In an increasingly complex digital landscape, where cyber threats evolve with unprecedented speed, the traditional…
Tag: Privacy
Azerbaijani Energy Firm Hit by Repeated Microsoft Exchange Exploitation
A highly persistent and multi-wave cyber intrusion, attributed with moderate-to-high confidence to the China-linked threat…

Microsoft Unveils MDASH: A Multi-Model AI System Revolutionizing Vulnerability Discovery and Remediation at Scale
Microsoft has officially unveiled MDASH, a groundbreaking multi-model artificial intelligence (AI)-driven system engineered to significantly…
RubyGems Repository Targeted in Novel GemStuffer Data Exfiltration Campaign, Raising Software Supply Chain Security Concerns
Cybersecurity researchers have issued an urgent alert regarding a sophisticated and unconventional campaign, dubbed GemStuffer,…
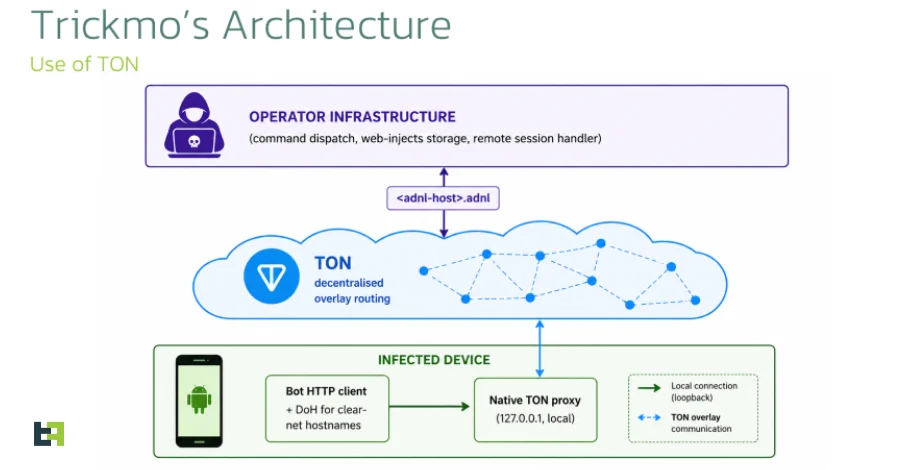
TrickMo Android Banking Trojan Adopts The Open Network (TON) for Stealthy Command-and-Control, Escalating Mobile Threat Landscape.
Cybersecurity researchers have issued a stark warning regarding a sophisticated new iteration of the TrickMo…
RubyGems Temporarily Suspends New Account Registrations Following Major Supply Chain Attack Targeting Open-Source Ecosystem
RubyGems, the quintessential package manager underpinning the Ruby programming language, has initiated an immediate and…
Exim Releases Critical Security Update for "Dead.Letter" Vulnerability Allowing Remote Code Execution.
Exim, a widely deployed open-source Mail Transfer Agent (MTA) integral to the global email infrastructure,…

Securing the Invisible Hand: The Urgent Imperative of Agentic AI Cybersecurity
Agentic Artificial Intelligence (AI) is already operating within the production environments of countless organizations globally,…

Google Discloses First AI-Developed Zero-Day Exploit Used in Mass Exploitation Campaign, Signaling a New Era of AI-Powered Cyber Warfare
Mountain View, CA – Google on Monday revealed a groundbreaking and concerning development in the…
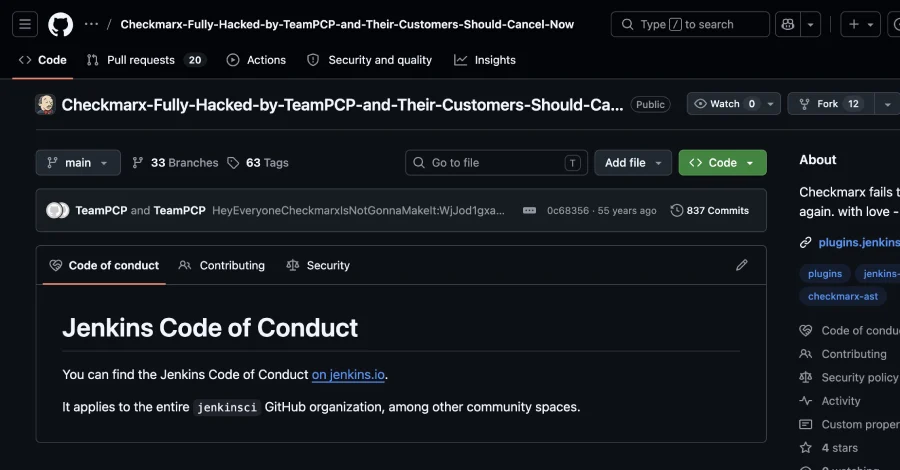
Checkmarx Confirms Second Major Supply Chain Breach as Modified Jenkins AST Plugin Found in Marketplace, Attributed to Persistent TeamPCP Attacks
A significant breach has once again impacted Checkmarx, a prominent application security testing (AST) vendor,…

