPS acts as a single point of control for verifying user identities and determining their access privileges. By consolidating these functions, administrators can ensure that a consistent security policy is applied across the entire network. This prevents disparate authentication methods on individual devices, which can lead to vulnerabilities and management headaches. NPS facilitates the creation of policies that define precisely which users or groups can access specific network resources, under what conditions, and with what level of permission. This granular control is fundamental to a strong security framework.
-
Accounting and Compliance: A critical aspect of network management is the ability to track resource usage and user activity. NPS captures detailed accounting information, providing a comprehensive log of who accessed what, when, and for how long. This data is invaluable for auditing purposes, allowing organizations to verify compliance with internal policies and external regulations. For industries with strict data handling mandates, such as healthcare or finance, the detailed audit trails provided by NPS are indispensable for demonstrating adherence to legal and ethical standards, thereby mitigating risks of penalties and reputational damage.
-
Policy-Based Network Management: NPS empowers administrators to move beyond simple access control and implement sophisticated, policy-driven network management. This means that network access decisions are not static but are dynamically made based on a set of predefined conditions. These conditions can include user group membership, time of day, the location of the connection attempt, the type of network access device being used, or even the health status of the connecting device (when integrated with Network Access Protection or NAP). This dynamic policy enforcement allows for highly tailored security postures, adapting to the evolving needs and risks faced by an organization.
Benefits of Using NPS
Implementing NPS within an organization’s network infrastructure yields significant advantages, enhancing both security and operational efficiency. These benefits make NPS a cornerstone for organizations looking to optimize their network management strategies and fortify their digital defenses.
Key benefits include:
- Enhanced Security: By centralizing AAA, NPS significantly reduces the attack surface. It ensures that only authenticated and authorized users and devices gain access, preventing unauthorized entry and mitigating the risk of data breaches. Granular policy controls allow for the enforcement of the principle of least privilege, further strengthening security.
- Improved Network Management: NPS simplifies the administration of network access. Instead of configuring policies on numerous individual access points or servers, administrators can manage everything from a central console. This reduces administrative overhead, minimizes the potential for human error, and allows for quicker deployment of security updates and policy changes.
- Scalability and Flexibility: NPS is designed to scale with an organization’s growth. It can handle a large number of RADIUS clients and authentication requests, making it suitable for small businesses to large enterprises. Its flexibility allows it to integrate with various network access technologies, including Wi-Fi, VPNs, and wired connections.
- Compliance and Auditing: The robust accounting features of NPS provide detailed logs necessary for compliance with industry regulations and internal security policies. This facilitates easy auditing and investigation of security incidents.
- Support for Wireless Network Security: NPS is a critical component for implementing secure wireless networks using standards like WPA2-Enterprise and WPA3-Enterprise, which leverage 802.1X authentication. This moves beyond simple pre-shared keys to individual user authentication.
- Load Balancing and Redundancy: When deployed in a clustered configuration, NPS can provide load balancing for RADIUS requests and offer redundancy, ensuring continuous network access even if one server fails.
- Integration with Other Microsoft Technologies: NPS integrates seamlessly with other Windows Server components and Active Directory, leveraging existing user accounts and group memberships for authentication and authorization, further streamlining management.
The 3 Roles of NPS
NPS is a multifaceted tool capable of fulfilling three distinct yet interconnected roles within a network infrastructure, each contributing to comprehensive network management and security.
-
NPS as a RADIUS Server:
In its primary role, NPS functions as a full-fledged RADIUS server. When a network access device (the RADIUS client) receives a connection request, it forwards the authentication credentials and connection details to the NPS server. NPS then processes these requests, consulting its configured policies and Active Directory (or other user directories) to authenticate the user or device and determine the appropriate authorization level. This can include granting or denying access, assigning an IP address, and specifying session parameters. This role is fundamental for securing access to resources like Wi-Fi networks, VPNs, and dial-up connections. It centralizes the decision-making process for access control, ensuring consistent application of security policies across the network. -
NPS as a RADIUS Proxy:
In more complex or distributed network environments, NPS can be configured as a RADIUS proxy. Instead of directly authenticating users, the NPS proxy acts as an intermediary, forwarding authentication and configuration requests to one or more remote RADIUS servers. This is particularly useful when an organization has multiple RADIUS servers located in different geographic locations or serving different network segments. The proxy can intelligently route requests to the appropriate server based on predefined conditions, such as the client’s IP address or the user’s domain. This role also enables load balancing, distributing requests across multiple backend RADIUS servers to prevent overload and improve performance. Furthermore, it can provide failover capabilities, directing traffic to an alternate server if the primary server becomes unavailable, thereby ensuring network access continuity. -
NPS as a Network Policy Server:
This role highlights NPS’s core function of managing and enforcing network access policies. It’s here that administrators define the intricate rules governing network access. NPS allows for the creation of highly specific policies based on a wide array of conditions. For example, a policy could dictate that only members of the "IT Administrators" group can access the network between 9 AM and 5 PM on weekdays, while members of the "Guest" group are restricted to internet-only access at all times. NPS evaluates these policies against incoming connection requests to grant or deny access. It can also integrate with Network Access Protection (NAP) to enforce device health policies, ensuring that only devices meeting specific security requirements (e.g., up-to-date antivirus definitions, installed patches) are allowed to connect to the network. This granular control over network access is a hallmark of advanced network security management.
NPS Best Practices
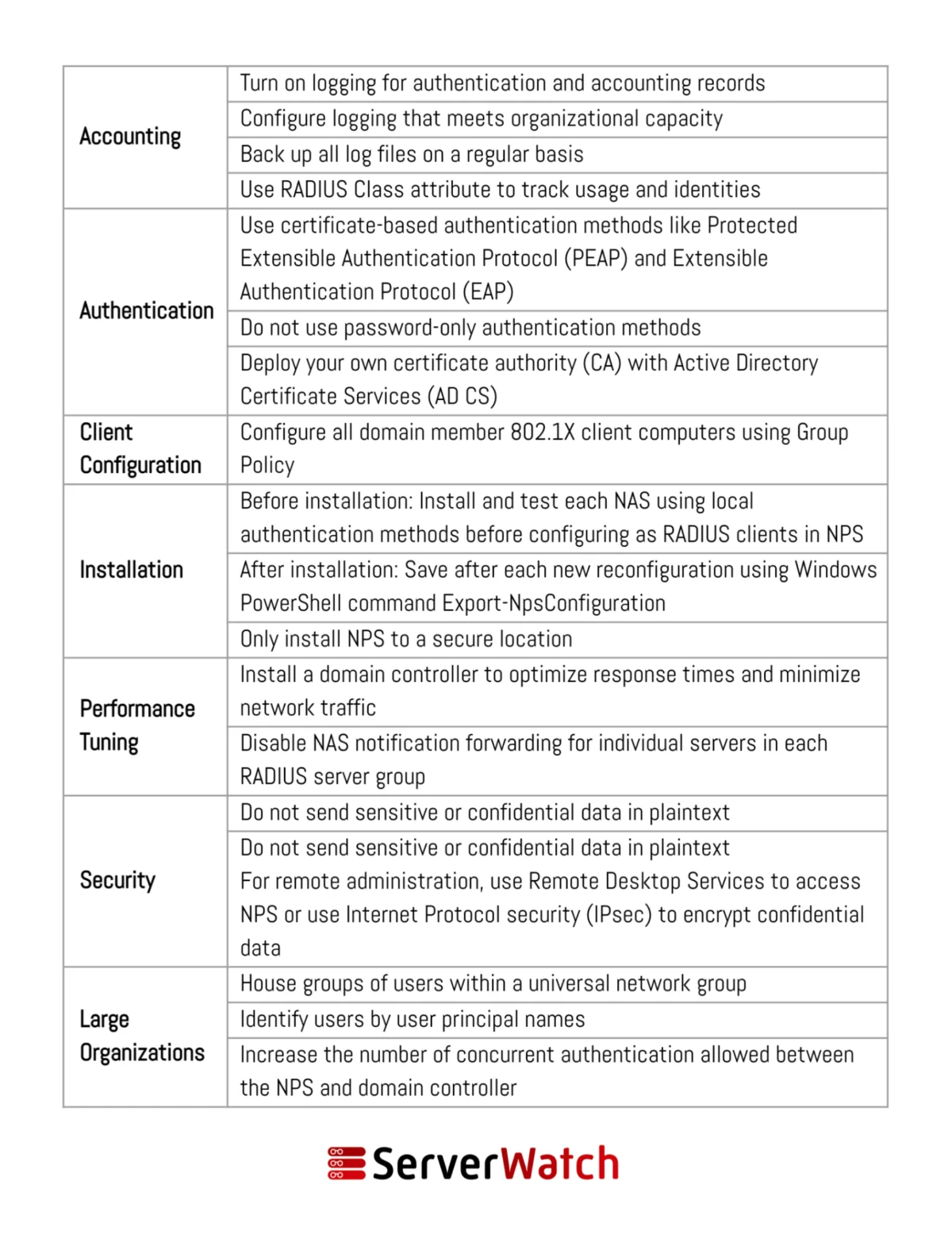
To ensure that NPS operates efficiently, securely, and in alignment with an organization’s network management objectives, adhering to established best practices is crucial. These recommendations, often provided by Microsoft and industry experts, help maximize the benefits of NPS while minimizing potential risks.
- Implement Strong Authentication Methods: While NPS supports various authentication protocols, leverage the most secure options available, such as PEAP-MSCHAPv2 for Wi-Fi or certificate-based authentication (EAP-TLS) for enhanced security. Avoid less secure methods where possible.
- Utilize Active Directory Groups: Integrate NPS with Active Directory and use security groups to manage user and device access policies. This simplifies policy administration and ensures consistency with existing user management practices.
- Configure RADIUS Clients with Shared Secrets: Ensure that the shared secrets configured on RADIUS clients (e.g., wireless access points) match precisely those configured on the NPS server. These secrets are a fundamental layer of security for RADIUS communication.
- Implement Network Policies with Specific Conditions: Create granular network policies that reflect actual business needs. Avoid overly broad policies. Define conditions based on user groups, connection types, time of day, and other relevant factors to enforce the principle of least privilege.
- Enable Accounting and Logging: Configure NPS to log connection requests, accounting information, and policy matches. Regularly review these logs for security incidents, unauthorized access attempts, and network usage patterns. Store logs securely and for an appropriate retention period.
- Deploy NPS in a Cluster for High Availability: For critical network services, deploy NPS in a cluster configuration. This provides redundancy, ensuring that network access remains available even if one NPS server fails. It also allows for load balancing of RADIUS requests.
- Secure the NPS Server Itself: Treat the NPS server as a critical infrastructure component. Secure it physically and logically, apply regular security updates, and restrict administrative access to authorized personnel only.
- Regularly Review and Update Policies: Network requirements and security threats evolve. Periodically review and update NPS policies to ensure they remain relevant, effective, and aligned with current business objectives and security best practices.
- Consider RADIUS Proxy for Scalability: In large or distributed environments, leverage the RADIUS proxy functionality of NPS to distribute the authentication load and manage access across multiple network segments or geographical locations.
- Monitor NPS Performance: Utilize performance monitoring tools to track NPS server health, resource utilization, and the volume of authentication requests. This helps identify potential bottlenecks and ensure optimal performance.
Bottom Line: The Integral Role of NPS in Modern Network Management
The Network Policy Server (NPS) has firmly established itself as an indispensable tool in the modern IT landscape, providing a robust, flexible, and scalable solution for securing and managing network access. Its ability to centralize authentication, authorization, and accounting processes, coupled with its powerful policy enforcement capabilities, makes it a cornerstone for any organization committed to maintaining a secure and efficient network environment.
By implementing NPS and adhering to best practices, organizations can significantly fortify their defenses against a growing array of cyber threats. This not only safeguards sensitive data and ensures operational continuity but also streamlines administrative tasks, reduces the complexity of network management, and supports compliance with stringent regulatory requirements. In an age where digital infrastructure is paramount, NPS provides the granular control and centralized management necessary to navigate the complexities of modern networking with confidence and security.
For organizations looking to enhance their NPS functionality and performance, exploring specialized RADIUS server testing and monitoring tools can offer deeper insights and more proactive management capabilities, further solidifying their network’s security and operational integrity.