A container is a lightweight, standalone, executable package of software that includes everything needed to run a piece of software: code, runtime, system tools, system libraries, and settings. This technology is part of a broader trend known as containerization, a method of packaging software so it can be run with its dependencies isolated from other processes.
This article explores what containerization is, the key components of containers, and its differences from virtual machines (VMs). The sections below will also touch on the benefits, use cases, and popular container technologies. Lastly, this article will look into potential challenges and future trends in containerization.
Understanding Containers: The Foundation of Modern Software Architecture
Containers have emerged as a transformative technology in the software development and deployment landscape. At their core, containers enable developers to package and run applications in isolated, reproducible environments. This process, known as containerization, ensures that an application functions consistently regardless of its underlying infrastructure, from a developer’s local machine to vast cloud deployments.
The fundamental principle behind containers is their ability to encapsulate an application along with all its dependencies. This includes the application’s code, runtime environment, libraries, system tools, and configuration settings, all bundled into a single, portable unit called a container image. Unlike traditional methods that often struggle with "it works on my machine" scenarios due to environmental discrepancies, containers offer a unified and efficient pathway for software delivery.
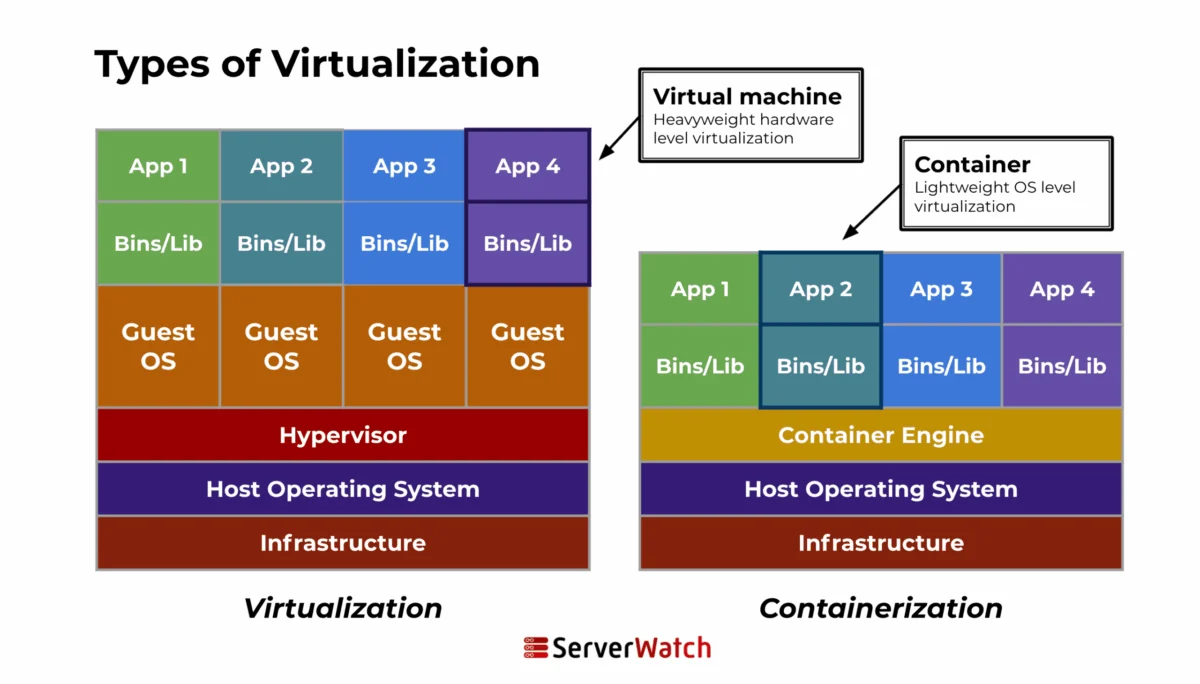
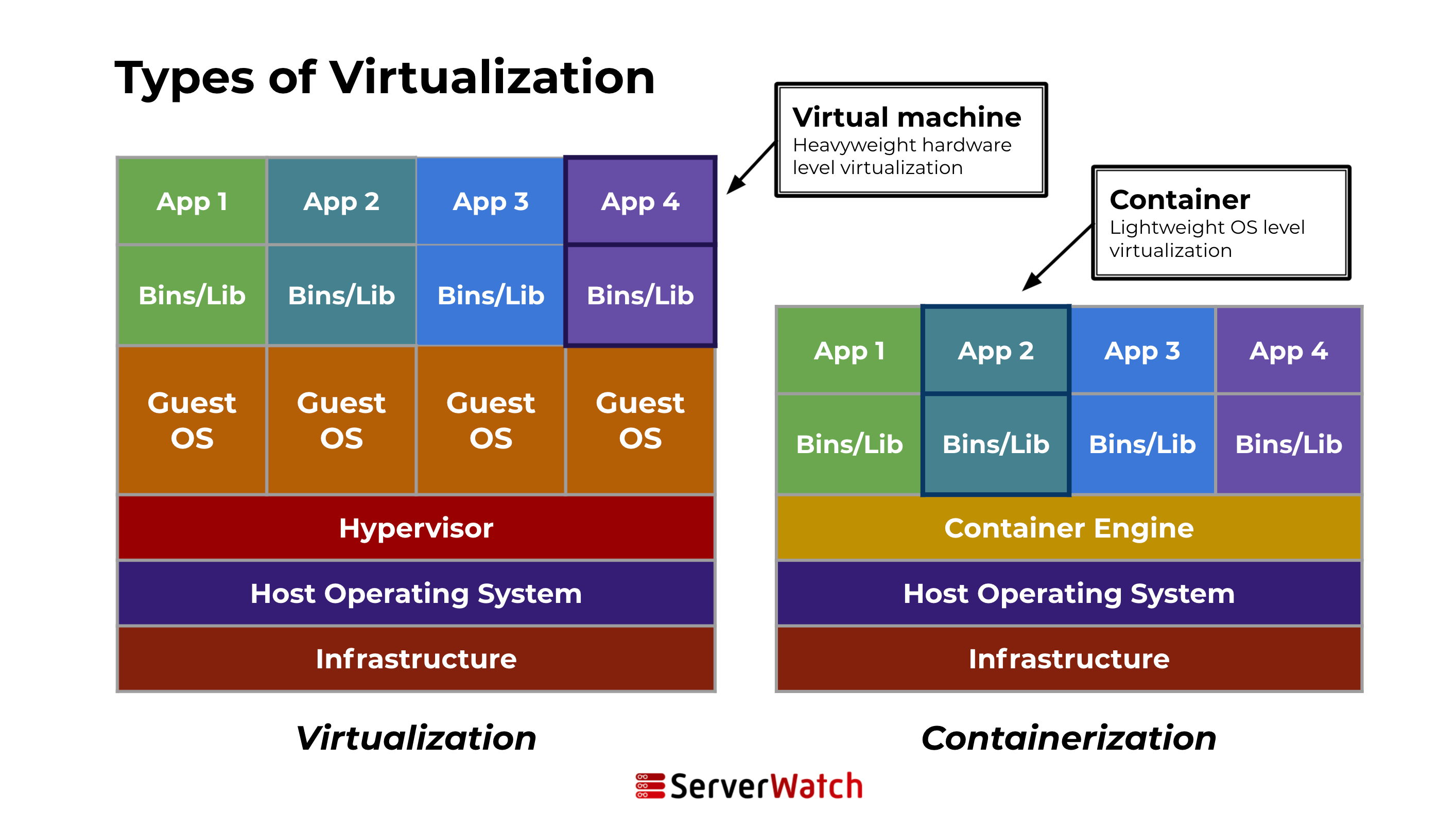
A key differentiator of containers lies in their resource efficiency. They achieve isolation by sharing the host system’s kernel while maintaining their own distinct filesystem, CPU, memory, and process space. This shared kernel architecture makes containers significantly lighter and faster to launch compared to virtual machines (VMs), which require a full guest operating system for each instance. This efficiency translates into better hardware utilization and reduced operational costs.
Containers vs. Virtual Machines: A Fundamental Architectural Divide
The distinction between containers and virtual machines is critical for understanding their respective roles in modern IT infrastructure. While both technologies provide isolated environments for running applications, their underlying architectures differ significantly.
| Feature | Containers | Virtual Machines |
|---|---|---|
| Architecture | Containers share the host system’s kernel, isolating application processes from the underlying OS. They do not require a full OS for each instance, making them lightweight and fast to start. | A VM includes the application, its dependencies, and an entire guest OS. This guest OS runs on virtual hardware managed by a hypervisor, which sits atop the host’s physical hardware. VMs offer strong isolation from each other and the host system, enhancing security. |
| Resource Management | Containers are highly efficient, consuming fewer resources because they share the host kernel and only need the application and its runtime. | The necessity of running a full OS in each VM leads to higher resource consumption. This can result in less efficient utilization of the underlying hardware compared to containerized environments. |
This architectural difference has profound implications for performance, scalability, and resource utilization. For instance, a server that can host 20 virtual machines might be able to run hundreds of containers, a testament to the efficiency gains offered by containerization.
How Does Containerization Work? The Mechanics of Encapsulation
The process of containerization involves packaging an application and its entire operating environment into a self-contained unit. This encapsulation ensures portability and consistency across diverse computing environments. The core mechanism relies on operating system-level virtualization, where specific kernel features are leveraged to create isolated user-space instances.
The typical workflow for creating and running a container involves several key steps:
- Image Creation: Developers define the container’s contents and configuration in a Dockerfile or similar specification. This file outlines the base operating system, dependencies, application code, and startup commands.
- Image Building: A container engine, such as Docker, reads the Dockerfile and builds a container image. This image is a read-only template containing all the necessary components.
- Container Runtime: When a container is launched, the container engine creates a writable layer on top of the read-only image. This creates an isolated environment where the application can run.
- Execution: The application within the container executes, interacting with its isolated environment while sharing the host’s kernel.
Key Components of a Container: The Building Blocks of Isolation
A container, while seemingly a single entity, is composed of several critical components that enable its functionality and isolation:
- Container Image: The immutable, read-only template that contains the application code, runtime, libraries, environment variables, and configuration files.
- Container Runtime: The software responsible for running containers, managing their lifecycle, and enforcing isolation. Examples include containerd, CRI-O, and Docker Engine.
- Namespaces: A Linux kernel feature that provides process isolation by giving each container its own view of the system’s resources, such as process IDs, network interfaces, and mount points.
- Control Groups (cgroups): Another Linux kernel feature that limits and allocates system resources (CPU, memory, I/O) to containers, preventing one container from consuming all available resources and impacting others.
- Union File Systems (UnionFS): A layered filesystem that allows multiple directories or file systems to be transparently overlaid, forming a single coherent file system. This enables efficient sharing of base image layers among multiple containers.
- Networking Interface: Each container typically gets its own network namespace, allowing it to have its own IP address, routing table, and network ports, separate from the host and other containers.
Container Use Cases: Driving Innovation Across Industries
The versatility and efficiency of containerization have led to its widespread adoption across a multitude of use cases, fundamentally reshaping how software is developed, deployed, and managed.
Microservices and Cloud-Native Applications: The Perfect Pairing
Containers are a natural fit for microservices architectures, a design pattern that structures an application as a collection of small, independent services. Each microservice can be packaged and deployed in its own container, promoting loose coupling and enabling independent development, deployment, and scaling. This modular approach enhances agility and resilience.
In the realm of cloud-native applications, containers are indispensable. They facilitate the creation of highly scalable, resilient, and manageable applications designed to thrive in dynamic cloud environments. Orchestration platforms like Kubernetes automate the deployment, scaling, and management of containerized microservices, ensuring high availability and efficient resource utilization through features like automated healing and load balancing. This synergy allows organizations to build applications that can dynamically adapt to fluctuating demands.
Continuous Integration/Continuous Deployment (CI/CD) Pipelines: Accelerating Software Delivery
Containerization has become a cornerstone of modern CI/CD pipelines, significantly streamlining the software development lifecycle. By encapsulating applications and their dependencies, containers ensure consistency across development, testing, staging, and production environments. This eliminates the common "works on my machine" problem and reduces deployment failures caused by environmental inconsistencies.
Automated testing is another area where containers excel. Each code commit can be tested in a production-like containerized environment, ensuring that issues are identified and resolved early in the development cycle. This leads to more robust software releases and accelerates the pace at which new features and updates can be delivered to users. The ability to quickly spin up and tear down ephemeral testing environments further enhances efficiency.
Application Packaging and Distribution: Unlocking Portability
The inherent portability of containers simplifies the packaging and distribution of software. An application, along with all its necessary components, can be bundled into a single container image, which can then be run on any system that supports the container runtime. This eliminates the complexities of managing dependencies and environment configurations across different platforms and cloud providers.
Container registries, such as Docker Hub or Amazon Elastic Container Registry (ECR), act as central repositories for storing and sharing container images. This facilitates version control, enabling teams to easily roll back to previous stable versions of an application if issues arise, thereby enhancing the reliability and stability of deployments.
13 Benefits of Containerization: A Transformative Advantage
Containerization has emerged as a pivotal technology, offering a comprehensive suite of advantages that empower organizations to innovate faster and operate more efficiently. The benefits extend across development, operations, and business outcomes.
- Increased Agility: Faster development cycles and quicker deployment of new features.
- Enhanced Portability: Applications run consistently across different environments, from laptops to the cloud.
- Improved Resource Utilization: Lighter weight compared to VMs leads to better hardware efficiency and reduced costs.
- Faster Deployment Times: Applications can be spun up and scaled rapidly.
- Consistent Environments: Eliminates "works on my machine" issues by packaging applications with their dependencies.
- Isolation: Applications and their dependencies are isolated, preventing conflicts.
- Scalability: Easily scale applications up or down based on demand.
- Simplified Management: Orchestration tools streamline the management of complex containerized applications.
- Cost Savings: Reduced infrastructure needs and more efficient resource usage contribute to lower costs.
- Microservices Support: Ideal for building and deploying granular, independent services.
- DevOps Enablement: Fosters collaboration and efficiency between development and operations teams.
- Faster Time to Market: Accelerates the entire software delivery pipeline.
- Improved Reliability and Resilience: Easier to recover from failures and maintain application uptime.
Challenges and Considerations in Containerization: Navigating the Complexities
While the advantages of containerization are significant, organizations must also be aware of the potential challenges and considerations associated with its adoption and management.
Security Issues: Fortifying the Containerized Ecosystem
Security is paramount in any computing environment, and containerization introduces its own set of considerations. Common security concerns include:
- Image Vulnerabilities: Container images can contain known vulnerabilities in their base operating system or application dependencies. Regular scanning and updating are crucial.
- Runtime Security: Ensuring the container runtime itself is secure and properly configured is vital to prevent unauthorized access or manipulation.
- Container Escapes: While rare, a compromised container could potentially exploit vulnerabilities in the host kernel to gain access to the host system or other containers.
- Network Security: Proper network segmentation and access controls are necessary to protect containerized applications and prevent lateral movement in case of a breach.
- Secrets Management: Securely managing sensitive information like API keys and passwords within containerized applications requires dedicated solutions.
Complexity in Management: Orchestrating at Scale
While containers simplify many aspects of deployment, managing large-scale containerized environments can introduce new complexities:
- Orchestration Overhead: Implementing and managing container orchestration platforms like Kubernetes requires specialized skills and can be resource-intensive.
- Monitoring and Logging: Gaining visibility into the performance and health of numerous distributed containers requires robust monitoring and logging solutions.
- Networking Complexity: Managing network policies, service discovery, and ingress/egress traffic for a dynamic set of containers can be challenging.
- Stateful Applications: Managing stateful applications (e.g., databases) within containers requires careful consideration of data persistence and recovery strategies.
- Skill Gaps: Organizations may face challenges in finding or training personnel with the necessary expertise in containerization technologies.
Integration with Existing Systems: Bridging the Old and the New
Adopting containerization often involves integrating this modern technology with existing legacy systems and infrastructure. This process presents unique challenges:
- Compatibility Issues: Ensuring that containerized applications can seamlessly interact with existing databases, APIs, and middleware can be complex.
- Data Migration: Migrating data from traditional systems to containerized environments or ensuring data consistency between the two can be a significant undertaking.
- Cultural Shift: Embracing containerization often requires a shift in development and operations culture, moving towards DevOps practices and a more automated approach.
- Security Policy Alignment: Ensuring that container security practices align with existing organizational security policies and compliance requirements is essential.
Popular Container Technologies: The Tools of the Trade
The container ecosystem is rich with powerful tools and platforms that enable developers and operators to harness the benefits of containerization.
Docker: The Pioneer of Containerization
Docker has played a pivotal role in popularizing container technology, making it accessible and user-friendly. It provides a comprehensive platform for building, shipping, and running containerized applications.
Key Features of Docker:
- Dockerfile: A script for automating the creation of container images.
- Docker Engine: The core runtime that builds and runs containers.
- Docker Hub: A cloud-based registry for sharing and discovering container images.
- Docker Compose: A tool for defining and running multi-container Docker applications.
- Container Isolation: Utilizes OS-level features for process and filesystem isolation.
Benefits of Docker:
- Ease of Use: Simplified workflow for creating and deploying containers.
- Portability: Images are designed to run consistently across different environments.
- Large Community and Ecosystem: Extensive support, tools, and pre-built images.
Kubernetes: The De Facto Standard for Container Orchestration
Kubernetes (K8s) has emerged as the leading open-source platform for automating the deployment, scaling, and management of containerized applications. It is designed to manage containerized workloads and services at scale.
Key Features of Kubernetes:
- Automated Rollouts and Rollbacks: Manages application updates and can automatically revert to previous versions.
- Service Discovery and Load Balancing: Automatically exposes containers to the network and distributes traffic.
- Self-Healing: Restarts failed containers, replaces and reschedules containers when nodes die.
- Storage Orchestration: Allows automatic mounting of storage systems.
- Secret and Configuration Management: Enables secure storage and management of sensitive information.
Benefits of Kubernetes:
- Scalability and Resilience: Built to handle large-scale deployments and ensure high availability.
- Portability: Works across various cloud providers and on-premises environments.
- Extensibility: A rich ecosystem of plugins and extensions allows for customization.
- Declarative Configuration: Define desired states, and Kubernetes works to achieve them.
Other Notable Containers and Technologies
Beyond Docker and Kubernetes, several other technologies contribute to the containerization landscape:
- containerd: An industry-standard container runtime that focuses on simplicity, robustness, and portability. It is a core component used by Docker and Kubernetes.
- CRI-O: A lightweight container runtime specifically designed for Kubernetes, focusing on adhering to the Kubernetes Container Runtime Interface (CRI).
- Podman: A daemonless container engine for developing, managing, and running OCI (Open Container Initiative) containers on Linux systems. It offers a Docker-compatible CLI.
- LXC/LXD: Linux Containers (LXC) provide OS-level virtualization. LXD builds upon LXC to offer a more user-friendly experience for managing containers.
- OpenShift: A Red Hat enterprise Kubernetes platform that provides a comprehensive suite of tools for containerized application development and deployment.
Future Trends in Containerization: Evolving with Technology
The evolution of containerization is far from over. As it becomes more deeply integrated into the fabric of IT infrastructure, several key trends are shaping its future.
Integration with Emerging Technologies: A Symbiotic Relationship
Containerization is not an isolated technology; it is rapidly converging with and enabling other cutting-edge fields:
- Artificial Intelligence (AI) and Machine Learning (ML): Containers provide consistent and reproducible environments for training and deploying complex AI/ML models, simplifying dependency management and scaling computational resources.
- Edge Computing: Containerization is crucial for deploying and managing applications at the network edge, enabling distributed intelligence and reducing latency.
- Serverless Computing: While seemingly distinct, serverless platforms often leverage containers under the hood to manage and execute functions, offering a streamlined developer experience.
- WebAssembly (Wasm): Emerging standards are exploring how WebAssembly can be used within containerized environments, offering enhanced security and portability for web and non-web applications.
- Blockchain and Distributed Ledgers: Containers can be used to deploy and manage nodes within blockchain networks, simplifying infrastructure management.
Evolution of Container Standards and Regulations: Towards Maturity and Security
As containerization matures and becomes more integral to critical business operations, the development of robust standards and regulatory frameworks is essential:
- Standardization Efforts: Continued work on Open Container Initiative (OCI) standards for image formats and runtimes ensures interoperability and reduces vendor lock-in.
- Security Standards and Best Practices: Growing emphasis on developing and enforcing comprehensive security standards for container images, registries, and runtimes.
- Compliance and Governance: Increased focus on ensuring that containerized environments meet regulatory compliance requirements (e.g., GDPR, HIPAA) through auditing, policy enforcement, and secure configurations.
- Supply Chain Security: Enhanced measures to secure the software supply chain, from the origin of base images to the final deployed application, are becoming critical.
Bottom Line: The Role of Containers Will Continue to Grow
Containers have fundamentally altered the landscape of software development and deployment, offering unparalleled efficiency, scalability, and consistency. Their ability to package applications with their dependencies into portable units has streamlined development workflows, accelerated deployment cycles, and enabled the widespread adoption of microservices and cloud-native architectures.
As these technologies continue to evolve and mature, containers are poised to become even more integral to modern IT infrastructure. The ongoing integration with emerging technologies like AI, edge computing, and WebAssembly, coupled with the development of more robust standards and security frameworks, suggests a future where containers are not just a deployment mechanism but a foundational element of innovation. Organizations that effectively leverage container technologies will be well-positioned to adapt to the dynamic demands of the digital era, driving efficiency and unlocking new possibilities in software development and beyond.
Learn more about virtual machines, and get to know the best virtualization companies to pick the one that most suits your needs.