A sophisticated and expansive Vietnamese-linked cyber operation, codenamed "AccountDumpling" by cybersecurity firm Guardio, has been uncovered, revealing the cunning use of Google AppSheet as a "phishing relay" to disseminate highly deceptive phishing emails. This campaign has led to the estimated compromise of approximately 30,000 Facebook accounts, primarily targeting business owners, with the stolen credentials subsequently funneled into an illicit underground marketplace for monetary gain. The discovery, detailed in a recent report by Guardio, underscores a persistent and evolving threat landscape where cybercriminals leverage trusted platforms to execute their malicious schemes, bypassing conventional security measures with alarming efficacy.
The Anatomy of Deception: Google AppSheet as a Phishing Conduit
The "AccountDumpling" operation distinguishes itself through its innovative exploitation of Google AppSheet, a no-code development platform designed to build mobile and web applications from data sources. By weaponizing this legitimate Google service, the threat actors have managed to send phishing emails from an ostensibly trustworthy source: [email protected]. This critical tactical maneuver allows the malicious emails to circumvent many standard spam filters, landing directly in victims’ inboxes and lending an air of legitimacy to the fraudulent communications. The implication is profound: users, conditioned to trust emails originating from reputable domains like Google, are far more likely to engage with these messages, significantly increasing the success rate of the phishing attacks.
Guardio’s security researcher, Shaked Chen, highlighted the campaign’s complexity, stating, "What we found wasn’t a single phishing kit. It was a living operation with real-time operator panels, advanced evasion, continuous evolution and a criminal-commercial loop that quietly feeds on the same accounts it helps steal back." This description paints a picture of a well-resourced and dynamically managed operation, far removed from amateur phishing attempts. The use of real-time operator panels suggests a level of interactive management, allowing the perpetrators to adapt their tactics and monitor the success of their campaigns on the fly, further refining their approach to maximize victim compromise.

Chronology of a Campaign: Evolving Lures and Global Reach
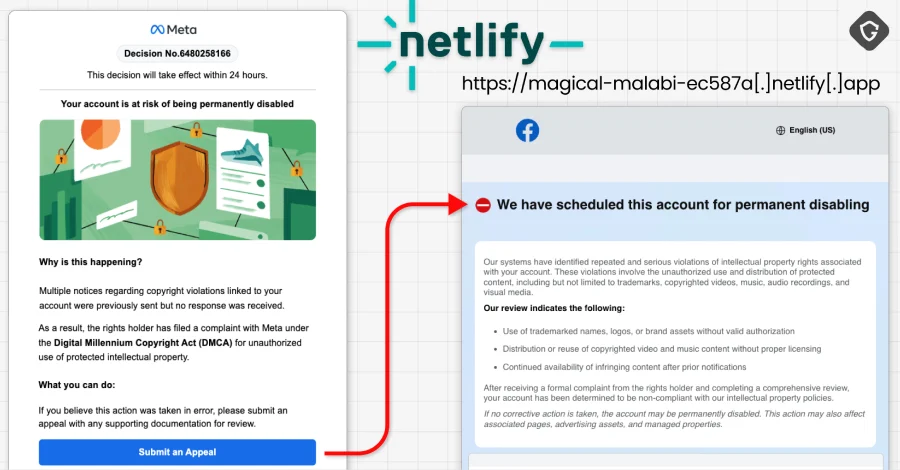
The genesis of these attacks lies in meticulously crafted phishing emails, primarily directed at owners of Facebook Business accounts. These emails are designed to induce immediate "Meta-related panic," employing a range of compelling lures. Initial tactics involved urgent appeals purportedly from "Meta Support," warning recipients of impending account deletion if they failed to submit an appeal. This false sense of urgency is a classic social engineering technique, designed to bypass critical thinking and provoke an emotional, rapid response from the victim.
Over the past several weeks and months, the threat actors have demonstrated a remarkable capacity for adaptation, diversifying their lures to maintain effectiveness and ensnare a broader spectrum of victims. These evolving pretexts have included:
- Account Disablement Warnings: Threatening the permanent closure of Facebook accounts, often citing vague violations of terms of service.
- Copyright Infringement Complaints: Falsely accusing business pages of copyright violations, demanding immediate action to avoid penalties.
- Verification Review Requests: Prompting users to "verify" their accounts or business pages, implying a loss of functionality or legitimacy if not completed.
- Executive Recruitment Opportunities: Targeting individuals with sophisticated job offers, likely aiming to gain access to professional networks or sensitive company data.
- Facebook Login Alerts: Notifying users of suspicious login attempts and urging them to "secure" their accounts by clicking a malicious link.
Each of these lures is strategically designed to exploit specific anxieties and responsibilities associated with managing a Facebook presence, particularly for businesses that rely on the platform for their operations and marketing. Upon clicking the deceptive links embedded in these emails, victims are redirected to meticulously cloned web pages that mimic official Facebook or Meta login portals. These fake pages are engineered to harvest login credentials, including usernames and passwords, which are then exfiltrated by the threat actors. The sheer volume of compromised accounts – an estimated 30,000 – speaks to the effectiveness of these highly targeted and sophisticated phishing campaigns.
The global footprint of the "AccountDumpling" operation is significant, with victims identified across numerous countries. Guardio’s analysis of the Telegram channels associated with three primary clusters of this campaign revealed approximately 30,000 victim records. The most affected regions include the U.S., Italy, Canada, the Philippines, India, Spain, Australia, the U.K., Brazil, and Mexico. This broad geographical distribution underscores the international nature of cybercrime and the widespread vulnerability to such advanced phishing techniques. The impact on these victims extends beyond mere inconvenience; being locked out of their accounts can lead to significant reputational damage for businesses, financial losses, and the potential for further fraud using their stolen identities.

Attribution: Unmasking the Operators Behind the Curtain
A pivotal breakthrough in attributing the "AccountDumpling" campaign to its orchestrators came from forensic analysis of the digital artifacts left behind. Specifically, Guardio researchers discovered "smoking gun" evidence in the metadata of PDFs generated as part of one of the campaign’s clusters. These PDFs, created using a free Canva account, contained metadata listing a Vietnamese name, "PHẠM TÀI TÂN," as the author.
This crucial piece of intelligence allowed researchers to connect the digital breadcrumbs to a real-world entity. Further open-source intelligence (OSINT) investigations led to the discovery of a website, phamtaitan[.]vn, which openly advertises digital marketing services. A post shared on X (formerly Twitter) in February 2023 from the website’s handle explicitly stated its specialization in "providing digital marketing services, marketing resources, and consulting on effective digital marketing strategies." The juxtaposition of offering legitimate digital marketing services with involvement in a large-scale phishing operation reveals a disturbing duality, suggesting that the same expertise used for legitimate purposes is being weaponized for illicit gain. This pattern of seemingly legitimate businesses engaging in or facilitating cybercrime is not unprecedented and complicates efforts to track and prosecute such actors.
Broader Context: Vietnamese Threat Actors and the Dark Market for Facebook Assets
The "AccountDumpling" operation is not an isolated incident but rather another entry in a recurring pattern of Vietnamese threat actors exhibiting a high degree of sophistication and persistence in targeting Facebook accounts. Over the past years, various reports have highlighted their diverse tactics, ranging from deploying Remote Access Trojans (RATs) via fake AI advertisements (e.g., "fake Kling AI Facebook ads") to using information stealers like the "PXA Stealer." These previous campaigns, reported in May and August 2025 respectively, illustrate a consistent focus on compromising Facebook assets for financial gain within underground ecosystems.

The illicit market for stolen social media accounts, particularly Facebook Business accounts, is robust and lucrative. These accounts are not merely sold for their login credentials; they become tradable commodities for various nefarious purposes. Compromised business accounts can be leveraged for:
- Ad Fraud: Running unauthorized advertisements, often for scams or malicious software, funded by the victim’s linked payment methods.
- Scams and Phishing: Using the compromised account’s reputation to launch further phishing campaigns or scams against its network of friends and followers.
- Brand Impersonation: Assuming the identity of a legitimate business to defraud customers or spread misinformation.
- Identity Theft: Harvesting personal data from the account to facilitate broader identity theft schemes.
- Account Recovery Services (Illicit): In a darkly ironic twist, some operators in this ecosystem even offer "account recovery" services for previously stolen accounts, effectively extorting victims to regain access to their own digital property.
As Shaked Chen noted, this campaign offers "a window into the dark market around stolen Facebook assets, where access, business identity, ad reputation, and even account recovery have all become tradable commodities." The continuous evolution of these tactics and the repurposing of trusted platforms for delivery, hosting, and monetization highlight a significant challenge for cybersecurity professionals and platform providers alike.
Implications for Platforms and Users
The exploitation of Google AppSheet raises critical questions about platform responsibility. While Google AppSheet is a legitimate and valuable tool, its abuse as a "phishing relay" underscores the inherent risks associated with open, versatile platforms. Google, like other technology giants, faces the continuous challenge of balancing platform utility with security against malicious actors. While specific statements from Google regarding this particular incident are not yet public, it is logical to infer that the company would be actively investigating the abuse of its service. Such incidents typically prompt platform providers to review and enhance their abuse detection mechanisms, tighten policies, and potentially implement technical safeguards to prevent similar exploitation in the future. The reputation of a trusted platform is a valuable asset, and its misuse for cybercrime can erode user confidence.
For Meta (Facebook), this campaign represents an ongoing battle against persistent and adaptive threats. Despite Meta’s substantial investments in security, sophisticated social engineering and the exploitation of third-party platforms continue to pose significant challenges. Meta’s inferred response would likely emphasize user education, the importance of strong, unique passwords, and robust multi-factor authentication (MFA). They would also be expected to continue enhancing their internal detection systems for compromised accounts and phishing attempts originating from external sources.

The primary burden, however, often falls on the end-user. The success of "AccountDumpling" is a stark reminder of the need for heightened vigilance and critical thinking in the digital realm. The psychological manipulation inherent in these phishing attempts—creating a sense of urgency, fear, or opportunity—is a potent weapon.
Preventative Measures and Recommendations
To mitigate the risk of falling victim to sophisticated phishing campaigns like "AccountDumpling," both individuals and businesses must adopt proactive security measures:
- Verify Sender Authenticity: Always scrutinize the sender’s email address. While
[email protected]might appear legitimate at first glance, any unexpected communication from a service like Google AppSheet, especially regarding a Meta account, should raise a red flag. Legitimate communications from Meta will typically come from official Meta or Facebook domains. - Exercise Caution with Links: Never click on links embedded in suspicious or unexpected emails. Instead, if an email purports to be from a service like Facebook or Meta and asks you to take action, navigate directly to the official website (e.g., Facebook.com or Business.Facebook.com) by typing the URL into your browser. Log in there and check for any notifications or alerts within your account dashboard.
- Enable Multi-Factor Authentication (MFA): MFA adds an essential layer of security by requiring a second form of verification (e.g., a code from your phone) in addition to your password. Even if your password is stolen, threat actors cannot access your account without this second factor. This is arguably the single most effective defense against credential theft.
- Recognize Social Engineering Tactics: Be aware of common phishing lures, such as threats of account deletion, urgent calls to action, promises of lucrative opportunities, or requests for sensitive information. Cybercriminals thrive on creating panic or excitement to bypass rational thought.
- Regularly Review Account Activity: Periodically check your Facebook account’s login history, linked apps, and security settings for any unauthorized activity. For Facebook Business accounts, regularly review ad spending and page roles.
- Employee Security Awareness Training: Businesses, particularly those with multiple individuals managing social media accounts, should implement regular security awareness training. Employees should be educated on how to identify phishing attempts, the importance of strong passwords, and proper incident reporting procedures.
- Keep Software Updated: Ensure operating systems, web browsers, and security software are always up to date to protect against known vulnerabilities.
In conclusion, the "AccountDumpling" campaign serves as a critical reminder of the dynamic and relentless nature of cyber threats. The sophisticated exploitation of legitimate platforms like Google AppSheet by well-organized cybercriminal groups, particularly those linked to Vietnam, necessitates a multi-faceted defense strategy. This strategy must encompass enhanced platform security measures, continuous user education, and a collective commitment to vigilance to safeguard digital identities and assets in an increasingly interconnected world. The battle against cybercrime is an ongoing one, demanding constant adaptation and proactive measures from all stakeholders.